Search
Search for projects by name or address
 Xterio Chain
Xterio Chain
Badges
About
Xterio Chain is an OP stack Optimium on Ethereum. The chain focuses on gaming, high performance and low fees .
Badges
About
Xterio Chain is an OP stack Optimium on Ethereum. The chain focuses on gaming, high performance and low fees .
Why is the project listed in others?
Consequence: projects without a proper proof system fully rely on single entities to safely update the state. A malicious proposer can finalize an invalid state, which can cause loss of funds.
Consequence: projects without a data availability bridge fully rely on single entities (the sequencer) to honestly rely available data roots on Ethereum. A malicious sequencer can collude with the proposer to finalize an unavailable state, which can cause loss of funds.
Learn more about the recategorisation here.
2024 May 29 — 2026 May 26
The section shows the operating costs that L2s pay to Ethereum.
2024 May 29 — 2026 May 26
Funds can be stolen if
- the sequencer is malicious and is able to economically outspend the altruistic challengers,
- there is no challenger willing to challenge unavailable data commitments,
- a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL),
- an invalid state root is submitted to the system (CRITICAL).
Funds can be frozen if
MEV can be extracted if
Currently the system permits invalid state roots. More details in project overview.
Proof construction and state derivation rely fully on data that is NOT published onchain. A custom data availability (DA) provider without attestations is used, but data unavailability can be challenged.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Only the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
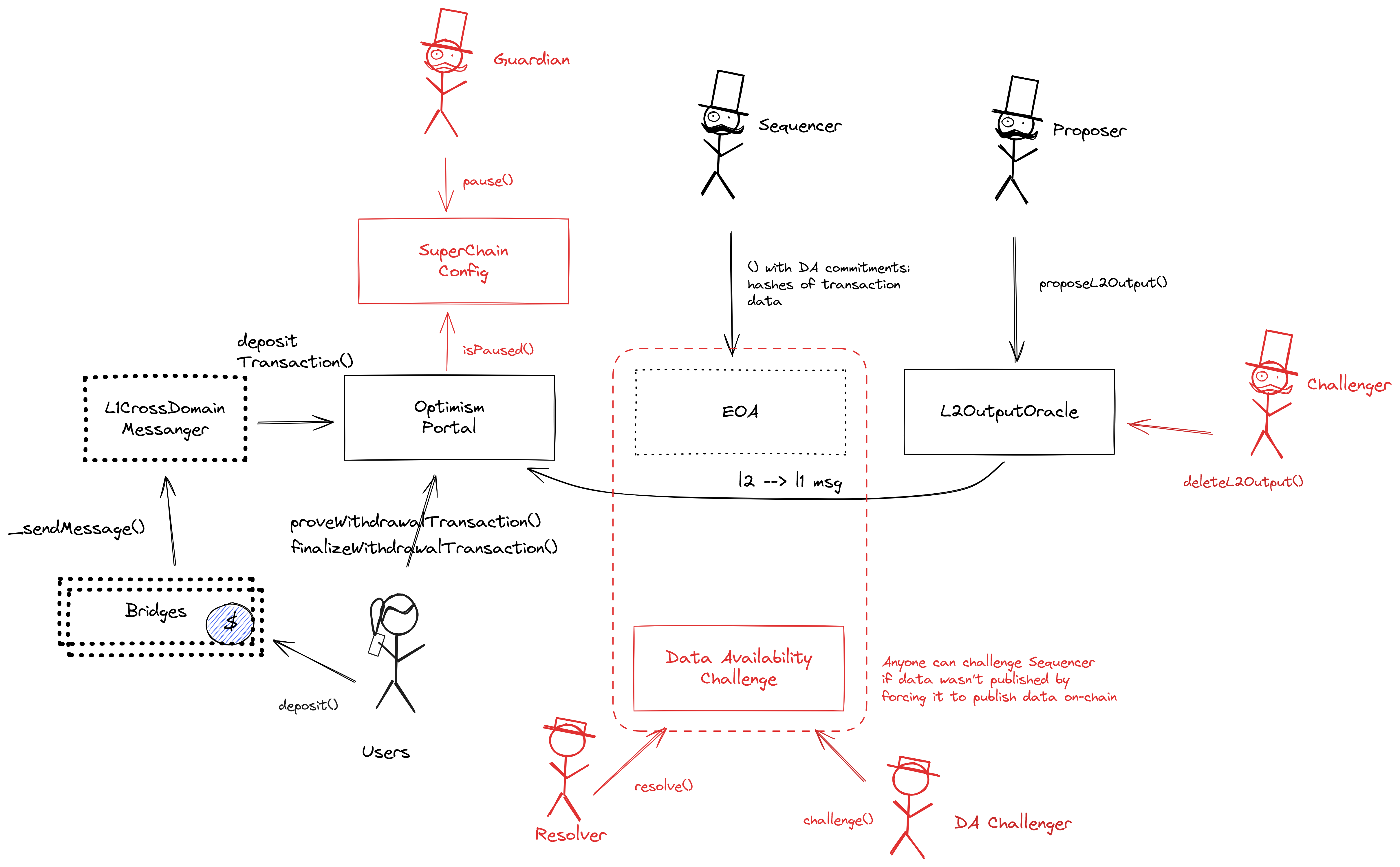
XterioDA is a data availability solution using data availability challenges (DA Challenges).
