 Blast
Blast
$2.68 B
1.73%
- The proof system is still under development.
- Users' withdrawals can be censored by the permissioned operators.
- Upgrades executed by actors with more centralized control than a Security Council provide less than 7d for users to exit if the permissioned operator is down or censoring.
...
Choose token
 PacMoon (PAC)
PacMoon (PAC) Renzo Restaked ETH (ezETH)
Renzo Restaked ETH (ezETH) Liquid staked Ether 2.0 (stETH)
Liquid staked Ether 2.0 (stETH) Ether (ETH)
Ether (ETH) Wrapped BTC (WBTC)
Wrapped BTC (WBTC) Uniswap (UNI)
Uniswap (UNI) Wrapped Ether (WETH)
Wrapped Ether (WETH) USD Coin (USDC)
USD Coin (USDC) Tether USD (USDT)
Tether USD (USDT) Renzo Restaked ETH (ezETH)
Renzo Restaked ETH (ezETH) 0x Protocol Token (ZRX)
0x Protocol Token (ZRX) 10Set Token (10SET)
10Set Token (10SET) 1INCH Token (1INCH)
1INCH Token (1INCH) Aave Token (AAVE)
Aave Token (AAVE) Across Protocol Token (ACX)
Across Protocol Token (ACX) Alchemix USD (alUSD)
Alchemix USD (alUSD) Alchemy (ACH)
Alchemy (ACH)...
...
Blast upgrades to censor exploiter
2024 Mar 26th
The Munchables exploiter is prohibited from forcing transactions.
Funds can be stolen if
Funds can be frozen if
MEV can be extracted if
State validation
In developmentCurrently the system permits invalid state roots. More details in project overview.
Data availability
On chainAll of the data needed for proof construction is published on chain.
Exit window
NoneThere is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Sequencer failure
Self sequenceIn the event of a sequencer failure, users can force transactions to be included in the project’s chain by sending them to L1. There is a 12h delay on this operation.
Proposer failure
Cannot withdrawOnly the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
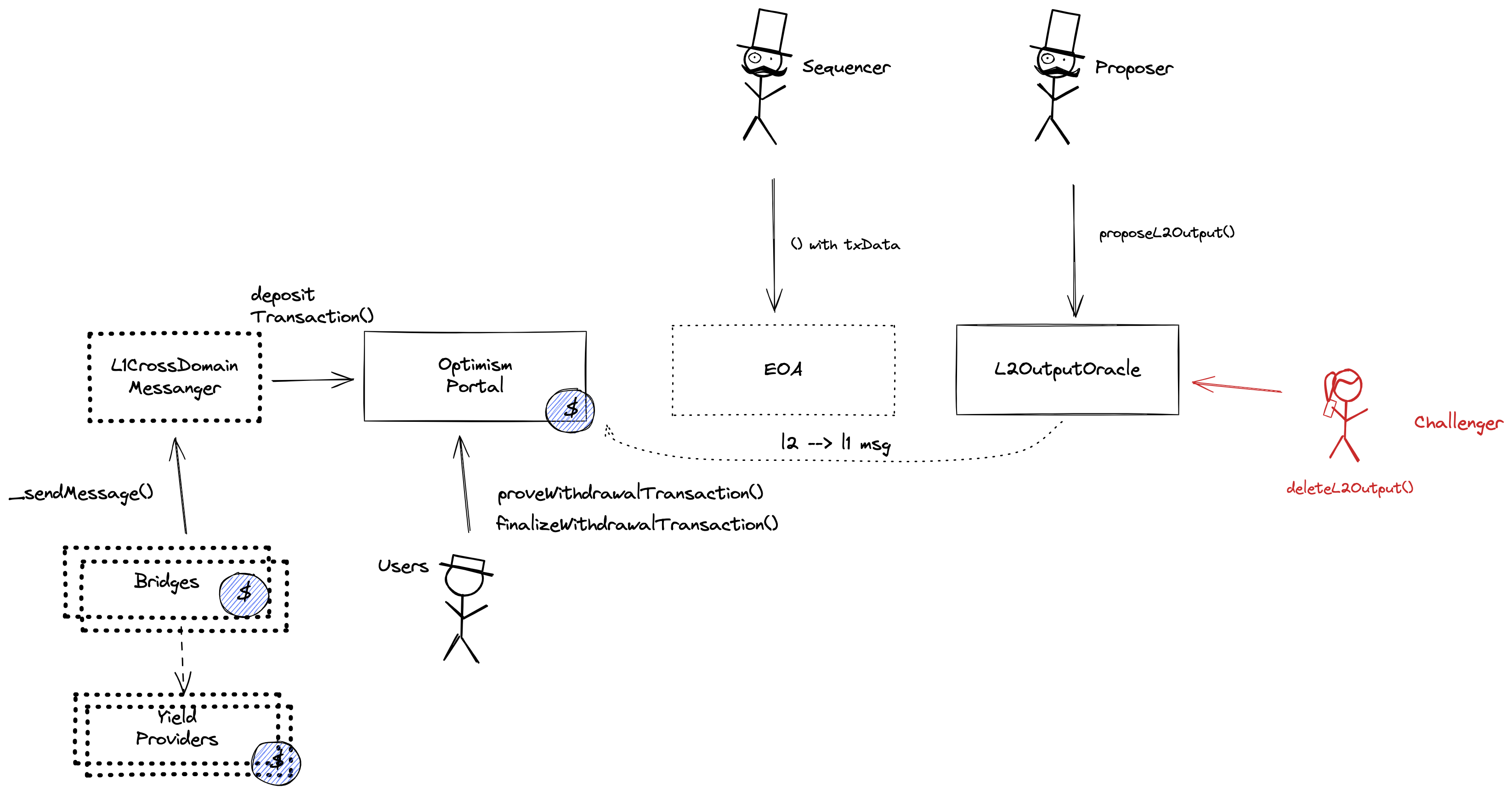
Fraud proofs are in development
Ultimately, OP stack chains will use interactive fraud proofs to enforce state correctness. This feature is currently in development and the system permits invalid state roots.
