Search
Search for projects by name or address
 ZKsync Era
ZKsync Era
Badges
About
ZKsync Era is a general-purpose ZK Rollup with full EVM compatibility.
Interop protocols used
Tokens transferred


Badges
About
ZKsync Era is a general-purpose ZK Rollup with full EVM compatibility.
2025 May 30 — 2026 May 30
The section shows the operating costs that L2s pay to Ethereum.
2025 May 30 — 2026 May 30
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
Last 30 day anomalies
All liveness anomalies detected for this project in the last 30 days, helping you review recent downtime and availability issues.
No State updates were performed for 3h 27m 24s (from 2026 May 25, 04:40 UTC until 2026 May 25, 08:08 UTC). These typically occur every 30min 14s on average.
No State updates were performed for 3h 31m 12s (from 2026 May 14, 02:19 UTC until 2026 May 14, 05:50 UTC). These typically occur every 30min 14s on average.
V29 Interop Messaging Upgrade
2025 Oct 6th
A protocol upgrade introducing native interop messaging between chains connected to ZKsync Gateway.
Proof system intervention
2025 Jul 30th
The proof system is manually paused due to a vulnerability, causing a partial liveness failure.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
Users can submit transactions to an L1 queue, but can’t force them. The sequencers cannot selectively skip transactions but can stop processing the queue entirely. In other words, if the sequencers censor or are down, they are so for everyone.
STARKs and SNARKs are zero knowledge proofs that ensure state correctness. STARKs proofs are wrapped in SNARKs proofs for efficiency. SNARKs require a trusted setup.
All of the data (SD = state diffs) needed for proof construction is published onchain.
Non-emergency upgrades go through a 4d 3h delay, but the central operator can still censor withdrawal transactions by implementing a TransactionFilterer with no delay.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Only the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen. There is a decentralized Governance system that can attempt changing Proposers with an upgrade.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap blobs or calldata. This ensures that it will be available for enough time.
The node software is open-source, and its source code can be found here. The main node software does not rely on Layer 1 (L1) to reconstruct the state, but you can use this tool for that purpose. Currently, there is no straightforward method to inject the state into the main node, but ZKsync is actively working on a solution for this.
There have been neither genesis states nor regenesis.
Details on data format can be found here.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
ZKsync Era proof system Boojum can be found here and contains essential tools like the Prover, the Verifier, and other backend components. The specs of the system can be found here.
Funds can be lost if the proof system is implemented incorrectly.
SNARK verification keys can be generated and checked against the Ethereum verifier contract using this tool. The system requires a trusted setup.
Trusted Setups
Onchain verifier
Onchain verifier
Onchain verifier | ||
Onchain verifier |
Program Hashes
Name | Hash | Repository | Verification | Used in | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
0x0100...51e6 | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
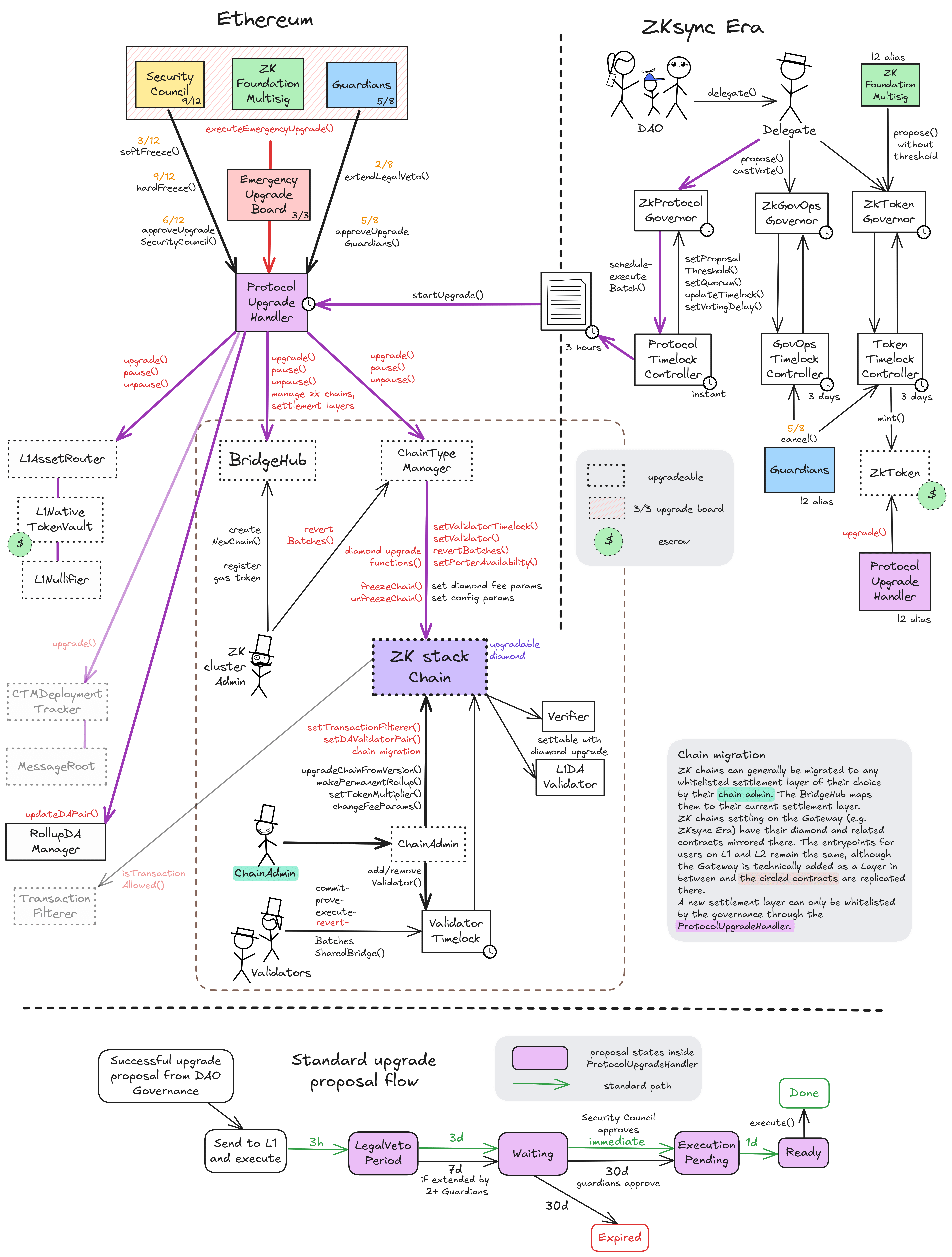