There are no onchain assets at risk of being slashed in case of a data withholding attack. However, there is a mechanism that allows users to challenge unavailability of data. The system is not secure if the malicious sequencer is able to outspend the altruistic challengers, and there is no pool of funds onchain to incentivize challengers.
There is no fraud detection mechanism in place. A data withholding attack can only be detected by nodes downloading the full data from the DA layer.
The committee does not meet basic security standards, either due to insufficient size, lack of member diversity, or poorly defined threshold parameters. The system lacks an effective DA bridge and it is reliant on the assumption of an honest sequencer, creating significant risks to data integrity and availability.
There is no delay in the upgradeability of the bridge. Users have no time to exit the system before the bridge implementation update is completed.
The relayer role is permissioned, and the DA bridge does not have a Security Council or a governance mechanism to propose new relayers. In case of relayer failure, the DA bridge will halt and be unable to recover without the intervention of a centralized entity.
Architecture

Data Availability Challenges
Xterio relies on DA challenges for data availability. The DA Provider submits an input commitment on Ethereum, and users can request the data behind the commitment off-chain from the DA Provider. If a DA challenger finds that the data behind a tx data commitment is not available, they can submit a challenge which requires locking a bond within 12h. A challenge can be resolved by publishing the preimage data within an additional 12h. In such case, a portion of the challenger bond is burned, with the exact amount estimated as the cost incurred by the resolver to publish the full data, meaning that the resolver and challenger will approximately lose the same amount of funds. The system is not secure if the malicious sequencer is able to outspend the altruistic challengers. If instead, after a challenge, the preimage data is not published, the chain reorgs to the last fully derivable state.
DA Bridge
Only hashes of data batches are posted as DA commitments to an EOA on Ethereum. However, there is a mechanism that allows users to challenge unavailability of data.
Funds can be lost if the sequencer posts an invalid data availability certificate and there are no challengers.
Funds can be lost if the sequencer posts an invalid data availability certificate, and he is able to outspend the challengers.
OP Stack projects can use the OP fault proof system, already being deployed on some. This project though is not using fault proofs yet and is relying on the honesty of the permissioned Proposer and Challengers to ensure state correctness. The smart contract system permits invalid state roots.
Funds can be stolen if an invalid state root is submitted to the system (CRITICAL).
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2025 April 18, 18:48 UTCHigh severity30changesupgrade to 'special' OptiPortal without deposited tx mechanism and with a permissioned withdrawEth function.
upgrade to ‘special’ OptiPortal without deposited tx mechanism and with a permissioned withdrawEth function.