Funds can be stolen if an invalid state root is submitted to the system (CRITICAL).
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap calldata. This ensures that it will always be available when needed.
The system has a centralized operator
The operator is the only entity that can propose blocks. A live and trustworthy operator is vital to the health of the system.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on-chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract directly.
Regular exit
The user initiates the withdrawal by submitting a regular transaction on this chain. When the block containing that transaction is finalized the funds become available for withdrawal on L1. The process of block finalization takes a challenge period of 12d to complete. Once funds are added to the withdrawal queue, operator must ensure there is enough liquidity for withdrawals. If not, they need to reclaim tokens from Yield Providers.
Funds can lose value if there is a hack or the yield goes negative for yield providers (CRITICAL).
Funds can be frozen if there is not enough liquidity in the bridge, transactions are locked in withdrawal queue (CRITICAL).
Forced exit
If the user experiences censorship from the operator with regular exit they can submit their withdrawal requests directly on L1. The system is then obliged to service this request or halt all withdrawals, including forced withdrawals from L1 and regular withdrawals initiated on L2. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular exit.
EVM compatible smart contracts are supported
OP stack chains are pursuing the EVM Equivalence model. No changes to smart contracts are required regardless of the language they are written in, i.e. anything deployed on L1 can be deployed on L2.
The system uses the following set of permissioned addresses:
Owner of AddressManager. Admin of OptimismPortal, SystemConfig, L2OutputOracle, L1ERC721Bridge, OptimismMintableERC20Factory, L1StandardBridge.
Central actor allowed to commit L2 transactions to L1.
Central actor allowed to post new L2 state roots to L1.
Central actor allowed to delete L2 state roots proposed by a Proposer.
Central actor allowed to pause deposits and withdrawals.
This address is the owner of all upgradable contracts. It is also designated as a Guardian of the OptimismPortal, meaning it can halt withdrawals and as a Challenger. It can upgrade the bridge implementation potentially gaining access to all funds, and change the sequencer, state root proposer or any other system component (unlimited upgrade power). This is a Gnosis Safe with 3 / 5 threshold.
Those are the participants of the BlastMultisig.
Account privileged to change System Config parameters such as Sequencer Address and gas limit.
The system consists of the following smart contracts:
The L2OutputOracle contract contains a list of proposed state roots which Proposers assert to be a result of block execution. Currently only the PROPOSER address can submit new state roots.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
The OptimismPortal contract is the main entry point to deposit funds from L1 to L2. It also allows to prove and finalize withdrawals. This contract stores the following tokens: ETH.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
It contains configuration parameters such as the Sequencer address, the L2 gas limit and the unsafe block signer address.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
The L1CrossDomainMessenger (L1xDM) contract sends messages from L1 to L2, and relays messages from L2 onto L1. In the event that a message sent from L1 to L2 is rejected for exceeding the L2 epoch gas limit, it can be resubmitted via this contract’s replay function.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
The L1StandardBridge contract is the main entry point to deposit ERC20 tokens from L1 to L2. This contract can store any token.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
The L1ERC721Bridge contract is used to bridge ERC-721 tokens from L1 to L2.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
The L1 Bridge to Blast with the facility to invest escrowed tokens.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Contract managing Yield Providers for ETH. This contract stores the following tokens: ETH, stETH.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Contract managing Yield Providers for stablecoins. This contract stores the following tokens: .
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Yield Provider for ETH investing ETH into stETH.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Yield Provider for DAI investing DAI into the MakerDAO DSR.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Value Locked is calculated based on these smart contracts and tokens:
Main entry point for users depositing ERC20 token that do not require custom gateway.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Escrow for ETH that is invested into a yield-bearing contracts such as stETH.
Main entry point for users depositing ETH.
Can be upgraded by: ProxyAdmin
Upgrade delay: No delay
Pre-launch Blast Vault that keeps stETH. Funds from this Vault can be migrated to Blast bridge.
Escrow for DAI that is invested into a yield-bearing contracts such as MakerDAO DSR.
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).