Search
Search for projects by name or address
 Linea
Linea
Badges
About
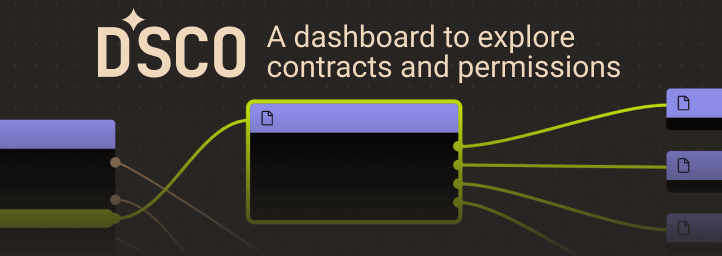
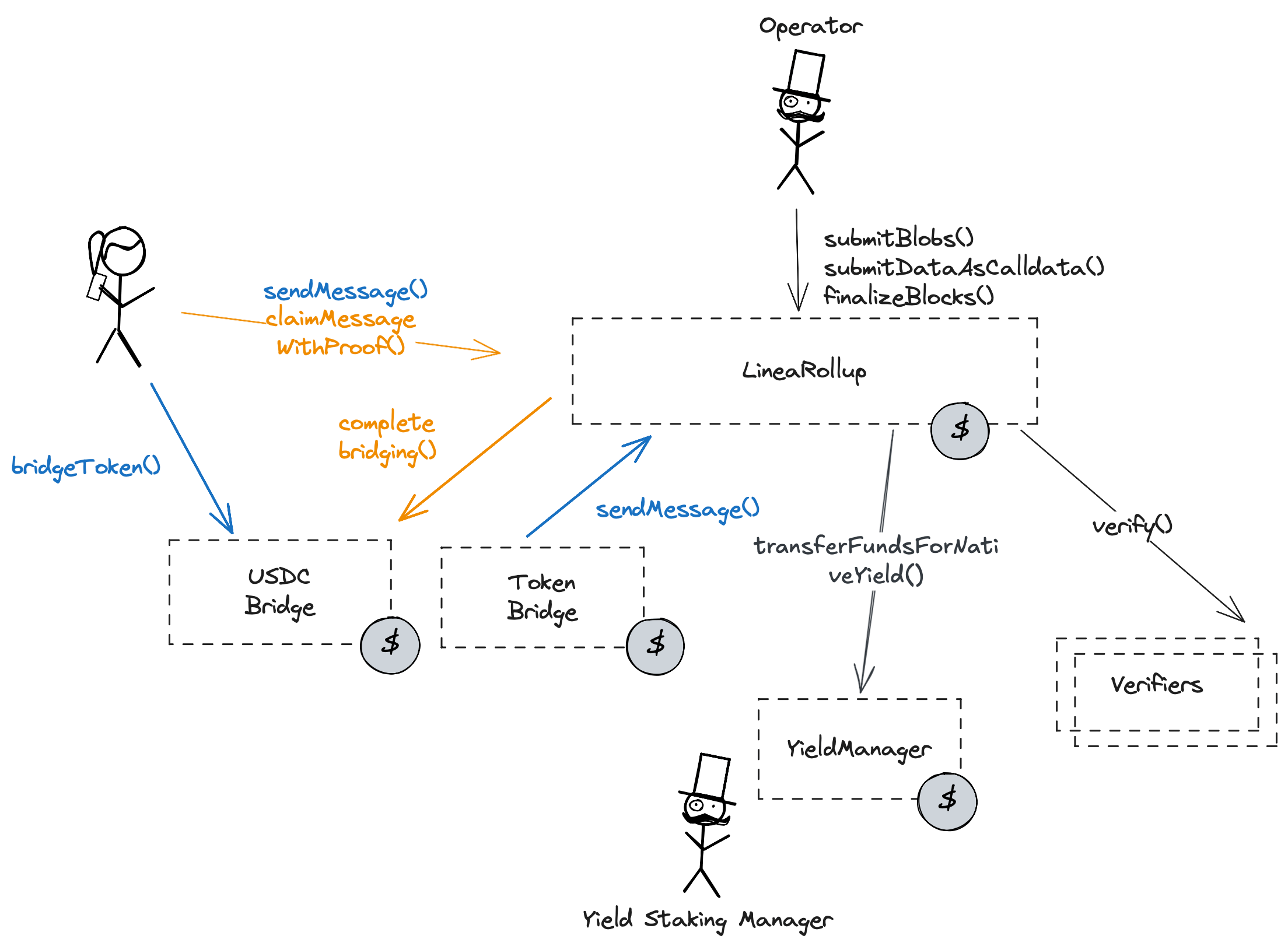
Linea is a ZK Rollup powered by a zkEVM developed at Consensys, designed to scale the Ethereum network.
Badges
About
Linea is a ZK Rollup powered by a zkEVM developed at Consensys, designed to scale the Ethereum network.
2025 Jun 11 — 2026 Jun 11
The section shows the operating costs that L2s pay to Ethereum.
2025 Jun 11 — 2026 Jun 11
This section shows how much data the project publishes to its data-availability (DA) layer over time. The project currently posts data to![]() Ethereum.
Ethereum.
2025 Jun 11 — 2026 Jun 11
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
2026 May 12 — Jun 11
Proof system is complete
2024 Jun 9th
The Linea proof system and verifier on ethereum covers 100% of the zkEVM.
Funds can be stolen if
Funds can be frozen if
Users can be censored if
MEV can be extracted if
SNARKs are succinct zero knowledge proofs that ensure state correctness, but require trusted setup.
All of the data needed for proof construction is published on Ethereum L1. Unlike most ZK rollups, transaction data is posted instead of state diffs.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Only the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen. Eventually (after 6 months of no finalized blocks) the Operator role becomes public, theoretically allowing anyone to propose state with valid proofs.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap blobs or calldata. This ensures that it will be available for enough time.
The node software (Linea Besu) and a guide to reconstruct the state from L1 is available here. Other node implementations like Nethermind, Geth or Erigon can sync too, but state derivation from L1 and Linea-specific features are unsupported.
Linea uses a bespoke lossless compression scheme based on LZSS (deflate-like). It is available as a dedicated library and a zk-decompression circuit in Gnark.
