Search
Search for projects by name
 Arbitrum Nova
Arbitrum Nova
Badges
About
Arbitrum Nova is an AnyTrust Optimium, differing from Arbitrum One by not posting transaction data onchain.
Badges
About
Arbitrum Nova is an AnyTrust Optimium, differing from Arbitrum One by not posting transaction data onchain.
2024 Jul 01 — 2025 Jul 01
2024 Jul 02 — 2025 Jul 01
The section shows the operating costs that L2s pay to Ethereum.
2024 Jul 02 — 2025 Jul 01
The chart illustrates how "live" the project's operators are by displaying how frequently they submit transactions of the selected type and if these intervals deviate from their typical schedule.
2025 Jun 01 — Jul 01
ArbOS 32 Emergency upgrade
2024 Sep 25th
SecurityCouncil emergency upgrades to fix attack vectors related to Stylus resource pricing.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
Fraud proofs allow 10 WHITELISTED actors watching the chain to prove that the state is incorrect. At least 5 Challengers are external to the Operator. Interactive proofs (INT) require multiple transactions over time to resolve. There is a 6d 8h challenge period.
Proof construction relies fully on data that is NOT published onchain. There exists a Data Availability Committee (DAC) with a threshold of 5/6 that is tasked with protecting and supplying the data.
Non-emergency upgrades are initiated on L2 and go through a 8d delay. Since there is a 1d delay to force a tx (forcing the inclusion in the following state update), users have only 7d to exit.
If users post a tx after that time, they would only be able to self propose a state root 28d after the last state root was proposed and then wait for the 6d 8h challenge window, while the upgrade would be confirmed just after the 6d 8h challenge window and the 3d L1 timelock.
Anyone can become a Proposer after 28d of inactivity from the currently whitelisted Proposers.
Set of parties responsible for signing and attesting to the availability of data.
There are no onchain assets at risk of being slashed in case of a data withholding attack. However, there is indirect economic security derived by the committee members being publicly known, and their reputation is at stake should they behave maliciously.
There is no fraud detection mechanism in place. A data withholding attack can only be detected by nodes downloading the full data from the DA layer.
For regular updates, there is a 17d 8h delay before the bridge implementation update is completed. The Security Council can upgrade the DA bridge without delay.