| contract OptimismPortal (0xBC2bEDA4ce7A1f40aa458322A33B44081b2F545A) { | |
| +++ description: The main entry point to deposit funds from host chain to this chain. It also allows to prove and finalize withdrawals. Forced transactions from Layer 1 are disabled. | |
| template: | |
| - | "opstack/OptimismPortal" |
| + | "opstack/OptimismPortalAdminWithdraw" |
| sourceHashes.1: | |
| - | "0xe35fb7bc0433439337b3eadda3d6fb7991918162f62a337a695e8c7f948cdd35" |
| + | "0x106b0e020294fd04557c64727796c1a7afc80dba9c83e38e52b5282d4d1531f5" |
| description: | |
| - | "The main entry point to deposit funds from host chain to this chain. It also allows to prove and finalize withdrawals." |
| + | "The main entry point to deposit funds from host chain to this chain. It also allows to prove and finalize withdrawals. Forced transactions from Layer 1 are disabled." |
| issuedPermissions.2: | |
| + | {"permission":"upgrade","to":"0xfF75Bd7672b79f2562fAf98D488bbb3Db1cD1574","via":[{"address":"0x9e48d6bBca781c23392Ec459BfB3657C40a794A8"}]} |
| issuedPermissions.1.permission: | |
| - | "upgrade" |
| + | "guard" |
| issuedPermissions.1.to: | |
| - | "0xfF75Bd7672b79f2562fAf98D488bbb3Db1cD1574" |
| + | "0xdF3700a9Cf9c7506Ca3B41E6ba991476677A8787" |
| issuedPermissions.1.via.0: | |
| - | {"address":"0x9e48d6bBca781c23392Ec459BfB3657C40a794A8"} |
| issuedPermissions.0.permission: | |
| - | "guard" |
| + | "interact" |
| issuedPermissions.0.to: | |
| - | "0xdF3700a9Cf9c7506Ca3B41E6ba991476677A8787" |
| + | "0x8f33C32503B860eDd31BeC1c80669aFee40901f3" |
| issuedPermissions.0.description: | |
| + | "withdraw all ETH without proof." |
| values.$implementation: | |
| - | "0xb6a5DCc244EfAbE3194cf5e5590a463f44eD5784" |
| + | "0xEdE953bab7C50B2e5150316Ae0574F0cbA4068a9" |
| values.$pastUpgrades.1: | |
| + | ["2024-05-24T08:53:23.000Z","0xc93dc2274b4ce4975aae8b5d6ffde3b52c6457d4c11400d710a63142d369fa83",["0xb6a5DCc244EfAbE3194cf5e5590a463f44eD5784"]] |
| values.$pastUpgrades.0.2: | |
| - | "0xc93dc2274b4ce4975aae8b5d6ffde3b52c6457d4c11400d710a63142d369fa83" |
| + | ["0xEdE953bab7C50B2e5150316Ae0574F0cbA4068a9"] |
| values.$pastUpgrades.0.1: | |
| - | "2024-05-24T08:53:23.000Z" |
| + | "0x28fc02b17e9d4fc1107f498afbce93158b39649d34acf6f709626e3a326037ad" |
| values.$pastUpgrades.0.0: | |
| - | ["0xb6a5DCc244EfAbE3194cf5e5590a463f44eD5784"] |
| + | "2025-04-16T15:34:35.000Z" |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| values.privilegedAddress: | |
| + | "0x8f33C32503B860eDd31BeC1c80669aFee40901f3" |
| } |
| + | Status: CREATED |
| contract Safe (0x8f33C32503B860eDd31BeC1c80669aFee40901f3) | |
| +++ description: None |
2025 April 06, 08:20 UTCHigh severity26changesOperators change, no change to implementations.
Operators change, no change to implementations.
| contract L2OutputOracle (0x5A0492D20D984eE904E46E6Ff24572bc755abb28) { | |
| +++ description: Contains a list of proposed state roots which Proposers assert to be a result of block execution. Currently only the PROPOSER address can submit new state roots. | |
| issuedPermissions.1.permission: | |
| - | "propose" |
| + | "challenge" |
| issuedPermissions.1.to: | |
| - | "0x7d2f9b38866141Bf090DD670A826F27eA2408Ad4" |
| + | "0x8b3B4F6C348f6baC39190B89c801E61E41F05b88" |
| issuedPermissions.0.permission: | |
| - | "challenge" |
| + | "propose" |
| issuedPermissions.0.to: | |
| - | "0xfA8d42bDE52C2B8B05fE5EeCbAdEa6CB698A0Bc5" |
| + | "0xE4Cb2fd9E409ABE977EC946D54b59034C39AB07D" |
| values.$pastUpgrades.2: | |
| + | ["2025-04-05T14:16:59.000Z","0x3c36d0fd57e70dee54e8ecc5c70de812a57dd8bc3db576cf12ce164acbeb8cce",["0xA9D78F579f1B30194F3c2Ca1987A9B91A33BDF08"]] |
| values.$pastUpgrades.1: | |
| + | ["2025-04-05T14:25:47.000Z","0x4dbaa9a0411962209ad663ec973dca85671030aef9bbf598b9727a292a83525d",["0x48Ef83Cf812f291EDB00C2D48440Ee90cD12be1a"]] |
| values.$upgradeCount: | |
| - | 1 |
| + | 3 |
| +++ severity: HIGH | |
| values.challenger: | |
| - | "0xfA8d42bDE52C2B8B05fE5EeCbAdEa6CB698A0Bc5" |
| + | "0x8b3B4F6C348f6baC39190B89c801E61E41F05b88" |
| values.CHALLENGER: | |
| - | "0xfA8d42bDE52C2B8B05fE5EeCbAdEa6CB698A0Bc5" |
| + | "0x8b3B4F6C348f6baC39190B89c801E61E41F05b88" |
| +++ severity: HIGH | |
| values.proposer: | |
