Search
Search for projects by name or address
 Morph
Morph
Badges
About
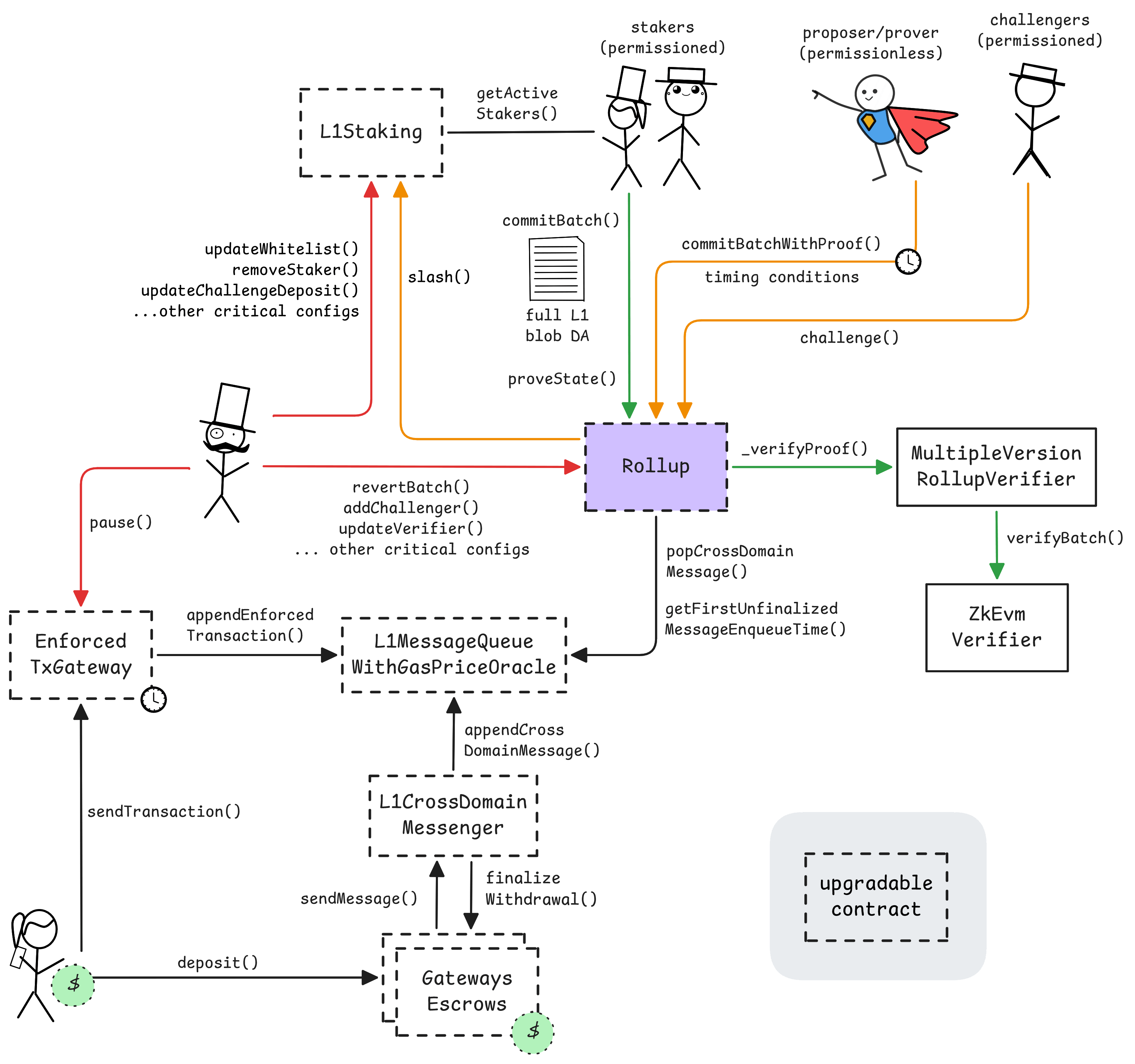
Morph is an EVM compatible rollup. It operates as an optimistic rollup with ZK fault proofs and has plans for decentralizing the Sequencer. Their mission is to build the first blockchain for consumers, where user-friendly applications integrate seamlessly... into everyday life, becoming indispensable utilities.