The relayer role is permissioned, but the DA bridge has a Security Council or a governance mechanism to propose new relayers. In case of relayer failure, the DA bridge liveness can be restored by proposing a new relayer after a delay of 17d 8h via governance upgrade, or through a Security Council without delay.
Architecture

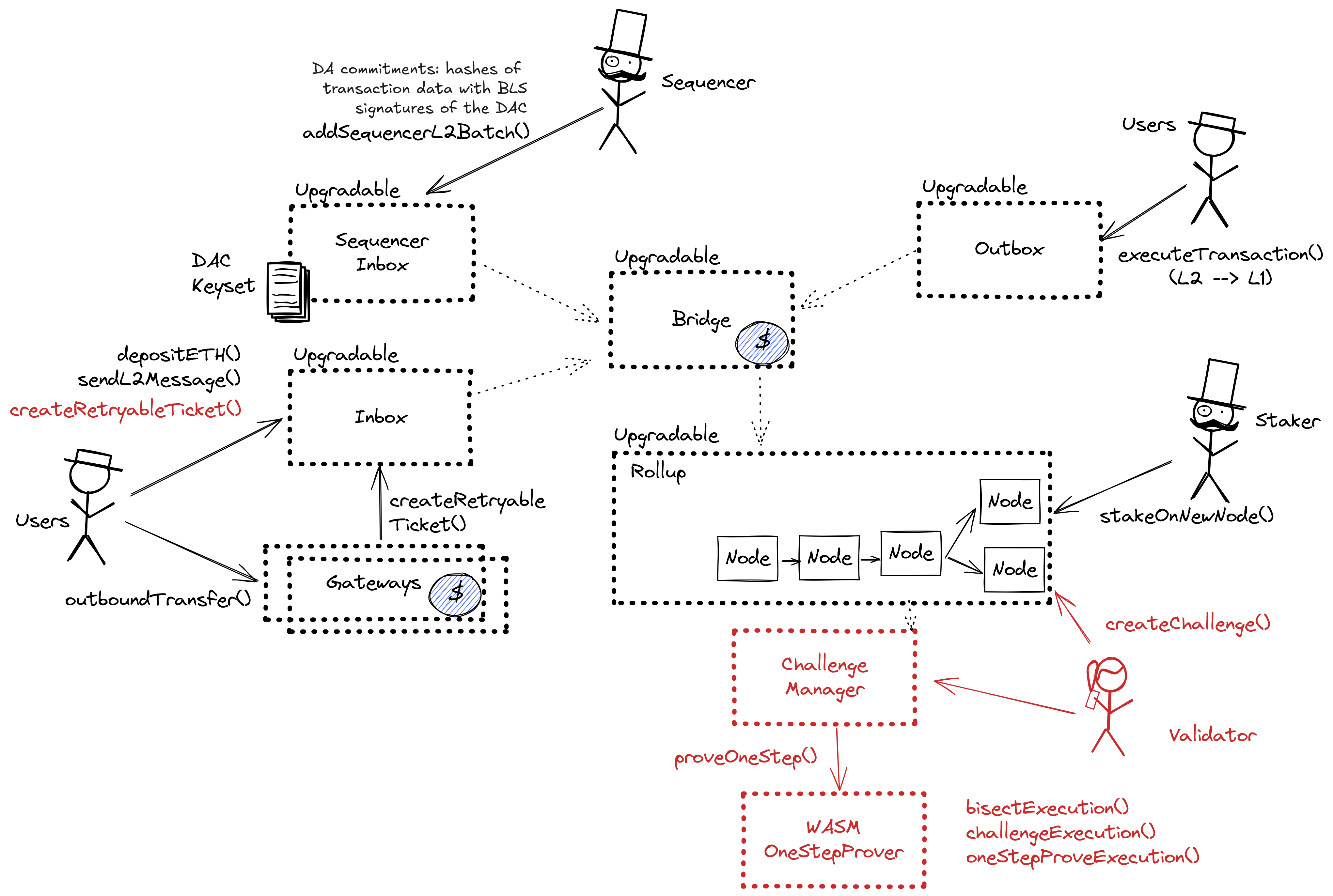
Nova is a data availability solution for Arbitrum rollups built on the AnyTrust protocol. It is composed of the following components:
- Sequencer Inbox: Main entry point for the Sequencer submitting transaction batches.
- Data Availability Committee (DAC): A group of members responsible for storing and providing data on demand.
- Data Availability Certificate (DACert): A commitment ensuring that data blobs are available without needing full data posting on the L1 chain.
Committee members run servers that support APIs for storing and retrieving data blobs. The Sequencer API allows the rollup Sequencer to submit data blobs for storage, while the REST API enables anyone to fetch data by hash. When the Sequencer produces a data batch, it sends the batch along with an expiration time to Committee members, who store it and sign it. Once enough signatures are collected, the Sequencer aggregates them into a valid DACert and posts it to the L1 chain inbox. If the Sequencer fails to collect enough signatures, it falls back to posting the full data to the L1 chain.
A DACert includes a hash of the data block, an expiration time, and proof that the required threshold of Committee members have signed off on the data. The proof consists of a hash of the Keyset used in signing, a bitmap indicating which members signed, and a BLS aggregated signature. L2 nodes reading from the sequencer inbox verify the certificate’s validity by checking the number of signers, the aggregated signature, and that the expiration time is at least two weeks ahead of the L2 timestamp. If the DACert is valid, it provides a proof that the corresponding data is available from honest committee members.
DA Bridge Architecture

In Nova architecture, the DA commitments are posted to the L1 through the sequencer inbox, using the inbox as a DA bridge. The DA commitment consists of Data Availability Certificate (DACert), including a hash of the data block, an expiration time, and a proof that the required threshold of Committee members have signed off on the data. The sequencer distributes the data and collects signatures from Committee members offchain. Only the DACert is posted by the sequencer to the L1 chain inbox (the DA bridge), achieving L2 transaction ordering finality in a single onchain transaction.