There are two main paths for contract upgrades in the shared ZK stack ecosystem - standard and emergency - both converging on the shared upgrade management contract ProtocolUpgradeHandler. The standard path involves a governance proposal and voting through the DAO, multiple timelock delays and finally approval by the Guardians or 4 SecurityCouncil participants. The emergency path allows for contract upgrades without any delay by the EmergencyUpgradeBoard, which acts as a 3/3 Multisig between SecurityCouncil, Guardians and the FoundationMultisig.
Standard path
On ZKsync Era
Delegates can start new proposals by reaching a threshold of 21M ZK tokens on the ZKsync Era Rollup’s ZkProtocolGovernor contract. This launches a 3d ‘voting delay’ after which the 7d voting period starts. During these first two periods, the proposal can be canceled by the proposer or if it falls below the proposing threshold. A proposal is only successful if it reaches both quorum (630M ZK tokens) and simple majority. When it reaches quorum, a remaining voting period of 3d is guaranteed by a potential late quorum vote extension. In the successful case, it can be queued in the 0s timelock which forwards it via the Gateway to Ethereum as an L2->L1 log.
On Ethereum
After the execution of the proposal-containing batch (3h delay), the proposal is now picked up by the ProtocolUpgradeHandler and enters the 3d ‘legal veto period’. This serves as a window in which a veto could be coordinated offchain, to be then enforced by non-approval of Guardians and SecurityCouncil. A threshold of 2 Guardians can extend the veto period to 7d. After this a proposal enters a waiting state of 1mo, from which it can be immediately approved (cancelling the delay) by 4 participants of the SecurityCouncil. For the unlikely case that the Security Council does not approve here, the Guardians can instead approve the proposal, or nobody. In the two latter cases, the waiting period is enforced in full. A proposal cannot be actively cancelled in the ProtocolUpgradeHandler, but will expire if not approved within the waiting period. An approved proposal now enters the pendingExecution state for a final delay of 1d and can then be executed.
Other governance tracks
There are two other tracks of Governance also starting with DAO Delegate proposals the ZKsync Era rollup: 1) Token Program Proposals that add new minters, allocations or upgrade the ZK token and 2) Governance Advisory Proposals that e.g. change the ZK Credo or other offchain Governance Procedures without onchain targets. The protocol for these two other tracks is similar to the first part of the standard path described above (albeit having different quorum and timelock values), and not passing over to the Ethereum L1. Further customizations are that the ZkFoundationMultisig can propose to the ZkTokenGovernor without a threshold and that the Guardians’ L2 alias can cancel proposals in the ZkTokenGovernor and the ZkGovOpsGovernor.
Emergency path
SecurityCouncil (6/8), Guardians (5/8) and ZkFoundationMultisig (3/5) form a de-facto 3/3 Multisig by pushing an immediate upgrade proposal through the EmergencyUpgradeBoard, which circumvents all delays and executes immediately via the ProtocolUpgradeHandler.
Upgrade Delays
The cumulative duration of the upgrade paths from the moment of a voted ‘successful’ proposal is 4d 3h or 8d 3h (depending on Guardians extending the LegalVetoPeriod) for Standard, 0 for Emergency and 1mo 4d for the path in which the SecurityCouncil is not approving the proposal.
Freezing
The SecurityCouncil can freeze (pause withdrawals and settlement) all chains connected to the current ChainTypeManager. Either for a softFreeze of 12h or a hardFreeze of 7d. After a softFreeze and / or a hardFreeze, a proposal from the EmergencyUpgradeBoard has to be passed before subsequent freezes are possible. Only the SecurityCouncil can unfreeze an active freeze.
