Search
Search for projects by name or address
 Edgeless
Edgeless
Badges
About
Edgeless is an Orbit stack general-purpose Optimium without application layer fees. It uses ewETH as the native token, which is a wrapped version of underlying investment strategies.
Badges
About
Edgeless is an Orbit stack general-purpose Optimium without application layer fees. It uses ewETH as the native token, which is a wrapped version of underlying investment strategies.
Why is the project listed in others?
Consequence: projects without a sufficiently decentralized set of challengers rely on few entities to safely update the state. A small set of challengers can collude with the proposer to finalize an invalid state, which can cause loss of funds.
Consequence: projects without a sufficiently decentralized data availability committee rely on few entities to safely attest data availability on Ethereum. A small set of entities can collude with the proposer to finalize an unavailable state, which can cause loss of funds.
Learn more about the recategorisation here.
2024 Mar 22 — 2026 May 29
The section shows the operating costs that L2s pay to Ethereum.
2024 Mar 22 — 2026 May 29
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
2024 Mar 22 — 2026 May 30
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
No actor outside of the single Proposer can submit fraud proofs. Interactive proofs (INT) require multiple transactions over time to resolve. The challenge protocol can be subject to delay attacks. There is a 6d 8h challenge period.
Proof construction relies fully on data that is NOT published onchain. There exists a Data Availability Committee (DAC) with a threshold of 1/1 that is tasked with protecting and supplying the data.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Anyone can become a Proposer after 12d 17h of inactivity from the currently whitelisted Proposers.
Set of parties responsible for signing and attesting to the availability of data.
There are no onchain assets at risk of being slashed in case of a data withholding attack, and the committee members are not publicly known.
There is no fraud detection mechanism in place. A data withholding attack can only be detected by nodes downloading the full data from the DA layer.
The committee does not meet basic security standards, either due to insufficient size, lack of member diversity, or poorly defined threshold parameters. The system lacks an effective DA bridge and it is reliant on the assumption of an honest sequencer, creating significant risks to data integrity and availability.
There is no delay in the upgradeability of the bridge. Users have no time to exit the system before the bridge implementation update is completed.
The relayer role is permissioned, and the DA bridge does not have a Security Council or a governance mechanism to propose new relayers. In case of relayer failure, the DA bridge will halt and be unable to recover without the intervention of a centralized entity.