Is available via the official Linea docs for Linea Besu (preloaded), Besu, Erigon, Nethermind, Geth.
Linea groups L2 blocks into batches which are then posted to L1 for proving. Each batch (whether sent as a blob or compressed calldata) contains L2 blocks. Blocks in turn include the transactions with unnecessary data stripped. More info on the compression, packing and blob structure.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
The Linea prover code is available on Github. Linea splits proving into: Corset (Go + Lisp DSL) expands EVM execution traces and generates a bespoke constraint system for the zk-EVM. gnark (Go) ingests the expanded traces and constraint system, instantiates the circuits and produces the SNARK proof.
The constraint system lives in the public linea-constraints repo and is authored in a Lisp-style DSL before being compiled to Go. Gnark then turns those constraints into PLONK-compatible circuits over BN254. Internally, Linea’s flow uses a recursive proof stack called Vortex → Arcane → PLONK compression: Vortex/Arcane supply small inner proofs that are finally aggregated into a single PLONK proof that the L1 contract can verify.
Linea uses a Plonk-based proof system which requires a trusted setup. The verification keys are hardcoded in the verifier contract on-chain.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
Trusted Setups
Onchain verifier
Onchain verifier |
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2026 May 04, 10:44 UTCHigh severity29changesUpgraded Linea SC to Safe v1.4.1: https://github.com/safe-fndn/safe-smart-account/blob/release/v1.4.1/contracts/Safe.sol, upgraded Linea Multisig 3 to SafeL2 v1.4.1: https://github.com/safe-fndn/safe-smart-account/blob/release/v1.4.1/contracts/SafeL2.sol. Adjusted targetWithdrawalReservePercentageBps yield parameter, reduced the total amount of ether that can leave L2MessageService on Linea L2 per day.
Upgraded Linea SC to Safe v1.4.1: https://github.com/safe-fndn/safe-smart-account/blob/release/v1.4.1/contracts/Safe.sol, upgraded Linea Multisig 3 to SafeL2 v1.4.1: https://github.com/safe-fndn/safe-smart-account/blob/release/v1.4.1/contracts/SafeL2.sol.
Adjusted targetWithdrawalReservePercentageBps yield parameter, reduced the total amount of ether that can leave L2MessageService on Linea L2 per day.
| contract Linea Security Council (eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3) { | |
| +++ description: None | |
| sourceHashes.1: | |
| - | "0xd42bbf9f7dcd3720a7fc6bdc6edfdfae8800a37d6dd4decfa0ef6ca4a2e88940" |
| + | "0x7d388119a66f3eae147d748f86136f073d907d6b36f7e87e9363c4c7a2899a8a" |
| values.$implementation: | |
| - | "eth:0xd9Db270c1B5E3Bd161E8c8503c55cEABeE709552" |
| + | "eth:0x41675C099F32341bf84BFc5382aF534df5C7461a" |
| values.$members.1: | |
| - | "eth:0x497515578b0BE54d2f0f32cF3F08B85Bf8cEB6aB" |
| + | "eth:0xD6481cC92eD746EbC679788654723Ce49D45EbeA" |
| values.$members.7: | |
| - | "eth:0x99234cd9B532F30538ac797D33c212e3B69Fd087" |
| + | "eth:0x0F4df4939a6B126a088A40B4Bbf9F30337ACBFE4" |
| values.VERSION: | |
| - | "1.3.0" |
| + | "1.4.1" |
| implementationNames.eth:0xd9Db270c1B5E3Bd161E8c8503c55cEABeE709552: | |
| - | "GnosisSafe" |
| implementationNames.eth:0x41675C099F32341bf84BFc5382aF534df5C7461a: | |
| + | "Safe" |
| } |
| contract YieldManager (eth:0xeb63cABDd78537b9b72A2AFB573F7caa91bd8D94) { | |
| +++ description: Manages flows of ETH and staked ETH in and out of rollup contract reserves. Tracks the available ETH balance for L2 exits, configures target parameters for amount of staked ETH, communicates with yield provider adaptors. | |
| +++ description: Value relative to TVS, part of the computation of target rollup ETH reserve. | |
| values.targetWithdrawalReservePercentageBps: | |
| - | 9980 |
| + | 9888 |
| } |
| contract L2MessageService (linea:0x508Ca82Df566dCD1B0DE8296e70a96332cD644ec) { | |
| +++ description: None | |
| +++ description: The cap on the total amount of ether that can leave the contract via L1 -> L2 message claims per period given by periodInSeconds. | |
| values.limitInWei: | |
| - | "24000000000000000000000" |
| + | "8000000000000000000000" |
| } |
| contract Linea Multisig 3 (linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD) { | |
| +++ description: None | |
| sourceHashes.1: | |
| - | "0x59fe14e95a8aa7f52213f18bae5c9329cf583a7ba31194698b15eddb97d5e825" |
| + | "0x618c83d2fbbe19fd6f2d6ee6ee79a60e6206e48bf361eaf4812e1c1fc14b4527" |
| values.$implementation: | |
| - | "linea:0x3E5c63644E683549055b9Be8653de26E0B4CD36E" |
| + | "linea:0x29fcB43b46531BcA003ddC8FCB67FFE91900C762" |
| values.$members.2: | |
| - | "linea:0x497515578b0BE54d2f0f32cF3F08B85Bf8cEB6aB" |
| + | "linea:0xD6481cC92eD746EbC679788654723Ce49D45EbeA" |
| values.$members.8: | |
| - | "linea:0x99234cd9B532F30538ac797D33c212e3B69Fd087" |
| + | "linea:0x0F4df4939a6B126a088A40B4Bbf9F30337ACBFE4" |
| values.VERSION: | |
| - | "1.3.0" |
| + | "1.4.1" |
| implementationNames.linea:0x3E5c63644E683549055b9Be8653de26E0B4CD36E: | |
| - | "GnosisSafeL2" |
| implementationNames.linea:0x29fcB43b46531BcA003ddC8FCB67FFE91900C762: | |
| + | "SafeL2" |
| } |
| + | Status: CREATED |
| contract Safe (eth:0xD6481cC92eD746EbC679788654723Ce49D45EbeA) | |
| +++ description: None |
2026 April 22, 11:30 UTC8changesProver upgraded to the new version. I have regenerated it from the sources.
Prover upgraded to the new version. I have regenerated it from the sources.
