Search
Search for projects by name or address
 Kinto
Kinto
There are impactful changes and part of the information might be outdated.
Kinto shut down on September 30, 2025. Remaining assets were removed from the bridges and are redistributed through onchain smart contracts and the Kinto CVR frontend.
Badges
About
Kinto is an Orbit stack L2 with account abstraction and KYC enabled for all users, supporting both modern financial institutions and decentralized protocols.
Badges
About
Kinto is an Orbit stack L2 with account abstraction and KYC enabled for all users, supporting both modern financial institutions and decentralized protocols.
2023 Dec 15 — 2026 May 28
The section shows the operating costs that L2s pay to Ethereum.
2023 Dec 15 — 2026 May 28
This section shows how much data the project publishes to its data-availability (DA) layer over time. The project currently posts data to![]() Ethereum.
Ethereum.
2024 Jul 23 — 2026 May 28
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
2023 Dec 15 — 2026 May 29
Appchain Stage 1
2025 Mar 27th
Users can exit the L2 in case of unwanted upgrades by actors other than the Security Council.
Security Council Governance
2024 Nov 3rd
Kinto gives the ownership of all L1 system contracts to a Security Council that is properly set up.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
Fraud proofs allow 9 WHITELISTED actors watching the chain to prove that the state is incorrect. At least 5 Challengers are external to the Operator. Interactive proofs (INT) require multiple transactions over time to resolve. There is a 6d 8h challenge period.
All of the data needed for proof construction is published on Ethereum L1.
There is no exit window for users to exit in case of unwanted upgrades of the L1 as they are initiated by the Security Council with instant upgrade power and without proper notice. Upgrades initiated by actors other than the Security Council (e.g. KYC providers) on Layer 2 guarantee at least a 7d exit window to the user.
Anyone can become a Proposer after 12d 17h of inactivity from the currently whitelisted Proposers.
Rollup operators cannot compromise the system, but being application-specific might bring additional risk.
Kinto enforces the use of smart wallets and KYC. A valid state transition in Kinto disallows all transactions by EOAs and new contracts creation, unless specifically whitelisted. This setup effectively enforces smart wallet use because the auxiliary contracts of the standard KintoWallet smart wallet (like the EntryPoint and the KintoWalletFactory) are whitelisted. The KYC validation is part of the KintoWallet signature verification. Since all users must use the same implementation of this smart wallet, all user transactions on Kinto check for an up-to-date KYC flag, and are dropped in case the check fails. The system ensures that KYC can be revoked only if the Security Council proactively agrees to a proposed status change by a KYC provider. The Security Council has been historically following KYC provider decisions and it is explicitly tasked to do so. The KintoWallet implementation supports different signer thresholds with a maximum of 4 signers. The first signer for each users smart wallet though is enforced to be held by Turnkey in a TEE. Users can make transactions using this first signer only through Kinto's frontend. Authenticated by a passkey, the Turnkey TEE then signs the transaction for them and submits it to the L2. The user can still choose to not trust Turnkey by adding 2 EOA signers to their wallet and setting their signer policy to 2/3 during wallet creation. Contracts outside of the ones necessary to interact with the smart wallet and to withdraw the gas token are out of scope for the stage assessment and might present additional risks.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap blobs or calldata. This ensures that it will be available for enough time.
- Sequencing followed by deterministic execution - Arbitrum documentation
- SequencerInbox.sol - source code, addSequencerL2BatchFromOrigin function
Updates to the system state can be proposed and challenged by a set of whitelisted validators. If a state root passes the challenge period, it is optimistically considered correct and made actionable for withdrawals.
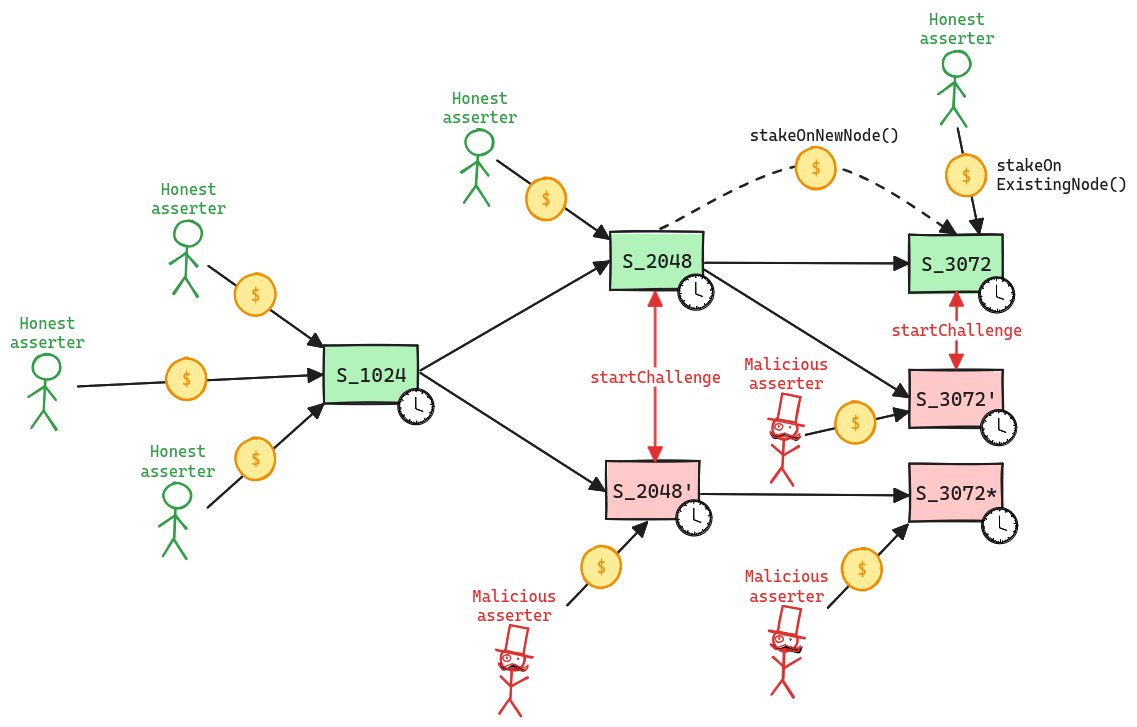
Whitelisted validators propose state roots as children of a previous state root. A state root can have multiple conflicting children. This structure forms a graph, and therefore, in the contracts, state roots are referred to as nodes. Each proposal requires a stake, currently set to 0.1 ETH, that can be slashed if the proposal is proven incorrect via a fraud proof. Stakes can be moved from one node to one of its children, either by calling stakeOnExistingNode or stakeOnNewNode. New nodes cannot be created faster than the minimum assertion period by the same validator, currently set to 15m. The oldest unconfirmed node can be confirmed if the challenge period has passed and there are no siblings, and rejected if the parent is not a confirmed node or if the challenge period has passed and no one is staked on it.
Funds can be stolen if none of the whitelisted verifiers checks the published state. Fraud proofs assume at least one honest and able validator (CRITICAL).
A challenge can be started between two siblings, i.e. two different state roots that share the same parent, by calling the startChallenge function. Validators cannot be in more than one challenge at the same time, meaning that the protocol operates with partial concurrency. Since each challenge lasts 6d 8h, this implies that the protocol can be subject to delay attacks, where a malicious actor can delay withdrawals as long as they are willing to pay the cost of losing their stakes. If the protocol is delayed attacked, the new stake requirement increases exponentially for each challenge period of delay. Challenges are played via a bisection game, where asserter and challenger play together to find the first instruction of disagreement. Such instruction is then executed onchain in the WASM OneStepProver contract to determine the winner, who then gets half of the stake of the loser. As said before, a state root is rejected only when no one left is staked on it. The protocol does not enforces valid bisections, meaning that actors can propose correct initial claim and then provide incorrect midpoints.
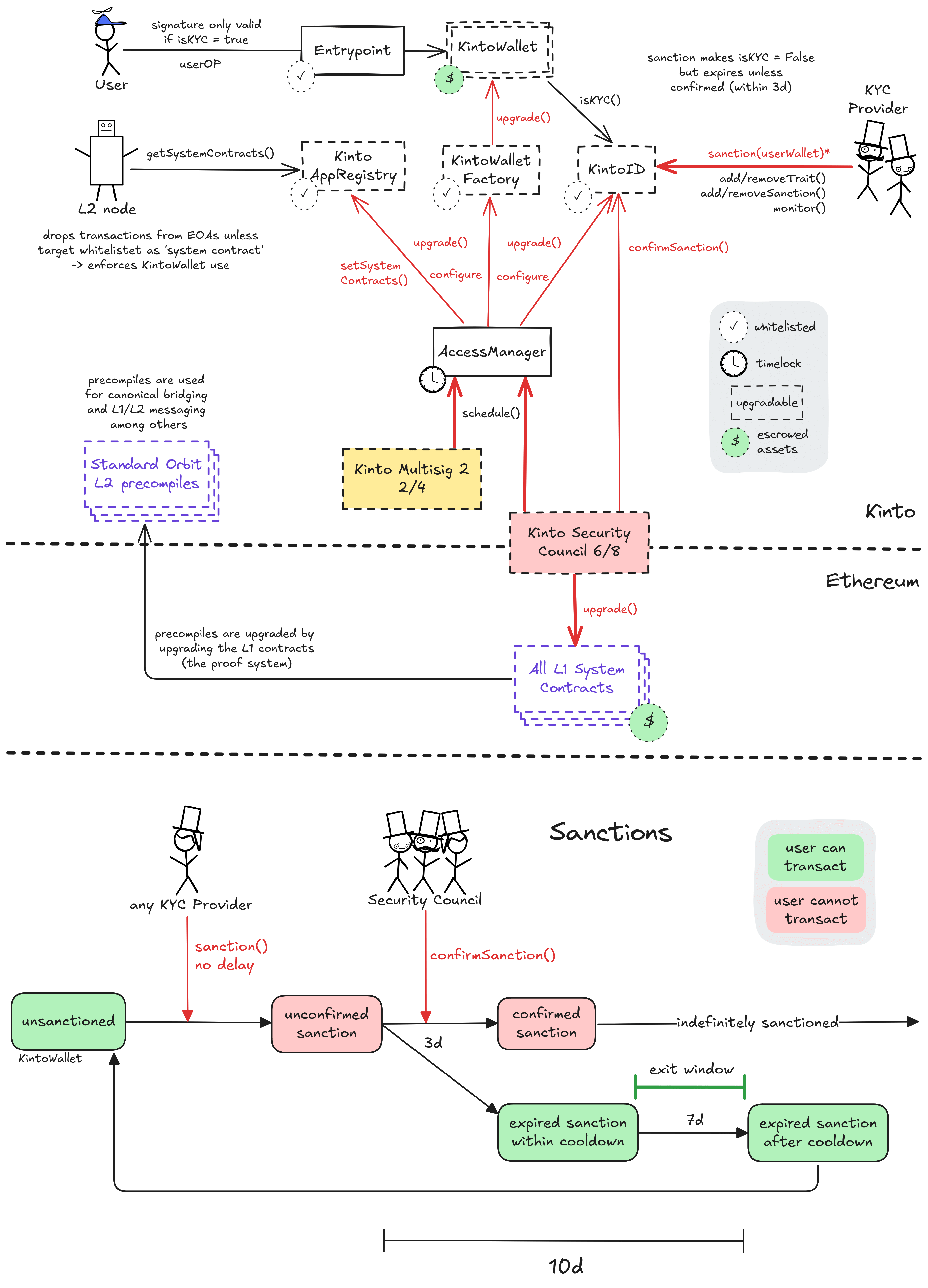
All critical system smart contracts are upgradeable (can be arbitrarily changed). This permission is held by the 6/8 Kinto Security Council on Layer 1 and can be executed without any delay. On the Kinto Layer 2, critical permissions are mostly guarded by an AccessManager contract, and then passed down with configurable delays to both the Security Council and the 2/4 Kinto Multisig 2.
The Appchain designation of Kinto is mainly due to a modified L2 node, which queries a special censoring contract on L2 (called KintoAppRegistry) for a whitelist to filter transactions. This makes the KintoAppRegistry contract a critical system contract and any change to its configuration equivalent to an upgrade of the Layer 2 system. The KintoAppRegistry contract is also governed via the AccessManager by the Security Council or the Kinto Multisig 2 with a 12d delay.
Another critical contract on the Appchain is called KintoID. Permissioned actors with the ‘KYC provider’ role in the KintoID contract can ‘sanction’ (freeze) user smart wallets, preventing them from transacting. To protect users from this role which is mostly held by EOAs, a sanction expires if not confirmed by the Security Council within 3d. An expired sanction guarantees the user a 9d cooldown window during which they cannot be sanctioned again.
The canonical (enforced) smartwallet for users on Kinto can be upgraded via the KintoWalletFactory, using the same path via the AccessManager. Additionally, each smart wallet must use a recoverer address custodied by Turnkey. This allows users to reset the wallet signers via their email in case they lose their passkey. It also necessitates a recovery delay to prevent turnkey from maliciously using their recoverer permission. During this period of 12d, the user can cancel the recovery process with any transaction in their smart wallet.
The permissioned sanctions logic by KYC providers necessitates at least an 12d delay on all upgrades that aren’t executed by the Security Council, allowing the user at least 7d to exit.