DA Bridge Upgradeability

The Arbitrum DAO controls Arbitrum Nova through upgrades and modifications to their smart contracts on Layer 1 Ethereum and the Layer 2s. Regular upgrades, Admin- and Owner actions originate from either the Arbitrum DAO or the non-emergency (proposer-) Security Council on Arbitrum One and pass through multiple delays and timelocks before being executed at their destination. Contrarily, the three Emergency Security Council multisigs (one on each chain: Arbitrum One, Ethereum, Arbitrum Nova) can skip delays and directly access all admin- and upgrade functions of all smart contracts. These two general paths have the same destination: the respective UpgradeExecutor smart contract. Regular upgrades are scheduled in the L2 Timelock. The proposer Security Council can do this directly and the Arbitrum DAO (ARB token holders and delegates) must meet a CoreGovernor-enforced 5% threshold of the votable tokens. The L2 Timelock queues the transaction for a 3d delay and then sends it to the Outbox contract on Ethereum. This incurs another delay (the challenge period) of 6d 8h. When that has passed, the L1 Timelock delays for additional 3d. Both timelocks serve as delays during which the transparent transaction contents can be audited, and even cancelled by the Emergency Security Council. Finally, the transaction can be executed, calling Admin- or Owner functions of the respective destination smart contracts through the UpgradeExecutor on Ethereum. If the predefined transaction destination is Arbitrum One or -Nova, this last call is executed on L2 through the canonical bridge and the aliased address of the L1 Timelock. Operator roles like the Sequencers and Validators are managed using the same paths. Sequencer changes can be delegated to a Batch Poster Manager.
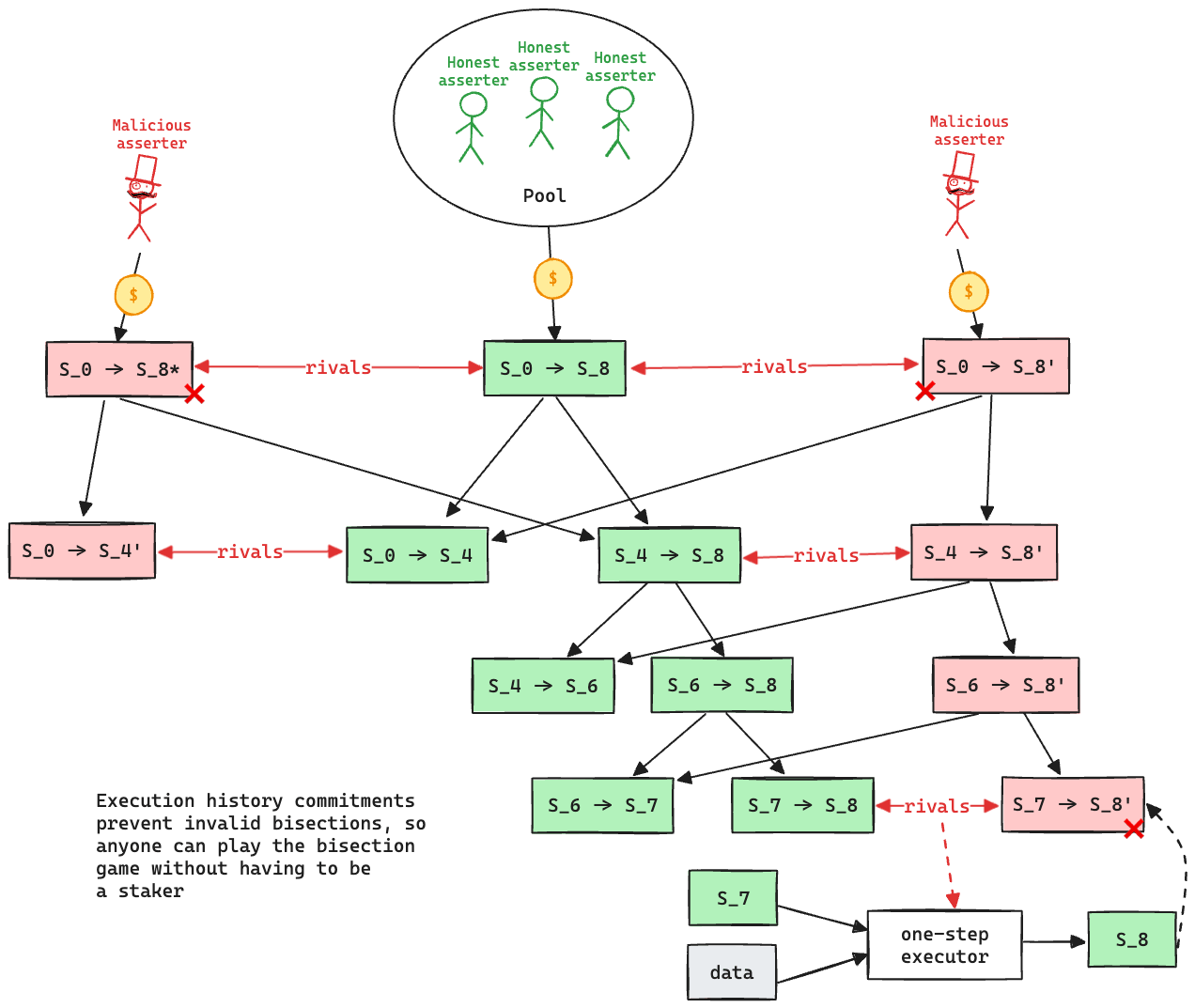
Updates to the system state can be proposed and challenged by a set of whitelisted validators. If a state root passes the challenge period, it is optimistically considered correct and made actionable for withdrawals.