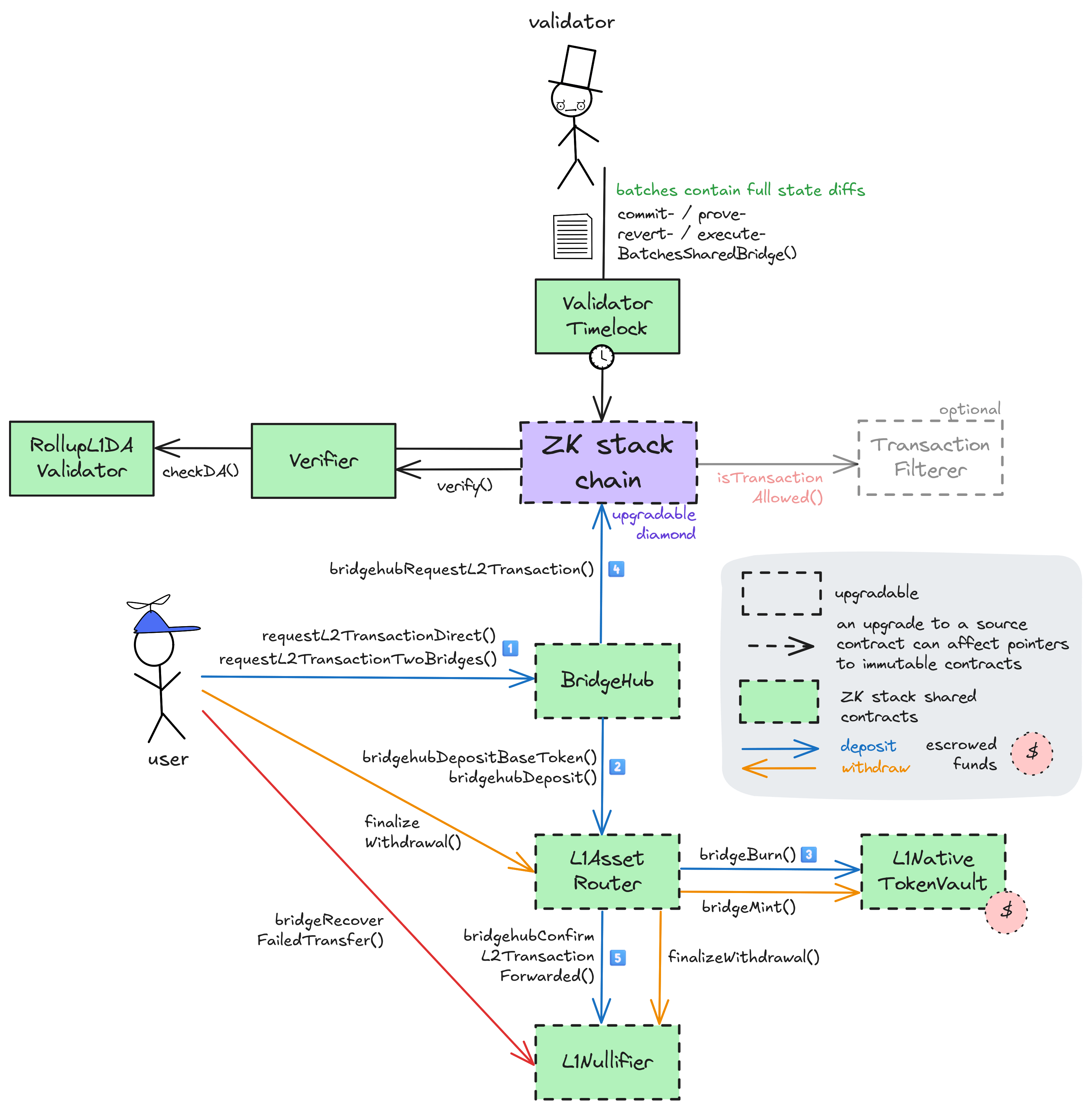
ZK cluster Admin and Chain Admin
Apart from the paths that can upgrade all shared implementations, the ZK stack governance system defines other roles that can modify the system: A single ZK cluster Admin role who governs parameters in the shared contracts and a Chain Admin role (defined in each chain-specific diamond contract) for managing parameters of each individual ZK chain that builds on the stack. These chain-specific actions include critical operations like setting a transaction filterer that can censor L1 -> L2 messages, changing the DA mode, migrating the chain to a different settlement layer and standard operations like setting fee parameters and adding / removing Validators in the ValidatorTimelock. For rollups, data availability on Ethereum is validated by a RollupL1DAValidator contract (or a RelayedSLDAValidator on the Gateway). Each rollup can become a permanent rollup (through their Chain Admin) which disallows DA changes to non-whitelisted sources or settlement layers in the future. The source of truth for rollup-compliant DA validator contracts is the RollupDAManager contract, which is administered via the ProtocolUpgradeHandler. ZKsync Era’s Chain Admin differs from the others as it also has the above ZK cluster Admin role in the shared ZK stack contracts.
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2026 May 04, 08:28 UTCHigh severity16changesEra multisig validator now has 3 (out of 8) threshold, instead of 0. This effectively enables the multisig operation. This contract allows registered validators stop block execution. This multisig is also made the only entity that can precommit, commit, revert, prove and execute blocks, earlier there were also two EOAs with these permissions.
Era multisig validator now has 3 (out of 8) threshold, instead of 0. This effectively enables the multisig operation. This contract allows registered validators stop block execution.