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2025 September 03, 11:21 UTC5changesms signer change.
ms signer change.
| contract Kinto Multisig (eth:0xf152Abda9E4ce8b134eF22Dc3C6aCe19C4895D82) { | |
| +++ description: None | |
| values.$members.0: | |
| - | "eth:0x5D973Ea995d14799E528B14472346bfDE21eAe2e" |
| values.$threshold: | |
| - | 3 |
| + | 2 |
| values.multisigThreshold: | |
| - | "3 of 4 (75%)" |
| + | "2 of 3 (67%)" |
| } |
2025 August 19, 08:24 UTCHigh severity2changesRemoved one KYC provider. There are now 6, down from 7.
Removed one KYC provider. There are now 6, down from 7.
| contract KintoID (0xf369f78E3A0492CC4e96a90dae0728A38498e9c7) { | |
| +++ description: Manages Kinto's KYC system: The KYC_PROVIDER roles responsible for managing the KYC status and KYC metadata of user wallets. Each KintoWallet checks the KYC status of its user in this contract as part of the signature check. | |
| values.accessControl.KYC_PROVIDER_ROLE.members.0: | |
| - | "kinto:0x52F09693c9eEaA93A64BA697e3d3e43a1eB65477" |
| +++ severity: HIGH | |
| values.KYC_PROVIDERs.0: | |
| - | "kinto:0x52F09693c9eEaA93A64BA697e3d3e43a1eB65477" |
| } |
2025 July 25, 13:26 UTC15changesKinto has added SC members to the validator list to satisfy the new stage 1 requirement.
Kinto has added SC members to the validator list to satisfy the new stage 1 requirement.
| EOA KintoFoundation (0x08E674c4538caE03B6c05405881dDCd95DcaF5a8) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators"}] |
| } |
| EOA (0x4a3BB34aDE10127752015A6aF6136da15fde636A) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators","via":[{"address":"eth:0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1"}]}] |
| } |
| contract RollupProxy (0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11) { | |
| +++ description: Central contract for the project's configuration like its execution logic hash (`wasmModuleRoot`) and addresses of the other system contracts. Entry point for Proposers creating new Rollup Nodes (state commitments) and Challengers submitting fraud proofs (In the Orbit stack, these two roles are both held by the Validators). | |
| +++ description: Increments on each Validator change. | |
| values.setValidatorCount: | |
| - | 4 |
| + | 5 |
| values.validators.0: | |
| + | "eth:0x08E674c4538caE03B6c05405881dDCd95DcaF5a8" |
| values.validators.3: | |
| + | "eth:0x5FB5040dfC5B8b9Ea40dFBd881188Ec85cDC0621" |
| values.validators.6: | |
| + | "eth:0x94561e98DD5E55271f91A103e4979aa6C493745E" |
| values.validators.7: | |
| + | "eth:0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1" |
| } |
| EOA Certora 1 (0x5FB5040dfC5B8b9Ea40dFBd881188Ec85cDC0621) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators"}] |
| } |
| EOA (0x8A577165f8ef813296043d5f75fF2F2F2349afFd) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators","via":[{"address":"eth:0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1"}]}] |
| } |
| EOA KintsugiFoundation (0x94561e98DD5E55271f91A103e4979aa6C493745E) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators"}] |
| } |
| EOA (0xad40f1440544475f4B70573a106F41dF1860598b) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators","via":[{"address":"eth:0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1"}]}] |
| } |
| EOA (0xCb5BCC84741b379BFa0968b841C5de1fC9240CBd) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators","via":[{"address":"eth:0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1"}]}] |
| } |
| contract Turnkey Multisig (0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1) { | |
| +++ description: None | |
| directlyReceivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators"}] |
| } |
| EOA (0xDcbb957bF991A0b252Fd996946Ea27E51ECabA69) { | |
| +++ description: None | |
| receivedPermissions: | |
| + | [{"permission":"validate","from":"eth:0x5073dA9cA4810f3E0aA01c20c7d9d02C3f522e11","description":"Can propose new state roots (called nodes) and challenge state roots on the host chain.","role":".validators","via":[{"address":"eth:0xD98B32e5D0Dcb5853e498225a15447a59b7a40e1"}]}] |
| } |
2025 June 18, 12:22 UTCHigh severity2changesdev helper role granted, no risk changes.
dev helper role granted, no risk changes.
| contract AccessManager (0xacC000818e5Bbd911D5d449aA81CB5cA24024739) { | |
| +++ description: OpenZeppelin AccessManager contract: Serves as a proxy contract defining the roles, permissions and delays to call functions in target contracts. | |
| values.accessControl.roles.DEV_HELPER_ROLE: | |
| + | {"members":[{"member":"0x2e2B1c42E38f5af81771e65D87729E57ABD1337a","since":1749945326,"executionDelay":0}]} |
| +++ description: List of roles granted to accounts. | |
| +++ severity: HIGH | |
| values.RolesGranted.12665434841745889720: | |
| + | [{"account":"0x2e2B1c42E38f5af81771e65D87729E57ABD1337a","delay":0,"since":1749945326,"newMember":true}] |
| } |
2025 June 09, 10:57 UTC1097changesnew pending sanction (not confirmed by the Security Council).
new pending sanction (not confirmed by the Security Council).
| contract KintoID (0xf369f78E3A0492CC4e96a90dae0728A38498e9c7) { | |
| +++ description: Manages Kinto's KYC system: The KYC_PROVIDER roles responsible for managing the KYC status and KYC metadata of user wallets. Each KintoWallet checks the KYC status of its user in this contract as part of the signature check. | |
| +++ description: addresses sanctioned by any KYC_PROVIDER role. | |
| values.pendingSanctions.324: | |
| + | {"_to":"0x19CC0e919b58e0d0eF7BaeBb103f72dee1031978","_timestamp":1706580004} |
| values.pendingSanctions.323._to: | |
| - | "0x19CC0e919b58e0d0eF7BaeBb103f72dee1031978" |
| + | "0x467Fa5244cd8386581635646F12E13C05Ad0f41F" |
| values.pendingSanctions.323._timestamp: | |
| - | 1706580004 |
| + | 1718846703 |
| values.pendingSanctions.322._to: | |
| - | "0x467Fa5244cd8386581635646F12E13C05Ad0f41F" |
| + | "0x70E21B6fB6835652642568Dd0143C2821e7EBC01" |
| values.pendingSanctions.322._timestamp: | |
| - | 1718846703 |
| + | 1743368147 |
| values.pendingSanctions.321._to: | |
| - | "0x70E21B6fB6835652642568Dd0143C2821e7EBC01" |
| + | "0x3CfA8C0e6eEb1e601f76355A82f583232b186a7D" |
| values.pendingSanctions.321._timestamp: | |
| - | 1743368147 |
| + | 1706580004 |
| values.pendingSanctions.320._to: | |
| - | "0x3CfA8C0e6eEb1e601f76355A82f583232b186a7D" |
| + | "0x275edFf82EB0c3845edaBa411D7A5bE31486C2B6" |
| values.pendingSanctions.320._timestamp: | |
| - | 1706580004 |
| + | 1710367221 |
| values.pendingSanctions.319._to: | |
| - | "0x275edFf82EB0c3845edaBa411D7A5bE31486C2B6" |
| + | "0x5718c0f092Da70702A0fC284d5C86C3EeDa218Ae" |
| values.pendingSanctions.319._timestamp: | |
| - | 1710367221 |
| + | 1743368131 |
| values.pendingSanctions.318._to: | |
| - | "0x5718c0f092Da70702A0fC284d5C86C3EeDa218Ae" |
| + | "0x83cCA28493b1940a16b6c22B77C7146C40463eD2" |
| values.pendingSanctions.318._timestamp: | |
| - | 1743368131 |
| + | 1743368167 |
| values.pendingSanctions.317._to: | |
| - | "0x83cCA28493b1940a16b6c22B77C7146C40463eD2" |
| + | "0xC62595F9ec07A7b8FBE9BdC64926a80f1a7115bD" |
| values.pendingSanctions.317._timestamp: | |
| - | 1743368167 |
| + | 1743368220 |
| values.pendingSanctions.316._to: | |
| - | "0xC62595F9ec07A7b8FBE9BdC64926a80f1a7115bD" |
| + | "0x685d6B0088397A00790DBDE7B3Ab8fAA7841a809" |
| values.pendingSanctions.316._timestamp: | |
| - | 1743368220 |
| + | 1743368147 |
| values.pendingSanctions.315._to: | |
| - | "0x685d6B0088397A00790DBDE7B3Ab8fAA7841a809" |
| + | "0x5cCF7b5170F0292106A6df1F111958ff62e8Edd3" |
| values.pendingSanctions.315._timestamp: | |
| - | 1743368147 |
| + | 1743368131 |
| values.pendingSanctions.314._to: | |
| - | "0x5cCF7b5170F0292106A6df1F111958ff62e8Edd3" |
| + | "0x81eEd39FC79B50DeBBcaEfc05221e9631Fb3b20f" |
| values.pendingSanctions.314._timestamp: | |
| - | 1743368131 |
| + | 1743368167 |
| values.pendingSanctions.313._to: | |
| - | "0x81eEd39FC79B50DeBBcaEfc05221e9631Fb3b20f" |
| + | "0x9961e674Dc623dc69f6AF4fBF4E2F1FAbcbc44Ce" |
| values.pendingSanctions.313._timestamp: | |
| - | 1743368167 |
| + | 1743368190 |
| values.pendingSanctions.312._to: | |
| - | "0x9961e674Dc623dc69f6AF4fBF4E2F1FAbcbc44Ce" |
| + | "0x8631D1Aa293c92A79C7717d933B785EcCF61b1ae" |
| values.pendingSanctions.312._timestamp: | |
| - | 1743368190 |
| + | 1743368167 |
| values.pendingSanctions.311._to: | |
| - | "0x8631D1Aa293c92A79C7717d933B785EcCF61b1ae" |
| + | "0xBD85550C39dE4844E501A278D6b632FbE68cF70F" |
| values.pendingSanctions.311._timestamp: | |
| - | 1743368167 |
| + | 1716580853 |
| values.pendingSanctions.310._to: | |
| - | "0xBD85550C39dE4844E501A278D6b632FbE68cF70F" |
| + | "0x4C2eEe16F3b55D45650c1a97bF329Fe810A517a2" |
| values.pendingSanctions.310._timestamp: | |
| - | 1716580853 |
| + | 1743368117 |
| values.pendingSanctions.309._to: | |
| - | "0x4C2eEe16F3b55D45650c1a97bF329Fe810A517a2" |
| + | "0x3Ee9cE9503bAa9a3CD4807Fa0146F848e3120b50" |
| values.pendingSanctions.309._timestamp: | |
| - | 1743368117 |
| + | 1743368100 |
| values.pendingSanctions.308._to: | |
| - | "0x3Ee9cE9503bAa9a3CD4807Fa0146F848e3120b50" |
| + | "0x3bB7Ff827729EB2F3cd419c67Fc3B151f22deDe7" |
| values.pendingSanctions.307._to: | |
| - | "0x3bB7Ff827729EB2F3cd419c67Fc3B151f22deDe7" |
| + | "0x5Da354DC30613Be81557323729b2bbE3D3D506d7" |
| values.pendingSanctions.307._timestamp: | |
| - | 1743368100 |
| + | 1743368131 |
| values.pendingSanctions.306._to: | |
| - | "0x5Da354DC30613Be81557323729b2bbE3D3D506d7" |
| + | "0x5383b0425760763baaa92677464C4E723Cdba191" |
| values.pendingSanctions.305._to: | |
| - | "0x5383b0425760763baaa92677464C4E723Cdba191" |
| + | "0x79e0F3d1DCEab60D446D9296adA1c5c0D3368d0b" |
| values.pendingSanctions.305._timestamp: | |
| - | 1743368131 |
| + | 1743368167 |
| values.pendingSanctions.304._to: | |
| - | "0x79e0F3d1DCEab60D446D9296adA1c5c0D3368d0b" |
| + | "0x4E56569186083eacEC60e38b9B76F1d7C6A03694" |
| values.pendingSanctions.304._timestamp: | |
| - | 1743368167 |
| + | 1743368131 |
| values.pendingSanctions.303._to: | |
| - | "0x4E56569186083eacEC60e38b9B76F1d7C6A03694" |
| + | "0x90231e5318110108B4748c67c9119CD8Ef28D0f0" |
| values.pendingSanctions.303._timestamp: | |
| - | 1743368131 |
| + | 1743368190 |
| values.pendingSanctions.302._to: | |
| - | "0x90231e5318110108B4748c67c9119CD8Ef28D0f0" |
| + | "0x9E339388d44B21E9d027ba95D71E08E75736CE0E" |
| values.pendingSanctions.301._to: | |
| - | "0x9E339388d44B21E9d027ba95D71E08E75736CE0E" |
| + | "0xE9D67E87DD59b29876CF0E1ace667cAE39210fa8" |
| values.pendingSanctions.301._timestamp: | |
| - | 1743368190 |
| + | 1743368286 |
| values.pendingSanctions.300._to: | |
| - | "0xE9D67E87DD59b29876CF0E1ace667cAE39210fa8" |
| + | "0x504a1ef47bF87a550bebfBA6ffe58a3a57bADeB7" |
| values.pendingSanctions.300._timestamp: | |
| - | 1743368286 |
| + | 1707652818 |
| values.pendingSanctions.299._to: | |
| - | "0x504a1ef47bF87a550bebfBA6ffe58a3a57bADeB7" |
| + | "0x6100c3fE678800EB6809DE473688b433eB081a5F" |
| values.pendingSanctions.299._timestamp: | |
| - | 1707652818 |
| + | 1743368147 |
| values.pendingSanctions.298._to: | |
| - | "0x6100c3fE678800EB6809DE473688b433eB081a5F" |
| + | "0x9c41f1FB592aFE978726FCa785a8fD2b1c836006" |
| values.pendingSanctions.298._timestamp: | |
| - | 1743368147 |
| + | 1743368207 |
| values.pendingSanctions.297._to: | |
| - | "0x9c41f1FB592aFE978726FCa785a8fD2b1c836006" |
| + | "0x9E292AFD2492f4ecBA6c1eb8B73BC87A5650eB8F" |
| values.pendingSanctions.297._timestamp: | |
| - | 1743368207 |
| + | 1718846645 |
| values.pendingSanctions.296._to: | |