Badges
About
Morph is an EVM compatible rollup. It operates as an optimistic rollup with ZK fault proofs and has plans for decentralizing the Sequencer. Their mission is to build the first blockchain for consumers, where user-friendly applications integrate seamlessly... into everyday life, becoming indispensable utilities.
2025 Jun 10 — 2026 Jun 10
This section shows how much data the project publishes to its data-availability (DA) layer over time. The project currently posts data to![]() Ethereum.
Ethereum.
2025 Jun 10 — 2026 Jun 10
Fraud proofs allow actors watching the chain to prove that the state is incorrect. Single round proofs (1R) only require a single transaction to resolve. ZK proofs are used to prove the correctness of the state transition. The system currently operates with at least 5 whitelisted challengers external to the team.
All of the data needed for proof construction is published on Ethereum L1.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap blobs or calldata. This ensures that it will be available for enough time.
Morph uses a one round fault proof system where whitelisted Challengers, if they find a faulty state root within the 2d challenge window, can post a 1 WEI bond and request a ZK proof of the state transition. At least 5 Challengers are operated by entities external to the team. After the challenge, during a 3d proving window, a ZK proof must be delivered, otherwise the state root is considered invalid and the root proposer bond, which is currently set to 1 ETH, is slashed. The zkVM used is SP1 by Succinct. If a valid proof is delivered, the Challenger loses the challenge bond. The Morph Multisig can revert unfinalized batches.
Funds can be stolen if no whitelisted challenger posts a challenge for an incorrect state root.
Trusted Setups
Onchain verifier
Onchain verifier |
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2026 June 08, 10:27 UTCHigh severity15changesAdded batch data version 2: https://disco.l2beat.com/diff/eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2/eth:0xaC3C379D772f3520B34690d32BA14510ab36C3fB, which handles submitting several blobs. Also, upgraded the verifier program, which is reproducible from the sources, and completely switched to SP1 Hypercube.
Added batch data version 2: https://disco.l2beat.com/diff/eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2/eth:0xaC3C379D772f3520B34690d32BA14510ab36C3fB, which handles submitting several blobs.
Also, upgraded the verifier program, which is reproducible from the sources, and completely switched to SP1 Hypercube.
| - | Status: DELETED |
| contract ZkEvmVerifierV1 (eth:0x045d4BC73Bd1918192f34e98532A5272Ef620423) [morph/ZkEvmVerifierV1] | |
| +++ description: A snark verifier based on SP1 by Succinct. It verifies RISC-V execution in a PLONK proof. Used to verify the validity of L2 state transitions for single round fraud proofs. |
| contract MultipleVersionRollupVerifier (eth:0x5d1584c27b4aD233283c6da1ca1B825d6f220EC1) [morph/MultipleVersionRollupVerifier] { | |
| +++ description: Used to update the verifier and keep track of current and old versions. Routes to a registered verifier by batch index, so that every batch is verified by the latest verifier that is enabled for this batch. | |
| values.latestVerifier.1.verifier: | |
| - | "eth:0x045d4BC73Bd1918192f34e98532A5272Ef620423" |
| + | "eth:0xD9F24400816c4CC1a3cBb9B851C9B0bAB63Ad692" |
| values.latestVerifier.1.startBatchIndex: | |
| - | 45847 |
| + | 54332 |
| } |
| contract Rollup (eth:0x759894Ced0e6af42c26668076Ffa84d02E3CeF60) [morph/Rollup] { | |
| +++ description: The main contract of the Morph rollup. Allows to post transaction data and state roots and implements the the proof system. Sequencing and proposing are behind a whitelist. If the EnforcedTxGateway is not paused, any sequencer must include at least one L1 -> L2 message in their proposal if the oldest message is > 7d old. If the Sequencers are censoring or down for more than 7d, users can permissionlessly propose and prove via `commitBatchWithProof()`. | |
| sourceHashes.1: | |
| - | "0x744e3febdbddacbc25d9934fa259bfb08b24e38cb1325cdce9e9740b9b6f192b" |
| + | "0x9505004977004cf77ebe02c63bae0f3420673028462e69fe68350d91356eb33b" |
| values.$implementation: | |
| - | "eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2" |
| + | "eth:0xaC3C379D772f3520B34690d32BA14510ab36C3fB" |
| values.$pastUpgrades.10: | |
| + | ["2026-06-03T11:26:11.000Z","0xe9128be913e8685a928c8e8468a030a95ad44ef4ad78534c688cd721af496a54",["eth:0xaC3C379D772f3520B34690d32BA14510ab36C3fB"]] |
| values.$upgradeCount: | |
| - | 10 |
| + | 11 |
| implementationNames.eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2: | |
| - | "Rollup" |
| implementationNames.eth:0xaC3C379D772f3520B34690d32BA14510ab36C3fB: | |
| + | "Rollup" |
| } |
| + | Status: CREATED |
| contract ZkEvmVerifierV1 (eth:0xD9F24400816c4CC1a3cBb9B851C9B0bAB63Ad692) [N/A] | |