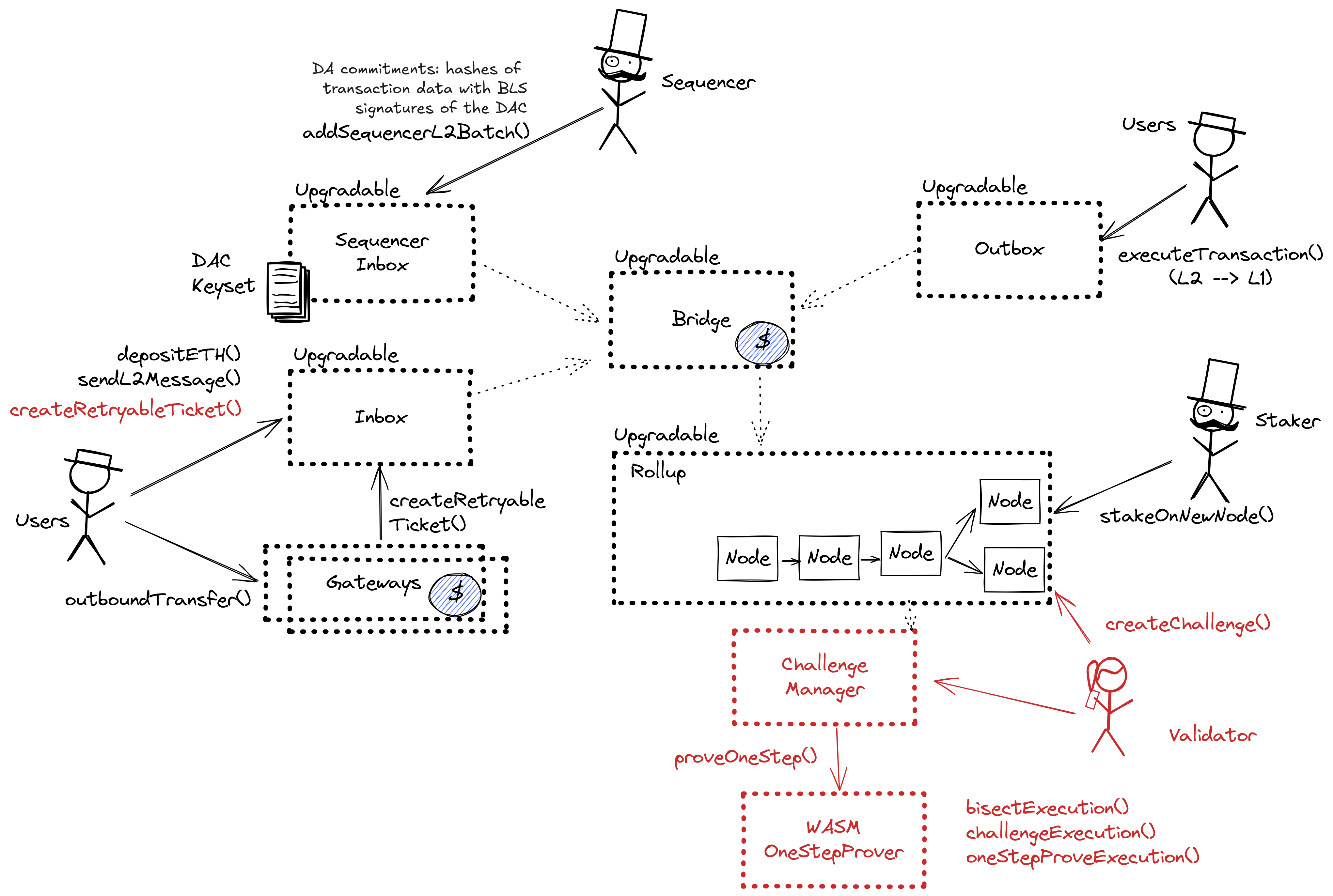
Architecture

The DAC uses a data availability solution built on the AnyTrust protocol. It is composed of the following components:
- Sequencer Inbox: Main entry point for the Sequencer submitting transaction batches.
- Data Availability Committee (DAC): A group of members responsible for storing and providing data on demand.
- Data Availability Certificate (DACert): A commitment ensuring that data blobs are available without needing full data posting on the L1 chain.
Committee members run servers that support APIs for storing and retrieving data blobs. The Sequencer API allows the rollup Sequencer to submit data blobs for storage, while the REST API enables anyone to fetch data by hash. When the Sequencer produces a data batch, it sends the batch along with an expiration time to Committee members, who store it and sign it. Once enough signatures are collected, the Sequencer aggregates them into a valid DACert and posts it to the L1 chain inbox. If the Sequencer fails to collect enough signatures, it falls back to posting the full data to the L1 chain as calldata.
A DACert includes a hash of the data block, an expiration time, and proof that the required threshold of Committee members have signed off on the data. The proof consists of a hash of the Keyset used in signing, a bitmap indicating which members signed, and a BLS aggregated signature. L2 nodes reading from the sequencer inbox verify the certificate’s validity by checking the number of signers, the aggregated signature, and that the expiration time is at least two weeks ahead of the L2 timestamp. If the DACert is valid, it provides a proof that the corresponding data is available from honest committee members.
DA Bridge Architecture

The DA commitments are posted to the destination chain through the sequencer inbox, using the inbox as a DA bridge. The DA commitment consists of Data Availability Certificate (DACert), including a hash of the data block, an expiration time, and a proof that the required threshold of Committee members have signed off on the data. The sequencer distributes the data and collects signatures from Committee members offchain. Only the DACert is posted by the sequencer to the destination chain inbox (the DA bridge), achieving destination chain transaction ordering finality in a single onchain transaction.
Funds can be lost if a malicious committee attests to an invalid data availability certificate.
Funds can be lost if the bridge contract or its dependencies receive a malicious code upgrade. There is no delay on code upgrades.
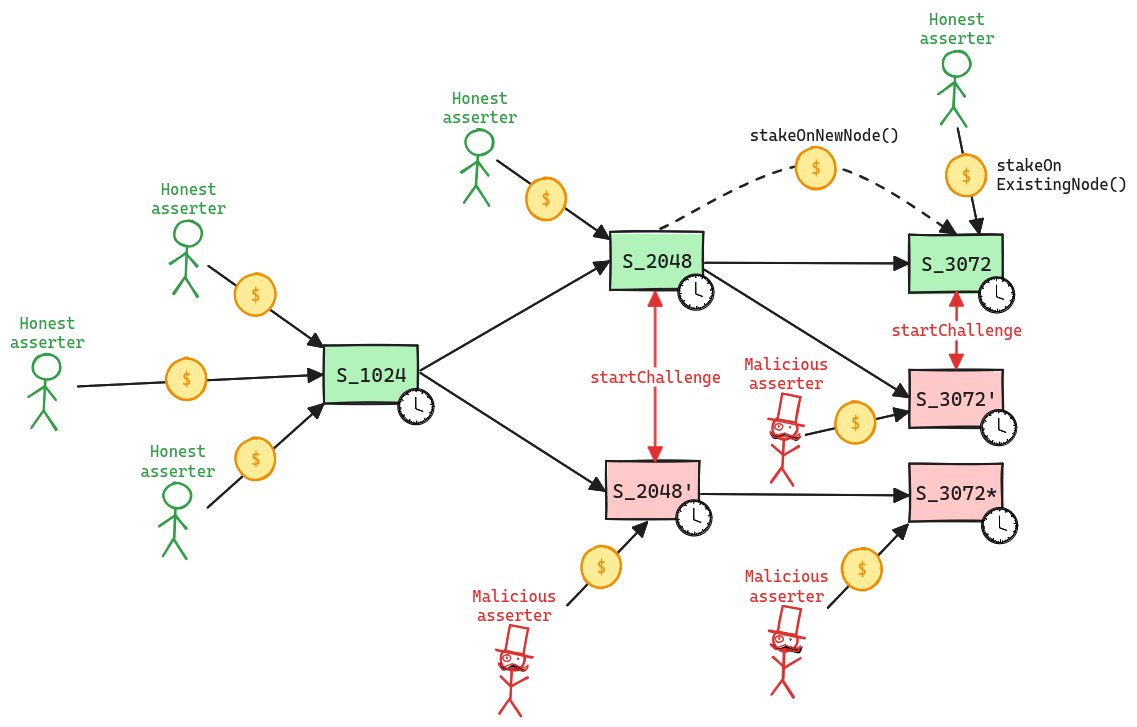
Updates to the system state can be proposed and challenged by a set of whitelisted validators. If a state root passes the challenge period, it is optimistically considered correct and made actionable for withdrawals.