Validators propose state roots as children of a previous state root. A state root can have multiple conflicting children. State roots are referred to as “assertions” within the contracts. Each chain of assertions only requires one stake, and validators staked on assertions with a child are considered inactive and can either move their stake to a new node or withdraw it. The function used to propose a new assertion is the stakeOnNewAssertion function. The stake is currently set to 1.0 ETH, and it can be slashed if the proposal is proven incorrect via a fraud proof. The protocol allows such funds to be trustlessly pooled together if necessary. New nodes cannot be created faster than the minimum assertion period, currently set to 15m. An assertion without “rivals” can be confirmed after the challenge period has passed, currently set to 6d 8h. If a rival is present, then it is checked that the assertion is the winner in the challenge protocol.
A challenge can be started between two siblings, i.e. two different state roots that share the same parent, by calling the createLayerZeroEdge function in the ChallengeManager contract. Edges represent assertions, or bisected assertions, within the challenge protocol. Challenges are played via a bisection game, where asserters and challengers play together to find the first instruction of disagreement. Such instruction is then executed onchain in the WASM OneStepProver contract to determine the winner. An edge can only be bisected when rivaled. The bisection process requires no new stake as their validity is checked against a parent “history root” that contains all intermediate states. An edge can also be confirmed if itself or its descendants spend enough time being unrivaled. Such time is set to 6d 8h. If both actors play as slow as possible, the maximum time to confirm an edge is double such value, i.e. 12d 17h. Due to the complexities of maintaining the history root, the challenge protocol is divided into 3 levels, where the lowest level represents assertions over blocks, the highest level represents assertions over single WASM instructions, and intermediate levels represent assertions over chunks of WASM instructions. When moving between levels, a new stake is required. Level 0 (block level) requires a stake of 0.0 ETH, level 1 requires a stake of 1.0 ETH, level 2 requires a stake of 1.0 ETH. The ratio between such stakes can be exploited to perform resource exhaustion attacks.
Funds can be stolen if an attacker successfully performs a resource exhaustion attack.
The system has a centralized sequencer
While forcing transaction is open to anyone the system employs a privileged sequencer that has priority for submitting transaction batches and ordering transactions.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly. After a delay of 1d in which a Sequencer has failed to include a transaction that was directly posted to the smart contract, it can be forcefully included by anyone on the host chain, which finalizes its ordering.
Buffered forced transactions
To force transactions from the host chain, users must first enqueue “delayed” messages in the “delayed” inbox of the Bridge contract. Only authorized Inboxes are allowed to enqueue delayed messages, and the so-called Inbox contract is the one used as the entry point by calling the sendMessage or sendMessageFromOrigin functions. If the centralized sequencer doesn’t process the request within some time bound, users can call the forceInclusion function on the SequencerInbox contract to include the message in the canonical chain. The time bound is defined to be the minimum between 1d and the time left in the delay buffer. The delay buffer gets replenished over time and gets consumed every time the sequencer doesn’t timely process a message. Only messages processed with a delay greater than 1h consume the buffer. The buffer is capped at 2d. The replenish rate is currently set at 1m every 20m. Even if the buffer is fully consumed, messages are still allowed to be delayed up to 1h.
