Search
Search for projects by name or address
 dYdX v3
dYdX v3
dYdX v3 shut down on October 28th and is currently processing withdrawals in escape-hatch mode. Read more or use the escape-hatch.
Badges
About
dYdX v3 aims to build a powerful and professional exchange for trading crypto assets where users can truly own their trades and, eventually, the exchange itself.
Badges
About
dYdX v3 aims to build a powerful and professional exchange for trading crypto assets where users can truly own their trades and, eventually, the exchange itself.
2021 Feb 20 — 2026 May 30
The section shows the operating costs that L2s pay to Ethereum.
2023 May 01 — 2026 May 30
dYdX v4 announcement
2022 Jun 22nd
dYdX V4 will be developed as a standalone blockchain based on the Cosmos SDK.
dYdX Foundation
2021 Aug 3rd
Independent foundation was created to participate in the Protocol governance.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
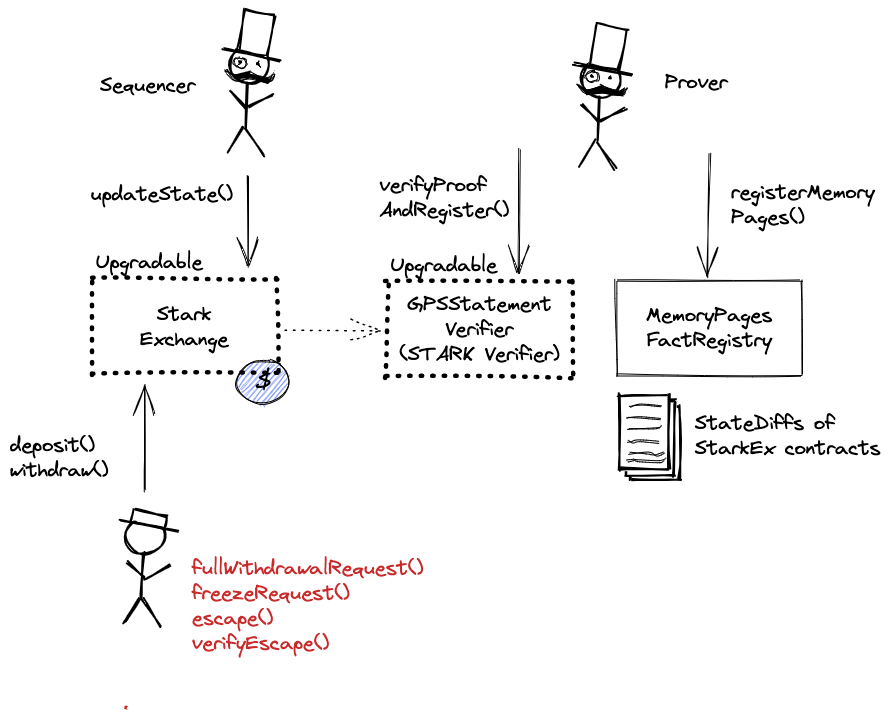
STARKs are zero knowledge proofs that ensure state correctness.
All of the data needed for proof construction is published on Ethereum L1.
There is a 9d exit window (or 2d if shortened by the Priority Controller).
Users are able to trustlessly exit by submitting a Merkle proof of funds. Positions will be closed using the average price from the last batch state update.
All data required for proofs is published on chain
All the relevant data that is used to recover the balances Merkle Tree is published onchain as calldata. This includes, in addition to the proven new state, the complete list of differences of the users’ balances from the previous state.
- Data Availability Modes - StarkEx documentation
- ZK Rollup - StarkEx documentation
- UpdatePerpetualState.sol#L82 - Etherscan source code, updateState function
State can be independently derived from data (state updates) published on Ethereum by running an open-source StarkEx Explorer. The explorer, once fully synced, provides UI interface to perform forced actions, trigger rollup freeze and withdraw funds using escape hatch.
No compression is used, state updates and other metadata are simply serialized for L1
There is no genesis file for dYdX. By default, all accounts were empty at the beginning.
dYdX doesn’t publish transactions. Balances of user positions are stored in a Merkle Tree and updates to that tree are published on Ethereum, together with Merkle Root and a ZK proof. Deserialization of that data is implemented here. Generating Merkle Proof is implemented here.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract. The system state is represented using Merkle roots.
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2024 October 31, 10:41 UTC4changesThe escape hatch is open and the according verifier operational. Link to escape hatch added to header warn.
The escape hatch is open and the according verifier operational. Link to escape hatch added to header warn.
| contract PerpetualEscapeVerifier (0x626211C1e9BC633f4D342Af99f4E8bc93f11F3DD) { | |
| +++ description: None | |
| values.hasRegisteredFact: | |
| - | false |
| + | true |
| } |
| contract StarkPerpetual (0xD54f502e184B6B739d7D27a6410a67dc462D69c8) { | |
| +++ description: None | |
| values.isFrozen: | |
| - | false |
| + | true |
| } |
2024 January 09, 11:54 UTCHigh severity11changesImplementation of Proposal DIP-29 intended to bridge ethDYDX tokens from Treasury on Ethereum to dYdX Chain.
Implementation of Proposal DIP-29 intended to bridge ethDYDX tokens from Treasury on Ethereum to dYdX Chain.
| contract Treasury (0x639192D54431F8c816368D3FB4107Bc168d0E871) { | |
| name: | |
| - | "Treasury" |
| + | "TreasuryBridge" |
| upgradeability.implementation: | |
| - | "0x0AdA60E07717Ab19E4A466f5f0ac68A66e3995Ce" |
| + | "0x8d0051943D4c72aF12D638c6b7253C71929A910A" |
| implementations.0: | |
| - | "0x0AdA60E07717Ab19E4A466f5f0ac68A66e3995Ce" |
| + | "0x8d0051943D4c72aF12D638c6b7253C71929A910A" |
| values.BRIDGE: | |
| + | "0x46b2DeAe6eFf3011008EA27EA36b7c27255ddFA9" |
| values.BURN_ADDRESS: | |
| + | "0x0000000000000000000000000000000000000001" |
| values.TREASURY_VESTER: | |
| + | "0xb9431E19B29B952d9358025f680077C3Fd37292f" |
| } |
| contract TreasuryVester (0xb9431E19B29B952d9358025f680077C3Fd37292f) { | |
| values.recipient: | |
| - | "0x639192D54431F8c816368D3FB4107Bc168d0E871" |
| + | "0x0000000000000000000000000000000000000001" |
| } |
2023 October 05, 07:17 UTC5changesProposal: <https://dydx.community/dashboard/proposal/15 TLDR: added wethDYDX in the calculation of governance power. wethDYDX is a token minted by locking Ethereum DYDX tokens (called ethDYDX) permanently which will be later bridged to the dYdX Chain. wethDYDX is a transferable ERC20. Does this mean that tokens will get duplicated? We don't have a specific section on the website to specify this information, but we will soon with the Governance section, so I'll wait before adding anything to the project page.
Proposal: https://dydx.community/dashboard/proposal/15
TLDR: added wethDYDX in the calculation of governance power. wethDYDX is a token minted by locking Ethereum DYDX tokens (called ethDYDX) permanently which will be later bridged to the dYdX Chain. wethDYDX is a transferable ERC20. Does this mean that tokens will get duplicated?
We don’t have a specific section on the website to specify this information, but we will soon with the Governance section, so I’ll wait before adding anything to the project page.
| contract DydxGovernor (0x7E9B1672616FF6D6629Ef2879419aaE79A9018D2) { | |
| values.getGovernanceStrategy: | |
| - | "0x90Dfd35F4a0BB2d30CDf66508085e33C353475D9" |
| + | "0xc2f5F3505910Da80F0592a3Cc023881C50b16505" |
| } |
| - | Status: DELETED |
| contract GovernanceStrategy (0x90Dfd35F4a0BB2d30CDf66508085e33C353475D9) { | |
| } |
| + | Status: CREATED |
| contract WrappedEthereumDydxToken (0x46b2DeAe6eFf3011008EA27EA36b7c27255ddFA9) { | |
| } |
| + | Status: CREATED |
| contract GovernanceStrategyV2 (0xc2f5F3505910Da80F0592a3Cc023881C50b16505) { | |
| } |
2023 September 26, 11:49 UTC1change
| contract SafetyModule (0x65f7BA4Ec257AF7c55fd5854E5f6356bBd0fb8EC) { | |
| values.slashings: | |
| + | [] |
| } |
The system has a centralized operator
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force exit the system
Force exit allows the users to escape censorship by withdrawing their funds. The system allows users to force the withdrawal of funds by submitting a request directly to the contract onchain. The request must be served within 14d. If this does not happen, the system will halt regular operation and permit trustless withdrawal of funds. Perpetual positions can also be force closed before withdrawing, however this requires the user to find the counterparty for the trade themselves.
Users can be censored if the operator refuses to include their transactions. However, there exists a mechanism to independently exit the system.
Funds can be lost if the user is unable to find the counterparty for the force trade.
Forced exit
If the user experiences censorship from the operator with regular exit they can submit their withdrawal requests directly on L1. The system is then obliged to service this request. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular exit.
Emergency exit
If the enough time deadline passes and the forced exit is still ignored the user can put the system into a frozen state, disallowing further state updates. In that case everybody can withdraw by submitting a merkle proof of their funds with their L1 transaction.