| - | Status: DELETED |
| contract PlonkVerifierMainnetFull (eth:0xC83ed08E2262fBa264D528C749c051f8fC526897) | |
| +++ description: None |
| contract LineaRollup (eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F) { | |
| +++ description: The main contract of the Linea zkEVM rollup. Contains state roots, the verifier addresses and manages messages between L1 and the L2. ETH deployed to the rollup contract can be transfered to a yield protocol. | |
| +++ description: The cap on the total amount of ether that can leave rollup contract via L2 -> L1 message claims per period given by periodInSeconds. | |
| values.limitInWei: | |
| - | "30000000000000000000000" |
| + | "10000000000000000000000" |
| +++ description: Mapping of proof type to ZK Plonk Verifier contract. | |
| values.verifiers.0: | |
| - | "eth:0xC83ed08E2262fBa264D528C749c051f8fC526897" |
| + | "eth:0x218C3339ff3fea595c02Ac31Ca8A782f5028C4dc" |
| } |
| contract YieldManager (eth:0xeb63cABDd78537b9b72A2AFB573F7caa91bd8D94) { | |
| +++ description: Manages flows of ETH and staked ETH in and out of rollup contract reserves. Tracks the available ETH balance for L2 exits, configures target parameters for amount of staked ETH, communicates with yield provider adaptors. | |
| +++ description: Value relative to TVS, part of the computation of target rollup ETH reserve. | |
| values.targetWithdrawalReservePercentageBps: | |
| - | 9985 |
| + | 9980 |
| } |
| + | Status: CREATED |
| contract PlonkVerifierFull (eth:0x218C3339ff3fea595c02Ac31Ca8A782f5028C4dc) | |
| +++ description: None |
2026 April 20, 11:14 UTCHigh severity4changesAdded Lido yield provider for Linea native yield. Currently there is total of 1 ETH (exactly) deployed via Lido Yield Provider, the contracts are fully ready for wider usage of the yield feature.
Added Lido yield provider for Linea native yield. Currently there is total of 1 ETH (exactly) deployed via Lido Yield Provider, the contracts are fully ready for wider usage of the yield feature.
| contract YieldManager (eth:0xeb63cABDd78537b9b72A2AFB573F7caa91bd8D94) { | |
| +++ description: Manages flows of ETH and staked ETH in and out of rollup contract reserves. Tracks the available ETH balance for L2 exits, configures target parameters for amount of staked ETH, communicates with yield provider adaptors. | |
| values.yieldProviderByIndex.0: | |
| + | "eth:0x486D8cADc10489B30b64c890aEc747F1220eEEC3" |
| +++ severity: HIGH | |
| values.yieldProviderCount: | |
| - | 0 |
| + | 1 |
| } |
| + | Status: CREATED |
| contract LidoStVaultYieldProvider (eth:0x486D8cADc10489B30b64c890aEc747F1220eEEC3) | |
| +++ description: None |
2026 April 07, 11:26 UTC4changesUpdated Type 1 verifier to a new version. Chain config is the same as the previous verifier.
Updated Type 1 verifier to a new version. Chain config is the same as the previous verifier.
| - | Status: DELETED |
| contract PlonkVerifierFull (eth:0x1442833180e253844897339aFb5800c797547987) | |
| +++ description: None |
| contract LineaRollup (eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F) { | |
| +++ description: The main contract of the Linea zkEVM rollup. Contains state roots, the verifier addresses and manages messages between L1 and the L2. ETH deployed to the rollup contract can be transfered to a yield protocol. | |
| +++ description: Mapping of proof type to ZK Plonk Verifier contract. | |
| values.verifiers.1: | |
| - | "eth:0x1442833180e253844897339aFb5800c797547987" |
| + | "eth:0x0D0f070386edC441A63fB8FAe8FB937Bbd88c5Cb" |
| } |
| + | Status: CREATED |
| contract PlonkVerifierFull (eth:0x0D0f070386edC441A63fB8FAe8FB937Bbd88c5Cb) | |
| +++ description: None |
2026 April 01, 09:58 UTCHigh severity188changesUpgraded Rollup contract: https://disco.l2beat.com/diff/eth:0x04728BF704a716C26F9EF4085013b760AC885631/eth:0xE68697690E8ff196A6aBB3E1385156D87Df85332. Changes: - SC can pause indefinitely now, other entities for 48 hours with a 48 hour cooldown afterwards. - Refactored Fallback Operator to Liveness Recovery Operator address that gets OPERATOR ROLE after 6 months of non-finalization. - Refactored querying shnarf (blob commitment) existence into a separate interface. - Added chain configuration to verifier smart contract. - Refactored transient storage and calling keccak. Also upgraded TokenBridge contract (on L1 and L2): https://disco.l2beat.com/diff/eth:0x2B6A2F8880220a66DfB9059FCB76F7dB54104a34/eth:0xF0e003F0dE2d583Ae28FA8cBF66aa096CdAce3ff and L2MessageService on L2 (https://disco.l2beat.com/diff/linea:0x05d43713B7E333d2D54be65cE3b5F3698aB960Fd/linea:0x9976fD7edDb78156a002DE74c9158E884702273d) They have similar changes: - SC can pause indefinitely now, other entities for 48 hours with a 48 hour cooldown afterwards. - Refactored transient storage and calling keccak.
Upgraded Rollup contract: https://disco.l2beat.com/diff/eth:0x04728BF704a716C26F9EF4085013b760AC885631/eth:0xE68697690E8ff196A6aBB3E1385156D87Df85332. Changes:
- SC can pause indefinitely now, other entities for 48 hours with a 48 hour cooldown afterwards.
- Refactored Fallback Operator to Liveness Recovery Operator address that gets OPERATOR_ROLE after 6 months of non-finalization.
- Refactored querying shnarf (blob commitment) existence into a separate interface.
- Added chain configuration to verifier smart contract.
- Refactored transient storage and calling keccak.
