Search
Search for projects by name or address
 Loopring
Loopring
Badges
About
Loopring is a ZK Rollup exchange protocol for trading and payments.
Badges
About
Loopring is a ZK Rollup exchange protocol for trading and payments.
2025 May 23 — 2026 May 23
The section shows the operating costs that L2s pay to Ethereum.
2025 May 23 — 2026 May 23
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
DeFi Port is Live on Loopring
2022 Sep 27th
Dutch auctions, lending, and other DeFi functions can be performed on Loopring.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
Users can force the sequencer to include a withdrawal transaction by submitting a request through L1 with a 0.02 ETH fee. If the sequencer is down for more than 15d, users can use the exit hatch to withdraw their funds. The sequencer can censor individual deposits, but in such case after 15d users can get their funds back.
SNARKs are succinct zero knowledge proofs that ensure state correctness, but require trusted setup.
All of the data needed for proof construction is published on Ethereum L1.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Users are able to trustlessly exit by submitting a Merkle proof of funds.
Rollup operators cannot compromise the system, but being application-specific might bring additional risk.
Loopring provides an orderbook decentralized exchange for spot trading. Arbitrary contracts are not supported.
All data required for proofs is published onchain
All the data that is used to construct the system state is published onchain in the form of cheap calldata. This ensures that it will always be available when needed.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
Funds can be lost if the proof system is implemented incorrectly.
Groth16 requires a circuit specific trusted setup, so they run their own ceremony. The first phase is run using Powers of Tau ceremony. Some of the instructions on how to regenerate the verification keys can be found here.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
The system has a centralized operator
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force exit the system
Force exit allows the users to escape censorship by withdrawing their funds. The system allows users to force the withdrawal of funds by submitting a request directly to the contract onchain. The request must be served within a defined time period. If this does not happen, the system will halt regular operation and permit trustless withdrawal of funds.
Users can be censored if the operator refuses to include their transactions. However, there exists a mechanism to independently exit the system.
Forced exit
If the user experiences censorship from the operator with regular exit they can submit their withdrawal requests directly on L1. The system is then obliged to service this request. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular exit.
Emergency exit
If the 15d deadline passes and the forced exit is still ignored the user can put the system into Withdrawal Mode, disallowing further state updates. In that case everybody can withdraw by submitting a merkle proof of their funds with their L1 transaction.

Ethereum
Actors:
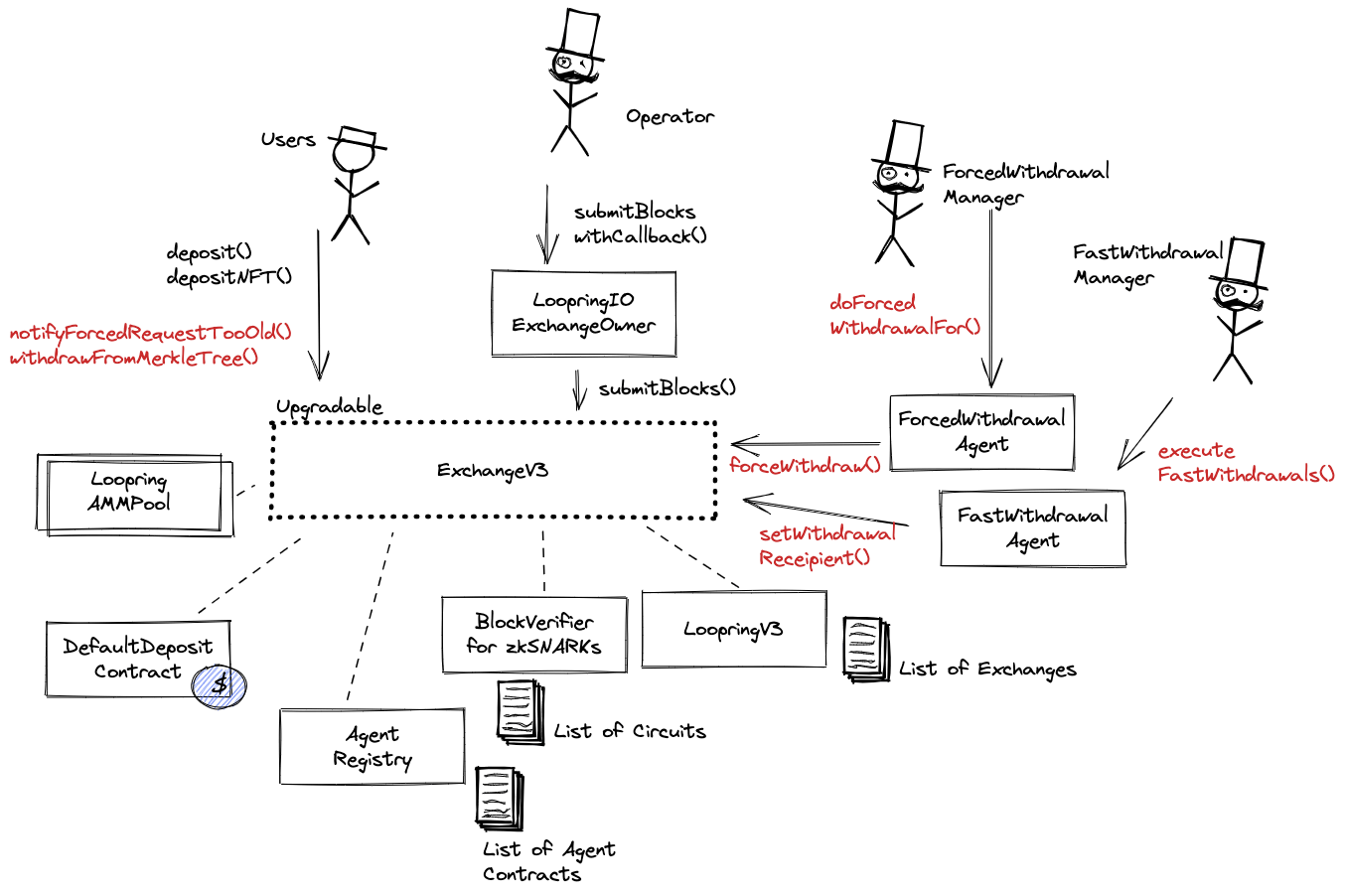
A Multisig with 2/3 threshold. This address is the owner of the following contracts: LoopringIOExchangeOwner, ExchangeV3 (proxy), BlockVerifier, AgentRegistry, LoopringV3. This allows it to grant access to submitting blocks, arbitrarily change the forced withdrawal fee, change the Verifier address and upgrade ExchangeV3 implementation potentially gaining access to all funds in DefaultDepositContract.

Ethereum
Main Loopring contract.
ERC 20 token basic deposit contract. Handles user deposits and withdrawals.
Contract managing LRC staking for exchanges (one Loopring contract can manage many exchanges). It also allows to change the forced withdrawal fee and the Verifier address.
Auxiliary contract allowing users to process fast withdrawals.
Auxiliary contract able to force withdrawals from L1 on behalf of users.
Agent registry that is used by all other Loopring contracts. Currently used are FastWithdrawalAgent, ForcedWithdrawalAgent, DestroyableWalletAgent and a number of LoopringAmmPool contracts.
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).