| - | "0x9E292AFD2492f4ecBA6c1eb8B73BC87A5650eB8F" |
| + | "0xB1bEaC3a3472436d9AA1f2D36aEaA2c215b66b9a" |
| values.pendingSanctions.296._timestamp: | |
| - | 1718846645 |
| + | 1743368207 |
| values.pendingSanctions.295._to: | |
| - | "0xB1bEaC3a3472436d9AA1f2D36aEaA2c215b66b9a" |
| + | "0x89Ea92eF445cC8EC1055C8d243Ed50A2eF5FD77C" |
| values.pendingSanctions.295._timestamp: | |
| - | 1743368207 |
| + | 1743368167 |
| values.pendingSanctions.294._to: | |
| - | "0x89Ea92eF445cC8EC1055C8d243Ed50A2eF5FD77C" |
| + | "0xE01874E2F6C78990F6a55Cb86B49ECCe070aEb0d" |
| values.pendingSanctions.294._timestamp: | |
| - | 1743368167 |
| + | 1743368286 |
| values.pendingSanctions.293._to: | |
| - | "0xE01874E2F6C78990F6a55Cb86B49ECCe070aEb0d" |
| + | "0xE459e4bE9844131F5b26544cA60D56A034D26A3c" |
| values.pendingSanctions.292._to: | |
| - | "0xE459e4bE9844131F5b26544cA60D56A034D26A3c" |
| + | "0xE65a2Dee17190786c76f83e36F489a085690686C" |
| values.pendingSanctions.292._timestamp: | |
| - | 1743368286 |
| + | 1707840030 |
| values.pendingSanctions.291._to: | |
| - | "0xE65a2Dee17190786c76f83e36F489a085690686C" |
| + | "0x4b2E0fDA7DB5Ab4f7471776F3A0e7E0D85444bFF" |
| values.pendingSanctions.291._timestamp: | |
| - | 1707840030 |
| + | 1743368131 |
| values.pendingSanctions.290._to: | |
| - | "0x4b2E0fDA7DB5Ab4f7471776F3A0e7E0D85444bFF" |
| + | "0xf685Ca101dd7598Ec26244d8ff0f5abEa0F23509" |
| values.pendingSanctions.290._timestamp: | |
| - | 1743368131 |
| + | 1743368491 |
| values.pendingSanctions.289._to: | |
| - | "0xf685Ca101dd7598Ec26244d8ff0f5abEa0F23509" |
| + | "0xD3Af5EAb05E1882439E8626F9102a0A0bDCa21DB" |
| values.pendingSanctions.289._timestamp: | |
| - | 1743368491 |
| + | 1743368220 |
| values.pendingSanctions.288._to: | |
| - | "0xD3Af5EAb05E1882439E8626F9102a0A0bDCa21DB" |
| + | "0xbf3fBce48ff8a49918dD8578290814ea466aB79F" |
| values.pendingSanctions.288._timestamp: | |
| - | 1743368220 |
| + | 1718846587 |
| values.pendingSanctions.287._to: | |
| - | "0xbf3fBce48ff8a49918dD8578290814ea466aB79F" |
| + | "0x91aDe5800dB3eBE7E103CFc05069487B00AE45ba" |
| values.pendingSanctions.287._timestamp: | |
| - | 1718846587 |
| + | 1743368190 |
| values.pendingSanctions.286._to: | |
| - | "0x91aDe5800dB3eBE7E103CFc05069487B00AE45ba" |
| + | "0xA211445157D68B451006f8452eB7309A2313DC7a" |
| values.pendingSanctions.286._timestamp: | |
| - | 1743368190 |
| + | 1743368207 |
| values.pendingSanctions.285._to: | |
| - | "0xA211445157D68B451006f8452eB7309A2313DC7a" |
| + | "0x81bb2B25eA1A01BADA25d41C67A34d81C9684712" |
| values.pendingSanctions.285._timestamp: | |
| - | 1743368207 |
| + | 1718846645 |
| values.pendingSanctions.284._to: | |
| - | "0x81bb2B25eA1A01BADA25d41C67A34d81C9684712" |
| + | "0xDe2918Cb894ecC8BfD81eeD617DFF2a461700312" |
| values.pendingSanctions.284._timestamp: | |
| - | 1718846645 |
| + | 1743368286 |
| values.pendingSanctions.283._to: | |
| - | "0xDe2918Cb894ecC8BfD81eeD617DFF2a461700312" |
| + | "0x533efF0d6Ee8cd7dEF21ea27BeC421Ef7b8cE796" |
| values.pendingSanctions.283._timestamp: | |
| - | 1743368286 |
| + | 1743368131 |
| values.pendingSanctions.282._to: | |
| - | "0x533efF0d6Ee8cd7dEF21ea27BeC421Ef7b8cE796" |
| + | "0xF53eEd3bD238d4038e8e2699e832323A03500D0e" |
| values.pendingSanctions.282._timestamp: | |
| - | 1743368131 |
| + | 1743368286 |
| values.pendingSanctions.281._to: | |
| - | "0xF53eEd3bD238d4038e8e2699e832323A03500D0e" |
| + | "0x8d2635Da6aB707E0370E2F55Bdd2D0b8dA0596A4" |
| values.pendingSanctions.281._timestamp: | |
| - | 1743368286 |
| + | 1743368167 |
| values.pendingSanctions.280._to: | |
| - | "0x8d2635Da6aB707E0370E2F55Bdd2D0b8dA0596A4" |
| + | "0x962C00Ebc894Fb3e9B32AfE1dd1fa31A076e50e5" |
| values.pendingSanctions.280._timestamp: | |
| - | 1743368167 |
| + | 1743368190 |
| values.pendingSanctions.279._to: | |
| - | "0x962C00Ebc894Fb3e9B32AfE1dd1fa31A076e50e5" |
| + | "0xcD984AD7eBB2ab7B2aE0afd967F371c6E24a4Bc6" |
| values.pendingSanctions.279._timestamp: | |
| - | 1743368190 |
| + | 1718846587 |
| values.pendingSanctions.278._to: | |
| - | "0xcD984AD7eBB2ab7B2aE0afd967F371c6E24a4Bc6" |
| + | "0xBa5F9be8C94E2955deD0982Dc276023051bED0AA" |
| values.pendingSanctions.278._timestamp: | |
| - | 1718846587 |
| + | 1743368207 |
| values.pendingSanctions.277._to: | |
| - | "0xBa5F9be8C94E2955deD0982Dc276023051bED0AA" |
| + | "0x483090b7B8AFBf4F9e650E5a45dbD013959d4867" |
| values.pendingSanctions.277._timestamp: | |
| - | 1743368207 |
| + | 1743368117 |
| values.pendingSanctions.276._to: | |
| - | "0x483090b7B8AFBf4F9e650E5a45dbD013959d4867" |
| + | "0x99758a8519691B6bffEeD3976080c943634B7364" |
| values.pendingSanctions.276._timestamp: | |
| - | 1743368117 |
| + | 1718846645 |
| values.pendingSanctions.275._to: | |
| - | "0x99758a8519691B6bffEeD3976080c943634B7364" |
| + | "0x4506633D9bBB3EA73c89ff4829695D67896104d4" |
| values.pendingSanctions.275._timestamp: | |
| - | 1718846645 |
| + | 1743368117 |
| values.pendingSanctions.274._to: | |
| - | "0x4506633D9bBB3EA73c89ff4829695D67896104d4" |
| + | "0x1075d13CE70F8F4eB840c4c264b6c84C2CD4E785" |
| values.pendingSanctions.274._timestamp: | |
| - | 1743368117 |
| + | 1708034428 |
| values.pendingSanctions.273._to: | |
| - | "0x1075d13CE70F8F4eB840c4c264b6c84C2CD4E785" |
| + | "0xC44F5CA2F187D5ece6864b8a31174C36dEFdC29c" |
| values.pendingSanctions.273._timestamp: | |
| - | 1708034428 |
| + | 1706139865 |
| values.pendingSanctions.272._to: | |
| - | "0xC44F5CA2F187D5ece6864b8a31174C36dEFdC29c" |
| + | "0xC10730513A843fa0E2Fc223eC2AE3B6d3d002294" |
| values.pendingSanctions.272._timestamp: | |
| - | 1706139865 |
| + | 1719715565 |
| values.pendingSanctions.271._to: | |
| - | "0xC10730513A843fa0E2Fc223eC2AE3B6d3d002294" |
| + | "0x72F50cBB3D4189179b1cC55435993eB3d0bF772C" |
| values.pendingSanctions.271._timestamp: | |
| - | 1719715565 |
| + | 1743368147 |
| values.pendingSanctions.270._to: | |
| - | "0x72F50cBB3D4189179b1cC55435993eB3d0bF772C" |
| + | "0x505D435C8B66a7511dbec7f3C8DA6F1e67D50dDA" |
| values.pendingSanctions.270._timestamp: | |
| - | 1743368147 |
| + | 1706148032 |
| values.pendingSanctions.269._to: | |
| - | "0x505D435C8B66a7511dbec7f3C8DA6F1e67D50dDA" |
| + | "0xaE8C34b3eB7bcc21085eB819d23afF8687B449fE" |
| values.pendingSanctions.269._timestamp: | |
| - | 1706148032 |
| + | 1743368466 |
| values.pendingSanctions.268._to: | |
| - | "0xaE8C34b3eB7bcc21085eB819d23afF8687B449fE" |
| + | "0x01e523cC67e5d3459bE930837d89bccEA85Fd1DC" |
| values.pendingSanctions.268._timestamp: | |
| - | 1743368466 |
| + | 1719715623 |
| values.pendingSanctions.267._to: | |
| - | "0x01e523cC67e5d3459bE930837d89bccEA85Fd1DC" |
| + | "0xaB769943901Bb757cf5048B122f4A2D5D0aEE957" |
| values.pendingSanctions.267._timestamp: | |
| - | 1719715623 |
| + | 1743368286 |
| values.pendingSanctions.266._to: | |
| - | "0xaB769943901Bb757cf5048B122f4A2D5D0aEE957" |
| + | "0xDABa2f9fdEc6Bada2902B4453239332FE591d9ee" |
| values.pendingSanctions.266._timestamp: | |
| - | 1743368286 |
| + | 1743368220 |
| values.pendingSanctions.265._to: | |
| - | "0xDABa2f9fdEc6Bada2902B4453239332FE591d9ee" |
| + | "0xD91110Bb87AEEFa8D74A274930804F7D61324f0E" |
| values.pendingSanctions.264._to: | |
| - | "0xD91110Bb87AEEFa8D74A274930804F7D61324f0E" |
| + | "0xD4a998c38f016cC342b7Abd9796113D596201be3" |
| values.pendingSanctions.263._to: | |
| - | "0xD4a998c38f016cC342b7Abd9796113D596201be3" |
| + | "0xE174390679C9Cb86e64131f9AA173FdC9C10b8af" |
| values.pendingSanctions.263._timestamp: | |
| - | 1743368220 |
| + | 1743368286 |
| values.pendingSanctions.262._to: | |
| - | "0xE174390679C9Cb86e64131f9AA173FdC9C10b8af" |
| + | "0x4d38B797655D0B8F5E61a01A5a71A0346B98A3DD" |
| values.pendingSanctions.262._timestamp: | |
| - | 1743368286 |
| + | 1743368131 |
| values.pendingSanctions.261._to: | |
| - | "0x4d38B797655D0B8F5E61a01A5a71A0346B98A3DD" |
| + | "0x5579CA784CdC93776b9c030618548f1317AB4c39" |
| values.pendingSanctions.261._timestamp: | |
| - | 1743368131 |
| + | 1706148032 |
| values.pendingSanctions.260._to: | |
| - | "0x5579CA784CdC93776b9c030618548f1317AB4c39" |
| + | "0x74a6001A9b9f9AAb26A4eDEe55DB40413569255A" |
| values.pendingSanctions.260._timestamp: | |
| - | 1706148032 |
| + | 1743368147 |
| values.pendingSanctions.259._to: | |
| - | "0x74a6001A9b9f9AAb26A4eDEe55DB40413569255A" |
| + | "0xFff5B9B7bf09DfC42865cDaDAA161f14Fd54498d" |
| values.pendingSanctions.259._timestamp: | |
| - | 1743368147 |
| + | 1743368286 |
| values.pendingSanctions.258._to: | |
| - | "0xFff5B9B7bf09DfC42865cDaDAA161f14Fd54498d" |
| + | "0xb2F1d7867fD8d1501f5747676823f8d27a6a12f2" |
| values.pendingSanctions.258._timestamp: | |
| - | 1743368286 |
| + | 1743368466 |
| values.pendingSanctions.257._to: | |
| - | "0xb2F1d7867fD8d1501f5747676823f8d27a6a12f2" |
| + | "0x414ded65867BdD1a2DcEcf730fBF4F92a72Ec55a" |
| values.pendingSanctions.257._timestamp: | |
| - | 1743368466 |
| + | 1743368117 |
| values.pendingSanctions.256._to: | |
| - | "0x414ded65867BdD1a2DcEcf730fBF4F92a72Ec55a" |
| + | "0x917A716dA88cE955f56A2C61313eeB1a1C80eC5b" |
| values.pendingSanctions.256._timestamp: | |
| - | 1743368117 |
| + | 1743368190 |
| values.pendingSanctions.255._to: | |
| - | "0x917A716dA88cE955f56A2C61313eeB1a1C80eC5b" |
| + | "0x49EbC2b33a410955D6291828af3f8EBeD3A1540e" |
| values.pendingSanctions.255._timestamp: | |
| - | 1743368190 |
| + | 1743368117 |
| values.pendingSanctions.254._to: | |
| - | "0x49EbC2b33a410955D6291828af3f8EBeD3A1540e" |
| + | "0xaEB8b6bB09c44c6eE9524Bf6a7842531e8870217" |
| values.pendingSanctions.254._timestamp: | |
| - | 1743368117 |
| + | 1743368466 |
| values.pendingSanctions.253._to: | |
| - | "0xaEB8b6bB09c44c6eE9524Bf6a7842531e8870217" |
| + | "0x72d47E7F0E341129Fd8815e84e396e86AF88484b" |
| values.pendingSanctions.253._timestamp: | |
| - | 1743368466 |
| + | 1743368147 |
| values.pendingSanctions.252._to: | |
| - | "0x72d47E7F0E341129Fd8815e84e396e86AF88484b" |
| + | "0xaBA02c3024E1b5A8dfA53f7bD82d6B75B8C7Fea2" |
| values.pendingSanctions.252._timestamp: | |
| - | 1743368147 |
| + | 1743368466 |
| values.pendingSanctions.251._to: | |
| - | "0xaBA02c3024E1b5A8dfA53f7bD82d6B75B8C7Fea2" |
| + | "0x75D9312845d38764229455Ea8d526A122b37768D" |
| values.pendingSanctions.251._timestamp: | |
| - | 1743368466 |
| + | 1719718623 |
| values.pendingSanctions.250._to: | |
| - | "0x75D9312845d38764229455Ea8d526A122b37768D" |
| + | "0x96aA815610caed4095B525042156560Ac5dBC8e9" |
| values.pendingSanctions.250._timestamp: | |
| - | 1719718623 |
| + | 1743394746 |
| values.pendingSanctions.249._to: | |
| - | "0x96aA815610caed4095B525042156560Ac5dBC8e9" |
| + | "0xe12BcEe0219f3c80FFF8C271D29e343bA42B814d" |
| values.pendingSanctions.249._timestamp: | |
| - | 1743394746 |
| + | 1707483639 |
| values.pendingSanctions.248._to: | |
| - | "0xe12BcEe0219f3c80FFF8C271D29e343bA42B814d" |
| + | "0xC34bd93d87AB32D8fbb966A0666dAa1021A698c2" |
| values.pendingSanctions.248._timestamp: | |
| - | 1707483639 |
| + | 1743368220 |
| values.pendingSanctions.247._to: | |
| - | "0xC34bd93d87AB32D8fbb966A0666dAa1021A698c2" |
| + | "0xe0d359F0f36d5eF22E1ee64135c572a076AaA826" |
| values.pendingSanctions.247._timestamp: | |
| - | 1743368220 |
| + | 1743368491 |
| values.pendingSanctions.246._to: | |
| - | "0xe0d359F0f36d5eF22E1ee64135c572a076AaA826" |
| + | "0xFD357B4975C97d48DfC8C5D5E3130a5634b89B8D" |
| values.pendingSanctions.246._timestamp: | |
| - | 1743368491 |
| + | 1743394746 |
| values.pendingSanctions.245._to: | |
| - | "0xFD357B4975C97d48DfC8C5D5E3130a5634b89B8D" |
| + | "0x933b0f5e531648Bef764b58Ff7782AfB13AB06D0" |
| values.pendingSanctions.245._timestamp: | |