Also upgraded TokenBridge contract (on L1 and L2): https://disco.l2beat.com/diff/eth:0x2B6A2F8880220a66DfB9059FCB76F7dB54104a34/eth:0xF0e003F0dE2d583Ae28FA8cBF66aa096CdAce3ff and L2MessageService on L2 (https://disco.l2beat.com/diff/linea:0x05d43713B7E333d2D54be65cE3b5F3698aB960Fd/linea:0x9976fD7edDb78156a002DE74c9158E884702273d) They have similar changes:
- SC can pause indefinitely now, other entities for 48 hours with a 48 hour cooldown afterwards.
- Refactored transient storage and calling keccak.
| contract TokenBridge (eth:0x051F1D88f0aF5763fB888eC4378b4D8B29ea3319) { | |
| +++ description: Contract used to bridge and escrow ERC-20 tokens. | |
| template: | |
| - | "linea/L1TokenBridge" |
| + | "linea/L1TokenBridge_v1_1" |
| sourceHashes.1: | |
| - | "0x49bdbe79d2cc9cefee03245e4b48260f4a71e7976af51741005758e7236d687d" |
| + | "0x9ef484e431e7c68a8c882205b5bfa7b266f67c9c5423cf7ac480938a86c78c23" |
| values.$implementation: | |
| - | "eth:0x2B6A2F8880220a66DfB9059FCB76F7dB54104a34" |
| + | "eth:0xF0e003F0dE2d583Ae28FA8cBF66aa096CdAce3ff" |
| values.$pastUpgrades.3: | |
| + | ["2026-03-31T15:26:47.000Z","0x2956910285297bc330ad8b1e31f6dd7866e58c26164fe126f09a44df6a65ce9b",["eth:0xF0e003F0dE2d583Ae28FA8cBF66aa096CdAce3ff"]] |
| values.$upgradeCount: | |
| - | 3 |
| + | 4 |
| values.accessControl.PAUSE_ALL_ROLE.members.1: | |
| + | "eth:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0" |
| values.accessControl.SET_REMOTE_TOKENBRIDGE_ROLE: | |
| - | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.0xbf094fe3c005c553ff0d33c7dff9d1273add12fb3f258b992f8d36224dd35b24: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.SECURITY_COUNCIL_ROLE: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.allPausers.1: | |
| + | "eth:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0" |
| values.CONTRACT_VERSION: | |
| - | "1.0" |
| + | "1.1" |
| values.isPaused_BLOB_SUBMISSION: | |
| - | false |
| values.isPaused_CALLDATA_SUBMISSION: | |
| - | false |
| values.remoteTokenBridgeSetters: | |
| - | ["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"] |
| values.SET_REMOTE_TOKENBRIDGE_ROLE: | |
| - | "0xbf094fe3c005c553ff0d33c7dff9d1273add12fb3f258b992f8d36224dd35b24" |
| values.COOLDOWN_DURATION: | |
| + | 172800 |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_REPORTING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_STAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_STATE_DATA_SUBMISSION: | |
| + | false |
| +++ description: Timestamp until which non security council entities can't pause the rollup. | |
| +++ severity: HIGH | |
| values.nonSecurityCouncilCooldownEnd: | |
| + | 0 |
| values.PAUSE_DURATION: | |
| + | 172800 |
| values.SECURITY_COUNCIL_ROLE: | |
| + | "0x1453a531db80c85f2d944d498709d84959bc5bf839eefe9acb784571e5a32118" |
| errors: | |
| - | {"@template":"Processing error occurred."} |
| fieldMeta.isPaused_BLOB_SUBMISSION: | |
| - | {"severity":"HIGH"} |
| fieldMeta.isPaused_CALLDATA_SUBMISSION: | |
| - | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_STAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_REPORTING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_STATE_DATA_SUBMISSION: | |
| + | {"severity":"HIGH"} |
| fieldMeta.nonSecurityCouncilCooldownEnd: | |
| + | {"severity":"HIGH","description":"Timestamp until which non security council entities can't pause the rollup."} |
| implementationNames.eth:0x2B6A2F8880220a66DfB9059FCB76F7dB54104a34: | |
| - | "TokenBridge" |
| implementationNames.eth:0xF0e003F0dE2d583Ae28FA8cBF66aa096CdAce3ff: | |
| + | "TokenBridge" |
| } |
| contract CallForwardingProxy (eth:0x3697bD0bC6C050135b8321F989a5316eACbF367D) { | |
| +++ description: A public proxy contract forwarding calls to a predefined target contract (eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F). Can be called by any address. | |
| receivedPermissions.0.role: | |
| - | ".fallbackOperator" |
| + | ".livenessRecoveryOperator" |
| } |
| - | Status: DELETED |
| contract PlonkVerifierMainnetFull (eth:0x66355689a9f067eeb9dc9d899E4192676988279C) | |
| +++ description: None |
| contract Linea Security Council (eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3) { | |
| +++ description: None | |
| receivedPermissions.10: | |
| - | {"permission":"interact","from":"eth:0x051F1D88f0aF5763fB888eC4378b4D8B29ea3319","description":"can set the contract that is recognized to be the token bridge contract on the other side.","role":".remoteTokenBridgeSetters"} |
| receivedPermissions.17: | |
| + | {"permission":"interact","from":"eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F","description":"pause the rollup for 2d, followed by 2d cooldown, during which the rollup cannot be paused, except by the Security Council.","role":".pauseAllAC"} |
| receivedPermissions.18: | |
| + | {"permission":"interact","from":"eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F","description":"pause the rollup indefinitely.","role":".securityCouncilAC"} |
| } |
| contract LineaRollup (eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F) { | |
| +++ description: The main contract of the Linea zkEVM rollup. Contains state roots, the verifier addresses and manages messages between L1 and the L2. ETH deployed to the rollup contract can be transfered to a yield protocol. | |
| template: | |
| - | "linea/LineaRollup_NativeYield" |
| + | "linea/LineaRollup_NativeYield_v7_1" |
| sourceHashes.1: | |
| - | "0x7f1b1a08526c142b2843c2e0d1fb7d8511f9fe0da9001aa980e58eea6ddd3fb1" |
| + | "0xc79888514ff3b0780c3947bdc52c7fb27664029407ec70360023b494f725f7b3" |
| values.$implementation: | |
| - | "eth:0x04728BF704a716C26F9EF4085013b760AC885631" |
| + | "eth:0xE68697690E8ff196A6aBB3E1385156D87Df85332" |
| values.$pastUpgrades.10: | |
| + | ["2026-03-31T15:26:47.000Z","0x2956910285297bc330ad8b1e31f6dd7866e58c26164fe126f09a44df6a65ce9b",["eth:0xE68697690E8ff196A6aBB3E1385156D87Df85332"]] |
| values.$upgradeCount: | |
| - | 10 |
| + | 11 |
| values.accessControl.PAUSE_ALL_ROLE.members.1: | |
| + | "eth:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0" |