| - | "0x7d2f9b38866141Bf090DD670A826F27eA2408Ad4" |
| + | "0xE4Cb2fd9E409ABE977EC946D54b59034C39AB07D" |
| values.PROPOSER: | |
| - | "0x7d2f9b38866141Bf090DD670A826F27eA2408Ad4" |
| + | "0xE4Cb2fd9E409ABE977EC946D54b59034C39AB07D" |
| } |
| contract SystemConfig (0x6E99cdE188DAAFeEcb6eD8AC28B98dE4c8eE5D6C) { | |
| +++ description: Contains configuration parameters such as the Sequencer address, gas limit on this chain and the unsafe block signer address. | |
| issuedPermissions.1.to: | |
| - | "0x7d6251D49A102a330CfB46d132982781620700Cb" |
| + | "0x39857a92E26648438d9c7dDDa1Ee3e481dea54B3" |
| values.batcherHash: | |
| - | "0x7d6251D49A102a330CfB46d132982781620700Cb" |
| + | "0x39857a92E26648438d9c7dDDa1Ee3e481dea54B3" |
| values.unsafeBlockSigner: | |
| - | "0xcbdD38Ce74BA96F0ae3D2E608DA96Ec744c80A7E" |
| + | "0x7a4e92aD7E40C8df264eD18010847e6C27AB3d82" |
| } |
2024 July 18, 14:50 UTC18changesProvide description of changes. This section will be preserved.
Provide description of changes. This section will be preserved.
Initial discovery
| + | Status: CREATED |
| contract PreimageOracle (0x089A4754538B74Ff63Bc6AbeaD7A95973aB03572) | |
| +++ description: None |
| + | Status: CREATED |
| contract DelayedWETH (0x0eCe16401A80551345bB672f177f51A8755FF775) | |
| +++ description: None |
| + | Status: CREATED |
| contract PermissionedDisputeGame (0x15b689D90a62C3F7380054C8867b7e7f17Fa7F4B) | |
| +++ description: None |
| + | Status: CREATED |
| contract DataAvailabilityChallenge (0x16193e14197c10109F3e81b938153A04A2a00190) | |
| +++ description: None |
| + | Status: CREATED |
| contract MIPS (0x253DdBb3549e0CEFaaaA7f71BE502C5b94771dDc) | |
| +++ description: None |
| + | Status: CREATED |
| contract L1ERC721Bridge (0x28d56C3BBbe4807c19Cc81E6D5207Fb681C3726b) | |
| +++ description: Used to bridge ERC-721 tokens from host chain to this chain. |
| + | Status: CREATED |
| contract L1StandardBridge (0x2AD84AbD52050956AcC9c490D024b821A59e3FB6) | |
| +++ description: The main entry point to deposit ERC20 tokens from host chain to this chain. This contract can store any token. |
| + | Status: CREATED |
| contract DisputeGameFactory (0x443164F044D8840479234e00E7aD5bb06b85fC78) | |
| +++ description: None |
| + | Status: CREATED |
| contract OptimismMintableERC20Factory (0x515A0c8b1d9574C65EA1924eCd767B1d9b6AC32f) | |
| +++ description: None |
| + | Status: CREATED |
| contract FaultDisputeGame (0x56c7D88ee46BfD6cab37508E2e39e985a68007a4) | |
| +++ description: None |
| + | Status: CREATED |
| contract L2OutputOracle (0x5A0492D20D984eE904E46E6Ff24572bc755abb28) | |
| +++ description: Contains a list of proposed state roots which Proposers assert to be a result of block execution. Currently only the PROPOSER address can submit new state roots. |
| + | Status: CREATED |
| contract SystemConfig (0x6E99cdE188DAAFeEcb6eD8AC28B98dE4c8eE5D6C) | |
| +++ description: Contains configuration parameters such as the Sequencer address, gas limit on this chain and the unsafe block signer address. |
| + | Status: CREATED |
| contract L1CrossDomainMessenger (0x702dF90E92A6841c9013faE6D724ddFA8F141d5C) | |
| +++ description: Sends messages from host chain to this chain, and relays messages back onto host chain. In the event that a message sent from host chain to this chain is rejected for exceeding this chain's epoch gas limit, it can be resubmitted via this contract's replay function. |
| + | Status: CREATED |
| contract ProxyAdmin (0x9e48d6bBca781c23392Ec459BfB3657C40a794A8) | |
| +++ description: None |
| + | Status: CREATED |
| contract OptimismPortal (0xBC2bEDA4ce7A1f40aa458322A33B44081b2F545A) | |
| +++ description: The main entry point to deposit funds from host chain to this chain. It also allows to prove and finalize withdrawals. |
| + | Status: CREATED |
| contract AddressManager (0xBdF852e2cc26Ea3C2dee7b493B1Fc12dA406175a) | |
| +++ description: None |
| + | Status: CREATED |
| contract SuperchainConfig (0xcbF423525a5471Fc5037a5397F99f6F09fe41379) | |
| +++ description: None |
| + | Status: CREATED |
| contract RollupOwnerMultisig (0xfF75Bd7672b79f2562fAf98D488bbb3Db1cD1574) | |
| +++ description: None |
The system has a centralized operator
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly.