Regular messaging
Autonomous exit
Users can (eventually) exit the system by pushing the transaction on L1 and providing the corresponding state root. The only way to prevent such withdrawal is via an upgrade.
EVM compatible and Stylus smart contracts are supported
Arbitrum One supports smart contracts written in Solidity and other programming languages (Rust, C++) that compile to WASM. Such smart contracts are executed by nodes using either a geth fork or a fork of wasmer inside the Nitro node, and can be proven with the onchain WASM VM.
Arbitrum DAO is in charge of upgrades
Arbitrum DAO allows $ARB token holders to propose and vote on changes to the organization and the technologies it governs. The governance smart contracts are implemented on Arbitrum One rollup chain. The DAO can upgrade the Arbitrum One contracts on L2 with 8d delay and - using L2 --> L1 Governance Relay, update contracts on L1 with additional 3d delay + 6d 8h delay for all L2 --> L1 messages (in total a delay of 17d 8h). The Security Council can upgrade the contracts without any delay. It can also cancel any upgrades initiated by the DAO.
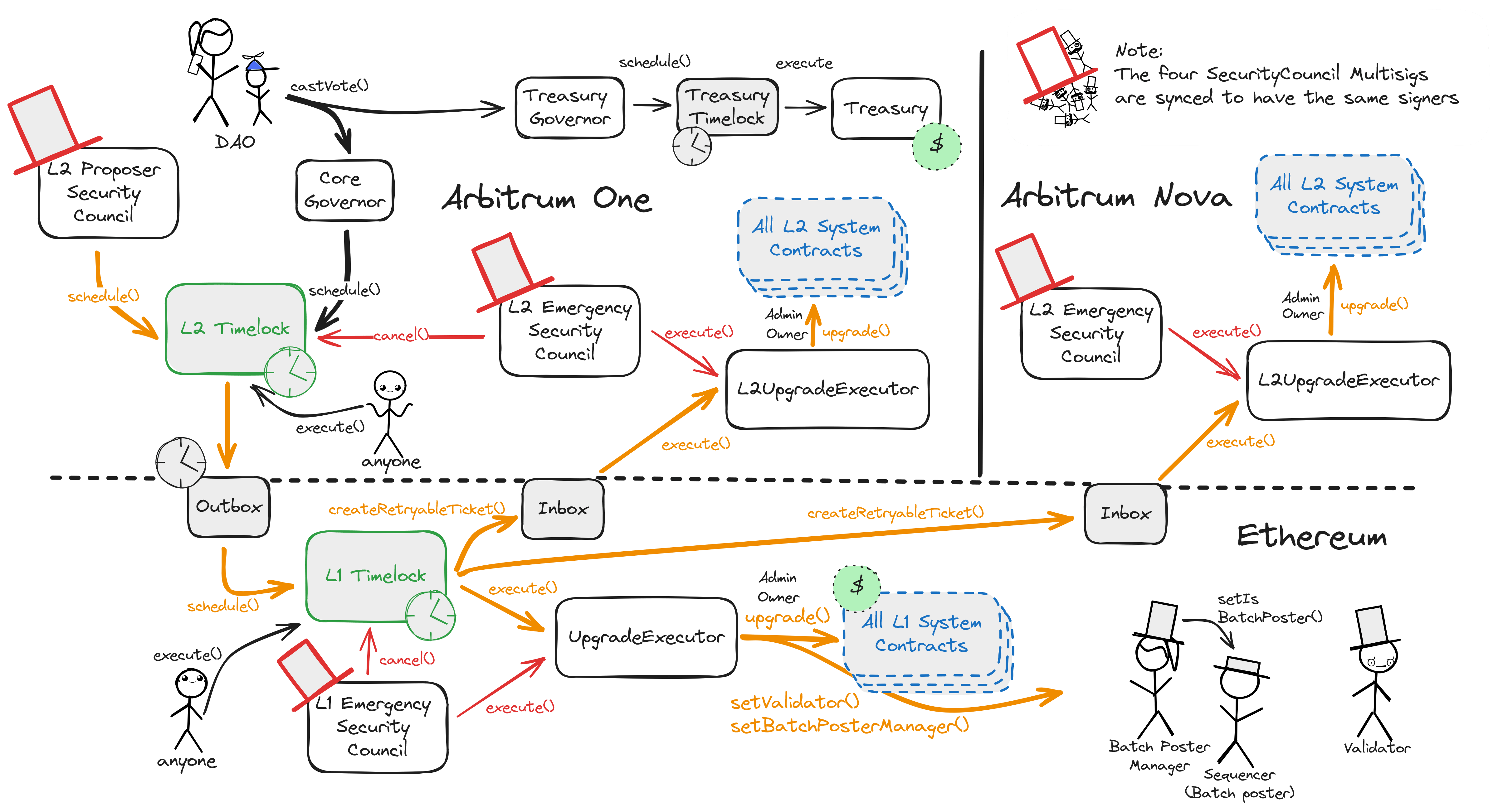
All critical system smart contracts are upgradeable (can be arbitrarily changed). This permission is governed by the Arbitrum Decentralized Autonomous Organization (DAO) and their elected Security Council. The Arbitrum DAO controls Arbitrum One and Arbitrum Nova through upgrades and modifications to their smart contracts on Layer 1 Ethereum and the Layer 2s. While the DAO governs through token-weighted governance in their associated ARB token, the Security Council can directly act through multisigs on all three chains. Although they are technically separate and connect to different target permissions, their member- and threshold configuration is kept in sync by a manager contract on Arbitrum One sending crosschain transactions.
