Search
Search for projects by name or address
 Cyber
Cyber
Badges
About
Cyber is a chain designed for social applications using an implementation of OP Plasma with DA challenges.
Badges
About
Cyber is a chain designed for social applications using an implementation of OP Plasma with DA challenges.
Why is the project listed in others?
Consequence: projects without a proper proof system fully rely on single entities to safely update the state. A malicious proposer can finalize an invalid state, which can cause loss of funds.
Consequence: projects without a data availability bridge fully rely on single entities (the sequencer) to honestly rely available data roots on Ethereum. A malicious sequencer can collude with the proposer to finalize an unavailable state, which can cause loss of funds.
Learn more about the recategorisation here.
2025 May 28 — 2026 May 28
The section shows the operating costs that L2s pay to Ethereum.
2025 May 28 — 2026 May 28
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
Funds can be stolen if
MEV can be extracted if
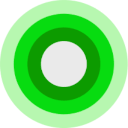
Fraud proofs allow actors watching the chain to prove that the state is incorrect. Interactive proofs (INT) require multiple transactions over time to resolve. Only one entity is currently allowed to propose and submit challenges, as only permissioned games are currently allowed.
Proof construction and state derivation rely fully on data that is NOT published onchain. A custom data availability (DA) provider without attestations is used, but data unavailability can be challenged.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Only the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
CyberDA is a data availability solution using data availability challenges (DA Challenges).
There are no onchain assets at risk of being slashed in case of a data withholding attack. However, there is a mechanism that allows users to challenge unavailability of data. The system is not secure if the malicious sequencer is able to outspend the altruistic challengers, and there is no pool of funds onchain to incentivize challengers.
There is no fraud detection mechanism in place. A data withholding attack can only be detected by nodes downloading the full data from the DA layer.
The committee does not meet basic security standards, either due to insufficient size, lack of member diversity, or poorly defined threshold parameters. The system lacks an effective DA bridge and it is reliant on the assumption of an honest sequencer, creating significant risks to data integrity and availability.
There is no delay in the upgradeability of the bridge. Users have no time to exit the system before the bridge implementation update is completed.
The relayer role is permissioned, and the DA bridge does not have a Security Council or a governance mechanism to propose new relayers. In case of relayer failure, the DA bridge will halt and be unable to recover without the intervention of a centralized entity.
Architecture

Data Availability Challenges
Cyber relies on DA challenges for data availability. The DA Provider submits an input commitment on Ethereum, and users can request the data behind the commitment off-chain from the DA Provider. If a DA challenger finds that the data behind a tx data commitment is not available, they can submit a challenge which requires locking a bond within 12h. A challenge can be resolved by publishing the preimage data within an additional 12h. In such case, a portion of the challenger bond is burned, with the exact amount estimated as the cost incurred by the resolver to publish the full data, meaning that the resolver and challenger will approximately lose the same amount of funds. The system is not secure if the malicious sequencer is able to outspend the altruistic challengers. If instead, after a challenge, the preimage data is not published, the chain reorgs to the last fully derivable state.
DA Bridge
Only hashes of data batches are posted as DA commitments to an EOA on Ethereum. However, there is a mechanism that allows users to challenge unavailability of data.
Funds can be lost if the sequencer posts an invalid data availability commitment and there are no challengers.
Funds can be lost if the sequencer posts an invalid data availability commitment, and they are able to outspend the challengers.
Updates to the system state can be proposed and challenged by permissioned operators only. If a state root passes the challenge period, it is optimistically considered correct and made actionable for withdrawals.
Proposers submit state roots as children of the latest confirmed state root (called anchor state), by calling the create function in the DisputeGameFactory. A state root can have multiple conflicting children. Each proposal requires a stake, currently set to 0.0 ETH, that can be slashed if the proposal is proven incorrect via a fraud proof. Stakes can be withdrawn only after the proposal has been confirmed. A state root gets confirmed if the challenge period has passed and it is not countered.