| values.accessControl.PAUSE_BLOB_SUBMISSION_ROLE: | |
| - | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.UNPAUSE_BLOB_SUBMISSION_ROLE: | |
| - | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.0x67c2dca7476ee0fe1dd3cba13428c6760bfe2599a6dfe26a9ad7ef27317c6e77: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.0xe4831f9e4316ac2c65117d1f602fbf56d38128a9973d5e3fdbc5b77265c18d40: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.SECURITY_COUNCIL_ROLE: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.PAUSE_STATE_DATA_SUBMISSION_ROLE: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.accessControl.UNPAUSE_STATE_DATA_SUBMISSION_ROLE: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"]} |
| values.CONTRACT_VERSION: | |
| - | "7.0" |
| + | "7.1" |
| values.fallbackOperator: | |
| - | "eth:0x3697bD0bC6C050135b8321F989a5316eACbF367D" |
| values.isPaused_BLOB_SUBMISSION: | |
| - | false |
| values.isPaused_CALLDATA_SUBMISSION: | |
| - | false |
| values.PAUSE_BLOB_SUBMISSION_ROLE: | |
| - | "0x67c2dca7476ee0fe1dd3cba13428c6760bfe2599a6dfe26a9ad7ef27317c6e77" |
| values.UNPAUSE_BLOB_SUBMISSION_ROLE: | |
| - | "0xe4831f9e4316ac2c65117d1f602fbf56d38128a9973d5e3fdbc5b77265c18d40" |
| +++ description: Mapping of proof type to ZK Plonk Verifier contract. | |
| values.verifiers.1: | |
| - | "eth:0x66355689a9f067eeb9dc9d899E4192676988279C" |
| + | "eth:0x1442833180e253844897339aFb5800c797547987" |
| values.COOLDOWN_DURATION: | |
| + | 172800 |
| +++ description: The duration of pausing cooldown period, for which rollup could not be paused after a previous pause. SC can always pause indefinitely. | |
| values.COOLDOWN_DURATION_fmt: | |
| + | "2d" |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_REPORTING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_STAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_STATE_DATA_SUBMISSION: | |
| + | false |
| +++ severity: HIGH | |
| values.livenessRecoveryOperator: | |
| + | "eth:0x3697bD0bC6C050135b8321F989a5316eACbF367D" |
| +++ description: Timestamp until which non security council entities can't pause the rollup. | |
| +++ severity: HIGH | |
| values.nonSecurityCouncilCooldownEnd: | |
| + | 0 |
| values.PAUSE_DURATION: | |
| + | 172800 |
| values.PAUSE_STATE_DATA_SUBMISSION_ROLE: | |
| + | "0x21aba2dd4535739d4ca4cddb3c024036bfcc88cfce067cb0847e7ad0f9cfaa55" |
| values.pauseAllAC: | |
| + | ["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3","eth:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0"] |
| +++ description: The duration of the rate limit window over which the withdrawal amounts are accumulated. | |
| values.pauseDuration_fmt: | |
| + | "2d" |
| values.SECURITY_COUNCIL_ROLE: | |
| + | "0x1453a531db80c85f2d944d498709d84959bc5bf839eefe9acb784571e5a32118" |
| values.securityCouncilAC: | |
| + | ["eth:0x892bb7EeD71efB060ab90140e7825d8127991DD3"] |
| +++ description: Smart contract that attests existence of blob commitments (shnarfs). | |
| +++ severity: HIGH | |
| values.shnarfProvider: | |
| + | "eth:0xd19d4B5d358258f05D7B411E21A1460D11B0876F" |
| values.UNPAUSE_STATE_DATA_SUBMISSION_ROLE: | |
| + | "0x4df33217c89b6f12af38ba46035cb312b5e88de78d22279286830fe079b642cd" |
| fieldMeta.isPaused_BLOB_SUBMISSION: | |
| - | {"severity":"HIGH"} |
| fieldMeta.isPaused_CALLDATA_SUBMISSION: | |
| - | {"severity":"HIGH"} |
| fieldMeta.periodInSeconds: | |
| - | {"description":"The duration of the rate limit window over which the withdrawal amounts are accumulated."} |
| fieldMeta.livenessRecoveryOperator: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_STAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_REPORTING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_STATE_DATA_SUBMISSION: | |
| + | {"severity":"HIGH"} |
| fieldMeta.pauseDuration_fmt: | |
| + | {"description":"The duration of the rate limit window over which the withdrawal amounts are accumulated."} |
| fieldMeta.COOLDOWN_DURATION_fmt: | |
| + | {"description":"The duration of pausing cooldown period, for which rollup could not be paused after a previous pause. SC can always pause indefinitely."} |
| fieldMeta.shnarfProvider: | |
| + | {"severity":"HIGH","description":"Smart contract that attests existence of blob commitments (shnarfs)."} |
| fieldMeta.nonSecurityCouncilCooldownEnd: | |
| + | {"severity":"HIGH","description":"Timestamp until which non security council entities can't pause the rollup."} |
| implementationNames.eth:0x04728BF704a716C26F9EF4085013b760AC885631: | |
| - | "LineaRollup" |
| implementationNames.eth:0xE68697690E8ff196A6aBB3E1385156D87Df85332: | |
| + | "LineaRollup" |
| } |
| contract TokenBridge (linea:0x353012dc4a9A6cF55c941bADC267f82004A8ceB9) { | |
| +++ description: Contract used to bridge and escrow ERC-20 tokens. | |
| template: | |
| - | "linea/L1TokenBridge" |
| + | "linea/L1TokenBridge_v1_1" |
| sourceHashes.1: | |
| - | "0x49bdbe79d2cc9cefee03245e4b48260f4a71e7976af51741005758e7236d687d" |
| + | "0x9ef484e431e7c68a8c882205b5bfa7b266f67c9c5423cf7ac480938a86c78c23" |
| values.$implementation: | |
| - | "linea:0xD90ed3D4f9d11262d3D346a4369058d5B3777137" |
| + | "linea:0x4a496167F187A97379e763f693A499cE1182848b" |
| values.$pastUpgrades.3: | |
| + | ["2026-03-31T15:28:55.000Z","0xee1773eabf52589c20884aceed118949ea8e03afc7bfd1df008206d2d69e1b01",["linea:0x4a496167F187A97379e763f693A499cE1182848b"]] |
| values.$upgradeCount: | |
| - | 3 |
| + | 4 |
| values.accessControl.PAUSE_ALL_ROLE.members.1: | |
| + | "linea:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0" |
| values.accessControl.SET_REMOTE_TOKENBRIDGE_ROLE: | |
| - | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD"]} |
| values.accessControl.0xbf094fe3c005c553ff0d33c7dff9d1273add12fb3f258b992f8d36224dd35b24: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD"]} |
| values.accessControl.SECURITY_COUNCIL_ROLE: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD"]} |
| values.allPausers.1: | |
| + | "linea:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0" |
| values.CONTRACT_VERSION: | |
