 Linea
Linea
$761.76 M
9.35%
- Users' withdrawals can be censored by the permissioned operators.
- Upgrades executed by actors with more centralized control than a Security Council provide less than 7d for users to exit if the permissioned operator is down or censoring.
- Security Council members are not publicly known.
| Website | linea.build |
|---|---|
| Docs | docs.linea.build |
| Explorer | explorer.linea.buildlinea.l2scan.co |
| Social | @LineaBuildDiscordlinea.mirror.xyz |
| rollup.codes | rollup.codes/linea |
...
Choose token
 Foxy (FOXY)
Foxy (FOXY) Linda (LINDA)
Linda (LINDA) Lynex (LYNX)
Lynex (LYNX) Mendi Finance (MENDI)
Mendi Finance (MENDI) StakeStone Ether (STONE)
StakeStone Ether (STONE) Renzo Restaked ETH (ezETH)
Renzo Restaked ETH (ezETH) Ether (ETH)
Ether (ETH) USD Coin (USDC)
USD Coin (USDC) Wrapped BTC (WBTC)
Wrapped BTC (WBTC) Tether USD (USDT)
Tether USD (USDT) Wrapped liquid staked Ether 2.0 (wstETH)
Wrapped liquid staked Ether 2.0 (wstETH) Dai Stablecoin (DAI)
Dai Stablecoin (DAI) Uniswap (UNI)
Uniswap (UNI) LUSD Stablecoin (LUSD)
LUSD Stablecoin (LUSD) Symbiosis (SIS)
Symbiosis (SIS) Kyber Network Crystal v2 (KNC)
Kyber Network Crystal v2 (KNC) SHIBA INU (SHIB)
SHIBA INU (SHIB) THORChain ETH.RUNE (RUNE)
THORChain ETH.RUNE (RUNE) Lido DAO Token (LDO)
Lido DAO Token (LDO) ChainLink Token (LINK)
ChainLink Token (LINK) Gnosis Token (GNO)
Gnosis Token (GNO)...
...
Open Testnet is Live
2023 Mar 28th
Linea has launched on the Goerli testnet, allowing users and developers to test the platform.
Funds can be stolen if
Funds can be frozen if
Users can be censored if
MEV can be extracted if
State validation
ZK proofs (SN)zkSNARKS are zero knowledge proofs that ensure state correctness, but require trusted setup.
Data availability
On chainAll of the data needed for proof construction is published on chain. Unlike most ZK rollups, transaction data is posted instead of state diffs.
Exit window
NoneThere is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Sequencer failure
No mechanismThere is no mechanism to have transactions be included if the sequencer is down or censoring.
Proposer failure
Cannot withdrawOnly the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
Validity proofs ensure state correctness
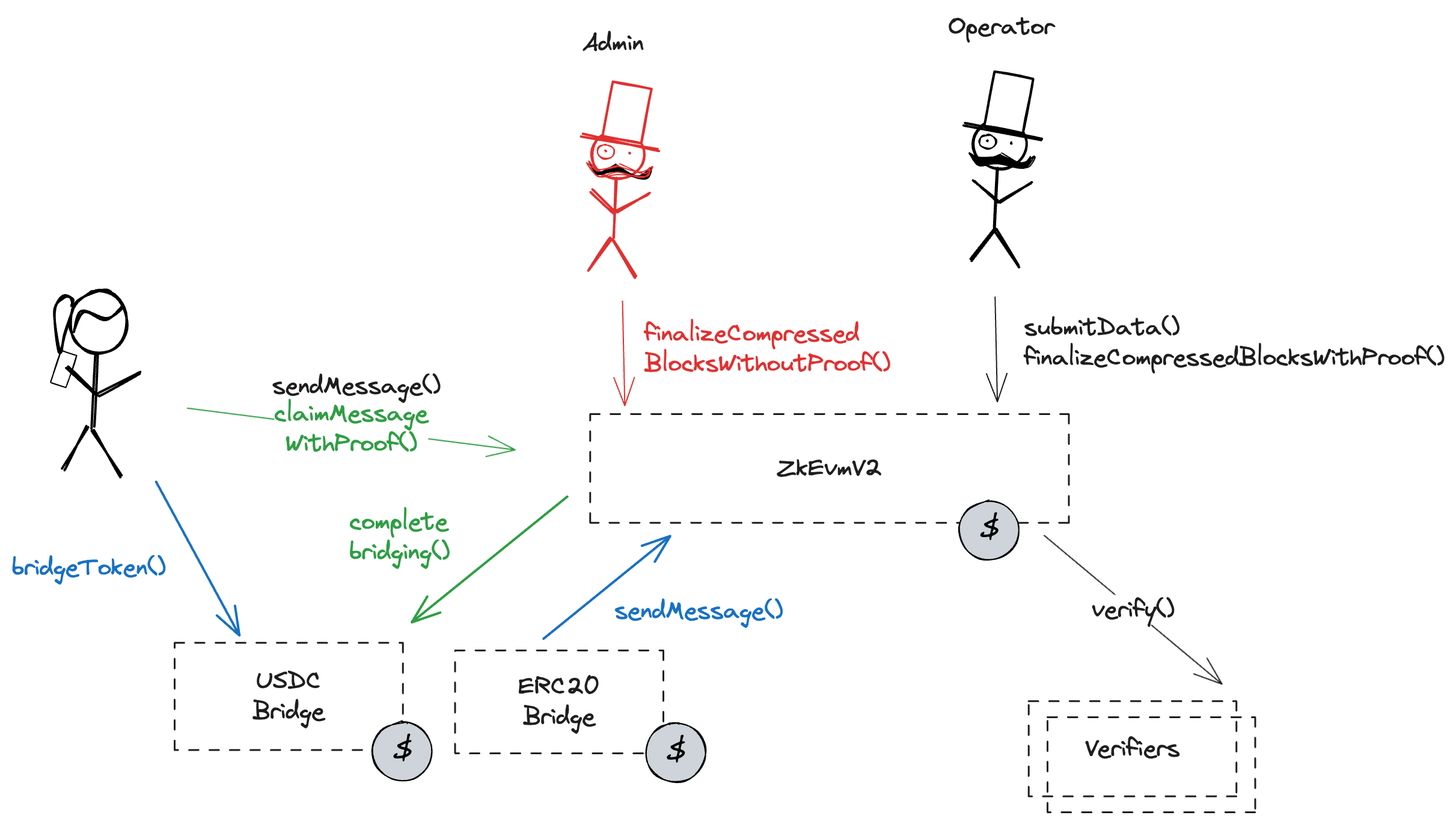
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract. Operator can finalize L2 state root without proof.
Funds can be stolen if the operator forces and finalizes L2 state root without proof.
Zero knowledge SNARK cryptography is used
Despite their production use zkSNARKs are still new and experimental cryptography. Cryptography has made a lot of advancements in the recent years but all cryptographic solutions rely on time to prove their security. In addition zkSNARKs require a trusted setup to operate.