Whitelisted validators propose state roots as children of a previous state root. A state root can have multiple conflicting children. This structure forms a graph, and therefore, in the contracts, state roots are referred to as nodes. Each proposal requires a stake, currently set to 0.1 ETH, that can be slashed if the proposal is proven incorrect via a fraud proof. Stakes can be moved from one node to one of its children, either by calling stakeOnExistingNode or stakeOnNewNode. New nodes cannot be created faster than the minimum assertion period by the same validator, currently set to 15m. The oldest unconfirmed node can be confirmed if the challenge period has passed and there are no siblings, and rejected if the parent is not a confirmed node or if the challenge period has passed and no one is staked on it.
Funds can be stolen if none of the whitelisted verifiers checks the published state. Fraud proofs assume at least one honest and able validator (CRITICAL).
A challenge can be started between two siblings, i.e. two different state roots that share the same parent, by calling the startChallenge function. Validators cannot be in more than one challenge at the same time, meaning that the protocol operates with partial concurrency. Since each challenge lasts 6d 8h, this implies that the protocol can be subject to delay attacks, where a malicious actor can delay withdrawals as long as they are willing to pay the cost of losing their stakes. If the protocol is delayed attacked, the new stake requirement increases exponentially for each challenge period of delay. Challenges are played via a bisection game, where asserter and challenger play together to find the first instruction of disagreement. Such instruction is then executed onchain in the WASM OneStepProver contract to determine the winner, who then gets half of the stake of the loser. As said before, a state root is rejected only when no one left is staked on it. The protocol does not enforces valid bisections, meaning that actors can propose correct initial claim and then provide incorrect midpoints.
Program Hashes
Name | Hash | Repository | Verification | Used in | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
0x1848...aa39 | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2025 April 09, 12:29 UTCHigh severity38changesSmall Bridge upgrade introducing custom decimals for the gas token and eip 7702 support (known contracts).
Small Bridge upgrade introducing custom decimals for the gas token and eip 7702 support (known contracts).
| contract Bridge (0x6B595398152999bBc759D5D8ed8169793F915488) { | |
| +++ description: Escrow contract for the project's gas token (can be different from ETH). Keeps a list of allowed Inboxes and Outboxes for canonical bridge messaging. | |
| sourceHashes.1: | |
| - | "0x057de68a7007d55f4394ba6eafb2c802efcaf13583ff9342ea4d0ee3924d9be1" |
| + | "0xa7e3f6c355703ed46fcb2156862c4f01792b87beb10a87a81ce3bd5beee79b67" |
| sourceHashes.0: | |
| - | "0xa7e3f6c355703ed46fcb2156862c4f01792b87beb10a87a81ce3bd5beee79b67" |
| + | "0x32c73666d391a33c17183e4ab20bcb0f2b925d8a99da436d2ff99c13f403e289" |