| - | "1.0" |
| + | "1.1" |
| values.isPaused_BLOB_SUBMISSION: | |
| - | false |
| values.isPaused_CALLDATA_SUBMISSION: | |
| - | false |
| values.remoteTokenBridgeSetters: | |
| - | ["linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD"] |
| values.SET_REMOTE_TOKENBRIDGE_ROLE: | |
| - | "0xbf094fe3c005c553ff0d33c7dff9d1273add12fb3f258b992f8d36224dd35b24" |
| values.COOLDOWN_DURATION: | |
| + | 172800 |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_REPORTING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_STAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_STATE_DATA_SUBMISSION: | |
| + | false |
| +++ description: Timestamp until which non security council entities can't pause the rollup. | |
| +++ severity: HIGH | |
| values.nonSecurityCouncilCooldownEnd: | |
| + | 0 |
| values.PAUSE_DURATION: | |
| + | 172800 |
| values.SECURITY_COUNCIL_ROLE: | |
| + | "0x1453a531db80c85f2d944d498709d84959bc5bf839eefe9acb784571e5a32118" |
| errors: | |
| - | {"@template":"Processing error occurred."} |
| fieldMeta.isPaused_BLOB_SUBMISSION: | |
| - | {"severity":"HIGH"} |
| fieldMeta.isPaused_CALLDATA_SUBMISSION: | |
| - | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_STAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_REPORTING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_STATE_DATA_SUBMISSION: | |
| + | {"severity":"HIGH"} |
| fieldMeta.nonSecurityCouncilCooldownEnd: | |
| + | {"severity":"HIGH","description":"Timestamp until which non security council entities can't pause the rollup."} |
| implementationNames.linea:0xD90ed3D4f9d11262d3D346a4369058d5B3777137: | |
| - | "TokenBridge" |
| implementationNames.linea:0x4a496167F187A97379e763f693A499cE1182848b: | |
| + | "TokenBridge" |
| } |
| contract L2MessageService (linea:0x508Ca82Df566dCD1B0DE8296e70a96332cD644ec) { | |
| +++ description: None | |
| template: | |
| - | "linea/L2MessageService" |
| + | "linea/L2MessageService_v1_0" |
| sourceHashes.1: | |
| - | "0x9436ff273e587ee919293672a7a5ba7bf371053a92565ee236a004932a5dda66" |
| + | "0x6239c25539f3ab00e89f637a6f0c8c125ada5ac83bb623a815236dfa315e293c" |
| values.$implementation: | |
| - | "linea:0x05d43713B7E333d2D54be65cE3b5F3698aB960Fd" |
| + | "linea:0x9976fD7edDb78156a002DE74c9158E884702273d" |
| values.$pastUpgrades.6: | |
| + | ["2026-03-31T15:28:55.000Z","0xee1773eabf52589c20884aceed118949ea8e03afc7bfd1df008206d2d69e1b01",["linea:0x9976fD7edDb78156a002DE74c9158E884702273d"]] |
| values.$upgradeCount: | |
| - | 6 |
| + | 7 |
| values.accessControl.PAUSE_ALL_ROLE.members.1: | |
| + | "linea:0x2532bfdc9Ba58B13358A9C5C05136d6938Bc42d0" |
| values.accessControl.SECURITY_COUNCIL_ROLE: | |
| + | {"adminRole":"DEFAULT_ADMIN_ROLE","members":["linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD"]} |
| +++ description: Value used to identify the crosschain caller during a crosschain call. It defaults to a inaccessible address outside of calls. | |
| values.sender: | |
| - | "linea:0x00000000000000000000000000000000075BCd15" |
| + | "linea:0x0000000000000000000000000000000000000000" |
| values.COOLDOWN_DURATION: | |
| + | 172800 |
| +++ severity: HIGH | |
| values.isPaused_COMPLETE_TOKEN_BRIDGING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_FINALIZATION: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_GENERAL: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_INITIATE_TOKEN_BRIDGING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_L1_L2: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_L2_L1: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_REPORTING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_STAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | false |
| +++ severity: HIGH | |
| values.isPaused_STATE_DATA_SUBMISSION: | |
| + | false |
| +++ description: Timestamp until which non security council entities can't pause the rollup. | |
| +++ severity: HIGH | |
| values.nonSecurityCouncilCooldownEnd: | |
| + | 0 |
| values.PAUSE_DURATION: | |
| + | 172800 |
| values.SECURITY_COUNCIL_ROLE: | |
| + | "0x1453a531db80c85f2d944d498709d84959bc5bf839eefe9acb784571e5a32118" |
| fieldMeta.isPaused_GENERAL: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_L1_L2: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_L2_L1: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_FINALIZATION: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_INITIATE_TOKEN_BRIDGING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_COMPLETE_TOKEN_BRIDGING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_STAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_UNSTAKING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_PERMISSIONLESS_ACTIONS: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_NATIVE_YIELD_REPORTING: | |
| + | {"severity":"HIGH"} |
| fieldMeta.isPaused_STATE_DATA_SUBMISSION: | |
| + | {"severity":"HIGH"} |
| fieldMeta.nonSecurityCouncilCooldownEnd: | |
| + | {"severity":"HIGH","description":"Timestamp until which non security council entities can't pause the rollup."} |
| implementationNames.linea:0x05d43713B7E333d2D54be65cE3b5F3698aB960Fd: | |
| - | "L2MessageService" |
| implementationNames.linea:0x9976fD7edDb78156a002DE74c9158E884702273d: | |
| + | "L2MessageService" |
| } |
| contract Linea Multisig 3 (linea:0xf5cc7604a5ef3565b4D2050D65729A06B68AA0bD) { | |
| +++ description: None | |
| receivedPermissions.7: | |
| - | {"permission":"interact","from":"linea:0x353012dc4a9A6cF55c941bADC267f82004A8ceB9","description":"can set the contract that is recognized to be the token bridge contract on the other side.","role":".remoteTokenBridgeSetters"} |
| } |
| + | Status: CREATED |
| contract PlonkVerifierFull (eth:0x1442833180e253844897339aFb5800c797547987) | |
| +++ description: None |
The system has a centralized sequencer
Only a trusted sequencer is allowed to submit transaction batches. A mechanism for users to submit their own batches is currently disabled.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Funds can be frozen if the sequencer refuses to include an exit transaction (CRITICAL).