Ethereum
Actors:
Can decrease the delay required for the Rollup upgrade to 2d.
Controlled by dYdX Governance. Owner of dYdX token. Can upgrade Treasury, Liquidity Module and Merkle Distributor. Currently there is 2d delay before the upgrade.
Controlled by dYdX Governance. Has the ability to update Governance Strategy resulting in different logic of votes counting. Can upgrade Safety Module. Currently there is 7d delay before the upgrade.
Controlled by dYdX Governance. The Merkle-pauser executor can freeze the Merkle root, which is updated periodically with each user cumulative reward balance, in case the proposed root is incorrect or malicious. It can also veto forced trade requests by any of the stark proxy contracts.Currently there is 0s delay before the upgrade.

Ethereum

Contract storing CAIRO Program Output, in case of dYdX, it stores state diffs of dYdX Exchange.
Contract responsible for validating force withdrawal requests.
The Merkle Distributor smart contract distributes DYDX token rewards according to a Merkle tree of balances.
The Liquidity Module is a collection of smart contracts for staking and borrowing, which incentivize the allocation of USDC funds for market making purposes on the dYdX layer 2 exchange.
The Safety Module is a staking pool that offers DYDX rewards to users who stake DYDX towards the security of the Protocol.
Contract storing dYdX Governance logic.
Contract storing logic for votes counting in dYdX Governance.
Token used by the dYdX Governance for voting.
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 9d delay on code upgrades.The delay can be decreased by the Priority Controller to 2d.