| values.$implementation: | |
| - | "0x7EfcB76D0e2E776A298aAa603d433336e5F8b6ab" |
| + | "0x75Ef99D9D2c166579fEB09c9015CC99e0Ca44a10" |
| values.$pastUpgrades.1: | |
| + | ["2024-03-22T01:00:23.000Z","0x9a69d7f74c80826a8d5c84398da524ff12f3bef236ff9115094e086382a33810",["0x7EfcB76D0e2E776A298aAa603d433336e5F8b6ab"]] |
| values.$pastUpgrades.0.2.0: | |
| - | "0x7EfcB76D0e2E776A298aAa603d433336e5F8b6ab" |
| + | "0x75Ef99D9D2c166579fEB09c9015CC99e0Ca44a10" |
| values.$pastUpgrades.0.1: | |
| - | "0x9a69d7f74c80826a8d5c84398da524ff12f3bef236ff9115094e086382a33810" |
| + | "0x6bbb4ef7e5fa8da1f41817558cbe9615c86c81a59d9eeecb90085ab91dd1beea" |
| values.$pastUpgrades.0.0: | |
| - | "2024-03-22T01:00:23.000Z" |
| + | "2025-04-07T16:23:23.000Z" |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| values.nativeTokenDecimals: | |
| + | 18 |
| } |
| contract Inbox (0xf51551afD112a50Fc5EDa0454111078fE6E6096E) { | |
| +++ description: Facilitates sending L1 to L2 messages like depositing ETH, but does not escrow funds. | |
| sourceHashes.0: | |
| - | "0xcb390b491549387c8fcc09fb22fbea7adf54cc74b7247a0c738369ddd7049b92" |
| + | "0x25984fdfffb8141859c99299fb29e7a7460732d77111e5fe23792baa99f336a3" |
| values.$implementation: | |
| - | "0x31fAAAB44e74eB408d1FC69A14806B4b9cA09da2" |
| + | "0xd29ED48868E393248645680ee4432999812eb30e" |
| values.$pastUpgrades.1: | |
| + | ["2024-03-22T01:00:23.000Z","0x9a69d7f74c80826a8d5c84398da524ff12f3bef236ff9115094e086382a33810",["0x31fAAAB44e74eB408d1FC69A14806B4b9cA09da2"]] |
| values.$pastUpgrades.0.2: | |
| - | "0x9a69d7f74c80826a8d5c84398da524ff12f3bef236ff9115094e086382a33810" |
| + | "0x1ead0e15dc06839305e7101c4f6ceeea0573e53ed013c571e3e66cd988906a1c" |
| values.$pastUpgrades.0.1: | |
| - | ["0x31fAAAB44e74eB408d1FC69A14806B4b9cA09da2"] |
| + | "2025-04-07T18:51:47.000Z" |
| values.$pastUpgrades.0.0: | |
| - | "2024-03-22T01:00:23.000Z" |
| + | ["0xd29ED48868E393248645680ee4432999812eb30e"] |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| } |
| contract SequencerInbox (0xFfbf2b49524e09B1F1fBcA707B830e79c68c2086) { | |
| +++ description: A sequencer (registered in this contract) can submit transaction batches or commitments here. | |
| sourceHashes.0: | |
| - | "0x50cf57b01499408fa99da27cf0fee96ec30f0d40667d1aa090c442bc80f0636b" |
| + | "0x6bb86ac4bd0d31e049f543fcf0a8f94c952252222f115246ef9d5b8104d803cc" |
| values.$implementation: | |
| - | "0x5054375f50f36812d1C45E6091b167aaFC3cA5b6" |
| + | "0x87Ca4B22A63c546eB998c26Ebec0aFE2821FC03C" |
| values.$pastUpgrades.2: | |
| + | ["2025-04-07T18:51:47.000Z","0x1ead0e15dc06839305e7101c4f6ceeea0573e53ed013c571e3e66cd988906a1c",["0x87Ca4B22A63c546eB998c26Ebec0aFE2821FC03C"]] |
| values.$upgradeCount: | |
| - | 2 |
| + | 3 |
| values.reader4844: | |
| - | "0x4Cc63d9A2aA0E0168F5EDfFA2D31d1F8cF0C270E" |
| + | "0x6607189DAA612804Bf9C992e19fba5D7E0740cED" |
| } |
2024 November 25, 10:42 UTCHigh severity35changesArbOS v32 upgrade to known contracts with unused fastConfirmer.
ArbOS v32 upgrade to known contracts with unused fastConfirmer.