Regular upgrades, Admin- and Owner actions originate from either the Arbitrum DAO or the non-emergency (Proposer-) Security Council on Arbitrum One and pass through multiple delays and timelocks before being executed at their destination. Contrarily, the three Emergency Security Council multisigs (one on each chain: Arbitrum One, Ethereum, Arbitrum Nova) can skip delays and directly access all admin- and upgrade functions of all smart contracts. These two general paths have the same destination: the respective UpgradeExecutor smart contract.
Regular upgrades are scheduled in the L2 Timelock. The proposer Security Council can do this directly and the Arbitrum DAO (ARB token holders and delegates) must meet a CoreGovernor-enforced 5% threshold of the votable tokens. The L2 Timelock queues the transaction for a 8d delay and then sends it to the Outbox contract on Ethereum. This incurs another delay (the challenge period) of 6d 8h. When that has passed, the L1 Timelock delays for additional 3d. Both timelocks serve as delays during which the transparent transaction contents can be audited, and, in the case of the final L1 timelock, cancelled by the Emergency Security Council. Finally, the transaction can be executed, calling Admin- or Owner restricted functions of the respective destination smart contracts through the UpgradeExecutor on Ethereum. If the predefined transaction destination is Arbitrum One or -Nova, this last call is executed on L2 through the canonical bridge and the aliased address of the L1 Timelock.
Operator roles like the Sequencers and Validators are managed using the same paths. Sequencer changes can be delegated to a Batch Poster Manager role.
Transactions targeting the Arbitrum DAO Treasury can be scheduled in the 3d Treasury Timelock by meeting a TreasuryGovernor-enforced 3% threshold of votable ARB tokens. The Security Council cannot regularly cancel these transactions or schedule different ones but can overwrite them anyway by having upgrade permissions for all the underlying smart contracts.
The DA committee has the following members:
Ethereum
Roles:
Can submit transaction batches or commitments to the SequencerInbox contract on the host chain.
Actors:
A timelock with access control. The current minimum delay is 3d. Proposals that passed their minimum delay can be executed by the anyone.