Challenges are opened to disprove invalid state roots using bisection games. Each bisection move requires a stake that increases expontentially with the depth of the bisection, with a factor of 1.09493. The maximum depth is 73, and reaching it therefore requires a cumulative stake of 0.00 ETH from depth 0. Actors can participate in any challenge by calling the defend or attack functions, depending whether they agree or disagree with the latest claim and want to move the bisection game forward. Actors that disagree with the top-level claim are called challengers, and actors that agree are called defenders. Each actor might be involved in multiple (sub-)challenges at the same time, meaning that the protocol operates with full concurrency. Challengers and defenders alternate in the bisection game, and they pass each other a clock that starts with 3d 12h. If a clock expires, the claim is considered defeated if it was countered, or it gets confirmed if uncountered. Since honest parties can inherit clocks from malicious parties that play both as challengers and defenders (see freeloader claims), if a clock gets inherited with less than 3h, it generally gets extended by 3h with the exception of 6h right before depth 30, and 1d right before the last depth. The maximum clock extension that a top level claim can get is therefore 10d. Since unconfirmed state roots are independent of one another, users can decide to exit with a subsequent confirmed state root if the previous one is delayed. Winners get the entire losers’ stake, meaning that sybils can potentially play against each other at no cost. The final instruction found via the bisection game is then executed onchain in the MIPS one step prover contract who determines the winner. The protocol does not enforce valid bisections, meaning that actors can propose correct initial claims and then provide incorrect midpoints. The protocol can be subject to resource exhaustion attacks (Spearbit 5.1.3).
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2026 May 15, 13:08 UTC6changesScheduled signer-key rotation on shared OP Stack governance contracts (no threshold or permission changes): - DeputyPauseModule ( 0x76fC2F971FB355D0453cF9F64d3F9E4f640E1754 ): deputy rotated from 0x352f1defB49718e7Ea411687E850aA8d6299F7aC to 0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c . Executed via superchain-ops eth/052; the DeputyPauseModule spec specifies that this is a regular rotation. - OpFoundationUpgradeSafe: Member rotated.
Scheduled signer-key rotation on shared OP Stack governance contracts (no threshold or permission changes):
- DeputyPauseModule (
0x76fC2F971FB355D0453cF9F64d3F9E4f640E1754):deputyrotated from0x352f1defB49718e7Ea411687E850aA8d6299F7aCto0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c. Executed via superchain-ops eth/052; the DeputyPauseModule spec specifies that this is a regular rotation. - OpFoundationUpgradeSafe: Member rotated.
| contract DeputyPauseModule (eth:0x76fC2F971FB355D0453cF9F64d3F9E4f640E1754) [opstack/DeputyPauseModule] { | |
| +++ description: Allows eth:0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c, called the deputy pauser, to act on behalf of the eth:0x847B5c174615B1B7fDF770882256e2D3E95b9D92 if set as its Safe module. | |
| description: | |
| - | "Allows eth:0x352f1defB49718e7Ea411687E850aA8d6299F7aC, called the deputy pauser, to act on behalf of the eth:0x847B5c174615B1B7fDF770882256e2D3E95b9D92 if set as its Safe module." |
| + | "Allows eth:0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c, called the deputy pauser, to act on behalf of the eth:0x847B5c174615B1B7fDF770882256e2D3E95b9D92 if set as its Safe module." |
| values.deputy: | |
| - | "eth:0x352f1defB49718e7Ea411687E850aA8d6299F7aC" |
| + | "eth:0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c" |
| } |
| contract OpFoundationUpgradeSafe (eth:0x847B5c174615B1B7fDF770882256e2D3E95b9D92) [GnosisSafe] { | |
| +++ description: None | |
| values.$members.6: | |
| - | "eth:0xc222ab08333109243B1f4E2a80e3D0A190714AB5" |
| + | "eth:0xa2A58E31C03C59e34ab4d996d811DA0C035BfDea" |
| } |
2026 May 05, 15:18 UTC2changesOptimism Security Council ( eth:0xc2819DC7... ) — member 12 swap: 0x92827223 → 0xcbC7dCeb . Shared multisig (referenced by multiple Superchain projects).