Users can't force any transaction
There is no general mechanism to force the sequencer to include the transaction.
Users can be censored if the operator refuses to include their transactions.
Regular messaging
The user initiates L2->L1 messages by submitting a regular transaction on this chain. When the block containing that transaction is settled, the message becomes available for processing on L1. ZK proofs are required to settle blocks. Note that withdrawal requests can be censored by the Sequencer. Currently, there is a general limit of 10000.0 ETH that can be withdrawn within each 1d time window. Users can (eventually, after 6 months of inactivity from the centralized Operator) exit by replacing the Operator. In such a case they need to self-propose and prove their new state on the base layer with the required software which is currently not made available.
Funds can be frozen if the operator censors withdrawal transaction.

Ethereum
Actors:
A Multisig with 5/9 threshold.
- Can upgrade with no delay
- TokenBridge Timelock → ProxyAdmin
- L1USDCBridge ProxyAdmin
- LineaRollup Timelock → ProxyAdmin
- YieldManager Timelock → ProxyAdmin
- Can interact with TokenBridge
- can pause the bridge
- can pause token bridging actions initiated from the other layer
- can pause token bridging actions initiated from this layer
- can prevent tokens that have not been bridged already from being bridged by assigning them a reserved status with 3mo delay or with no delay Delay with 3mo delay → Linea Multisig 2 - or - acting directly
- can remove the reserved status from a token, meaning that it is allowed to be bridged again with 3mo delay or with no delay Delay with 3mo delay → Linea Multisig 2 - or - acting directly
- can set custom ERC20 contracts for specific ERC20s with 3mo delay or with no delay Delay with 3mo delay → Linea Multisig 2 - or - acting directly
- can set the contract used as the source of truth from crosschain messages
- can unpause token bridging actions initiated from the other layer
- can unpause token bridging actions initiated from this layer
- manage all critical access control roles and permissions (full admin of the main bridge escrow)
- Can interact with Delay
- enable/disable the module, set delays and expiration of transactions, set the target with 3mo delay Delay with 3mo delay → Linea Multisig 2
- Can interact with UpgradeableBeacon
- change the beacon implementation
- Can interact with LineaRollup
- manage all critical access control roles and permissions (full admin of the rollup system)
- pause the rollup for 2d, followed by 2d cooldown, during which the rollup cannot be paused, except by the Security Council
- pause the rollup indefinitely
- send ETH from the rollup bridge to the YieldManager
- set the address of the yield manager contract that receives ETH from rollup bridge
- Can interact with Timelock
- cancel queued transactions
- execute transactions that are ready
- manage all access control roles and change the minimum delay Timelock
- propose transactions with 3mo delay or with no delay Delay with 3mo delay → Linea Multisig 2 - or - acting directly
- Can interact with YieldManager
- manage native yield staking: modify reserve parameters, set yield pools, set yield receiver addresses
- operate native yield staking: stake and unstake, collect yield, pause and unpause, ossify yield managers
A Multisig with 3/5 threshold. It uses the following modules: Delay (A simple Safe module for that can queue and execute transactions as Linea Multisig 2 after a delay of currently 3mo, if registered as a module there).
- Can interact with TokenBridge
- can prevent tokens that have not been bridged already from being bridged by assigning them a reserved status
- can remove the reserved status from a token, meaning that it is allowed to be bridged again
- can set custom ERC20 contracts for specific ERC20s
- Can interact with Delay
- enable/disable the module, set delays and expiration of transactions, set the target
- Can interact with Timelock
- propose transactions
A Multisig with 1/4 threshold. Member of Linea Security Council.
- Can interact with TokenBridge
- can pause the bridge
- Can interact with LineaRollup
- pause the rollup for 2d, followed by 2d cooldown, during which the rollup cannot be paused, except by the Security Council
Linea
Actors:
A Multisig with 3/5 threshold.
- Can interact with TokenBridge
- can prevent tokens that have not been bridged already from being bridged by assigning them a reserved status
- can remove the reserved status from a token, meaning that it is allowed to be bridged again
- can set custom ERC20 contracts for specific ERC20s
- Can interact with L2Timelock
- propose transactions
A Multisig with 5/9 threshold. It uses the following modules: L2Roles (The Zodiac ‘Roles’ module for Safe multisigs allows defining roles that can call preconfigured targets on behalf of the Gnosis Safe).