- Can upgrade with no delay
- SequencerInbox
via
- acting via UpgradeExecutor → ProxyAdmin - CustomGateway
via
- acting via UpgradeExecutor → ProxyAdmin 3 - RollupEventInbox
via
- acting via UpgradeExecutor → ProxyAdmin - UpgradeExecutor
via
- acting via UpgradeExecutor → ProxyAdmin 2 - ERC20Gateway
via
- acting via UpgradeExecutor → ProxyAdmin 3 - Bridge
via
- acting via UpgradeExecutor → ProxyAdmin - Inbox
via
- acting via UpgradeExecutor → ProxyAdmin - GatewayRouter
via
- acting via UpgradeExecutor → ProxyAdmin 3 - Outbox
via
- acting via UpgradeExecutor → ProxyAdmin - L1Timelock
via
- acting via UpgradeExecutor → ProxyAdmin 2 - RollupProxy
via
- acting via UpgradeExecutor - EdgeChallengeManager
via
- acting via UpgradeExecutor → ProxyAdmin
- SequencerInbox
- Can interact with L1Timelock
- cancel queued transactions
via
- acting via UpgradeExecutor - update the minimum delay and manage all access control roles of the timelock
via
- acting via UpgradeExecutor
- cancel queued transactions
- Can interact with RollupProxy
- Pause and unpause and set important roles and parameters in the system contracts: Can delegate Sequencer management to a BatchPosterManager address, manage data availability and DACs, set the Sequencer-only window, introduce an allowList to the bridge and whitelist Inboxes/Outboxes
via
- acting via UpgradeExecutor
- Pause and unpause and set important roles and parameters in the system contracts: Can delegate Sequencer management to a BatchPosterManager address, manage data availability and DACs, set the Sequencer-only window, introduce an allowList to the bridge and whitelist Inboxes/Outboxes
- A Multisig with 9/12 threshold. It uses the following modules: UpgradeExecutor (Central contract defining the access control permissions for upgrading the system contract implementations).
- Can upgrade with no delay
- SequencerInbox
via
- acting via UpgradeExecutor → ProxyAdmin - CustomGateway
via
- acting via UpgradeExecutor → ProxyAdmin 3 - RollupEventInbox
via
- acting via UpgradeExecutor → ProxyAdmin - UpgradeExecutor
via
- acting via UpgradeExecutor → ProxyAdmin 2 - ERC20Gateway
via
- acting via UpgradeExecutor → ProxyAdmin 3 - Bridge
via
- acting via UpgradeExecutor → ProxyAdmin - Inbox
via
- acting via UpgradeExecutor → ProxyAdmin - GatewayRouter
via
- acting via UpgradeExecutor → ProxyAdmin 3 - Outbox
via
- acting via UpgradeExecutor → ProxyAdmin - L1Timelock
via
- acting via UpgradeExecutor → ProxyAdmin 2 - RollupProxy
via
- acting via UpgradeExecutor - EdgeChallengeManager
via
- acting via UpgradeExecutor → ProxyAdmin
- SequencerInbox
- Can interact with L1Timelock
- cancel queued transactions
via
- acting via UpgradeExecutor - update the minimum delay and manage all access control roles of the timelock
via
- acting via UpgradeExecutor
- cancel queued transactions
- Can interact with RollupProxy
- Pause and unpause and set important roles and parameters in the system contracts: Can delegate Sequencer management to a BatchPosterManager address, manage data availability and DACs, set the Sequencer-only window, introduce an allowList to the bridge and whitelist Inboxes/Outboxes
via
- acting via UpgradeExecutor
- Pause and unpause and set important roles and parameters in the system contracts: Can delegate Sequencer management to a BatchPosterManager address, manage data availability and DACs, set the Sequencer-only window, introduce an allowList to the bridge and whitelist Inboxes/Outboxes
Participants (12):
fred - Arbitrum 2Michael Lewellen - blockaidCertora 2DennisonBertram-TallyJohnMorrow-GauntletGoncaloMagalhaes-Immunefigzeon-OffchainLabsEmilianoBonassi-ConduitGriffGreen-GivethStevenThornton-OpenZeppelinbartek.eth-L2BEATyoav.eth-EF- A Multisig with 4/6 threshold.
- Can interact with SequencerInbox
- Add/remove batchPosters (Sequencers)
Arbitrum Nova
Actors:
- A Multisig with 9/12 threshold. It uses the following modules: L2UpgradeExecutor (Central contract defining the access control permissions for upgrading the system contract implementations).
- Can upgrade with no delay
- L2GatewayRouter
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2WethGateway
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2UpgradeExecutor
via
- acting via L2UpgradeExecutor → L2ProxyAdmin - L2ARBGateway
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2ERC20Gateway
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2ArbitrumToken
via
- acting via L2UpgradeExecutor → L2ProxyAdmin
- L2GatewayRouter
- Can upgrade with no delay
- L2GatewayRouter
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2WethGateway
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2UpgradeExecutor
via
- acting via L2UpgradeExecutor → L2ProxyAdmin - L2ARBGateway
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2ERC20Gateway
via
- acting via L2UpgradeExecutor → L2GatewaysProxyAdmin - L2ArbitrumToken
via
- acting via L2UpgradeExecutor → L2ProxyAdmin
- L2GatewayRouter
Ethereum
A sequencer (registered in this contract) can submit transaction batches or commitments here.