| +++ description: None |
2026 May 22, 09:45 UTC6changesUpdated morph verifier to use SP1 v6.2.0. New program that is verified.
Updated morph verifier to use SP1 v6.2.0. New program that is verified.
| - | Status: DELETED |
| contract ZkEvmVerifierV1 (eth:0x059adC0Db833f7cCb12dC41BE0017626337AfA63) [morph/ZkEvmVerifierV1] | |
| +++ description: A snark verifier based on SP1 by Succinct. It verifies RISC-V execution in a PLONK proof. Used to verify the validity of L2 state transitions for single round fraud proofs. |
| contract MultipleVersionRollupVerifier (eth:0x5d1584c27b4aD233283c6da1ca1B825d6f220EC1) [morph/MultipleVersionRollupVerifier] { | |
| +++ description: Used to update the verifier and keep track of current and old versions. Routes to a registered verifier by batch index, so that every batch is verified by the latest verifier that is enabled for this batch. | |
| values.latestVerifier.0.verifier: | |
| - | "eth:0x059adC0Db833f7cCb12dC41BE0017626337AfA63" |
| + | "eth:0x9774CE99E8Ab3f13582bC6c2Bd2832e5A25C4624" |
| values.latestVerifier.0.startBatchIndex: | |
| - | 51566 |
| + | 53283 |
| } |
| + | Status: CREATED |
| contract ZkEvmVerifierV1 (eth:0x9774CE99E8Ab3f13582bC6c2Bd2832e5A25C4624) [N/A] | |
| +++ description: None |
2026 April 10, 08:41 UTC6changesUpgraded one (out of two) SP1 verifiers to a standard SP1 Turbo version.
Upgraded one (out of two) SP1 verifiers to a standard SP1 Turbo version.
| contract MultipleVersionRollupVerifier (eth:0x5d1584c27b4aD233283c6da1ca1B825d6f220EC1) { | |
| +++ description: Used to update the verifier and keep track of current and old versions. Routes to a registered verifier by batch index, so that every batch is verified by the latest verifier that is enabled for this batch. | |
| values.latestVerifier.0.verifier: | |
| - | "eth:0x5ff102a4A4Ce2040288a797CE4CCCa85eE1E2d70" |
| + | "eth:0x059adC0Db833f7cCb12dC41BE0017626337AfA63" |
| values.latestVerifier.0.startBatchIndex: | |
| - | 47944 |
| + | 51566 |
| } |
| - | Status: DELETED |
| contract ZkEvmVerifierV1 (eth:0x5ff102a4A4Ce2040288a797CE4CCCa85eE1E2d70) | |
| +++ description: A snark verifier based on SP1 by Succinct. It verifies RISC-V execution in a PLONK proof. Used to verify the validity of L2 state transitions for single round fraud proofs. |
| + | Status: CREATED |
| contract ZkEvmVerifierV1 (eth:0x059adC0Db833f7cCb12dC41BE0017626337AfA63) | |
| +++ description: A snark verifier based on SP1 by Succinct. It verifies RISC-V execution in a PLONK proof. Used to verify the validity of L2 state transitions for single round fraud proofs. |
2026 April 01, 13:53 UTCHigh severity9changesNew upgrade, introduces mandatory reuse of blob data after reverting a batch. attack: 1. use commitBatches() with garbage in blob data 2. ... 3. brick (liveness) - nobody can prove - nobody can revert the blob part even ..withProof() reverts because of the existing blob data
New upgrade, introduces mandatory reuse of blob data after reverting a batch.