- Can upgrade with no delay
- TokenBridge L2Timelock → ProxyAdmin
- L2MessageService L2Timelock → ProxyAdmin
- L2USDCBridge ProxyAdmin
- Can interact with TokenBridge
- can pause the bridge
- can pause token bridging actions initiated from the other layer
- can pause token bridging actions initiated from this layer
- can prevent tokens that have not been bridged already from being bridged by assigning them a reserved status
- can remove the reserved status from a token, meaning that it is allowed to be bridged again
- can set custom ERC20 contracts for specific ERC20s
- can set the contract used as the source of truth from crosschain messages
- can unpause token bridging actions initiated from the other layer
- can unpause token bridging actions initiated from this layer
- manage all critical access control roles and permissions (full admin of the main bridge escrow)
- Can interact with L2Timelock
- cancel queued transactions
- execute transactions that are ready
- manage all access control roles and change the minimum delay L2Timelock
- propose transactions
- Can interact with UpgradeableBeacon
- change the beacon implementation
- Can interact with TokenBridge
- can pause the bridge
- Can interact with L2MessageService
- Can anchor L1 data on the L2. A check is supposed to be added to the proof system on L1 so that it is not possible to settle if the anchor is not correct. The function is permissioned because otherwise anyone can cause a liveness failure by posting an invalid anchor
- Can interact with L2Roles
- can pause the L2MessageService, the TokenBridge and the L2USDCBridge
- Can interact with L2Roles
- can mint XP soulbound tokens as part of the Voyage campaign

Ethereum
Contract used to bridge and escrow ERC-20 tokens.
- Roles:
- admin: ProxyAdmin; ultimately Linea Security Council
- allPausers: EOA 1, Linea Security Council
- allUnpausers: Linea Security Council
- completeTokenBridgingPausers: Linea Security Council
- completeTokenBridgingUnpausers: Linea Security Council
- customContractSetters: Linea Multisig 2, Linea Security Council; ultimately Linea Security Council
- defaultAdmin: Linea Security Council
- initiateTokenBridgingPausers: Linea Security Council
- initiateTokenBridgingUnpausers: Linea Security Council
- messageServiceSetters: Linea Security Council
- reserveTokenRemovers: Linea Multisig 2, Linea Security Council; ultimately Linea Security Council
- reserveTokenSetters: Linea Multisig 2, Linea Security Council; ultimately Linea Security Council
All supported tokens in this escrow are included in the value secured calculation.
Standard implementation used for assets that are native to the other layer and are bridged to this layer.
- Roles:
- owner: Linea Security Council
L1 side of the old and now unused USDC bridge.
- Roles:
- admin: ProxyAdmin; ultimately Linea Security Council
A simple Safe module for that can queue and execute transactions as Linea Multisig 2 after a delay of currently 3mo, if registered as a module there.
- Roles:
- owner: Linea Multisig 2; ultimately Linea Security Council
- zodiacModule_modules: Linea Security Council
A beacon with an upgradeable implementation currently set as BridgedToken. Beacon proxy contracts pointing to this beacon will all use its implementation.
- Roles:
- owner: Linea Security Council
The main contract of the Linea zkEVM rollup. Contains state roots, the verifier addresses and manages messages between L1 and the L2. ETH deployed to the rollup contract can be transfered to a yield protocol.
- Roles:
- admin: ProxyAdmin; ultimately Linea Security Council
- defaultAdmin: Linea Security Council
- ethStaker: EOA 4, Linea Security Council
- livenessRecoveryOperator: CallForwardingProxy
- operators: EOA 2, EOA 3
- pauseAll: EOA 1, Linea Security Council
- securityCouncil: Linea Security Council
- yieldManagerSetter: Linea Security Council
A standard timelock with access control. The current minimum delay is 0s.
- Roles:
- canceller: Linea Security Council
- executor: Linea Security Council
- proposer: Linea Multisig 2, Linea Security Council; ultimately Linea Security Council
- timelockAdmin: Timelock; ultimately Linea Security Council
Manages flows of ETH and staked ETH in and out of rollup contract reserves. Tracks the available ETH balance for L2 exits, configures target parameters for amount of staked ETH, communicates with yield provider adaptors.
- Roles:
- admin: ProxyAdmin; ultimately Linea Security Council
- yieldStakingManager: Linea Security Council
- yieldStakingOperator: EOA 4, Linea Security Council
- Roles:
- owner: Timelock
Linea
- Roles:
- owner: L2Timelock
Contract used to bridge and escrow ERC-20 tokens.
- Roles:
- admin: ProxyAdmin; ultimately Linea Multisig 3
- allPausers: EOA 5, Linea Multisig 3
- allUnpausers: Linea Multisig 3
- completeTokenBridgingPausers: Linea Multisig 3
- completeTokenBridgingUnpausers: Linea Multisig 3
- customContractSetters: Linea Multisig 3, Linea Multisig 4
- defaultAdmin: Linea Multisig 3
- initiateTokenBridgingPausers: Linea Multisig 3
- initiateTokenBridgingUnpausers: Linea Multisig 3
- messageServiceSetters: Linea Multisig 3
- reserveTokenRemovers: Linea Multisig 3, Linea Multisig 4
- reserveTokenSetters: Linea Multisig 3, Linea Multisig 4
The Zodiac ‘Roles’ module for Safe multisigs allows defining roles that can call preconfigured targets on behalf of the Gnosis Safe.
- Roles:
- pausers: EOA 7
- voyageXpMinters: EOA 8
- Roles:
- admin: ProxyAdmin; ultimately Linea Multisig 3
- l1l2MessageSetter: EOA 6
A standard timelock with access control. The current minimum delay is 0s.
- Roles:
- canceller: Linea Multisig 3
- executor: Linea Multisig 3
- proposer: Linea Multisig 3, Linea Multisig 4
- timelockAdmin: L2Timelock; ultimately Linea Multisig 3
- Roles:
- owner: Linea Multisig 3
Voyage XP tokens are non-transferrable, soulbound tokens that are distributed to recognize the community’s contribution toward the growth of the Linea ecosystem.
Standard implementation used for assets that are native to the other layer and are bridged to this layer.
A beacon with an upgradeable implementation currently set as BridgedToken. Beacon proxy contracts pointing to this beacon will all use its implementation.
- Roles:
- owner: Linea Multisig 3
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 0s delay on code upgrades.