- Roles:
- admin: ProxyAdmin; ultimately L1Timelock, SecurityCouncil
- batchPosterManager: BatchPosterManagerMultisig
- batchPosters: EOA 1, EOA 2
Escrow contract for the project’s gas token (can be different from ETH). Keeps a list of allowed Inboxes and Outboxes for canonical bridge messaging.
- Roles:
- admin: ProxyAdmin; ultimately L1Timelock, SecurityCouncil
- This contract stores the following tokens: ETH.
Central contract for the project’s configuration like its execution logic hash (wasmModuleRoot) and addresses of the other system contracts. Entry point for Proposers creating new assertions (state commitments) and Challengers submitting fraud proofs (In the Orbit stack, these two roles are both called Validators).
- Roles:
- admin: UpgradeExecutor; ultimately L1Timelock, SecurityCouncil
- owner: UpgradeExecutor; ultimately L1Timelock, SecurityCouncil
Contract that implements the main challenge protocol logic of the fraud proof system.
- Roles:
- admin: ProxyAdmin; ultimately L1Timelock, SecurityCouncil
Central contract defining the access control permissions for upgrading the system contract implementations.
- Roles:
- admin: ProxyAdmin 2; ultimately L1Timelock, SecurityCouncil
- executors: L1Timelock, SecurityCouncil
Escrows deposited ERC-20 assets for the canonical Bridge. Upon depositing, a generic token representation will be minted at the destination. Withdrawals are initiated by the Outbox contract.
- Roles:
- admin: ProxyAdmin 3; ultimately L1Timelock, SecurityCouncil
- This contract can store any token.
Escrows deposited assets for the canonical bridge that are externally governed or need custom token contracts with e.g. minting rights or upgradeability.
- Roles:
- admin: ProxyAdmin 3; ultimately L1Timelock, SecurityCouncil
- This contract can store any token.
This routing contract maps tokens to the correct escrow (gateway) to be then bridged with canonical messaging.
- Roles:
- admin: ProxyAdmin 3; ultimately L1Timelock, SecurityCouncil
Helper contract sending configuration data over the bridge during the systems initialization.
- Roles:
- admin: ProxyAdmin; ultimately L1Timelock, SecurityCouncil
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
- Roles:
- owner: UpgradeExecutor
- Roles:
- owner: UpgradeExecutor
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Simple escrow that accepts tokens and allows to configure permissioned addresses that can access the tokens.
- This contract stores the following tokens: DAI.
- Roles:
- owner: UpgradeExecutor
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Arbitrum Nova
Central contract defining the access control permissions for upgrading the system contract implementations.
- Roles:
- admin: L2ProxyAdmin; ultimately L1Timelock, L2SecurityCouncilEmergency
- executors: L1Timelock, L2SecurityCouncilEmergency
Router managing token <–> gateway mapping on L2.
- Roles:
- admin: L2GatewaysProxyAdmin; ultimately L1Timelock, L2SecurityCouncilEmergency
This contract receives all SurplusFees: Transaction fee component that covers the cost beyond that covered by the L2 Base Fee during chain congestion. They are withdrawable to a configurable set of recipients.
This contract receives all SurplusFees: Transaction fee component that covers the cost beyond that covered by the L2 Base Fee during chain congestion. They are withdrawable to a configurable set of recipients.
- Roles:
- owner: L2UpgradeExecutor
- Roles:
- admin: L2GatewaysProxyAdmin; ultimately L1Timelock, L2SecurityCouncilEmergency
- Roles:
- owner: L2UpgradeExecutor
- Roles:
- admin: L2ProxyAdmin; ultimately L1Timelock, L2SecurityCouncilEmergency
Value Secured is calculated based on these smart contracts and tokens:
Main entry point for users depositing ERC20 tokens. Upon depositing, on L2 a generic, “wrapped” token will be minted.
Main entry point for users depositing ERC20 tokens that require minting a custom token on the L2.
Contract managing Inboxes and Outboxes. It escrows ETH sent to L2.
DAI Vault for custom DAI Gateway. Fully controlled by MakerDAO governance.
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).