This multisig is also made the only entity that can precommit, commit, revert, prove and execute blocks, earlier there were also two EOAs with these permissions.
| contract ValidatorTimelock (eth:0x2e5110cF18678Ec99818bFAa849B8C881744b776) { | |
| +++ description: Intermediary contract between the *Validators* and the central diamond contract that delays block execution (ie withdrawals and other L2 --> L1 messages) by 3h. | |
| values.validatorVTL.PRECOMMITTER_ROLE.members.0: | |
| - | "eth:0x882A6C2ecbAbfFc40686D599a9375ad3b35427Fd" |
| values.validatorVTL.PRECOMMITTER_ROLE.members.1: | |
| - | "eth:0xc75cDcBEef3aE3365ABF0217815748586F9047F1" |
| values.validatorVTL.COMMITTER_ROLE.members.0: | |
| - | "eth:0x882A6C2ecbAbfFc40686D599a9375ad3b35427Fd" |
| values.validatorVTL.COMMITTER_ROLE.members.1: | |
| - | "eth:0xc75cDcBEef3aE3365ABF0217815748586F9047F1" |
| values.validatorVTL.REVERTER_ROLE.members.0: | |
| - | "eth:0x882A6C2ecbAbfFc40686D599a9375ad3b35427Fd" |
| values.validatorVTL.REVERTER_ROLE.members.1: | |
| - | "eth:0xc75cDcBEef3aE3365ABF0217815748586F9047F1" |
| values.validatorVTL.PROVER_ROLE.members.0: | |
| - | "eth:0x882A6C2ecbAbfFc40686D599a9375ad3b35427Fd" |
| values.validatorVTL.PROVER_ROLE.members.1: | |
| - | "eth:0xc75cDcBEef3aE3365ABF0217815748586F9047F1" |
| values.validatorVTL.EXECUTOR_ROLE.members.0: | |
| - | "eth:0x882A6C2ecbAbfFc40686D599a9375ad3b35427Fd" |
| values.validatorVTL.EXECUTOR_ROLE.members.1: | |
| - | "eth:0xc75cDcBEef3aE3365ABF0217815748586F9047F1" |
| } |
| EOA (eth:0x882A6C2ecbAbfFc40686D599a9375ad3b35427Fd) { | |
| +++ description: None | |
| receivedPermissions.1: | |
| - | {"permission":"validateZkStack","from":"eth:0x2e5110cF18678Ec99818bFAa849B8C881744b776","role":".validatorVTL"} |
| } |
| EOA (eth:0xc75cDcBEef3aE3365ABF0217815748586F9047F1) { | |
| +++ description: None | |
| receivedPermissions.1: | |
| - | {"permission":"validateZkStack","from":"eth:0x2e5110cF18678Ec99818bFAa849B8C881744b776","role":".validatorVTL"} |
| } |
| contract EraMultisigValidator (eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d) { | |
| +++ description: A multisig wrapper around `ValidatorTimelock` that requires a threshold of approvals before batch execution can proceed, provides additional security through 2FA. | |
| values.$threshold: | |
| - | 0 |
| + | 3 |
| +++ severity: HIGH | |
| values.threshold: | |
| - | 0 |
| + | 3 |
| } |
2026 April 27, 13:21 UTC22changesUpgraded ExecutionMultisigValidator: https://disco.l2beat.com/diff/eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7/eth:0xc954B4D51031870624f3e779Ead14C57249C111D (although diff is not very readable). This is a intermediary contract that lets validators stop block execution. The main changes are: - It is made EIP1967 upgradeable - Multisig rotation now emits events, which allows tracking the members in disco - Added EIP-712 structured data hashing - General refactor
Upgraded ExecutionMultisigValidator: https://disco.l2beat.com/diff/eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7/eth:0xc954B4D51031870624f3e779Ead14C57249C111D (although diff is not very readable). This is a intermediary contract that lets validators stop block execution. The main changes are:
- It is made EIP1967 upgradeable
- Multisig rotation now emits events, which allows tracking the members in disco
- Added EIP-712 structured data hashing
- General refactor
| contract ValidatorTimelock (eth:0x2e5110cF18678Ec99818bFAa849B8C881744b776) { | |
| +++ description: Intermediary contract between the *Validators* and the central diamond contract that delays block execution (ie withdrawals and other L2 --> L1 messages) by 3h. | |
| values.validatorVTL.PRECOMMITTER_ROLE.members.0: | |
| - | "eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7" |
| values.validatorVTL.PRECOMMITTER_ROLE.members.2: | |
| + | "eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d" |
| values.validatorVTL.COMMITTER_ROLE.members.0: | |
| - | "eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7" |
| values.validatorVTL.COMMITTER_ROLE.members.2: | |
| + | "eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d" |
| values.validatorVTL.REVERTER_ROLE.members.0: | |
| - | "eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7" |
| values.validatorVTL.REVERTER_ROLE.members.2: | |
| + | "eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d" |
| values.validatorVTL.PROVER_ROLE.members.0: | |
| - | "eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7" |
| values.validatorVTL.PROVER_ROLE.members.2: | |
| + | "eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d" |
| values.validatorVTL.EXECUTOR_ROLE.members.0: | |
| - | "eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7" |
| values.validatorVTL.EXECUTOR_ROLE.members.2: | |
| + | "eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d" |