| - | 1743394746 |
| + | 1718846703 |
| values.pendingSanctions.244._to: | |
| - | "0x933b0f5e531648Bef764b58Ff7782AfB13AB06D0" |
| + | "0xA56c58a135fcE29642f7Fb8Cd4Df826Ee4f35528" |
| values.pendingSanctions.244._timestamp: | |
| - | 1718846703 |
| + | 1743368207 |
| values.pendingSanctions.243._to: | |
| - | "0xA56c58a135fcE29642f7Fb8Cd4Df826Ee4f35528" |
| + | "0x2a14E7B96D2362bdf1Df8C0bB4544714e7601Af0" |
| values.pendingSanctions.243._timestamp: | |
| - | 1743368207 |
| + | 1734246668 |
| values.pendingSanctions.242._to: | |
| - | "0x2a14E7B96D2362bdf1Df8C0bB4544714e7601Af0" |
| + | "0x52f6755e5b4dcf8a51B8E161B1D32038b3460BD9" |
| values.pendingSanctions.242._timestamp: | |
| - | 1734246668 |
| + | 1743368131 |
| values.pendingSanctions.241._to: | |
| - | "0x52f6755e5b4dcf8a51B8E161B1D32038b3460BD9" |
| + | "0xFDFEb1b9F613E2CB841E493B5359c124De59499e" |
| values.pendingSanctions.241._timestamp: | |
| - | 1743368131 |
| + | 1743368286 |
| values.pendingSanctions.240._to: | |
| - | "0xFDFEb1b9F613E2CB841E493B5359c124De59499e" |
| + | "0x7C92dEf48191e751C61F96d1B9A058546F8fc5bd" |
| values.pendingSanctions.240._timestamp: | |
| - | 1743368286 |
| + | 1743368167 |
| values.pendingSanctions.239._to: | |
| - | "0x7C92dEf48191e751C61F96d1B9A058546F8fc5bd" |
| + | "0x65E24c0623336b5dae5b566Bb996863ffC36e877" |
| values.pendingSanctions.239._timestamp: | |
| - | 1743368167 |
| + | 1743394986 |
| values.pendingSanctions.238._to: | |
| - | "0x65E24c0623336b5dae5b566Bb996863ffC36e877" |
| + | "0x493ff963FAAbbBeDBA2Aa19378bF8d8a0F0e2C5E" |
| values.pendingSanctions.238._timestamp: | |
| - | 1743394986 |
| + | 1718846587 |
| values.pendingSanctions.237._to: | |
| - | "0x493ff963FAAbbBeDBA2Aa19378bF8d8a0F0e2C5E" |
| + | "0x3bFD323C9D44625D0B8A77ac19b13e75b9A0f2E4" |
| values.pendingSanctions.237._timestamp: | |
| - | 1718846587 |
| + | 1743368100 |
| values.pendingSanctions.236._to: | |
| - | "0x3bFD323C9D44625D0B8A77ac19b13e75b9A0f2E4" |
| + | "0xFCF53d74a16e899b576eb86FDBb76006854Ef763" |
| values.pendingSanctions.236._timestamp: | |
| - | 1743368100 |
| + | 1743368286 |
| values.pendingSanctions.235._to: | |
| - | "0xFCF53d74a16e899b576eb86FDBb76006854Ef763" |
| + | "0xA4EcEAB6C954C3b967cF18e947879A6708A96D5e" |
| values.pendingSanctions.235._timestamp: | |
| - | 1743368286 |
| + | 1719715444 |
| values.pendingSanctions.234._to: | |
| - | "0xA4EcEAB6C954C3b967cF18e947879A6708A96D5e" |
| + | "0x89F6188006a35b9D0407c37f01FCa27AeD48CA3B" |
| values.pendingSanctions.234._timestamp: | |
| - | 1719715444 |
| + | 1719718683 |
| values.pendingSanctions.233._to: | |
| - | "0x89F6188006a35b9D0407c37f01FCa27AeD48CA3B" |
| + | "0xeeAdb06d44f927b77C0bA23B257A4CfEa60EDfB7" |
| values.pendingSanctions.233._timestamp: | |
| - | 1719718683 |
| + | 1743368491 |
| values.pendingSanctions.232._to: | |
| - | "0xeeAdb06d44f927b77C0bA23B257A4CfEa60EDfB7" |
| + | "0xeF4D08EbDAa2373Df18C12173898Ef09beb1Cd45" |
| values.pendingSanctions.231._to: | |
| - | "0xeF4D08EbDAa2373Df18C12173898Ef09beb1Cd45" |
| + | "0xE32AfFACe8f8f0f5A867FDe3d2C5ea1321dB83e8" |
| values.pendingSanctions.231._timestamp: | |
| - | 1743368491 |
| + | 1743368286 |
| values.pendingSanctions.230._to: | |
| - | "0xE32AfFACe8f8f0f5A867FDe3d2C5ea1321dB83e8" |
| + | "0x2A2ad91467443Ef61c49d5957546554EDb90Fe8a" |
| values.pendingSanctions.230._timestamp: | |
| - | 1743368286 |
| + | 1743394746 |
| values.pendingSanctions.229._to: | |
| - | "0x2A2ad91467443Ef61c49d5957546554EDb90Fe8a" |
| + | "0x985540465088C9c667690cC17BFf732fC703D2E5" |
| values.pendingSanctions.229._timestamp: | |
| - | 1743394746 |
| + | 1719718623 |
| values.pendingSanctions.228._to: | |
| - | "0x985540465088C9c667690cC17BFf732fC703D2E5" |
| + | "0xe3f7A57629a00558EBD24100A9D26A66FD4EbAc3" |
| values.pendingSanctions.228._timestamp: | |
| - | 1719718623 |
| + | 1743368491 |
| values.pendingSanctions.227._to: | |
| - | "0xe3f7A57629a00558EBD24100A9D26A66FD4EbAc3" |
| + | "0xA3a0A02e0866a95685062d7a1053912d6eda3E8B" |
| values.pendingSanctions.227._timestamp: | |
| - | 1743368491 |
| + | 1743368207 |
| values.pendingSanctions.226._to: | |
| - | "0xA3a0A02e0866a95685062d7a1053912d6eda3E8B" |
| + | "0xBbaEb862386383C67045cF2e538b6f3BfA1e8f5a" |
| values.pendingSanctions.225._to: | |
| - | "0xBbaEb862386383C67045cF2e538b6f3BfA1e8f5a" |
| + | "0x1f16335Fd1dD3e8DCC8b401f5ae8BA57F8AD76a8" |
| values.pendingSanctions.225._timestamp: | |
| - | 1743368207 |
| + | 1706580004 |
| values.pendingSanctions.224._to: | |
| - | "0x1f16335Fd1dD3e8DCC8b401f5ae8BA57F8AD76a8" |
| + | "0x2955ca0D791C30C16e7298B803BB116bED5d7269" |
| values.pendingSanctions.223._to: | |
| - | "0x2955ca0D791C30C16e7298B803BB116bED5d7269" |
| + | "0x92c248622427367b4cfa70e60C038c63B148C748" |
| values.pendingSanctions.223._timestamp: | |
| - | 1706580004 |
| + | 1743368190 |
| values.pendingSanctions.222._to: | |
| - | "0x92c248622427367b4cfa70e60C038c63B148C748" |
| + | "0x6E6E2044A4cfeA057E02d6FB72c33Fc893A9B788" |
| values.pendingSanctions.222._timestamp: | |
| - | 1743368190 |
| + | 1718846703 |
| values.pendingSanctions.221._to: | |
| - | "0x6E6E2044A4cfeA057E02d6FB72c33Fc893A9B788" |
| + | "0xf30BF377b3C4ed1f111E6E28CF26003CE5a682Cf" |
| values.pendingSanctions.221._timestamp: | |
| - | 1718846703 |
| + | 1706580004 |
| values.pendingSanctions.220._to: | |
| - | "0xf30BF377b3C4ed1f111E6E28CF26003CE5a682Cf" |
| + | "0xdCfA8062948095423c6117a327949198519741b0" |
| values.pendingSanctions.220._timestamp: | |
| - | 1706580004 |
| + | 1743368491 |
| values.pendingSanctions.219._to: | |
| - | "0xdCfA8062948095423c6117a327949198519741b0" |
| + | "0xd138D5DBA662DE76F6Ce4EB60CA486313Ab7d15C" |
| values.pendingSanctions.218._to: | |
| - | "0xd138D5DBA662DE76F6Ce4EB60CA486313Ab7d15C" |
| + | "0x326d76c60952e8a6A1c0af55D0F592E8c4E9597a" |
| values.pendingSanctions.218._timestamp: | |
| - | 1743368491 |
| + | 1743368100 |
| values.pendingSanctions.217._to: | |
| - | "0x326d76c60952e8a6A1c0af55D0F592E8c4E9597a" |
| + | "0xD09E358552fC7Ce6F7E7BDDCE40e52fF1fE0745c" |
| values.pendingSanctions.217._timestamp: | |
| - | 1743368100 |
| + | 1743368220 |
| values.pendingSanctions.216._to: | |
| - | "0xD09E358552fC7Ce6F7E7BDDCE40e52fF1fE0745c" |
| + | "0x60C460346394178b79CC9254D397B44a074e1dbD" |
| values.pendingSanctions.216._timestamp: | |
| - | 1743368220 |
| + | 1743368147 |
| values.pendingSanctions.215._to: | |
| - | "0x60C460346394178b79CC9254D397B44a074e1dbD" |
| + | "0x7CB6AfA77bb4E67b4c24293D3B5C5052851b5EB0" |
| values.pendingSanctions.215._timestamp: | |
| - | 1743368147 |
| + | 1743368167 |
| values.pendingSanctions.214._to: | |
| - | "0x7CB6AfA77bb4E67b4c24293D3B5C5052851b5EB0" |
| + | "0x8e31D4A303eDEeE7ca509CCC8D5965f50D6B25D8" |
| values.pendingSanctions.213._to: | |
| - | "0x8e31D4A303eDEeE7ca509CCC8D5965f50D6B25D8" |
| + | "0x8006D189F5311E28E7A43E843c9AF675CEBef4AF" |
| values.pendingSanctions.212._to: | |
| - | "0x8006D189F5311E28E7A43E843c9AF675CEBef4AF" |
| + | "0x894341e79e60b06C5D64684200BAb31C3c77AeF7" |
| values.pendingSanctions.211._to: | |
| - | "0x894341e79e60b06C5D64684200BAb31C3c77AeF7" |
| + | "0x9a46f537e8eA30BCCeDB0B7A2EBE03b16Df1170C" |
| values.pendingSanctions.211._timestamp: | |
| - | 1743368167 |
| + | 1743368190 |
| values.pendingSanctions.210._to: | |
| - | "0x9a46f537e8eA30BCCeDB0B7A2EBE03b16Df1170C" |
| + | "0x3C9A0d73EF1a155e0b94CCc498068C1DB85fbEb5" |
| values.pendingSanctions.210._timestamp: | |
| - | 1743368190 |
| + | 1743368100 |
| values.pendingSanctions.209._to: | |
| - | "0x3C9A0d73EF1a155e0b94CCc498068C1DB85fbEb5" |
| + | "0xE9Cb04a602cAA9D2C649dDE854Ab7389C98CF912" |
| values.pendingSanctions.209._timestamp: | |
| - | 1743368100 |
| + | 1706139865 |
| values.pendingSanctions.208._to: | |
| - | "0xE9Cb04a602cAA9D2C649dDE854Ab7389C98CF912" |
| + | "0x459A9b243DE7aab18c60E25Ab0D6c99A445faC12" |
| values.pendingSanctions.208._timestamp: | |
| - | 1706139865 |
| + | 1743368117 |
| values.pendingSanctions.207._to: | |
| - | "0x459A9b243DE7aab18c60E25Ab0D6c99A445faC12" |
| + | "0x3dec956335f3E48DC1Fb99DC9A2d21350a30e245" |
| values.pendingSanctions.206._to: | |
| - | "0x3dec956335f3E48DC1Fb99DC9A2d21350a30e245" |
| + | "0xaa7Fc1a0c9fcb6721a082740d7E4BC0885951d7a" |
| values.pendingSanctions.206._timestamp: | |
| - | 1743368117 |
| + | 1743368466 |
| values.pendingSanctions.205._to: | |
| - | "0xaa7Fc1a0c9fcb6721a082740d7E4BC0885951d7a" |
| + | "0x2B5CA5A2ABd55846C02439Dd268Ae733F104C866" |
| values.pendingSanctions.205._timestamp: | |
| - | 1743368466 |
| + | 1743368100 |
| values.pendingSanctions.204._to: | |
| - | "0x2B5CA5A2ABd55846C02439Dd268Ae733F104C866" |
| + | "0x73fcfBefa7e9650049c7BcA3c76F99D085Eaf462" |
| values.pendingSanctions.204._timestamp: | |
| - | 1743368100 |
| + | 1743368147 |
| values.pendingSanctions.203._to: | |
| - | "0x73fcfBefa7e9650049c7BcA3c76F99D085Eaf462" |
| + | "0x45Ace2D41040B7267a465A4dF8733F3327EEFBb5" |
| values.pendingSanctions.203._timestamp: | |
| - | 1743368147 |
| + | 1719715444 |
| values.pendingSanctions.202._to: | |
| - | "0x45Ace2D41040B7267a465A4dF8733F3327EEFBb5" |
| + | "0xCf4b2B67e584F71f0a888817Eab97061e0CcC139" |
| values.pendingSanctions.202._timestamp: | |
| - | 1719715444 |
| + | 1743368220 |
| values.pendingSanctions.201._to: | |
| - | "0xCf4b2B67e584F71f0a888817Eab97061e0CcC139" |
| + | "0x579e88fF20811E8B7327A1b81d324E2302337E3B" |
| values.pendingSanctions.201._timestamp: | |
| - | 1743368220 |
| + | 1743368131 |
| values.pendingSanctions.200._to: | |
| - | "0x579e88fF20811E8B7327A1b81d324E2302337E3B" |
| + | "0x76De7fC28E69bb78e6475C8Fd71B71793B663E31" |
| values.pendingSanctions.200._timestamp: | |
| - | 1743368131 |
| + | 1707346822 |
| values.pendingSanctions.199._to: | |
| - | "0x76De7fC28E69bb78e6475C8Fd71B71793B663E31" |
| + | "0x4C403211d9BcAC321b683e0161CED2cE749FF0A4" |
| values.pendingSanctions.199._timestamp: | |
| - | 1707346822 |
| + | 1743368131 |
| values.pendingSanctions.198._to: | |
| - | "0x4C403211d9BcAC321b683e0161CED2cE749FF0A4" |
| + | "0x7B31BC4FD8A00f734690AD0607903AA2C770a802" |
| values.pendingSanctions.198._timestamp: | |
| - | 1743368131 |
| + | 1718846645 |
| values.pendingSanctions.197._to: | |
| - | "0x7B31BC4FD8A00f734690AD0607903AA2C770a802" |
| + | "0x4E5c14bc3E148C01d02f9086c889f6a7854eEa42" |
| values.pendingSanctions.197._timestamp: | |
| - | 1718846645 |
| + | 1743394746 |
| values.pendingSanctions.196._to: | |
| - | "0x4E5c14bc3E148C01d02f9086c889f6a7854eEa42" |
| + | "0x2bD3B86856EEeC97CbC01150833aCc0771491049" |
| values.pendingSanctions.196._timestamp: | |
| - | 1743394746 |
| + | 1743368100 |
| values.pendingSanctions.195._to: | |
| - | "0x2bD3B86856EEeC97CbC01150833aCc0771491049" |
| + | "0x463d21B0620C77620aeD87A769e5836132158855" |
| values.pendingSanctions.195._timestamp: | |
| - | 1743368100 |
| + | 1707627639 |
| values.pendingSanctions.194._to: | |
| - | "0x463d21B0620C77620aeD87A769e5836132158855" |
| + | "0x4fc472c29A8cBED38ce871a4Caf6CbDd1Cfd3369" |
| values.pendingSanctions.194._timestamp: | |
| - | 1707627639 |
| + | 1743368131 |
| values.pendingSanctions.193._to: | |
| - | "0x4fc472c29A8cBED38ce871a4Caf6CbDd1Cfd3369" |
| + | "0xA911DDC91FDBDBBe22dD219CA05DC8634e9255d2" |
| values.pendingSanctions.193._timestamp: | |
| - | 1743368131 |
| + | 1743368207 |
| values.pendingSanctions.192._to: | |
| - | "0xA911DDC91FDBDBBe22dD219CA05DC8634e9255d2" |
| + | "0xB84a63047b0E7b6e1C670479C5ae682e6386d423" |
| values.pendingSanctions.192._timestamp: | |
| - | 1743368207 |
| + | 1743394986 |
| values.pendingSanctions.191._to: | |