| - | Status: DELETED |
| contract OneStepProver0 (0x05cd95968709034744797cC37a58FD43fabFff9F) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| - | Status: DELETED |
| contract OneStepProverHostIo (0x34da361b71484F3F6B459531852ff4a60C36fE55) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| - | Status: DELETED |
| contract OneStepProverMemory (0x7B3cF41acea4230183e4e367c456d878467925Bf) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| contract RollupProxy (0x890025891508a463A636f81D2f532a97210240de) { | |
| +++ description: Central contract for the project's configuration like its execution logic hash (`wasmModuleRoot`) and addresses of the other system contracts. Entry point for Proposers creating new Rollup Nodes (state commitments) and Challengers submitting fraud proofs (In the Orbit stack, these two roles are both held by the Validators). | |
| sourceHashes.2: | |
| - | "0xef94a66bd5339efd18fb9ca1f8031482e7ef7bbe6c5a0a10fae254ab83712406" |
| + | "0x7ee21b18b2e18c636bfafc08ff72692cc43302b2599ba75f0abad67282866dd5" |
| sourceHashes.1: | |
| - | "0x8b48118fe606012c0dcac2ccc1821785935aec89fab8f219f47b32c482b0017e" |
| + | "0x9349e73cbc2d2b818c1d79711574ba210b56249d8d3845bc78c776caf8f8ff42" |
| values.$implementation.1: | |
| - | "0x660ea1675F7323dC3Ba0c8dDFB593225Eb01E3C1" |
| + | "0x4944f77757AE7050A7EF843FacA82FC449aB5901" |
| values.$implementation.0: | |
| - | "0x0aE4dD666748bF0F6dB5c149Eab1D8aD27820A6A" |
| + | "0xA798E033b1B3976d77a4A6aeDC496873a7264156" |
| values.$pastUpgrades.1: | |
| + | ["2024-11-24T16:28:35.000Z","0xf0976079c29124f6917774cf38e659b554b89d59a451fd9c6ebe546e87b53cbd",["0xA798E033b1B3976d77a4A6aeDC496873a7264156","0x4944f77757AE7050A7EF843FacA82FC449aB5901"]] |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| +++ description: ArbOS version derived from known wasmModuleRoots. | |
| values.arbOsFromWmRoot: | |
| - | "ArbOS v20 wasmModuleRoot" |
| + | "ArbOS v32 wasmModuleRoot" |
| +++ description: Root hash of the WASM module used for execution, like a fingerprint of the L2 logic. Can be associated with ArbOS versions. | |
| values.wasmModuleRoot: | |
| - | "0x8b104a2e80ac6165dc58b9048de12f301d70b02a0ab51396c22b4b4b802a16a4" |
| + | "0x184884e1eb9fefdc158f6c8ac912bb183bf3cf83f0090317e0bc4ac5860baa39" |
| values.anyTrustFastConfirmer: | |
| + | "0x0000000000000000000000000000000000000000" |
| } |
| contract ChallengeManager (0x893057442A952E3254CA53d007AD6BBB502f557e) { | |
| +++ description: Contract that allows challenging state roots. Can be called through the RollupProxy by Validators or the UpgradeExecutor. | |
| sourceHashes.1: | |
| - | "0x58a6261c83c2766f749641902ad6fdb695ea189d2747f073b57a8f35b9a547e5" |
| + | "0x1a095768302d7d1c3d02375eaa3341833b4f1aaac707e1c608bce478c87cbf27" |
| values.$implementation: | |
| - | "0x38B79f7D08326833051AA4D0a119D8095247716f" |
| + | "0x92726c81BbECbC9b871304B290b412EC78cF842b" |
| values.$pastUpgrades.2: | |
| + | ["2024-11-24T16:28:35.000Z","0xf0976079c29124f6917774cf38e659b554b89d59a451fd9c6ebe546e87b53cbd",["0x92726c81BbECbC9b871304B290b412EC78cF842b"]] |
| values.$upgradeCount: | |
| - | 2 |
| + | 3 |
| values.osp: | |
| - | "0xcd6fda29E15919de86De6E94C348776d544cFa6E" |
| + | "0x1F58949AB4C6A65C4055f45fdF9297C5F216CD95" |
| } |
| - | Status: DELETED |
| contract OneStepProofEntry (0xcd6fda29E15919de86De6E94C348776d544cFa6E) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| - | Status: DELETED |
| contract OneStepProverMath (0xdFa7A279F4DF9dd16cA91094ac429eC5B12EDB94) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProofEntry (0x1F58949AB4C6A65C4055f45fdF9297C5F216CD95) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverHostIo (0x251E34E4644D06b319AD39c602b857E47cCa13C3) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverMemory (0x6119D59799E83329847de25Dc787A0D9ab4c0323) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProver0 (0xaac292Cb9a205A140003775529181787fdbc4DC6) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverMath (0xE6068c35d4FB1899b9419cE3e7B66D318C652847) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
2024 November 21, 10:53 UTCHigh severity38changesArbOS v20 upgrade (to known contracts). Move to discoverydriven data.
ArbOS v20 upgrade (to known contracts). Move to discoverydriven data.