Optimism Security Council (eth:0xc2819DC7...) — member 12 swap: 0x92827223 → 0xcbC7dCeb. Shared multisig (referenced by multiple Superchain projects).
| contract Optimism Security Council (eth:0xc2819DC788505Aac350142A7A707BF9D03E3Bd03) { | |
| +++ description: None | |
| values.$members.12: | |
| - | "eth:0x92827223f6b397CE9F208eE352bacA710765cACb" |
| + | "eth:0xcbC7dCeb857F0b25523618cCa0A03c419a6d7eA6" |
| } |
2026 March 25, 10:05 UTC7changesThree signers of the shared OpFoundation multisigs (OpFoundationUpgradeSafe) were rotated. The old signer at position 0 was a GnosisSafe (0x42d27eEA1AD6e22Af6284F609847CB3Cd56B9c64) which was replaced by a new EOA.
Three signers of the shared OpFoundation multisigs (OpFoundationUpgradeSafe) were rotated. The old signer at position 0 was a GnosisSafe (0x42d27eEA1AD6e22Af6284F609847CB3Cd56B9c64) which was replaced by a new EOA.
| - | Status: DELETED |
| contract GnosisSafe (eth:0x42d27eEA1AD6e22Af6284F609847CB3Cd56B9c64) | |
| +++ description: None |
| contract OpFoundationUpgradeSafe (eth:0x847B5c174615B1B7fDF770882256e2D3E95b9D92) { | |
| +++ description: None | |
| values.$members.0: | |
| - | "eth:0x42d27eEA1AD6e22Af6284F609847CB3Cd56B9c64" |
| + | "eth:0x6419F81580343DF023E68715C6e269aFb00a2cc7" |
| values.$members.2: | |
| - | "eth:0xE7dEA1306D9F829bA469d1904c50903b46ebd02e" |
| + | "eth:0xC2Db495f5a1F91172A361AAFA6FdE47c41de6dF5" |
| values.$members.6: | |
| - | "eth:0x9bbFB9919062C29a5eE15aCD93c9D7c3b14d31aa" |
| + | "eth:0xc222ab08333109243B1f4E2a80e3D0A190714AB5" |
| } |
2026 February 27, 13:19 UTC4changesOptimism Security Council: 2 members replaced.
Optimism Security Council: 2 members replaced.
| contract Optimism Security Council (eth:0xc2819DC788505Aac350142A7A707BF9D03E3Bd03) { | |
| +++ description: None | |
| values.$members.0: | |
| - | "eth:0x07dC0893cAfbF810e3E72505041f2865726Fd073" |
| + | "eth:0xE61F12136bA47De67D15a1D59fE2f383ec5176aE" |
| values.$members.2: | |
| - | "eth:0x1822b35B09f5ce1C78ecbC06AC0A4e17885b925e" |
| + | "eth:0x5c1f9E9384Ca9fE0499277F6a015a2ac0A317a81" |
| } |
2026 January 24, 16:32 UTC2changesSaferSafes module (LivenessModule + TimelockGuard) added to OpFoundationUpgradeSafe. Timelock delays currently 0.
SaferSafes module (LivenessModule + TimelockGuard) added to OpFoundationUpgradeSafe. Timelock delays currently 0.
| contract OpFoundationUpgradeSafe (eth:0x847B5c174615B1B7fDF770882256e2D3E95b9D92) { | |
| +++ description: None | |
| values.GnosisSafe_modules.0: | |
| + | "eth:0xA8447329e52F64AED2bFc9E7a2506F7D369f483a" |
| } |
| + | Status: CREATED |
| contract SaferSafes (eth:0xA8447329e52F64AED2bFc9E7a2506F7D369f483a) | |
| +++ description: A Gnosis Safe module combining LivenessModule and TimelockGuard. Provides liveness checks where a fallback owner can challenge and take over if Safe owners are unresponsive, plus optional timelock delays for transaction scheduling. |
The system has a centralized operator
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly.