Funds can be stolen if the cryptography is broken or implemented incorrectly.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap blobs or calldata. This ensures that it will be available for enough time.
The system has a centralized sequencer
Only a trusted sequencer is allowed to submit transaction batches. A mechanism for users to submit their own batches is currently disabled.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Funds can be frozen if the sequencer refuses to include an exit transaction (CRITICAL).
Users can't force any transaction
There is no general mechanism to force the sequencer to include the transaction.
Users can be censored if the operator refuses to include their transactions.
Regular exit
The user initiates the withdrawal by submitting a regular transaction on this chain. When the block containing that transaction is proven the funds become available for withdrawal on L1. Finally the user submits an L1 transaction to claim the funds. This transaction does not require a merkle proof. Note that withdrawal requests can be censored by the Sequencer. Currently, there is a general limit of 18750.0 ETH that can be withdrawn within each 1d time window.
Funds can be frozen if the operator censors withdrawal transaction.
The system uses the following set of permissioned addresses:
Admin of the Linea rollup. It can upgrade core contracts, bridges, update permissioned actors, and publish blocks by effectively overriding the proof system. This is a Gnosis Safe with 4 / 8 threshold.
Those are the participants of the AdminMultisig.
Module to the AdminMultisig. Allows to add additional members to the multisig via permissions to call functions specified by roles.
The operators are allowed to prove blocks and post the corresponding transaction data.
Address allowed to pause the ERC20Bridge, the USDCBridge and the core functionalities of the project.
The verifier setters are allowed to change the verifier address.
The system consists of the following smart contracts:
The main contract of the Linea zkEVM rollup. Contains state roots, the verifier addresses and manages messages between L1 and the L2. The contract is pausable by 0x892bb7EeD71efB060ab90140e7825d8127991DD3. This contract stores the following tokens: ETH.
Can be upgraded by: AdminMultisig
Upgrade delay: No delay
Owner of the ProxyAdmin and Verifier Setter. The current delay is 0s.
Contract used to bridge ERC20 tokens. This contract can store any token.
Can be upgraded by: AdminMultisig
Upgrade delay: No delay
Contract used to bridge USDC tokens. This contract stores the following tokens: USDC.
Can be upgraded by: AdminMultisig
Upgrade delay: No delay
Value Locked is calculated based on these smart contracts and tokens:
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 0s delay on code upgrades.