| - | Status: DELETED |
| contract OneStepProofEntry (0x09824fe72BFF474d16D9c2774432E381BBD60662) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| - | Status: DELETED |
| contract OneStepProverMemory (0x4811500e0d376Fa8d2EA3CCb7c61E0afB4F5A7f1) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| contract RollupProxy (0x890025891508a463A636f81D2f532a97210240de) { | |
| +++ description: Central contract for the project's configuration like its execution logic hash (`wasmModuleRoot`) and addresses of the other system contracts. Entry point for Proposers creating new Rollup Nodes (state commitments) and Challengers submitting fraud proofs (In the Orbit stack, these two roles are both held by the Validators). | |
| +++ description: ArbOS version derived from known wasmModuleRoots. | |
| values.arbOsFromWmRoot: | |
| - | "ArbOS v11.1 wasmModuleRoot" |
| + | "ArbOS v20 wasmModuleRoot" |
| +++ description: Root hash of the WASM module used for execution, like a fingerprint of the L2 logic. Can be associated with ArbOS versions. | |
| values.wasmModuleRoot: | |
| - | "0x68e4fe5023f792d4ef584796c84d710303a5e12ea02d6e37e2b5e9c4332507c4" |
| + | "0x8b104a2e80ac6165dc58b9048de12f301d70b02a0ab51396c22b4b4b802a16a4" |
| } |
| contract ChallengeManager (0x893057442A952E3254CA53d007AD6BBB502f557e) { | |
| +++ description: Contract that allows challenging state roots. Can be called through the RollupProxy by Validators or the UpgradeExecutor. | |
| sourceHashes.1: | |
| - | "0x7e1cd1e10119e118ffaa576ddbe1c0f9810a0859a4bf2f65a4ff596c0ed4183d" |
| + | "0x58a6261c83c2766f749641902ad6fdb695ea189d2747f073b57a8f35b9a547e5" |
| values.$implementation: | |
| - | "0xEe9E5546A11Cb5b4A86e92DA05f2ef75C26E4754" |
| + | "0x38B79f7D08326833051AA4D0a119D8095247716f" |
| values.$pastUpgrades.1: | |
| + | ["2024-11-18T17:15:59.000Z","0xbc68abaef39524b8b9ee1cf1d43eee32963c1c9c3ebf91e38a9e40d9b1fadcb3",["0x38B79f7D08326833051AA4D0a119D8095247716f"]] |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| values.osp: | |
| - | "0x09824fe72BFF474d16D9c2774432E381BBD60662" |
| + | "0xcd6fda29E15919de86De6E94C348776d544cFa6E" |
| } |
| - | Status: DELETED |
| contract OneStepProverMath (0x89AF7C4C2198c426cFe6E86de0680A0850503e06) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| - | Status: DELETED |
| contract OneStepProverHostIo (0x99a2A31300816C1FA3f40818AC9280fe7271F878) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| - | Status: DELETED |
| contract OneStepProver0 (0xDf94F0474F205D086dbc2e66D69a856FCf520622) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| contract SequencerInbox (0xFfbf2b49524e09B1F1fBcA707B830e79c68c2086) { | |
| +++ description: A sequencer (registered in this contract) can submit transaction batches or commitments here. | |
| sourceHashes.1: | |
| - | "0x08792f333db7e8a060c38033f92e3fc10c30e2648c56fc49c7460ee1c94343a0" |
| + | "0x50cf57b01499408fa99da27cf0fee96ec30f0d40667d1aa090c442bc80f0636b" |
| values.$implementation: | |
| - | "0x873484Ba63353C8b71210ce123B465512d408B27" |
| + | "0x5054375f50f36812d1C45E6091b167aaFC3cA5b6" |
| values.$pastUpgrades.1: | |
| + | ["2024-11-18T17:15:59.000Z","0xbc68abaef39524b8b9ee1cf1d43eee32963c1c9c3ebf91e38a9e40d9b1fadcb3",["0x5054375f50f36812d1C45E6091b167aaFC3cA5b6"]] |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| values.batchPosterManager: | |
| + | "0x0000000000000000000000000000000000000000" |
| values.BROTLI_MESSAGE_HEADER_FLAG: | |
| + | "0x00" |
| values.DAS_MESSAGE_HEADER_FLAG: | |
| + | "0x80" |
| values.DATA_BLOB_HEADER_FLAG: | |
| + | "0x50" |
| values.isUsingFeeToken: | |
| + | true |
| values.reader4844: | |
| + | "0x4Cc63d9A2aA0E0168F5EDfFA2D31d1F8cF0C270E" |
| values.TREE_DAS_MESSAGE_HEADER_FLAG: | |
| + | "0x08" |
| values.ZERO_HEAVY_MESSAGE_HEADER_FLAG: | |
| + | "0x20" |
| } |
| + | Status: CREATED |
| contract OneStepProver0 (0x05cd95968709034744797cC37a58FD43fabFff9F) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverHostIo (0x34da361b71484F3F6B459531852ff4a60C36fE55) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverMemory (0x7B3cF41acea4230183e4e367c456d878467925Bf) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProofEntry (0xcd6fda29E15919de86De6E94C348776d544cFa6E) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverMath (0xdFa7A279F4DF9dd16cA91094ac429eC5B12EDB94) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
2024 August 14, 07:23 UTC3changesThe EOA that was able to execute upgrades was removed. Now there's only the 3/4 multisig left.