| } |
| - | Status: DELETED |
| reference (eth:0x3068415e0F857A5eEd03302A1F7E44f67468d2Bc) | |
| +++ description: None |
| - | Status: DELETED |
| reference (eth:0x3F0009D00cc78979d00Eb635490F23E8d6aCc481) | |
| +++ description: None |
| - | Status: DELETED |
| reference (eth:0x4A333c167Ce76C46149c6B0197977ae02aaeC929) | |
| +++ description: None |
| - | Status: DELETED |
| reference (eth:0x5C7E59Dba6557C7dAB3B69ccd3E309d1965Cf1B1) | |
| +++ description: None |
| - | Status: DELETED |
| reference (eth:0x7408A268e5E6e8F08917c5b71015F4B9044970C7) | |
| +++ description: None |
| - | Status: DELETED |
| reference (eth:0xAf0B2B58289857e9A6Cf91Fd30410dDcad9D9B28) | |
| +++ description: None |
| - | Status: DELETED |
| contract Safe (eth:0xd972d03C8A45eF3c7937a279d998E4AeCCc2b63D) | |
| +++ description: None |
| - | Status: DELETED |
| contract ExecutionMultisigValidator (eth:0xE222D6354b49eaF8a7099fC4E7F9C0B4FE72d1E7) | |
| +++ description: Intermediary contract between the *Validators* and the central diamond contract that delays block execution (ie withdrawals and other L2 --> L1 messages) by 3h. NOTE: This is a modified version of validatorTimelock, where a sufficient number of execution multisig members must approve a batch before execution. Multisig members are kept in a mapping and updates emit no events, so the only way to track them is to manually analyze all trxs from the owner. |
| - | Status: DELETED |
| reference (eth:0xFAdb20191Ab38362C50f52909817B74214CA79AE) | |
| +++ description: None |
| + | Status: CREATED |
| contract ProxyAdmin (eth:0x0D8d1be440f997bDB9CA44C0140fD12551f99BBB) | |
| +++ description: None |
| + | Status: CREATED |
| reference Matter Labs Multisig (eth:0x4e4943346848c4867F81dFb37c4cA9C5715A7828) | |
| +++ description: None |
| + | Status: CREATED |
| contract EraMultisigValidator (eth:0xdC26B08F0335b68721F64001C38b05D0BC9B539d) | |
| +++ description: Intermediary contract between the *Validators* and the central diamond contract that delays block execution (ie withdrawals and other L2 --> L1 messages) by 3h. NOTE: This is a modified version of validatorTimelock, where a sufficient number of execution multisig members must approve a batch before execution. Multisig members are kept in a mapping. |
2026 April 20, 10:40 UTCHigh severity13changeswstETH bridge resumed after being paused because of a potential vulnerability. Its implementation was upgraded adding one small check: https://disco.l2beat.com/diff/eth:0x9a810469F4a451Ebb7ef53672142053b4971587c/eth:0x43a66B32c9AdcA1A59b273E69b61Da5197c21cCd.
wstETH bridge resumed after being paused because of a potential vulnerability. Its implementation was upgraded adding one small check: https://disco.l2beat.com/diff/eth:0x9a810469F4a451Ebb7ef53672142053b4971587c/eth:0x43a66B32c9AdcA1A59b273E69b61Da5197c21cCd.
| contract L1ERC20Bridge_wstETH (eth:0x41527B2d03844dB6b0945f25702cB958b6d55989) { | |
| +++ description: Bridge for depositing wrapped stETH (Lido) to ZKsync Era. These deposits and withdrawals do not go through the shared Bridge. | |
| sourceHashes.1: | |
| - | "0x8d6377528b46831d215e352a53f276acbd18ec4bc66c04894dd72dad36288c4d" |
| + | "0x887b9d27b8b5ffb156d6a159bc56c0b8bb6e24d70f3568550066b1f247acf4fe" |
| values.$implementation: | |
| - | "eth:0x9a810469F4a451Ebb7ef53672142053b4971587c" |
| + | "eth:0x43a66B32c9AdcA1A59b273E69b61Da5197c21cCd" |
| values.$pastUpgrades.1: | |
| + | ["2026-04-17T16:42:11.000Z","0xf43f6fe63edc60ae6eb0bc919b3c682ac0c068df7eb1cb44aa514302539f19cb",["eth:0x43a66B32c9AdcA1A59b273E69b61Da5197c21cCd"]] |
| values.$upgradeCount: | |
| - | 1 |
| + | 2 |
| values.isDepositsEnabled: | |
| - | false |
| + | true |
| values.proxy__getImplementation: | |
| - | "eth:0x9a810469F4a451Ebb7ef53672142053b4971587c" |
| + | "eth:0x43a66B32c9AdcA1A59b273E69b61Da5197c21cCd" |
| implementationNames.eth:0x9a810469F4a451Ebb7ef53672142053b4971587c: | |
| - | "L1ERC20Bridge" |
| implementationNames.eth:0x43a66B32c9AdcA1A59b273E69b61Da5197c21cCd: | |
| + | "L1ERC20Bridge" |
| } |
2026 March 04, 14:38 UTC2changeswstETH bridge paused deposits due to a potential vulnerability: https://x.com/lidofinance/status/2028803376306336068?s=46&t=q4Q232TdEyWIiMZPfDpI4A.
wstETH bridge paused deposits due to a potential vulnerability: https://x.com/lidofinance/status/2028803376306336068?s=46&t=q4Q232TdEyWIiMZPfDpI4A.
| contract L1ERC20Bridge_wstETH (eth:0x41527B2d03844dB6b0945f25702cB958b6d55989) { | |
| +++ description: Bridge for depositing wrapped stETH (Lido) to ZKsync Era. These deposits and withdrawals do not go through the shared Bridge. | |
| values.isDepositsEnabled: | |
| - | true |
| + | false |
| } |
2026 February 09, 12:10 UTCHigh severity15changesUpgraded verifiers to the next version.
Upgraded verifiers to the next version.