Regular exits
The user initiates the withdrawal by submitting a regular transaction on this chain. When a state root containing such transaction is settled, the funds become available for withdrawal on L1 after 3d 12h. Withdrawal inclusion can be proven before state root settlement, but a 7d period has to pass before it becomes actionable. The process of state root settlement takes a challenge period of at least 3d 12h to complete. Finally the user submits an L1 transaction to claim the funds. This transaction requires a merkle proof.
Forced messaging
If the user experiences censorship from the operator with regular L2->L1 messaging they can submit their messages directly on L1. The system is then obliged to service this request or halt all messages, including forced withdrawals from L1 and regular messages initiated on L2. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular message.
EVM compatible smart contracts are supported
OP stack chains are pursuing the EVM Equivalence model. No changes to smart contracts are required regardless of the language they are written in, i.e. anything deployed on L1 can be deployed on L2.

Ethereum
Roles:
Allowed to challenge or delete state roots proposed by a Proposer.
Allowed to pause withdrawals. In op stack systems with a proof system, the Guardian can also blacklist dispute games and set the respected game type (permissioned / permissionless).
- OpFoundationUpgradeSafe has the role if the number of Optimism Security Council members falls below 8
- SaferSafes has the role if the number of Optimism Security Council members falls below 8
- Optimism EOA 1 has the role though restricted to the SuperchainConfig’s
pause()function
Allowed to post new state roots of the current layer to the host chain.
Allowed to commit transactions from the current layer to the host chain.
Actors:
A Multisig with 3/4 threshold.
- Can upgrade with no delay
- AnchorStateRegistry ProxyAdmin
- DataAvailabilityChallenge ProxyAdmin
- L1StandardBridge ProxyAdmin
- OptimismPortal2 ProxyAdmin
- L1CrossDomainMessenger ProxyAdmin
- L1ERC721Bridge ProxyAdmin
- OptimismMintableERC20Factory ProxyAdmin
- SystemConfig ProxyAdmin
- DelayedWETH ProxyAdmin
- DisputeGameFactory ProxyAdmin
- Can interact with AddressManager
- set and change address mappings ProxyAdmin
- Can interact with DelayedWETH
- can pull funds from the contract in case of emergency
A Multisig with 5/7 threshold. It uses the following modules: SaferSafes (A Gnosis Safe module combining LivenessModule and TimelockGuard. Provides liveness checks where a fallback owner can challenge and take over if Safe owners are unresponsive, plus optional timelock delays for transaction scheduling). Member of SuperchainProxyAdminOwner.
- A Guardian LivenessModule if the number of Optimism Security Council members falls below 8 → Optimism Security Council → Optimism Guardian Multisig
A Gnosis Safe module combining LivenessModule and TimelockGuard. Provides liveness checks where a fallback owner can challenge and take over if Safe owners are unresponsive, plus optional timelock delays for transaction scheduling.
- A Guardian OpFoundationUpgradeSafe → LivenessModule if the number of Optimism Security Council members falls below 8 → Optimism Security Council → Optimism Guardian Multisig
A Multisig with 10/13 threshold. It uses the following modules: LivenessModule (used to remove members inactive for 3mo 8d while making sure that the threshold remains above 75%. If the number of members falls below 8, the OpFoundationUpgradeSafe takes ownership of the multisig). Member of Optimism Guardian Multisig, SuperchainProxyAdminOwner.
- A Guardian Optimism Guardian Multisig
Participants (13):
0xE61F…76aE0x652B…cB5f0x5c1f…7a810x4A73…e61E0x3A53…aa940xEF9A…877c0x6323…c8650xd5b7…aC900x7ed8…9E390x0aA3…75D70x0a87…efE60xbfA0…E0d90xcbC7…7eA6A Multisig with 2/2 threshold.