| - | "0xB84a63047b0E7b6e1C670479C5ae682e6386d423" |
| + | "0xD0aC63a724dCb105561F981c3D9dda033570193e" |
| values.pendingSanctions.191._timestamp: | |
| - | 1743394986 |
| + | 1718846587 |
| values.pendingSanctions.190._to: | |
| - | "0xD0aC63a724dCb105561F981c3D9dda033570193e" |
| + | "0x81c0d080426CbEa108c1e74C712a6A2ceDAB89e1" |
| values.pendingSanctions.190._timestamp: | |
| - | 1718846587 |
| + | 1743368167 |
| values.pendingSanctions.189._to: | |
| - | "0x81c0d080426CbEa108c1e74C712a6A2ceDAB89e1" |
| + | "0xfb02369649FABe532c600983C41840d54F4592a7" |
| values.pendingSanctions.189._timestamp: | |
| - | 1743368167 |
| + | 1743368523 |
| values.pendingSanctions.188._to: | |
| - | "0xfb02369649FABe532c600983C41840d54F4592a7" |
| + | "0x660dD692777AF51FBFE15C5B47178994d825911a" |
| values.pendingSanctions.188._timestamp: | |
| - | 1743368523 |
| + | 1743368147 |
| values.pendingSanctions.187._to: | |
| - | "0x660dD692777AF51FBFE15C5B47178994d825911a" |
| + | "0xb4696a1465286802b7Bc8E39120B10F951E07C4d" |
| values.pendingSanctions.187._timestamp: | |
| - | 1743368147 |
| + | 1743368466 |
| values.pendingSanctions.186._to: | |
| - | "0xb4696a1465286802b7Bc8E39120B10F951E07C4d" |
| + | "0xfB474dDfDc91293aD2a37A58DC94D6505d2c88dF" |
| values.pendingSanctions.186._timestamp: | |
| - | 1743368466 |
| + | 1738203485 |
| values.pendingSanctions.185._to: | |
| - | "0xfB474dDfDc91293aD2a37A58DC94D6505d2c88dF" |
| + | "0xd382432B50d12b5803A7D666662320ceEe22313f" |
| values.pendingSanctions.185._timestamp: | |
| - | 1738203485 |
| + | 1743368491 |
| values.pendingSanctions.184._to: | |
| - | "0xd382432B50d12b5803A7D666662320ceEe22313f" |
| + | "0x298805bE3bbe036224BB11cE5007636423ca46F6" |
| values.pendingSanctions.184._timestamp: | |
| - | 1743368491 |
| + | 1743368100 |
| values.pendingSanctions.183._to: | |
| - | "0x298805bE3bbe036224BB11cE5007636423ca46F6" |
| + | "0xdFc1f20b21259ee313d20D33D46D54691E4371CB" |
| values.pendingSanctions.183._timestamp: | |
| - | 1743368100 |
| + | 1743368491 |
| values.pendingSanctions.182._to: | |
| - | "0xdFc1f20b21259ee313d20D33D46D54691E4371CB" |
| + | "0xC2068323986708a8b2480Bf491B4ad5921234EF7" |
| values.pendingSanctions.182._timestamp: | |
| - | 1743368491 |
| + | 1743368220 |
| values.pendingSanctions.181._to: | |
| - | "0xC2068323986708a8b2480Bf491B4ad5921234EF7" |
| + | "0xf2670E8C64430F10163e53BD38e71741d18D7840" |
| values.pendingSanctions.181._timestamp: | |
| - | 1743368220 |
| + | 1743368491 |
| values.pendingSanctions.180._to: | |
| - | "0xf2670E8C64430F10163e53BD38e71741d18D7840" |
| + | "0xb064e41602F2EA83741161A27DC045A6dD7F6b93" |
| values.pendingSanctions.180._timestamp: | |
| - | 1743368491 |
| + | 1743368466 |
| values.pendingSanctions.179._to: | |
| - | "0xb064e41602F2EA83741161A27DC045A6dD7F6b93" |
| + | "0xdE2c001797a4a6e8784743FB1835F82efb95b18f" |
| values.pendingSanctions.179._timestamp: | |
| - | 1743368466 |
| + | 1743368491 |
| values.pendingSanctions.178._to: | |
| - | "0xdE2c001797a4a6e8784743FB1835F82efb95b18f" |
| + | "0x80c5A724E484B2b96c61c45e06918D7B68dB256B" |
| values.pendingSanctions.178._timestamp: | |
| - | 1743368491 |
| + | 1743368167 |
| values.pendingSanctions.177._to: | |
| - | "0x80c5A724E484B2b96c61c45e06918D7B68dB256B" |
| + | "0x8Cf85f74408Cb7e27cF0f52493c93fF6E150BAFa" |
| values.pendingSanctions.176._to: | |
| - | "0x8Cf85f74408Cb7e27cF0f52493c93fF6E150BAFa" |
| + | "0x927491618ECd06afBCEDeA84a2fEF71c991f00Eb" |
| values.pendingSanctions.176._timestamp: | |
| - | 1743368167 |
| + | 1707354023 |
| values.pendingSanctions.175._to: | |
| - | "0x927491618ECd06afBCEDeA84a2fEF71c991f00Eb" |
| + | "0x8862Dd4657aBCdf04c96402cD4C3007511538500" |
| values.pendingSanctions.175._timestamp: | |
| - | 1707354023 |
| + | 1719718683 |
| values.pendingSanctions.174._to: | |
| - | "0x8862Dd4657aBCdf04c96402cD4C3007511538500" |
| + | "0x28c6fFE7b230F54510247FE09e5CbaaAB314ee82" |
| values.pendingSanctions.174._timestamp: | |
| - | 1719718683 |
| + | 1743368100 |
| values.pendingSanctions.173._to: | |
| - | "0x28c6fFE7b230F54510247FE09e5CbaaAB314ee82" |
| + | "0x2ed2A34623aF70467ef88E473a693F879176B5a2" |
| values.pendingSanctions.172._to: | |
| - | "0x2ed2A34623aF70467ef88E473a693F879176B5a2" |
| + | "0x6402119871Cc942Edc26e4815B99711750B87DBB" |
| values.pendingSanctions.172._timestamp: | |
| - | 1743368100 |
| + | 1719718623 |
| values.pendingSanctions.171._to: | |
| - | "0x6402119871Cc942Edc26e4815B99711750B87DBB" |
| + | "0x437415907a0FdB07aeDCaBC085Cf940D370cfA6c" |
| values.pendingSanctions.171._timestamp: | |
| - | 1719718623 |
| + | 1743368117 |
| values.pendingSanctions.170._to: | |
| - | "0x437415907a0FdB07aeDCaBC085Cf940D370cfA6c" |
| + | "0x773d712C230654121bE68D09C4ccaA9011d20895" |
| values.pendingSanctions.170._timestamp: | |
| - | 1743368117 |
| + | 1743368167 |
| values.pendingSanctions.169._to: | |
| - | "0x773d712C230654121bE68D09C4ccaA9011d20895" |
| + | "0x4813eD84135cB27eC096d8b86eE35B8d62402c07" |
| values.pendingSanctions.169._timestamp: | |
| - | 1743368167 |
| + | 1743368117 |
| values.pendingSanctions.168._to: | |
| - | "0x4813eD84135cB27eC096d8b86eE35B8d62402c07" |
| + | "0xc3106dd6f982d4269a6618E77f49927d44BCCafD" |
| values.pendingSanctions.168._timestamp: | |
| - | 1743368117 |
| + | 1706580004 |
| values.pendingSanctions.167._to: | |
| - | "0xc3106dd6f982d4269a6618E77f49927d44BCCafD" |
| + | "0x3EA0B857a9579259096F067b6Dd914D1ae75C338" |
| values.pendingSanctions.167._timestamp: | |
| - | 1706580004 |
| + | 1743368100 |
| values.pendingSanctions.166._to: | |
| - | "0x3EA0B857a9579259096F067b6Dd914D1ae75C338" |
| + | "0xA74B09B9f886ac101FDB1091147f4a67FE7c19e7" |
| values.pendingSanctions.166._timestamp: | |
| - | 1743368100 |
| + | 1743368207 |
| values.pendingSanctions.165._to: | |
| - | "0xA74B09B9f886ac101FDB1091147f4a67FE7c19e7" |
| + | "0x96D4FD6006d1BBAF629feeAec1ddDB9D13bd5778" |
| values.pendingSanctions.165._timestamp: | |
| - | 1743368207 |
| + | 1743368190 |
| values.pendingSanctions.164._to: | |
| - | "0x96D4FD6006d1BBAF629feeAec1ddDB9D13bd5778" |
| + | "0x4DF0384CA53D96bbED7452f10b9dDC325AF037c0" |
| values.pendingSanctions.164._timestamp: | |
| - | 1743368190 |
| + | 1743368131 |
| values.pendingSanctions.163._to: | |
| - | "0x4DF0384CA53D96bbED7452f10b9dDC325AF037c0" |
| + | "0x6e77aE496c67441Ee772f88471b27Bf62Ef04d07" |
| values.pendingSanctions.163._timestamp: | |
| - | 1743368131 |
| + | 1743368147 |
| values.pendingSanctions.162._to: | |
| - | "0x6e77aE496c67441Ee772f88471b27Bf62Ef04d07" |
| + | "0xC6235424501FF4dCEf8fC7C96DFD9474b40E95E6" |
| values.pendingSanctions.162._timestamp: | |
| - | 1743368147 |
| + | 1743368220 |
| values.pendingSanctions.161._to: | |
| - | "0xC6235424501FF4dCEf8fC7C96DFD9474b40E95E6" |
| + | "0xf152EBa9da07Bec19fbd6078D9dB047E74687A6a" |
| values.pendingSanctions.161._timestamp: | |
| - | 1743368220 |
| + | 1743368491 |
| values.pendingSanctions.160._to: | |
| - | "0xf152EBa9da07Bec19fbd6078D9dB047E74687A6a" |
| + | "0x9b70559E61949033dE5a90F58fD4ed051470B851" |
| values.pendingSanctions.160._timestamp: | |
| - | 1743368491 |
| + | 1743368190 |
| values.pendingSanctions.159._to: | |
| - | "0x9b70559E61949033dE5a90F58fD4ed051470B851" |
| + | "0x59ED194974A49f7D817EC46bCE8E00A6F24133E1" |
| values.pendingSanctions.159._timestamp: | |
| - | 1743368190 |
| + | 1743368131 |
| values.pendingSanctions.158._to: | |
| - | "0x59ED194974A49f7D817EC46bCE8E00A6F24133E1" |
| + | "0x015374c2Dc040eE1c40739936C72D5F035186f0f" |
| values.pendingSanctions.158._timestamp: | |
| - | 1743368131 |
| + | 1706662831 |
| values.pendingSanctions.157._to: | |
| - | "0x015374c2Dc040eE1c40739936C72D5F035186f0f" |
| + | "0xbd0e49D0dA6F10e8A74964e8282B86900396f7A3" |
| values.pendingSanctions.157._timestamp: | |
| - | 1706662831 |
| + | 1743368466 |
| values.pendingSanctions.156._to: | |
| - | "0xbd0e49D0dA6F10e8A74964e8282B86900396f7A3" |
| + | "0xB92293Fd1D65c09361f863bF4d202cff763CE9e4" |
| values.pendingSanctions.156._timestamp: | |
| - | 1743368466 |
| + | 1743368207 |
| values.pendingSanctions.155._to: | |
| - | "0xB92293Fd1D65c09361f863bF4d202cff763CE9e4" |
| + | "0x585E38F443aFEA52D5DB05A273d0145Bd17887be" |
| values.pendingSanctions.155._timestamp: | |
| - | 1743368207 |
| + | 1743368131 |
| values.pendingSanctions.154._to: | |
| - | "0x585E38F443aFEA52D5DB05A273d0145Bd17887be" |
| + | "0x95263Dab911Dd8B05ED1713f2549E9C8cf574323" |
| values.pendingSanctions.154._timestamp: | |
| - | 1743368131 |
| + | 1743368190 |
| values.pendingSanctions.153._to: | |
| - | "0x95263Dab911Dd8B05ED1713f2549E9C8cf574323" |
| + | "0x8cc7888b6C9B9EF917CdE097210a7eB12ca8441e" |
| values.pendingSanctions.153._timestamp: | |
| - | 1743368190 |
| + | 1743368167 |
| values.pendingSanctions.152._to: | |
| - | "0x8cc7888b6C9B9EF917CdE097210a7eB12ca8441e" |
| + | "0x10888fc193ec8a5b9ce29a0213473B2ceFA1E707" |
| values.pendingSanctions.152._timestamp: | |
| - | 1743368167 |
| + | 1719715565 |
| values.pendingSanctions.151._to: | |
| - | "0x10888fc193ec8a5b9ce29a0213473B2ceFA1E707" |
| + | "0x9868A6E272365Ec421C3aF0690F5aa97121B91c4" |
| values.pendingSanctions.151._timestamp: | |
| - | 1719715565 |
| + | 1743368190 |
| values.pendingSanctions.150._to: | |
| - | "0x9868A6E272365Ec421C3aF0690F5aa97121B91c4" |
| + | "0x61C81bBa4D9b4cc3BB109Fcf1482cb5Ce4b87205" |
| values.pendingSanctions.150._timestamp: | |
| - | 1743368190 |
| + | 1743368147 |
| values.pendingSanctions.149._to: | |
| - | "0x61C81bBa4D9b4cc3BB109Fcf1482cb5Ce4b87205" |
| + | "0x9E33F1333587Ee7f96772523821187de185d2ead" |
| values.pendingSanctions.149._timestamp: | |
| - | 1743368147 |
| + | 1719715565 |
| values.pendingSanctions.148._to: | |
| - | "0x9E33F1333587Ee7f96772523821187de185d2ead" |
| + | "0x23C1c317368AB6Dc5F92a496e08A79ceE6f90392" |
| values.pendingSanctions.148._timestamp: | |
| - | 1719715565 |
| + | 1719718683 |
| values.pendingSanctions.147._to: | |
| - | "0x23C1c317368AB6Dc5F92a496e08A79ceE6f90392" |
| + | "0xfd1dCf92A221f333061575FD8B7D02b6E3A5957D" |
| values.pendingSanctions.147._timestamp: | |
| - | 1719718683 |
| + | 1710867621 |
| values.pendingSanctions.146._to: | |
| - | "0xfd1dCf92A221f333061575FD8B7D02b6E3A5957D" |
| + | "0x3b2E6A063125c95f327aE214eD1F20B901801059" |
| values.pendingSanctions.146._timestamp: | |
| - | 1710867621 |
| + | 1719715506 |
| values.pendingSanctions.145._to: | |
| - | "0x3b2E6A063125c95f327aE214eD1F20B901801059" |
| + | "0xAb96909d9a35150a249a55670e0bB8B8C583565b" |
| values.pendingSanctions.145._timestamp: | |
| - | 1719715506 |
| + | 1743368207 |
| values.pendingSanctions.144._to: | |
| - | "0xAb96909d9a35150a249a55670e0bB8B8C583565b" |
| + | "0x9381d90765A0cE4BE62e4cE9f115291C6244862E" |
| values.pendingSanctions.144._timestamp: | |
| - | 1743368207 |
| + | 1743368190 |
| values.pendingSanctions.143._to: | |
| - | "0x9381d90765A0cE4BE62e4cE9f115291C6244862E" |
| + | "0xbDbb9De0ee5c3CC100bf0DcF0e11881Ea568307D" |
| values.pendingSanctions.143._timestamp: | |
| - | 1743368190 |
| + | 1743368466 |
| values.pendingSanctions.142._to: | |
| - | "0xbDbb9De0ee5c3CC100bf0DcF0e11881Ea568307D" |
| + | "0x41b6cBA6EDf1bD2BC61b80B228104bb27db3e504" |
| values.pendingSanctions.142._timestamp: | |
| - | 1743368466 |
| + | 1743368117 |
| values.pendingSanctions.141._to: | |
| - | "0x41b6cBA6EDf1bD2BC61b80B228104bb27db3e504" |
| + | "0xB907Fd315C94FE2D2484B426f293D9980Da40A3d" |
| values.pendingSanctions.141._timestamp: | |
| - | 1743368117 |
| + | 1743368207 |
| values.pendingSanctions.140._to: | |
| - | "0xB907Fd315C94FE2D2484B426f293D9980Da40A3d" |