| contract Diamond (eth:0x32400084C286CF3E17e7B677ea9583e60a000324) { | |
| +++ description: The main contract defining the Layer 2. Operator actions like commiting blocks, providing ZK proofs and executing batches ultimately target this contract which then processes transactions. During batch execution it processes L1 --> L2 and L2 --> L1 transactions. isPermanentRollup was set to true in this contract which prevents changing the DA mode to Validium in the future. | |
| values.$pastUpgrades.25: | |
| + | ["2026-02-06T15:23:35.000Z","0x96d827f588ce0b3868ebdf99ca1099d1128a8112ddbb140416d9ffdcfd72e9af",["eth:0x37CefD5b44c131FEf27e9Bc542e5B77A177A7253","eth:0x1666124221622eb6154306Ea9BA87043e8be88B2","eth:0x1e34aB39a9682149165ddeCc0583d238A5448B45","eth:0x0597CaA8A823A699d7CD9E62B5E5d4153FF82691"]] |
| values.$upgradeCount: | |
| - | 25 |
| + | 26 |
| +++ description: Protocol version, increments with each protocol upgrade. | |
| +++ severity: HIGH | |
| values.getProtocolVersion: | |
| - | 124554051587 |
| + | 124554051588 |
| values.getSemverProtocolVersion.2: | |
| - | 3 |
| + | 4 |
| values.getVerifier: | |
| - | "eth:0x4f06ef57618b16959879fC86E65eda0bd629A12B" |
| + | "eth:0xCD279BD537c8e1A1acC46aC2205bebD8902F7A45" |
| } |
| - | Status: DELETED |
| contract DualVerifier (eth:0x4f06ef57618b16959879fC86E65eda0bd629A12B) | |
| +++ description: A router contract for verifiers. Routes verification requests to eth:0xE3743181a4b0A0C1260826105c6BBA4b6e18D79d or eth:0xB3f4396C2040e502d0556Cbb16C0B22fE777A026 depending on the supplied proof type. |
| - | Status: DELETED |
| contract L1VerifierPlonk (eth:0xB3f4396C2040e502d0556Cbb16C0B22fE777A026) | |
| +++ description: Verifies a zk-SNARK proof using an implementation of the PlonK proof system. |
| - | Status: DELETED |
| contract L1VerifierFflonk (eth:0xE3743181a4b0A0C1260826105c6BBA4b6e18D79d) | |
| +++ description: Verifies a zk-SNARK proof using an implementation of the fflonk proof system. |
| + | Status: CREATED |
| contract L1VerifierPlonk (eth:0x7f33D100f482093182111d69a4a457289e99f4ec) | |
| +++ description: Verifies a zk-SNARK proof using an implementation of the PlonK proof system. |
| + | Status: CREATED |
| contract L1VerifierFflonk (eth:0xa38a0Df579F9eCA29fbA560b9885B1113b1Df442) | |
| +++ description: Verifies a zk-SNARK proof using an implementation of the fflonk proof system. |
| + | Status: CREATED |
| contract DualVerifier (eth:0xCD279BD537c8e1A1acC46aC2205bebD8902F7A45) | |
| +++ description: A router contract for verifiers. Routes verification requests to eth:0xa38a0Df579F9eCA29fbA560b9885B1113b1Df442 or eth:0x7f33D100f482093182111d69a4a457289e99f4ec depending on the supplied proof type. |
The system has a centralized operator
The operator is the only entity that can propose blocks. A live and trustworthy operator is vital to the health of the system.
Batch execution is initiated by permissioned executor EOAs, but each batch also requires approval from the sufficient number of EraMultisigValidator members before it can be executed on L1.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can be censored if the validator multisig does not approve batch execution.
Users can force any transaction via L1
Users can be censored if the operator refuses to include their transactions.
Users can be censored if the operator implements a TransactionFilterer, which is possible without delay.
Forced messaging
If the user experiences censorship from the operator with regular L2->L1 messaging they can submit their messages directly on L1. The system is then obliged to service this request or halt all messages from L1, including all forced withdrawals and deposits. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular message.

Ethereum
Roles:
Permissioned to call the functions to commit, prove, execute and revert L2 batches through the ValidatorTimelock in the main Diamond contract.
Actors:
A custom contract allowing a 3/3 of SecurityCouncil, ZK Foundation Multisig and Guardians to executeEmergencyUpgrade() via the ProtocolUpgradeHandler.
- Can upgrade with no delay
- BridgeHub ProtocolUpgradeHandler → ProxyAdmin
- MessageRoot ProtocolUpgradeHandler → ProxyAdmin
- CTMDeploymentTracker ProtocolUpgradeHandler → ProxyAdmin
- L1AssetRouter ProtocolUpgradeHandler → ProxyAdmin
- L1NativeTokenVault ProtocolUpgradeHandler → ProxyAdmin
- ChainTypeManager ProtocolUpgradeHandler → ProxyAdmin
- L1Nullifier ProtocolUpgradeHandler → ProxyAdmin
- ChainAssetHandler ProtocolUpgradeHandler → ProxyAdmin
- ProtocolUpgradeHandler ProtocolUpgradeHandler → ProxyAdmin
- Can interact with BridgeHub
- set critical contract addresses for the shared cluster, register settlement layers, pause and unpause migrations and the bridge and manage zk chain registration ProtocolUpgradeHandler
- Can interact with L1NativeTokenVault
- pause / unpause the bridge ProtocolUpgradeHandler
- Can interact with ChainTypeManager
- manage the shared ValidatorTimelock contract address and the admin role, register and execute upgrades (and set their deadlines), freeze, revert batches and set permissioned validators and fee params for all connected chains ProtocolUpgradeHandler
- Can interact with L1Nullifier
- pause, unpause and set critical escrow address references ProtocolUpgradeHandler
- Can interact with ChainAssetHandler
- pause, resume chain migrations ProtocolUpgradeHandler
- Can interact with RollupDAManager
A Multisig with 5/8 threshold.