The EOA that was able to execute upgrades was removed. Now there’s only the 3/4 multisig left.
| contract UpgradeExecutor (0xc213d433802ea473e23623476b26FB12e9B4eFe6) { | |
| +++ description: None | |
| values.accessControl.EXECUTOR_ROLE.members.1: | |
| - | "0x4dE424B0BDe70504Ad7b3c644EaAd052F4D993b4" |
| values.accessControl.EXECUTOR_ROLE.members.0: | |
| - | "0xa43ce4721Ac0faB33E8636e0DDB55E76e3EFF461" |
| + | "0x4dE424B0BDe70504Ad7b3c644EaAd052F4D993b4" |
| } |
2024 July 16, 10:40 UTC27changesOrbit chain with investment strategies baked in the deposit contract.
Orbit chain with investment strategies baked in the deposit contract.
Initial discovery
| + | Status: CREATED |
| contract OneStepProofEntry (0x09824fe72BFF474d16D9c2774432E381BBD60662) | |
| +++ description: None |
| + | Status: CREATED |
| contract StakingManager (0x1e6d08769be5Dc83d38C64C5776305Ad6F01c227) | |
| +++ description: None |
| + | Status: CREATED |
| contract (0x27C7Bfd2cC11429e9b80c443b42FDBe4754F6c91) | |
| +++ description: None |
| + | Status: CREATED |
| contract ValidatorUtils (0x2b0E04Dc90e3fA58165CB41E2834B44A56E766aF) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProverMemory (0x4811500e0d376Fa8d2EA3CCb7c61E0afB4F5A7f1) | |
| +++ description: None |
| + | Status: CREATED |
| contract OrbitProxyAdmin (0x48E84C45fE99859B1D72FA56Ce5D3c76FF2F7006) | |
| +++ description: None |
| + | Status: CREATED |
| contract ExecutorMultisig (0x4dE424B0BDe70504Ad7b3c644EaAd052F4D993b4) | |
| +++ description: None |
| + | Status: CREATED |
| contract Outbox (0x5e8749760c5051fF80b73319cCf4d05ef9959563) | |
| +++ description: None |
| + | Status: CREATED |
| contract L1ERC20Gateway (0x6a1B2ea25c3099CAFcbd4E60a3Ae251E52B69e78) | |
| +++ description: None |
| + | Status: CREATED |
| contract Bridge (0x6B595398152999bBc759D5D8ed8169793F915488) | |
| +++ description: None |
| + | Status: CREATED |
| contract EdgelessDeposit (0x7E0bc314535f430122caFEF18eAbd508d62934bf) | |
| +++ description: None |
| + | Status: CREATED |
| contract RollupProxy (0x890025891508a463A636f81D2f532a97210240de) | |
| +++ description: Manages rollup components, list of Stakers and Validators. Entry point for Validators creating new Rollup Nodes (state commits) and Challengers submitting fraud proofs. |
| + | Status: CREATED |
| contract ChallengeManager (0x893057442A952E3254CA53d007AD6BBB502f557e) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProverMath (0x89AF7C4C2198c426cFe6E86de0680A0850503e06) | |
| +++ description: None |
| + | Status: CREATED |
| contract L1CustomGateway (0x99790790B030CF116efed1c7577e2262072EfCc9) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProverHostIo (0x99a2A31300816C1FA3f40818AC9280fe7271F878) | |
| +++ description: None |
| + | Status: CREATED |
| contract ValidatorWalletCreator (0x9CAd81628aB7D8e239F1A5B497313341578c5F71) | |
| +++ description: None |
| + | Status: CREATED |
| contract StrategiesProxyAdmin (0xa5f13fbc57f14Bf322C900Cae0F67b4819364281) | |
| +++ description: None |
| + | Status: CREATED |
| contract L1OrbitGatewayRouter (0xb47D14b4282DF795E036e9Ea43E54C31FCB0eCAC) | |
| +++ description: None |
| + | Status: CREATED |
| contract RenzoStrategy (0xBCc1Ceb75De4BBb75918627E7CB301DF9Ccc8aF9) | |
| +++ description: None |
| + | Status: CREATED |
| contract EthStrategy (0xbD95aa0f68B95e6C01d02F1a36D8fde29C6C8e7b) | |
| +++ description: None |
| + | Status: CREATED |
| contract UpgradeExecutor (0xc213d433802ea473e23623476b26FB12e9B4eFe6) | |
| +++ description: None |
| + | Status: CREATED |
| contract WrappedToken (0xcD0aa40948c662dEDd9F157085fd6369A255F2f7) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProver0 (0xDf94F0474F205D086dbc2e66D69a856FCf520622) | |
| +++ description: None |
| + | Status: CREATED |
| contract Inbox (0xf51551afD112a50Fc5EDa0454111078fE6E6096E) | |
| +++ description: None |
| + | Status: CREATED |
| contract ERC20RollupEventInbox (0xFa213CdA43f879FfaF17170B6E3b3AbE9900cAB1) | |
| +++ description: None |
| + | Status: CREATED |
| contract SequencerInbox (0xFfbf2b49524e09B1F1fBcA707B830e79c68c2086) | |
| +++ description: State batches / commitments get posted here. |
The system has a centralized sequencer
While forcing transaction is open to anyone the system employs a privileged sequencer that has priority for submitting transaction batches and ordering transactions.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly. After a delay of 1d in which a Sequencer has failed to include a transaction that was directly posted to the smart contract, it can be forcefully included by anyone on the host chain, which finalizes its ordering.