| + | "0xF936497C1E9215fdf91E0332c6D6D50b528Df14d" |
| values.pendingSanctions.140._timestamp: | |
| - | 1743368207 |
| + | 1743368286 |
| values.pendingSanctions.139._to: | |
| - | "0xF936497C1E9215fdf91E0332c6D6D50b528Df14d" |
| + | "0xc77D572231C4b8bfe3c4DB4aF478ad17FEBA0648" |
| values.pendingSanctions.139._timestamp: | |
| - | 1743368286 |
| + | 1743368466 |
| values.pendingSanctions.138._to: | |
| - | "0xc77D572231C4b8bfe3c4DB4aF478ad17FEBA0648" |
| + | "0x69E657BD35BA291D6A299F47d10249F24C86edD8" |
| values.pendingSanctions.138._timestamp: | |
| - | 1743368466 |
| + | 1743394623 |
| values.pendingSanctions.137._to: | |
| - | "0x69E657BD35BA291D6A299F47d10249F24C86edD8" |
| + | "0xE6f4103fCbdae587756C8273a440DFf8BA4Bb21a" |
| values.pendingSanctions.137._timestamp: | |
| - | 1743394623 |
| + | 1743368286 |
| values.pendingSanctions.136._to: | |
| - | "0xE6f4103fCbdae587756C8273a440DFf8BA4Bb21a" |
| + | "0xAE932423eb4c00139dF70b2644CfF269b110E130" |
| values.pendingSanctions.136._timestamp: | |
| - | 1743368286 |
| + | 1743368207 |
| values.pendingSanctions.135._to: | |
| - | "0xAE932423eb4c00139dF70b2644CfF269b110E130" |
| + | "0x3C43b337a56c5c9387614ebfAC01d3b5d0734Fcc" |
| values.pendingSanctions.135._timestamp: | |
| - | 1743368207 |
| + | 1743368100 |
| values.pendingSanctions.134._to: | |
| - | "0x3C43b337a56c5c9387614ebfAC01d3b5d0734Fcc" |
| + | "0x9991bCFde3f20Cc14A893CcC3a32b81801C80253" |
| values.pendingSanctions.134._timestamp: | |
| - | 1743368100 |
| + | 1743368190 |
| values.pendingSanctions.133._to: | |
| - | "0x9991bCFde3f20Cc14A893CcC3a32b81801C80253" |
| + | "0x7Faf6f69caD10Eaf3903847434bF92b4Bb6fC955" |
| values.pendingSanctions.133._timestamp: | |
| - | 1743368190 |
| + | 1719718623 |
| values.pendingSanctions.132._to: | |
| - | "0x7Faf6f69caD10Eaf3903847434bF92b4Bb6fC955" |
| + | "0xC6138fB05b8c0536EB2Ea791D2504eA72420d7d7" |
| values.pendingSanctions.132._timestamp: | |
| - | 1719718623 |
| + | 1743394623 |
| values.pendingSanctions.131._to: | |
| - | "0xC6138fB05b8c0536EB2Ea791D2504eA72420d7d7" |
| + | "0x5F0d5D4DA8692787F5267415DCc2494526E1C507" |
| values.pendingSanctions.131._timestamp: | |
| - | 1743394623 |
| + | 1743368131 |
| values.pendingSanctions.130._to: | |
| - | "0x5F0d5D4DA8692787F5267415DCc2494526E1C507" |
| + | "0x127917d1A8308Da2a1400dB50346B4a3F17813d3" |
| values.pendingSanctions.130._timestamp: | |
| - | 1743368131 |
| + | 1743394565 |
| values.pendingSanctions.129._to: | |
| - | "0x127917d1A8308Da2a1400dB50346B4a3F17813d3" |
| + | "0xB7522F061afb810b411a858769e2295A10080a32" |
| values.pendingSanctions.129._timestamp: | |
| - | 1743394565 |
| + | 1743368207 |
| values.pendingSanctions.128._to: | |
| - | "0xB7522F061afb810b411a858769e2295A10080a32" |
| + | "0xA98522A6a33c97af048aB966460e3C57Cd44eB17" |
| values.pendingSanctions.127._to: | |
| - | "0xA98522A6a33c97af048aB966460e3C57Cd44eB17" |
| + | "0x2548e483ceeFBe4de727f2F853AF0124869Ae75E" |
| values.pendingSanctions.127._timestamp: | |
| - | 1743368207 |
| + | 1707566427 |
| values.pendingSanctions.126._to: | |
| - | "0x2548e483ceeFBe4de727f2F853AF0124869Ae75E" |
| + | "0xc2811Dfd12FF70b229d26E465359664f9e60b9D2" |
| values.pendingSanctions.126._timestamp: | |
| - | 1707566427 |
| + | 1706148032 |
| values.pendingSanctions.125._to: | |
| - | "0xc2811Dfd12FF70b229d26E465359664f9e60b9D2" |
| + | "0xD823abbe3EdAB9A7175EBbE13b2891A3356F06ab" |
| values.pendingSanctions.125._timestamp: | |
| - | 1706148032 |
| + | 1743368220 |
| values.pendingSanctions.124._to: | |
| - | "0xD823abbe3EdAB9A7175EBbE13b2891A3356F06ab" |
| + | "0x07B69c2e2dE1e41EA60F6E5e382012774A61A80a" |
| values.pendingSanctions.124._timestamp: | |
| - | 1743368220 |
| + | 1743367391 |
| values.pendingSanctions.123._to: | |
| - | "0x07B69c2e2dE1e41EA60F6E5e382012774A61A80a" |
| + | "0xC7370caAfFE87e1089b1E86f3D6dc6283effdb3E" |
| values.pendingSanctions.123._timestamp: | |
| - | 1743367391 |
| + | 1743368220 |
| values.pendingSanctions.122._to: | |
| - | "0xC7370caAfFE87e1089b1E86f3D6dc6283effdb3E" |
| + | "0xcd82cdd2023BCc783bef35fDb86a70baA368c2c3" |
| values.pendingSanctions.122._timestamp: | |
| - | 1743368220 |
| + | 1743368466 |
| values.pendingSanctions.121._to: | |
| - | "0xcd82cdd2023BCc783bef35fDb86a70baA368c2c3" |
| + | "0x9baE98859a9D5Ba64AD43E0C22F99d8BAd7FB554" |
| values.pendingSanctions.121._timestamp: | |
| - | 1743368466 |
| + | 1710363512 |
| values.pendingSanctions.120._to: | |
| - | "0x9baE98859a9D5Ba64AD43E0C22F99d8BAd7FB554" |
| + | "0x0828b8Fe631347dA81a46E3D23394C3b18395aD4" |
| values.pendingSanctions.120._timestamp: | |
| - | 1710363512 |
| + | 1707498031 |
| values.pendingSanctions.119._to: | |
| - | "0x0828b8Fe631347dA81a46E3D23394C3b18395aD4" |
| + | "0x30096fdCc337A5395d275ecba9d0558484baad31" |
| values.pendingSanctions.119._timestamp: | |
| - | 1707498031 |
| + | 1743368100 |
| values.pendingSanctions.118._to: | |
| - | "0x30096fdCc337A5395d275ecba9d0558484baad31" |
| + | "0x3787445aa612a19D140840862cEf99694d9EA3De" |
| values.pendingSanctions.117._to: | |
| - | "0x3787445aa612a19D140840862cEf99694d9EA3De" |
| + | "0xdF45DcC1C326Af55ac389D09327d79699839E31b" |
| values.pendingSanctions.117._timestamp: | |
| - | 1743368100 |
| + | 1743368491 |
| values.pendingSanctions.116._to: | |
| - | "0xdF45DcC1C326Af55ac389D09327d79699839E31b" |
| + | "0xdb563dA812f5d90727bb12a0959F5679B9a2Ea5F" |
| values.pendingSanctions.116._timestamp: | |
| - | 1743368491 |
| + | 1710533543 |
| values.pendingSanctions.115._to: | |
| - | "0xdb563dA812f5d90727bb12a0959F5679B9a2Ea5F" |
| + | "0x47c33fd0772e8B103aBEe763d1C2FB864b665B3B" |
| values.pendingSanctions.115._timestamp: | |
| - | 1710533543 |
| + | 1743368117 |
| values.pendingSanctions.114._to: | |
| - | "0x47c33fd0772e8B103aBEe763d1C2FB864b665B3B" |
| + | "0xda250570f0DBf9650C8f80989390e71118A64B51" |
| values.pendingSanctions.114._timestamp: | |
| - | 1743368117 |
| + | 1743368491 |
| values.pendingSanctions.113._to: | |
| - | "0xda250570f0DBf9650C8f80989390e71118A64B51" |
| + | "0x52F09693c9eEaA93A64BA697e3d3e43a1eB65477" |
| values.pendingSanctions.113._timestamp: | |
| - | 1743368491 |
| + | 1707401778 |
| values.pendingSanctions.112._to: | |
| - | "0x52F09693c9eEaA93A64BA697e3d3e43a1eB65477" |
| + | "0x9568D407b9BD55F20d20982306C6Feca5e43eb47" |
| values.pendingSanctions.112._timestamp: | |
| - | 1707401778 |
| + | 1743368190 |
| values.pendingSanctions.111._to: | |
| - | "0x9568D407b9BD55F20d20982306C6Feca5e43eb47" |
| + | "0xD32f6b08314E52744d244c764d1DA85c04514f34" |
| values.pendingSanctions.111._timestamp: | |
| - | 1743368190 |
| + | 1743368220 |
| values.pendingSanctions.110._to: | |
| - | "0xD32f6b08314E52744d244c764d1DA85c04514f34" |
| + | "0x6E944c6B214B215dfe053e7287f04f700a467DA8" |
| values.pendingSanctions.110._timestamp: | |
| - | 1743368220 |
| + | 1743368147 |
| values.pendingSanctions.109._to: | |
| - | "0x6E944c6B214B215dfe053e7287f04f700a467DA8" |
| + | "0x1d9E490938feD3dF12A09528aa25ff6620d69d1b" |
| values.pendingSanctions.109._timestamp: | |
| - | 1743368147 |
| + | 1743367401 |
| values.pendingSanctions.108._to: | |
| - | "0x1d9E490938feD3dF12A09528aa25ff6620d69d1b" |
| + | "0xdb563dA812f5d90727bb12a0959F5679B9a2Ea5F" |
| values.pendingSanctions.108._timestamp: | |
| - | 1743367401 |
| + | 1710533376 |
| values.pendingSanctions.107._to: | |
| - | "0xdb563dA812f5d90727bb12a0959F5679B9a2Ea5F" |
| + | "0x09A95021fB4E9C7e391B3e7D4726748251C5d970" |
| values.pendingSanctions.107._timestamp: | |
| - | 1710533376 |
| + | 1743367391 |
| values.pendingSanctions.106._to: | |
| - | "0x09A95021fB4E9C7e391B3e7D4726748251C5d970" |
| + | "0xF8e3A7C50095B105dd049643f32531cDE57eBDA7" |
| values.pendingSanctions.106._timestamp: | |
| - | 1743367391 |
| + | 1743368286 |
| values.pendingSanctions.105._to: | |
| - | "0xF8e3A7C50095B105dd049643f32531cDE57eBDA7" |
| + | "0xaACA709AaD0E99891A16c4e2028Ad5053cEeB2b0" |
| values.pendingSanctions.104._to: | |
| - | "0xaACA709AaD0E99891A16c4e2028Ad5053cEeB2b0" |
| + | "0x1695b31503e1C49123c000ab24626750b858E972" |
| values.pendingSanctions.104._timestamp: | |
| - | 1743368286 |
| + | 1743367401 |
| values.pendingSanctions.103._to: | |
| - | "0x1695b31503e1C49123c000ab24626750b858E972" |
| + | "0x42AAd1F0E18C9867Dd1bE8FB7E6f4119BAC62740" |
| values.pendingSanctions.103._timestamp: | |
| - | 1743367401 |
| + | 1743368117 |
| values.pendingSanctions.102._to: | |
| - | "0x42AAd1F0E18C9867Dd1bE8FB7E6f4119BAC62740" |
| + | "0xb2c54B111705B23BCB4cf584C396982c3B613F99" |
| values.pendingSanctions.102._timestamp: | |
| - | 1743368117 |
| + | 1707739213 |
| values.pendingSanctions.101._to: | |
| - | "0xb2c54B111705B23BCB4cf584C396982c3B613F99" |
| + | "0x3c500E160EaB2CD26027a3389b70ED4e17cd9544" |
| values.pendingSanctions.101._timestamp: | |
| - | 1707739213 |
| + | 1743368117 |
| values.pendingSanctions.100._to: | |
| - | "0x3c500E160EaB2CD26027a3389b70ED4e17cd9544" |
| + | "0xa5AFC38dDBE6e2dda8dC7A4fdae380a9Dbe12a06" |
| values.pendingSanctions.100._timestamp: | |
| - | 1743368117 |
| + | 1707472806 |
| values.pendingSanctions.99._to: | |
| - | "0xa5AFC38dDBE6e2dda8dC7A4fdae380a9Dbe12a06" |
| + | "0xac2ec1ec2E53098Ebbd36753187CDDf7E3d438AB" |
| values.pendingSanctions.99._timestamp: | |
| - | 1707472806 |
| + | 1743368466 |
| values.pendingSanctions.98._to: | |
| - | "0xac2ec1ec2E53098Ebbd36753187CDDf7E3d438AB" |
| + | "0x0E00e97FefD00F71b54E038899a97b470D6f662F" |
| values.pendingSanctions.98._timestamp: | |
| - | 1743368466 |
| + | 1719718683 |
| values.pendingSanctions.97._to: | |
| - | "0x0E00e97FefD00F71b54E038899a97b470D6f662F" |
| + | "0xd9E77167C8b13b9D1AFF04CC469Ad55BEeB78358" |
| values.pendingSanctions.97._timestamp: | |
| - | 1719718683 |
| + | 1743368491 |
| values.pendingSanctions.96._to: | |
| - | "0xd9E77167C8b13b9D1AFF04CC469Ad55BEeB78358" |
| + | "0x4F5D61De15F7D9C933f78937295402b3E0D9AA6f" |
| values.pendingSanctions.96._timestamp: | |
| - | 1743368491 |
| + | 1708077610 |
| values.pendingSanctions.95._to: | |
| - | "0x4F5D61De15F7D9C933f78937295402b3E0D9AA6f" |
| + | "0xcf011278736204F57B343568A8A8DC09f266a834" |
| values.pendingSanctions.95._timestamp: | |
| - | 1708077610 |
| + | 1706580004 |
| values.pendingSanctions.94._to: | |
| - | "0xcf011278736204F57B343568A8A8DC09f266a834" |
| + | "0x63b6bbBcab97d26d87abfb2E68E63ebd7772C0cb" |
| values.pendingSanctions.94._timestamp: | |
| - | 1706580004 |
| + | 1743368147 |
| values.pendingSanctions.93._to: | |
| - | "0x63b6bbBcab97d26d87abfb2E68E63ebd7772C0cb" |
| + | "0xf6f06e71eFB2671eAaBcf6E2C090357c995C495D" |
| values.pendingSanctions.93._timestamp: | |
| - | 1743368147 |
| + | 1718846587 |
| values.pendingSanctions.92._to: | |
| - | "0xf6f06e71eFB2671eAaBcf6E2C090357c995C495D" |
| + | "0x1971eB33A28eCFa6BF701a6efec4255633F338FB" |
| values.pendingSanctions.92._timestamp: | |
| - | 1718846587 |
| + | 1718846645 |
| values.pendingSanctions.91._to: | |
| - | "0x1971eB33A28eCFa6BF701a6efec4255633F338FB" |
| + | "0xfF4a476cf39589be4b6Ad7e4b36d7156710b5c3e" |
| values.pendingSanctions.91._timestamp: | |
| - | 1718846645 |
| + | 1743368523 |
| values.pendingSanctions.90._to: | |
| - | "0xfF4a476cf39589be4b6Ad7e4b36d7156710b5c3e" |
| + | "0x62671619ccb07Db5f94A8381A308989C953A0Cc9" |
| values.pendingSanctions.90._timestamp: | |
| - | 1743368523 |
| + | 1743368147 |
| values.pendingSanctions.89._to: | |
| - | "0x62671619ccb07Db5f94A8381A308989C953A0Cc9" |
| + | "0xb6753e1DEbD7e615bC9c89aF2D2b8580F6B06b13" |
| values.pendingSanctions.89._timestamp: | |
| - | 1743368147 |