- Can upgrade with no delay
- ServerNotifier EraChainAdminProxy → ProxyAdmin
- Can interact with BridgeHub
- create new zk chains (based on the current version), register tokens (ZK cluster Admin role) EraChainAdminProxy
- Can interact with ChainTypeManager
- revert batches for any connected chain (ZK cluster Admin role) EraChainAdminProxy
Participants (8):
0x4A33…C9290x3F00…c4810x5C7E…f1B10x3068…d2Bc0x702c…78b70xFAdb…79AE0xAf0B…9B280x7408…70C7A Multisig with 6/8 threshold. Custom Multisig implementation that has a general threshold of 6 but also specific thresholds for upgrade approvals (4) or soft freezes (3).
- Can interact with ProtocolUpgradeHandler
- soft freeze, hard freeze, approve a protocol upgrade
- Can interact with EmergencyUpgradeBoard
- one of its 3/3 signers
A Multisig with 5/8 threshold. Custom Multisig implementation that has a general threshold of 5 and a specific threshold for extending the legal voting period of 2.
- Can interact with ProtocolUpgradeHandler
- extend the legal veto period, approve a protocol upgrade
- Can interact with EmergencyUpgradeBoard
- one of its 3/3 signers
Intermediary contract between the Validators and the central diamond contract that delays block execution (ie withdrawals and other L2 --> L1 messages) by 3h.
- Can interact with Diamond
- commit, prove, execute, revert batches directly in the main Diamond contract. This role is typically held by a proxying ValidatorTimelock
- Can upgrade with no delay
- EraMultisigValidator
A Multisig with 3/8 threshold.
A multisig wrapper around ValidatorTimelock that requires a threshold of approvals before batch execution can proceed, provides additional security through 2FA.
- A Validator - acting directly
A Multisig with 3/5 threshold.
- Can interact with EmergencyUpgradeBoard
- one of its 3/3 signers
- Can interact with ProtocolUpgradeHandler
- start (queue) upgrades
ZKsync Era
Actors:
Main Governance contract allowing for token voting (simple majority) with the ZK token through delegates. This contract is used for protocol upgrade proposals (ZIPs) that start on ZKsync Era, go through Ethereum Layer 1 and can - from there - target all L1 and L2 contracts. At least 21M ZK tokens are necessary to start a proposal and a 630M quorum of voted tokens must be met to succeed.
- Can interact with ProtocolTimelockController
- cancel queued transactions
- execute transactions that are ready
- manage all access control roles and change the minimum delay ProtocolTimelockController
- propose transactions
Governance contract allowing for token voting (simple majority) with the ZK token through delegates. This contract is used for Token Program Proposals (TPPs) usually targeting the ZK token on ZKsync Era. At least 21M ZK tokens are necessary to start a proposal (for delegates) and a 630M quorum of voted tokens must be met to succeed.
- Can interact with ZkToken
- grant the MINTER_ROLE to arbitrary addresses, thus controlling the minting of the ZK token with 3d delay ZkTokenTimelockController with 3d delay
- Can interact with ZkTokenTimelockController
- manage all access control roles and change the minimum delay with 6d delay ZkTokenTimelockController with 3d delay with 3d delay
- cancel queued transactions
- execute transactions that are ready
- propose transactions
Governance contract allowing for token voting (simple majority) with the ZK token through delegates. This contract is used for Governance Advisory Proposals (GAPs) that are not executable onchain. At least 21M ZK tokens are necessary to start a proposal and a 630M quorum of voted tokens must be met to succeed.
- Can interact with GovOpsTimelockController
- manage all access control roles and change the minimum delay with 6d delay GovOpsTimelockController with 3d delay with 3d delay
- cancel queued transactions
- execute transactions that are ready
- propose transactions
- Can interact with ZkTokenGovernor
- cancel proposals while they are pending (after having been proposed) or active (during the voting period)
- Can interact with ZkGovOpsGovernor
- cancel proposals while they are pending (after having been proposed) or active (during the voting period)
- Can interact with ZkTokenGovernor
- make direct proposals without owning ZK tokens. In propose-guarded mode, this address is the ONLY allowed proposer. Propose-guarded mode is currently set to false
- Can upgrade with no delay
- ZkToken ZkTokenProxyAdmin
- Can interact with ZkToken
- control all roles in the ZkToken access control, including the minter roles

Ethereum
The main contract defining the Layer 2. Operator actions like commiting blocks, providing ZK proofs and executing batches ultimately target this contract which then processes transactions. During batch execution it processes L1 --> L2 and L2 --> L1 transactions. isPermanentRollup was set to true in this contract which prevents changing the DA mode to Validium in the future.