Delayed forced transactions
To force transactions from the host chain, users must first enqueue “delayed” messages in the “delayed” inbox of the Bridge contract. Only authorized Inboxes are allowed to enqueue delayed messages, and the so-called Inbox contract is the one used as the entry point by calling the sendMessage or sendMessageFromOrigin functions. If the centralized sequencer doesn’t process the request within some time bound, users can call the forceInclusion function on the SequencerInbox contract to include the message in the canonical chain. The time bound is hardcoded to be 1d.
Autonomous exit
Users can (eventually) exit the system by pushing the transaction on L1 and providing the corresponding state root. The only way to prevent such withdrawal is via an upgrade.
EVM compatible smart contracts are supported
Arbitrum One uses Nitro technology that allows running fraud proofs by executing EVM code on top of WASM.

Ethereum
Roles:
Can submit transaction batches or commitments to the SequencerInbox contract on the host chain.
Can propose new state roots (called nodes) and challenge state roots on the host chain.
Actors:
A Multisig with 3/4 threshold.
- Can upgrade with no delay
- Outbox UpgradeExecutor → OrbitProxyAdmin
- ERC20Gateway UpgradeExecutor → OrbitProxyAdmin
- Bridge UpgradeExecutor → OrbitProxyAdmin
- RollupProxy UpgradeExecutor
- ChallengeManager UpgradeExecutor → OrbitProxyAdmin
- CustomGateway UpgradeExecutor → OrbitProxyAdmin
- GatewayRouter UpgradeExecutor → OrbitProxyAdmin
- UpgradeExecutor UpgradeExecutor → OrbitProxyAdmin
- Inbox UpgradeExecutor → OrbitProxyAdmin
- RollupEventInbox UpgradeExecutor → OrbitProxyAdmin
- SequencerInbox UpgradeExecutor → OrbitProxyAdmin
- Can interact with RollupProxy
- Pause and unpause and set important roles and parameters in the system contracts: Can delegate Sequencer management to a BatchPosterManager address, manage data availability, DACs and the fastConfirmer role, set the Sequencer-only window, introduce an allowList to the bridge and whitelist Inboxes/Outboxes UpgradeExecutor
- A Validator - acting directly
- A Sequencer - acting directly
- Can upgrade with no delay
- StakingManager StrategiesProxyAdmin
- EdgelessDeposit StrategiesProxyAdmin
- RenzoStrategy StrategiesProxyAdmin
- EthStrategy StrategiesProxyAdmin

Ethereum
Central contract for the project’s configuration like its execution logic hash (wasmModuleRoot) and addresses of the other system contracts. Entry point for Proposers creating new Rollup Nodes (state commitments) and Challengers submitting fraud proofs (In the Orbit stack, these two roles are both held by the Validators).
- Roles:
- admin: UpgradeExecutor; ultimately EdgelessMultisig
- owner: UpgradeExecutor; ultimately EdgelessMultisig
- validators: EOA 1
Contract that allows challenging state roots. Can be called through the RollupProxy by Validators or the UpgradeExecutor.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
A sequencer (registered in this contract) can submit transaction batches or commitments here.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
- batchPosters: EOA 2
Central contract defining the access control permissions for upgrading the system contract implementations.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
- executors: EdgelessMultisig
Escrows deposited ERC-20 assets for the canonical Bridge. Upon depositing, a generic token representation will be minted at the destination. Withdrawals are initiated by the Outbox contract.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
Escrows deposited assets for the canonical bridge that are externally governed or need custom token contracts with e.g. minting rights or upgradeability.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
This routing contract maps tokens to the correct escrow (gateway) to be then bridged with canonical messaging.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
Manages strategies to be used with funds forwarded from the EdgelessDeposit contract.
- Roles:
- admin: StrategiesProxyAdmin; ultimately EOA 3
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
This contract implements view only utilities for validators.
- Roles:
- owner: UpgradeExecutor
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Receives deposits and issues ewETH tokens. Funds are forwarded to the StakingManger contract.
- Roles:
- admin: StrategiesProxyAdmin; ultimately EOA 3
- Roles:
- owner: EOA 3
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Deposits funds into the Renzo protocol.
- Roles:
- admin: StrategiesProxyAdmin; ultimately EOA 3
Deposits funds into the Lido protocol.
- Roles:
- admin: StrategiesProxyAdmin; ultimately EOA 3
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Helper contract sending configuration data over the bridge during the systems initialization.
- Roles:
- admin: OrbitProxyAdmin; ultimately EdgelessMultisig
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).
Program Hashes
Name | Hash | Repository | Verification | Used in | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
0x1848...aa39 | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||