- Can upgrade with no delay
- SuperchainConfig SuperchainProxyAdmin
- Can interact with AddressManager
- set and change address mappings SuperchainProxyAdmin
Modular contract to be used together with the LivenessModule. Tracks liveness / activity of Safe owners.
- Can interact with LivenessModule
- can remove members of Optimism Security Council inactive for 3mo 8d
A Multisig with 1/1 threshold. It uses the following modules: DeputyPauseModule (Allows 0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c, called the deputy pauser, to act on behalf of the OpFoundationUpgradeSafe if set as its Safe module).
Participants (1):
Optimism Security Council- A Sequencer - acting directly
Member of Cyber Multisig 2.
- Can interact with DataAvailabilityChallenge
- can upgrade the parameters of DA challenges like the bond size or refund percentages, potentially making challenges infeasable or insecure
- A Guardian DeputyPauseModule though restricted to the SuperchainConfig’s
pause()function → Optimism Guardian Multisig
- A Proposer - acting directly
- A Challenger - acting directly

Ethereum
The DataAvailabilityChallenge contract is used to challenge the full availability of data behind commimted transaction data hashes. See the technology section for more details.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
- owner: EOA 2
The dispute game factory allows the creation of dispute games, used to propose state roots and eventually challenge them.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
Used to manage global configuration values for multiple OP Chains within a single Superchain network. The SuperchainConfig contract manages individual pause states for each chain connected to it, as well as a global pause state for all chains. The guardian role can pause either separately, but each pause expires after 3 months if left untouched.
- Roles:
- admin: SuperchainProxyAdmin; ultimately SuperchainProxyAdminOwner
- guardian: Optimism Guardian Multisig; ultimately OpFoundationUpgradeSafe, Optimism EOA 1, Optimism Security Council, SaferSafes
The main entry point to deposit ERC20 tokens from host chain to this chain.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
All supported tokens in this escrow are included in the value secured calculation.
Sends messages from host chain to this chain, and relays messages back onto host chain. In the event that a message sent from host chain to this chain is rejected for exceeding this chain’s epoch gas limit, it can be resubmitted via this contract’s replay function.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
Used to bridge ERC-721 tokens from host chain to this chain.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
used to remove members inactive for 3mo 8d while making sure that the threshold remains above 75%. If the number of members falls below 8, the OpFoundationUpgradeSafe takes ownership of the multisig
- Roles:
- fallbackOwner: OpFoundationUpgradeSafe if the number of Optimism Security Council members falls below 8
- livenessGuard: LivenessGuard
Contains the latest confirmed state root that can be used as a starting point in a dispute game.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
A helper contract that generates OptimismMintableERC20 contracts on the network it’s deployed to. OptimismMintableERC20 is a standard extension of the base ERC20 token contract designed to allow the L1StandardBridge contracts to mint and burn tokens. This makes it possible to use an OptimismMintableERC20 as this chain’s representation of a token on the host chain, or vice-versa.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
The MIPS contract is used to execute the final step of the dispute game which objectively determines the winner of the dispute.
Contract designed to hold the bonded ETH for each game. It is designed as a wrapper around WETH to allow an owner to function as a backstop if a game would incorrectly distribute funds.
- Roles:
- admin: ProxyAdmin; ultimately Cyber Multisig 1
- owner: Cyber Multisig 1
Allows 0x2fA150379bF32b6d79Eeb4ff9bD280E76049a87c, called the deputy pauser, to act on behalf of the OpFoundationUpgradeSafe if set as its Safe module.
- Roles:
- deputy: Optimism EOA 1 though restricted to the SuperchainConfig’s
pause()function
- deputy: Optimism EOA 1 though restricted to the SuperchainConfig’s
- Roles:
- owner: Cyber Multisig 1
The PreimageOracle contract is used to load the required data from L1 for a dispute game.
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).