- Roles:
- validators: ValidatorTimelock
The main registry (hub) for all the contracts in the ZK stack cluster and central entrypoint for bridge transactions. Stores important mappings like from chainId to diamond address, from chainId to parent CTM, from chainId to base token etc. A clone of Bridgehub is also deployed on each L2 chain, but this clone is only used on settlement layers.
- Roles:
- admin: EraChainAdminProxy, ProxyAdmin; ultimately EmergencyUpgradeBoard, Matter Labs Multisig
- owner: ProtocolUpgradeHandler; ultimately EmergencyUpgradeBoard
Aggregates remote bridge message roots from all ZK stack chains. To be used with the Gateway when deployed.
- Roles:
- admin: ProxyAdmin; ultimately EmergencyUpgradeBoard
Asset deployment tracker where the ‘asset’ is a ChainTypeManager. The registering of asset IDs for ChainTypeManagers is necessary to be able to migrate them to a given settlement layer, for example the Gateway.
- Roles:
- admin: ProxyAdmin; ultimately EmergencyUpgradeBoard
Contract that verifies the data availability of ethereum calldata and blobs. Can be used by ZK stack rollups as the L1 part of a DAValidator pair.
Defines L2 diamond contract versions, creation and upgrade data and the proof system for all ZK stack chains connected to it. ZK chains are children of this central contract and can only upgrade to versions that were previously registered here. The current protocol version is 0,29,4.
- Roles:
- admin: EraChainAdminProxy, ProxyAdmin; ultimately EmergencyUpgradeBoard, Matter Labs Multisig
- owner: ProtocolUpgradeHandler; ultimately EmergencyUpgradeBoard
Contract responsible for bookkeeping L1 bridging transactions. Used to finalize withdrawals and reclaim failed deposits. Does not escrow funds.
- Roles:
- admin: ProxyAdmin; ultimately EmergencyUpgradeBoard
- owner: ProtocolUpgradeHandler; ultimately EmergencyUpgradeBoard
The central upgrade contract and Governance proxy for all ZK stack contracts. Accepts successful DAO proposals from L2 and emergency proposals from the EmergencyUpgradeBoard. The three members of the EmergencyUpgradeBoard also have special roles and permissions in this contract.
Simple registry for allowed DA address pairs for the ‘rollup’ data availability mode (can be permanently enforced with isPermanentRollup=true). Rollup DA address pairs (especially the L1 part) usually point to contracts that validate if data was made available on Ethereum.
- Roles:
- owner: ProtocolUpgradeHandler; ultimately EmergencyUpgradeBoard
A governance proxy that lets Matter Labs Multisig act through it.
- Roles:
- owner: Matter Labs Multisig
Legacy bridge for depositing ERC20 tokens to ZKsync Era. Forwards deposits and withdrawals to the BridgeHub.
All supported tokens in this escrow are included in the value secured calculation.

Verifies a zk-SNARK proof using an implementation of the PlonK proof system.
Verifies a zk-SNARK proof using an implementation of the fflonk proof system.
A router contract for verifiers. Routes verification requests to L1VerifierFflonk or L1VerifierPlonk depending on the supplied proof type.
Canonical central asset escrow for all ZK stack chains.
- Roles:
- admin: ProxyAdmin; ultimately EmergencyUpgradeBoard
- owner: ProtocolUpgradeHandler; ultimately EmergencyUpgradeBoard
All supported tokens in this escrow are included in the value secured calculation.
Specialized contract for managing chain assets, i.e. chain migrations.
- Roles:
- admin: ProxyAdmin; ultimately EmergencyUpgradeBoard
- owner: ProtocolUpgradeHandler; ultimately EmergencyUpgradeBoard
A simple contract that can be called by the ChainAdmin to emit notifications about chain migrations.
- Roles:
- admin: ProxyAdmin; ultimately Matter Labs Multisig
ZKsync Era
Timelock contract allowing the queueing of transactions with a minimum delay of 0s.
- Roles:
- canceller: ZkProtocolGovernor
- executor: ZkProtocolGovernor
- proposer: ZkProtocolGovernor
- timelockAdmin: ProtocolTimelockController; ultimately ZkProtocolGovernor
The ZK token contract on ZKsync Era. Mintable through access control roles. Used for voting in the ZK stack governance system.
- Roles:
- admin: ZkTokenProxyAdmin; ultimately ProtocolUpgradeHandler_l2Alias
- defaultAdmin: ProtocolUpgradeHandler_l2Alias
- minterAdmin: ZkTokenTimelockController; ultimately ZkTokenGovernor
Timelock contract allowing the queueing of transactions with a minimum delay of 3d.
- Roles:
- canceller: ZkGovOpsGovernor
- executor: ZkGovOpsGovernor
- proposer: ZkGovOpsGovernor
- timelockAdmin: GovOpsTimelockController; ultimately ZkGovOpsGovernor
Timelock contract allowing the queueing of transactions with a minimum delay of 3d.
- Roles:
- canceller: ZkTokenGovernor
- executor: ZkTokenGovernor
- proposer: ZkTokenGovernor
- timelockAdmin: ZkTokenTimelockController; ultimately ZkTokenGovernor
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 4d 3h - 8d 3h delay on code upgrades unless upgrade is initiated by the EmergencyUpgradeBoard in which case there is no delay.
Program Hashes
Name | Hash | Repository | Verification | Used in | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
0x0100...51e6 | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||