Regular messaging
Funds can be frozen if the centralized validator goes down. Users cannot produce blocks themselves and exiting the system requires new block production (CRITICAL).
Forced messaging
If the user experiences censorship from the operator with regular L2->L1 messaging they can submit their messages directly on L1. The system is then obliged to service this request or halt all messages, including forced withdrawals from L1 and regular messages initiated on L2. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular message.
EVM compatible smart contracts are supported
OP stack chains are pursuing the EVM Equivalence model. No changes to smart contracts are required regardless of the language they are written in, i.e. anything deployed on L1 can be deployed on L2.

Ethereum
Roles:
Allowed to challenge or delete state roots proposed by a Proposer.
Allowed to pause withdrawals. In op stack systems with a proof system, the Guardian can also blacklist dispute games and set the respected game type (permissioned / permissionless).
Allowed to post new state roots of the current layer to the host chain.
Allowed to commit transactions from the current layer to the host chain.
Actors:
A Multisig with 3/4 threshold.
- Can upgrade with no delay
- DataAvailabilityChallenge ProxyAdmin
- L1ERC721Bridge ProxyAdmin
- L1StandardBridge ProxyAdmin
- OptimismMintableERC20Factory ProxyAdmin
- L2OutputOracle ProxyAdmin
- SystemConfig ProxyAdmin
- L1CrossDomainMessenger ProxyAdmin
- OptimismPortal ProxyAdmin
- SuperchainConfig ProxyAdmin
- Can interact with AddressManager
- set and change address mappings ProxyAdmin
A Multisig with 3/4 threshold.
- Can interact with OptimismPortal
- withdraw all ETH without proof
- A Guardian - acting directly
- A Challenger - acting directly
- Can interact with DataAvailabilityChallenge
- can upgrade the parameters of DA challenges like the bond size or refund percentages, potentially making challenges infeasable or insecure
- Can interact with SystemConfig
- A Proposer - acting directly
- A Sequencer - acting directly

Ethereum
The DataAvailabilityChallenge contract is used to challenge the full availability of data behind commimted transaction data hashes. See the technology section for more details.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
- owner: EOA 3
Contains a list of proposed state roots which Proposers assert to be a result of block execution. Currently only the PROPOSER address can submit new state roots.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
- challenger: EOA 2
- proposer: EOA 4
The main entry point to deposit funds from host chain to this chain. It also allows to prove and finalize withdrawals. Forced transactions from Layer 1 are disabled.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
- guardian: EOA 1
- privilegedAddress: Safe
This is NOT the shared SuperchainConfig contract of the OP stack Superchain but rather a local fork. It manages the PAUSED_SLOT, a boolean value indicating whether the local chain is paused, and GUARDIAN_SLOT, the address of the guardian which can pause and unpause the system.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
- guardian: EOA 1
Used to bridge ERC-721 tokens from host chain to this chain.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
The main entry point to deposit ERC20 tokens from host chain to this chain.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
All supported tokens in this escrow are included in the value secured calculation.
Sends messages from host chain to this chain, and relays messages back onto host chain. In the event that a message sent from host chain to this chain is rejected for exceeding this chain’s epoch gas limit, it can be resubmitted via this contract’s replay function.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
A helper contract that generates OptimismMintableERC20 contracts on the network it’s deployed to. OptimismMintableERC20 is a standard extension of the base ERC20 token contract designed to allow the L1StandardBridge contracts to mint and burn tokens. This makes it possible to use an OptimismMintableERC20 as this chain’s representation of a token on the host chain, or vice-versa.
- Roles:
- admin: ProxyAdmin; ultimately Xterio Multisig
- Roles:
- owner: Xterio Multisig
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).