| + | 1743368466 |
| values.pendingSanctions.88._to: | |
| - | "0xb6753e1DEbD7e615bC9c89aF2D2b8580F6B06b13" |
| + | "0xcb1fb203B40de4EC7B685907D8901B249480e534" |
| values.pendingSanctions.88._timestamp: | |
| - | 1743368466 |
| + | 1743395045 |
| values.pendingSanctions.87._to: | |
| - | "0xcb1fb203B40de4EC7B685907D8901B249480e534" |
| + | "0x2AC29F4a5bA804844fCb72c2E1d739C7F24fC749" |
| values.pendingSanctions.87._timestamp: | |
| - | 1743395045 |
| + | 1743368100 |
| values.pendingSanctions.86._to: | |
| - | "0x2AC29F4a5bA804844fCb72c2E1d739C7F24fC749" |
| + | "0x9C31138FDb4baC14eAC4dbc0C4Ec8F1ea77E9682" |
| values.pendingSanctions.86._timestamp: | |
| - | 1743368100 |
| + | 1743368190 |
| values.pendingSanctions.85._to: | |
| - | "0x9C31138FDb4baC14eAC4dbc0C4Ec8F1ea77E9682" |
| + | "0xCD856EfFC6ee06b8395bCD81d46884356680D658" |
| values.pendingSanctions.85._timestamp: | |
| - | 1743368190 |
| + | 1743368220 |
| values.pendingSanctions.84._to: | |
| - | "0xCD856EfFC6ee06b8395bCD81d46884356680D658" |
| + | "0xEA240C87B28a5074abbb34058935AD26391e6126" |
| values.pendingSanctions.84._timestamp: | |
| - | 1743368220 |
| + | 1743368286 |
| values.pendingSanctions.83._to: | |
| - | "0xEA240C87B28a5074abbb34058935AD26391e6126" |
| + | "0xf5B0cF796D4E58c74480Ddc20A701d7d159D7C70" |
| values.pendingSanctions.83._timestamp: | |
| - | 1743368286 |
| + | 1743395045 |
| values.pendingSanctions.82._to: | |
| - | "0xf5B0cF796D4E58c74480Ddc20A701d7d159D7C70" |
| + | "0x634D84AFE8Bed2f308F99bdE4677A6D1F8DBfC6D" |
| values.pendingSanctions.82._timestamp: | |
| - | 1743395045 |
| + | 1743368147 |
| values.pendingSanctions.81._to: | |
| - | "0x634D84AFE8Bed2f308F99bdE4677A6D1F8DBfC6D" |
| + | "0xca3E2E5c75121Cb46360E4459F6F94dCA6D868f4" |
| values.pendingSanctions.81._timestamp: | |
| - | 1743368147 |
| + | 1707462016 |
| values.pendingSanctions.80._to: | |
| - | "0xca3E2E5c75121Cb46360E4459F6F94dCA6D868f4" |
| + | "0x8F14A1990cB5D327E545be6aF2a03B517aC58259" |
| values.pendingSanctions.80._timestamp: | |
| - | 1707462016 |
| + | 1706074667 |
| values.pendingSanctions.79._to: | |
| - | "0x8F14A1990cB5D327E545be6aF2a03B517aC58259" |
| + | "0xfafdcA2FfEE318eaA4463003F6a99A16B8FEe45c" |
| values.pendingSanctions.79._timestamp: | |
| - | 1706074667 |
| + | 1743368523 |
| values.pendingSanctions.78._to: | |
| - | "0xfafdcA2FfEE318eaA4463003F6a99A16B8FEe45c" |
| + | "0x3e8c3aB6C952d626A48EdBCA0fd86c891Ab3c63f" |
| values.pendingSanctions.78._timestamp: | |
| - | 1743368523 |
| + | 1743368117 |
| values.pendingSanctions.77._to: | |
| - | "0x3e8c3aB6C952d626A48EdBCA0fd86c891Ab3c63f" |
| + | "0x6dc56C56e81EE1D496274f9349696657Dd005B0a" |
| values.pendingSanctions.77._timestamp: | |
| - | 1743368117 |
| + | 1743368147 |
| values.pendingSanctions.76._to: | |
| - | "0x6dc56C56e81EE1D496274f9349696657Dd005B0a" |
| + | "0xC3124240b6faAC99FaCeaC43E9698efFc5A997ad" |
| values.pendingSanctions.76._timestamp: | |
| - | 1743368147 |
| + | 1743368220 |
| values.pendingSanctions.75._to: | |
| - | "0xC3124240b6faAC99FaCeaC43E9698efFc5A997ad" |
| + | "0x403fA81DB3CB6095007E8377500E676cB7dbFcB9" |
| values.pendingSanctions.75._timestamp: | |
| - | 1743368220 |
| + | 1743368117 |
| values.pendingSanctions.74._to: | |
| - | "0x403fA81DB3CB6095007E8377500E676cB7dbFcB9" |
| + | "0x6CDB95f68B61922d4fE0708e55792390D8c669e4" |
| values.pendingSanctions.74._timestamp: | |
| - | 1743368117 |
| + | 1719718623 |
| values.pendingSanctions.73._to: | |
| - | "0x6CDB95f68B61922d4fE0708e55792390D8c669e4" |
| + | "0x574CFb5AA6F7A05B111Cd298b73A4123AAfdF97f" |
| values.pendingSanctions.73._timestamp: | |
| - | 1719718623 |
| + | 1710932425 |
| values.pendingSanctions.72._to: | |
| - | "0x574CFb5AA6F7A05B111Cd298b73A4123AAfdF97f" |
| + | "0x2c0c5825cD05B58d504E76d0e0571b9Bc07DF2A3" |
| values.pendingSanctions.72._timestamp: | |
| - | 1710932425 |
| + | 1743368100 |
| values.pendingSanctions.71._to: | |
| - | "0x2c0c5825cD05B58d504E76d0e0571b9Bc07DF2A3" |
| + | "0x1E25292Ed119b1ca6aEaaF11F520ff0bCb638740" |
| values.pendingSanctions.71._timestamp: | |
| - | 1743368100 |
| + | 1743367401 |
| values.pendingSanctions.70._to: | |
| - | "0x1E25292Ed119b1ca6aEaaF11F520ff0bCb638740" |
| + | "0xCfcB156E4EB3f85A6FE1cec2DC83FBFEcF8Ee7FC" |
| values.pendingSanctions.70._timestamp: | |
| - | 1743367401 |
| + | 1743368220 |
| values.pendingSanctions.69._to: | |
| - | "0xCfcB156E4EB3f85A6FE1cec2DC83FBFEcF8Ee7FC" |
| + | "0x4996Ea58A0E3cAB8A324366E9684d1E2e679ce67" |
| values.pendingSanctions.69._timestamp: | |
| - | 1743368220 |
| + | 1743368117 |
| values.pendingSanctions.68._to: | |
| - | "0x4996Ea58A0E3cAB8A324366E9684d1E2e679ce67" |
| + | "0x9bfAd309FA457804B60FBec15Ec6D174111587f5" |
| values.pendingSanctions.68._timestamp: | |
| - | 1743368117 |
| + | 1743368207 |
| values.pendingSanctions.67._to: | |
| - | "0x9bfAd309FA457804B60FBec15Ec6D174111587f5" |
| + | "0x1B2888e792e82fe352FC9D1E73cdc91C6217F55c" |
| values.pendingSanctions.67._timestamp: | |
| - | 1743368207 |
| + | 1717533287 |
| values.pendingSanctions.66._to: | |
| - | "0x1B2888e792e82fe352FC9D1E73cdc91C6217F55c" |
| + | "0x615E981442C93325449cB379d991237a01c06b15" |
| values.pendingSanctions.66._timestamp: | |
| - | 1717533287 |
| + | 1719715389 |
| values.pendingSanctions.65._to: | |
| - | "0x615E981442C93325449cB379d991237a01c06b15" |
| + | "0xB3902654321D214d2B7Ca531832d0EF19780fDef" |
| values.pendingSanctions.65._timestamp: | |
| - | 1719715389 |
| + | 1719718623 |
| values.pendingSanctions.64._to: | |
| - | "0xB3902654321D214d2B7Ca531832d0EF19780fDef" |
| + | "0x2bf871ca38EbF4D6Ce0124d8551F236BA33F6e8A" |
| values.pendingSanctions.64._timestamp: | |
| - | 1719718623 |
| + | 1742239091 |
| values.pendingSanctions.63._to: | |
| - | "0x2bf871ca38EbF4D6Ce0124d8551F236BA33F6e8A" |
| + | "0x3365dB4c3490AC6A43986Cfe2c26FE61B22aA917" |
| values.pendingSanctions.63._timestamp: | |
| - | 1742239091 |
| + | 1707494421 |
| values.pendingSanctions.62._to: | |
| - | "0x3365dB4c3490AC6A43986Cfe2c26FE61B22aA917" |
| + | "0x6baa2c84A37999D264DA7bEe9639cDd3171c1397" |
| values.pendingSanctions.62._timestamp: | |
| - | 1707494421 |
| + | 1719718683 |
| values.pendingSanctions.61._to: | |
| - | "0x6baa2c84A37999D264DA7bEe9639cDd3171c1397" |
| + | "0x258DcCC0802232B7C9BC9ee71fde382Ed88d7Ce0" |
| values.pendingSanctions.61._timestamp: | |
| - | 1719718683 |
| + | 1743367401 |
| values.pendingSanctions.60._to: | |
| - | "0x258DcCC0802232B7C9BC9ee71fde382Ed88d7Ce0" |
| + | "0xfD73361D700410FC1513e91acf5E138d00a3dBe3" |
| values.pendingSanctions.60._timestamp: | |
| - | 1743367401 |
| + | 1743368523 |
| values.pendingSanctions.59._to: | |
| - | "0xfD73361D700410FC1513e91acf5E138d00a3dBe3" |
| + | "0xbafC930Eff179386813D17AF4f70A7d367f37E55" |
| values.pendingSanctions.59._timestamp: | |
| - | 1743368523 |
| + | 1743394986 |
| values.pendingSanctions.58._to: | |
| - | "0xbafC930Eff179386813D17AF4f70A7d367f37E55" |
| + | "0x0E084652CDc1a68f42218522b9A8a68FC4e6619f" |
| values.pendingSanctions.58._timestamp: | |
| - | 1743394986 |
| + | 1743367391 |
| values.pendingSanctions.57._to: | |
| - | "0x0E084652CDc1a68f42218522b9A8a68FC4e6619f" |
| + | "0x73163b73F526F436DD3234a439c4b691f5Db6F0c" |
| values.pendingSanctions.57._timestamp: | |
| - | 1743367391 |
| + | 1743394746 |
| values.pendingSanctions.56._to: | |
| - | "0x73163b73F526F436DD3234a439c4b691f5Db6F0c" |
| + | "0x92D620d0279359727A0128cC19b84EEF89621Fb4" |
| values.pendingSanctions.56._timestamp: | |
| - | 1743394746 |
| + | 1708164033 |
| values.pendingSanctions.55._to: | |
| - | "0x92D620d0279359727A0128cC19b84EEF89621Fb4" |
| + | "0x504CC21F6343F966E672ce27054f9b7e546cd918" |
| values.pendingSanctions.55._timestamp: | |
| - | 1708164033 |
| + | 1719715623 |
| values.pendingSanctions.54._to: | |
| - | "0x504CC21F6343F966E672ce27054f9b7e546cd918" |
| + | "0x3C9959C3EfEC9674926D86D8CAA814A486bA047B" |
| values.pendingSanctions.54._timestamp: | |
| - | 1719715623 |
| + | 1712740568 |
| values.pendingSanctions.53._to: | |
| - | "0x3C9959C3EfEC9674926D86D8CAA814A486bA047B" |
| + | "0x07bAA7EFD71836c440115add44f433B660cf61b8" |
| values.pendingSanctions.53._timestamp: | |
| - | 1712740568 |
| + | 1743367391 |
| values.pendingSanctions.52._to: | |
| - | "0x07bAA7EFD71836c440115add44f433B660cf61b8" |
| + | "0x158B49eCD928000B49036a4B3dD1E45ad7FEcEBE" |
| values.pendingSanctions.52._timestamp: | |
| - | 1743367391 |
| + | 1743367401 |
| values.pendingSanctions.51._to: | |
| - | "0x158B49eCD928000B49036a4B3dD1E45ad7FEcEBE" |
| + | "0xdD330d70F14AEa4Ce7b9E777fDCC117321c74124" |
| values.pendingSanctions.51._timestamp: | |
| - | 1743367401 |
| + | 1722940629 |
| values.pendingSanctions.50._to: | |
| - | "0xdD330d70F14AEa4Ce7b9E777fDCC117321c74124" |
| + | "0x49aEa6275e1D94Df2AC90c3ee4e4afd47e468d71" |
| values.pendingSanctions.50._timestamp: | |
| - | 1722940629 |
| + | 1712710928 |
| values.pendingSanctions.49._to: | |
| - | "0x49aEa6275e1D94Df2AC90c3ee4e4afd47e468d71" |
| + | "0x93402720154e26A044E8389D2733F281fF830c5c" |
| values.pendingSanctions.49._timestamp: | |
| - | 1712710928 |
| + | 1717937047 |
| values.pendingSanctions.48._to: | |
| - | "0x93402720154e26A044E8389D2733F281fF830c5c" |
| + | "0x32C4a3feAcff6592ed5a3878cFb839dD282f5807" |
| values.pendingSanctions.48._timestamp: | |
| - | 1717937047 |
| + | 1743394623 |
| values.pendingSanctions.47._to: | |
| - | "0x32C4a3feAcff6592ed5a3878cFb839dD282f5807" |
| + | "0x273DDd44f634c71112D2244B59999eD9A9Dd0562" |
| values.pendingSanctions.47._timestamp: | |
| - | 1743394623 |
| + | 1743367401 |
| values.pendingSanctions.46._to: | |
| - | "0x273DDd44f634c71112D2244B59999eD9A9Dd0562" |
| + | "0xaE815562105d42a06D06ff31139A63eE3F72128a" |
| values.pendingSanctions.46._timestamp: | |
| - | 1743367401 |
| + | 1743368466 |
| values.pendingSanctions.45._to: | |
| - | "0xaE815562105d42a06D06ff31139A63eE3F72128a" |
| + | "0x7498cF5863fd745eE79d7F07516725b87fE9C8FB" |
| values.pendingSanctions.45._timestamp: | |
| - | 1743368466 |
| + | 1706148032 |
| values.pendingSanctions.44._to: | |
| - | "0x7498cF5863fd745eE79d7F07516725b87fE9C8FB" |
| + | "0x1e9478A59d7182ddEd839bCc1aC7249D9c779003" |
| values.pendingSanctions.44._timestamp: | |
| - | 1706148032 |
| + | 1743367401 |
| values.pendingSanctions.43._to: | |
| - | "0x1e9478A59d7182ddEd839bCc1aC7249D9c779003" |
| + | "0x23c48DE9c94873Ca477871987c5a6C691517cc7C" |
| values.pendingSanctions.42._to: | |
| - | "0x23c48DE9c94873Ca477871987c5a6C691517cc7C" |
| + | "0xc884086a4e38a1072a0B4ED81054E9eEc92637ae" |
| values.pendingSanctions.42._timestamp: | |
| - | 1743367401 |
| + | 1743368466 |
| values.pendingSanctions.41._to: | |
| - | "0xc884086a4e38a1072a0B4ED81054E9eEc92637ae" |
| + | "0xe7e376c075D142f2b2A8de8708D723aC4a0d02aC" |
| values.pendingSanctions.41._timestamp: | |
| - | 1743368466 |
| + | 1743368491 |
| values.pendingSanctions.40._to: | |
| - | "0xe7e376c075D142f2b2A8de8708D723aC4a0d02aC" |
| + | "0x7B33a8711b11e9db091451D01730E2640F331bB3" |
| values.pendingSanctions.40._timestamp: | |
| - | 1743368491 |
| + | 1749084849 |
| } |
The system has a centralized sequencer
While forcing transaction is open to anyone the system employs a privileged sequencer that has priority for submitting transaction batches and ordering transactions.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly. After a delay of 1d in which a Sequencer has failed to include a transaction that was directly posted to the smart contract, it can be forcefully included by anyone on the host chain, which finalizes its ordering.