attack:
- use commitBatches() with garbage in blob data
- …
- brick (liveness)
- nobody can prove
- nobody can revert the blob part even …withProof() reverts because of the existing blob data
| contract Rollup (eth:0x759894Ced0e6af42c26668076Ffa84d02E3CeF60) { | |
| +++ description: The main contract of the Morph rollup. Allows to post transaction data and state roots and implements the the proof system. Sequencing and proposing are behind a whitelist. If the EnforcedTxGateway is not paused, any sequencer must include at least one L1 -> L2 message in their proposal if the oldest message is > 7d old. If the Sequencers are censoring or down for more than 7d, users can permissionlessly propose and prove via `commitBatchWithProof()`. | |
| sourceHashes.1: | |
| - | "0x1d0f1289361a17ee6c79d7879b1c620c7cee6f143ec4d14090b6aeedb6ed730a" |
| + | "0x4ae0d375d97899b0fd3cb34e7aa502f2b652e417b27b23df262734b951560256" |
| values.$implementation: | |
| - | "eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF" |
| + | "eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2" |
| values.$pastUpgrades.9: | |
| + | ["2026-03-30T09:36:47.000Z","0xd2892f5b4e5c8fe4bd476e83689b21f4716a38185a3923bd1fcbcf61deefb8f9",["eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2"]] |
| values.$upgradeCount: | |
| - | 9 |
| + | 10 |
| implementationNames.eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF: | |
| - | "Rollup" |
| implementationNames.eth:0x9e2Fb684935a32CEd121972f23BD0e4634377cA2: | |
| + | "Rollup" |
| } |
2026 March 27, 10:58 UTCHigh severity13changesRollup upgrade to make commitBatchWithProof() permissionless under any of these conditions: - The last committed batch has a timestamp that is 7d ago (rollupDelayPeriod) - The first message in the forced tx queue is more than 7d old this moves sequencer failure and proposer failure to green. for stage 1 at least an SC as upgrader is needed. because of the forced queue and the rollupDelayPeriod mechanic, the proof system might already be good for stage 1. https://disco.l2beat.com/diff/eth:0x1320d6A438d268044c8EEff0eE6B24E5EC9584e3/eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF
Rollup upgrade to make commitBatchWithProof() permissionless under any of these conditions:
- The last committed batch has a timestamp that is > 7d ago (rollupDelayPeriod)
- The first message in the forced tx queue is more than 7d old
this moves sequencer failure and proposer failure to green.
for stage 1 at least an SC as upgrader is needed. because of the forced queue and the rollupDelayPeriod mechanic, the proof system might already be good for stage 1.
https://disco.l2beat.com/diff/eth:0x1320d6A438d268044c8EEff0eE6B24E5EC9584e3/eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF
| contract Rollup (eth:0x759894Ced0e6af42c26668076Ffa84d02E3CeF60) { | |
| +++ description: The main contract of the Morph rollup. Allows to post transaction data and state roots and implements the the proof system. Sequencing and proposing are behind a whitelist. If the EnforcedTxGateway is not paused, any sequencer must include at least one L1 -> L2 message in their proposal if the oldest message is > 7d old. If the Sequencers are censoring or down for more than 7d, users can permissionlessly propose and prove via `commitBatchWithProof()`. | |
| template: | |
| - | "morph/MorphOldRollup" |
| + | "morph/Rollup" |
| sourceHashes.1: | |
| - | "0x8918639fcac94fac40711260ca7cb4027dbac6a2a48b10cd380818ede6636206" |
| + | "0x1d0f1289361a17ee6c79d7879b1c620c7cee6f143ec4d14090b6aeedb6ed730a" |
| description: | |
| - | "The main contract of the Morph rollup. Allows to post transaction data and state roots and implements the challenge mechanism along with the proof system. Sequencing and proposing are behind a whitelist. If the EnforcedTxGateway is not paused, any sequencer must include at least one L1 -> L2 message in their proposal if the oldest message is > 7d old. Although the contract exposes the external function commitBatchWithProof(), it currently reverts for non-whitelisted actors." |
| + | "The main contract of the Morph rollup. Allows to post transaction data and state roots and implements the the proof system. Sequencing and proposing are behind a whitelist. If the EnforcedTxGateway is not paused, any sequencer must include at least one L1 -> L2 message in their proposal if the oldest message is > 7d old. If the Sequencers are censoring or down for more than 7d, users can permissionlessly propose and prove via `commitBatchWithProof()`." |
| values.$implementation: | |
| - | "eth:0x1320d6A438d268044c8EEff0eE6B24E5EC9584e3" |
| + | "eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF" |
| values.$pastUpgrades.8: | |
| + | ["2026-03-27T01:34:11.000Z","0x8eec835066ebedafa6430fc7b0cd1de2b7a46eb09e56519868ca9dbb938f4c8f",["eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF"]] |
| values.$upgradeCount: | |
| - | 8 |
| + | 9 |
| implementationNames.eth:0x1320d6A438d268044c8EEff0eE6B24E5EC9584e3: | |
| - | "Rollup" |
| implementationNames.eth:0xB2F539aede77DF4cD1d427d046bBbBd8dB4cBAAF: | |
| + | "Rollup" |
| } |
Decentralised sequencer network
BLS signatures of the Sequencers are not verified onchain. Sequencing is centralized an permissioned to the listed sequencers in practice.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force transactions
Users can force the sequencer to include a transaction by submitting a request through L1. If the sequencer censors such a request or is down for 7d, any new proposal must include at least 1 transaction from the queue. Proposing is permissionless under these conditions if proven immediately.