Delayed forced transactions
To force transactions from the host chain, users must first enqueue “delayed” messages in the “delayed” inbox of the Bridge contract. Only authorized Inboxes are allowed to enqueue delayed messages, and the so-called Inbox contract is the one used as the entry point by calling the sendMessage or sendMessageFromOrigin functions. If the centralized sequencer doesn’t process the request within some time bound, users can call the forceInclusion function on the SequencerInbox contract to include the message in the canonical chain. The time bound is hardcoded to be 1d.
Autonomous exit
Users can (eventually) exit the system by pushing the transaction on L1 and providing the corresponding state root. The only way to prevent such withdrawal is via an upgrade.
Enforced smart wallets and KYC
The Kinto L2 node is a fork of Arbitrum’s geth implementation with notable changes to the state transition function. A valid state transition in Kinto disallows all transactions by EOAs and new contract creation, unless specifically whitelisted. The current whitelist is sourced directly from the KintoAppRegistry smart contract on Kinto L2, and can be modified by the L2 governance. This setup effectively enforces smart wallet use because the auxiliary contracts of the standard KintoWallet smart wallet (like the EntryPoint and the KintoWalletFactory) are whitelisted. The KYC validation is part of the KintoWallet signature verification. Since all users must use the same implementation of this smart wallet, all user transactions on Kinto check for an up-to-date KYC flag, and are dropped in case the check fails.
Users can be censored if a KYC provider changes the users' KYC status and the Security Council confirms it.
Funds can be lost if the user interacts with a compromised whitelisted contract.

Ethereum
Roles:
Can submit transaction batches or commitments to the SequencerInbox contract on the host chain.
Can propose new state roots (called nodes) and challenge state roots on the host chain.
Actors:
A Multisig with 2/3 threshold.
- Can upgrade with no delay
- Bridger
A Multisig with 1/5 threshold. Member of Kinto Security Council.
Member of Kinto Security Council.
- A Validator - acting directly
- A Validator - acting directly
Member of Kinto Security Council, Kinto Multisig.
- A Validator - acting directly
- A Sequencer - acting directly
A Multisig with 6/8 threshold.
- Can upgrade with no delay
- RollupProxy UpgradeExecutor
- RollupEventInbox UpgradeExecutor → ProxyAdmin
- UpgradeExecutor UpgradeExecutor → ProxyAdmin
- ChallengeManager UpgradeExecutor → ProxyAdmin
- Outbox UpgradeExecutor → ProxyAdmin
- ERC20Gateway UpgradeExecutor → ProxyAdmin
- Bridge UpgradeExecutor → ProxyAdmin
- Inbox UpgradeExecutor → ProxyAdmin
- GatewayRouter UpgradeExecutor → ProxyAdmin
- SequencerInbox UpgradeExecutor → ProxyAdmin
- Can interact with RollupProxy
- Pause and unpause and set important roles and parameters in the system contracts: Can delegate Sequencer management to a BatchPosterManager address, manage data availability, DACs and the fastConfirmer role, set the Sequencer-only window, introduce an allowList to the bridge and whitelist Inboxes/Outboxes UpgradeExecutor
Kinto
Actors:
A Multisig with 2/4 threshold.
- Can upgrade with no delay
- Faucet
- SponsorPaymaster
- Can interact with NioGuardians
- mint Nio Guardian NFTs to any address, inheriting the permissions of the NFT
- Can interact with AccessManager
- change the configuration of all AccessManager permissions (minimum delay shown, the total delay can be longer for some operations) with 12d delay - acting directly with 12d delay
- approve smart wallet recoveries for any KintoWallet
- Can interact with KintoID
- manage the KYC status of any user (sanction status and KYC metadata) and mint/burn KintoID NFTs
- Can interact with AccessManager
- change the configuration of all AccessManager permissions (minimum delay shown, the total delay can be longer for some operations) with 7d delay - acting directly with 7d delay
- manage the whitelisted addresses in the KintoAppRegistry which affects censorship on the entire rollup with 11d delay - acting directly with 11d delay
- upgrade the implementation of the core contracts KintoID, KintoAppRegistry and KintoWalletFactory with 11d delay - acting directly with 11d delay
- confirm sanctions, making them permanent without providing an exit window

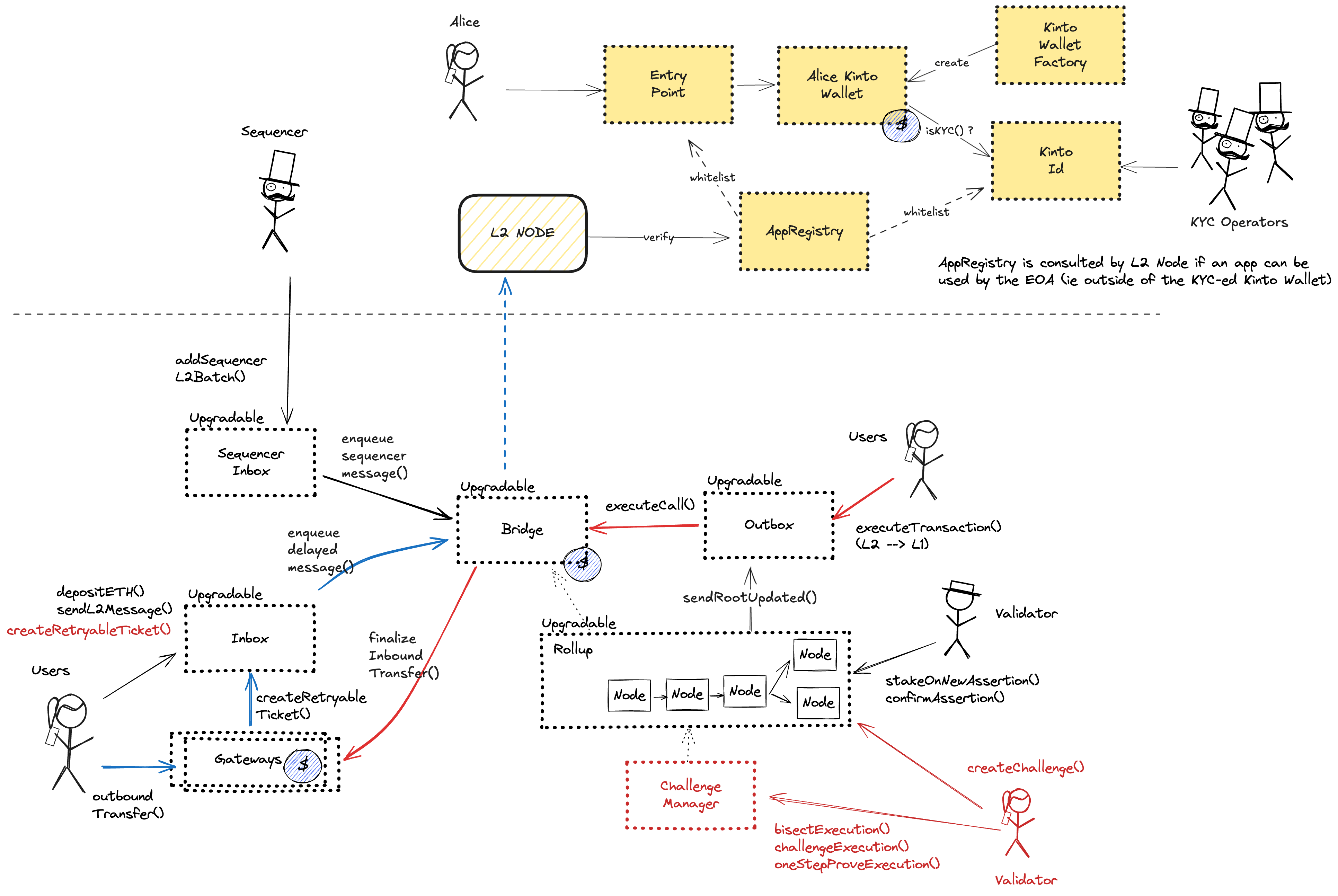
Ethereum
Central contract for the project’s configuration like its execution logic hash (wasmModuleRoot) and addresses of the other system contracts. Entry point for Proposers creating new Rollup Nodes (state commitments) and Challengers submitting fraud proofs (In the Orbit stack, these two roles are both held by the Validators).
- Roles:
- admin: UpgradeExecutor; ultimately Kinto Security Council
- owner: UpgradeExecutor; ultimately Kinto Security Council
- validators: Ankr, Caldera2, Certora 1, Hypernative2, KintoFoundation, KintsugiFoundation, MamoriLabs3, Turnkey Multisig, Venn2; ultimately EOA 1, EOA 2, EOA 3, EOA 4, EOA 5
Contract that allows challenging state roots. Can be called through the RollupProxy by Validators or the UpgradeExecutor.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
A sequencer (registered in this contract) can submit transaction batches or commitments here.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
- batchPosters: EOA 6
Central contract defining the access control permissions for upgrading the system contract implementations.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
- executors: Kinto Security Council
Facilitates L2 to L1 contract calls: Messages initiated from L2 (for example withdrawal messages) eventually resolve in execution on L1.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
Escrows deposited ERC-20 assets for the canonical Bridge. Upon depositing, a generic token representation will be minted at the destination. Withdrawals are initiated by the Outbox contract.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
Facilitates sending L1 to L2 messages like depositing ETH, but does not escrow funds.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
This routing contract maps tokens to the correct escrow (gateway) to be then bridged with canonical messaging.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
This contract implements view only utilities for validators.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Helper contract sending configuration data over the bridge during the systems initialization.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
- Roles:
- owner: UpgradeExecutor
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
Escrow contract for the project’s gas token (can be different from ETH). Keeps a list of allowed Inboxes and Outboxes for canonical bridge messaging.
- Roles:
- admin: ProxyAdmin; ultimately Kinto Security Council
Kinto
Central system contract defining addresses that are allowed to be called by EOAs. The modified Kinto node reads this configuration and drops all other transactions from EOAs (enforced by a modified state transition function). As a result, users can only transact using a canonical smart wallet.
- Roles:
- admin: AccessManager
- owner: AccessManager
Deploys new KintoWallet smartwallets for users upon passing KYC checks. Also manages the beacon implementation for all KintoWallets and their recovery logic. KintoWallets can be funded with ETH via this contract.
- Roles:
- admin: AccessManager
- owner: AccessManager
Manages Kinto’s KYC system: The KYC_PROVIDER roles responsible for managing the KYC status and KYC metadata of user wallets. Each KintoWallet checks the KYC status of its user in this contract as part of the signature check.
- Roles:
- dEFAULT_ADMINs: AccessManager
- gOVERNANCErs: AccessManager
- kYC_PROVIDERs: AccessManager, EOA 10, EOA 7, EOA 8, EOA 9, Kinto Multisig 2
- uPGRADERs: AccessManager
OpenZeppelin AccessManager contract: Serves as a proxy contract defining the roles, permissions and delays to call functions in target contracts.
- Roles:
- kintoMultisig2Permission: Kinto Multisig 2
- securityCouncilPermission: KintoSecurityCouncil_L2Alias
Central contract for bridging via the external socket bridge.
Used as entrypoint to transact using smartwallets and UserOps.
Beacon proxy for the KintoWallet smartwallet implementation that is used for all users.
- Roles:
- owner: KintoWalletFactory
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).