Ethereum
Roles:
Allowed to challenge or delete state roots proposed by a Proposer.
Actors:
A Multisig with 3/5 threshold.
- Can interact with L1Staking
- Can interact with TimelockController
- cancel queued transactions
- propose transactions
- Can interact with MultipleVersionRollupVerifier
- register new verifiers to be used starting from a given L2 batch index
- Can interact with L1GatewayRouter
- manage token to escrow mapping and (un-)register escrows
- Can interact with Rollup
- can pause and unpause, revert unfinalized batches, update proof window and finalization period, manage challengers, modify the verifier address
- Can interact with EnforcedTxGateway
- pause and unpause, update the fee vault
- Can interact with Whitelist
- manage the whitelist
- A Challenger - acting directly
A Multisig with 4/6 threshold.
- Can upgrade with no delay
- L1Staking TimelockController → ProxyAdmin
- L1ETHGateway TimelockController → ProxyAdmin
- L1MessageQueueWithGasPriceOracle TimelockController → ProxyAdmin
- L1StandardERC20Gateway TimelockController → ProxyAdmin
- TimelockController ProxyAdmin
- L1GatewayRouter TimelockController → ProxyAdmin
- Rollup TimelockController → ProxyAdmin
- EnforcedTxGateway TimelockController → ProxyAdmin
- L1CrossDomainMessenger TimelockController → ProxyAdmin
- Can interact with TimelockController
- execute transactions that are ready
- manage all access control roles TimelockController - or - acting directly

Ethereum
- Roles:
- owner: TimelockController
A timelock with access control. The current minimum delay is 0s.
- Roles:
- admin: ProxyAdmin; ultimately Morph Multisig 1
- canceller: Morph Multisig 2
- defaultAdmin: Morph Multisig 1, TimelockController; ultimately Morph Multisig 1
- executor: Morph Multisig 1
- proposer: Morph Multisig 2
Main entrypoint for depositing ETH and ERC20 tokens, which are then forwarded to the correct escrow.
- Roles:
- admin: ProxyAdmin; ultimately Morph Multisig 1
- owner: Morph Multisig 2
The main contract of the Morph rollup. Allows to post transaction data and state roots and implements the the proof system. Sequencing and proposing are behind a whitelist. If the EnforcedTxGateway is not paused, any sequencer must include at least one L1 -> L2 message in their proposal if the oldest message is > 7d old. If the Sequencers are censoring or down for more than 7d, users can permissionlessly propose and prove via commitBatchWithProof().
- Roles:
- admin: ProxyAdmin; ultimately Morph Multisig 1
- challengers: EOA 1, EOA 10, EOA 11, EOA 13, EOA 14, EOA 15, EOA 16, EOA 18, EOA 19, EOA 2, EOA 20, EOA 21, EOA 22, EOA 23, EOA 24, EOA 25, EOA 26, EOA 27, EOA 28, EOA 3, EOA 30, EOA 31, EOA 32, EOA 33, EOA 34, EOA 35, EOA 36, EOA 37, EOA 38, EOA 4, EOA 40, EOA 41, EOA 42, EOA 5, EOA 6, EOA 8, EOA 9, Morph Multisig 2
- owner: Morph Multisig 2
- Roles:
- owner: Morph Multisig 1
Contract used to send L1 -> L2 and relay messages from L2. It allows to replay failed messages and to drop skipped messages. L1 -> L2 messages sent using this contract pay for L2 gas on L1 and will have the aliased address of this contract as the sender.
- Roles:
- admin: ProxyAdmin; ultimately Morph Multisig 1
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).