 ZKSpace
ZKSpace
$2.74 M
6.29%
- Upgrades executed by actors with more centralized control than a Security Council provide less than 7d for users to exit if the permissioned operator is down or censoring.
| Website | zks.org |
|---|---|
| App | zks.app |
| Docs | en.wiki.zks.org |
| Explorer | zkspace.info |
| Repository | github.com/l2labs/zkswap-contracts |
| Social | @zkspaceofficial@ZKSpaceOfficialDiscordZKSpaceOfficialr/ZKSwap_Official |
...
Choose token
 Zks (ZKS)
Zks (ZKS) Ether (ETH)
Ether (ETH) Tether USD (USDT)
Tether USD (USDT) Wrapped BTC (WBTC)
Wrapped BTC (WBTC) USD Coin (USDC)
USD Coin (USDC) Dai Stablecoin (DAI)
Dai Stablecoin (DAI) Uniswap (UNI)
Uniswap (UNI) LoopringCoin V2 (LRC)
LoopringCoin V2 (LRC) 0x Protocol Token (ZRX)
0x Protocol Token (ZRX) 10Set Token (10SET)
10Set Token (10SET) 1INCH Token (1INCH)
1INCH Token (1INCH) Aave Token (AAVE)
Aave Token (AAVE) Across Protocol Token (ACX)
Across Protocol Token (ACX) Alchemix USD (alUSD)
Alchemix USD (alUSD) Alchemy (ACH)
Alchemy (ACH)...
Token Deposit Campaign started
2022 Feb 21st
Incentives program to onboard new users has started.
ZKSpace launched
2021 Dec 20th
All-in-One Layer2 Platform ZKSpace, Featuring ZKSwap v3.0, NFTs, & Payments is launched.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
State validation
ZK proofs (SN)zkSNARKS are zero knowledge proofs that ensure state correctness, but require trusted setup.
Data availability
On chainAll of the data needed for proof construction is published on chain.
Exit window
5dUsers have 5d to exit funds in case of an unwanted upgrade. There is a 8d delay before an upgrade is applied, and withdrawals can take up to 3d to be processed.
Sequencer failure
Force via L1Users can force the sequencer to include a withdrawal transaction by submitting a request through L1. If the sequencer censors or is down for for more than 3d, users can use the exit hatch to withdraw their funds.
Proposer failure
Use escape hatchUsers are able to trustlessly exit by submitting a zero knowledge proof of funds.
Validity proofs ensure state correctness
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
Zero knowledge SNARK cryptography is used
Despite their production use zkSNARKs are still new and experimental cryptography. Cryptography has made a lot of advancements in the recent years but all cryptographic solutions rely on time to prove their security. In addition zkSNARKs require a trusted setup to operate.
Funds can be stolen if the cryptography is broken or implemented incorrectly.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap calldata. This ensures that it will always be available when needed.
The system has a centralized operator
The operator is the only entity that can propose blocks. A live and trustworthy operator is vital to the health of the system.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force exit the system
Force exit allows the users to escape censorship by withdrawing their funds. The system allows users to force the withdrawal of funds by submitting a request directly to the contract on-chain. The request must be served within a defined time period. If this does not happen, the system will halt regular operation and permit trustless withdrawal of funds.
Users can be censored if the operator refuses to include their transactions. However, there exists a mechanism to independently exit the system.
Regular exit
The user initiates the withdrawal by submitting a regular transaction on this chain. When the block containing that transaction is proven the funds become available for withdrawal on L1. Finally the user submits an L1 transaction to claim the funds. This transaction does not require a merkle proof.
Forced exit
If the user experiences censorship from the operator with regular exit they can submit their withdrawal requests directly on L1. The system is then obliged to service this request. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular exit.
Emergency exit
If the enough time deadline passes and the forced exit is still ignored the user can put the system into Exodus Mode, disallowing further state updates. In that case everybody can withdraw by submitting a zero knowledge proof of their funds with their L1 transaction.
Funds can be lost if the user is unable to generate the non-trivial ZK proof for exodus withdraw.
The system uses the following set of permissioned addresses:
This address is the master of Upgrade Gatekeeper contract, which is allowed to perform upgrades for Governance, Verifier, VerifierExit, PairManager, ZkSeaNFT and ZkSync contracts.
This actor is allowed to propose, revert and execute L2 blocks on L1. A list of active validators is kept inside Governance contract and can be updated by zkSpace Admin.
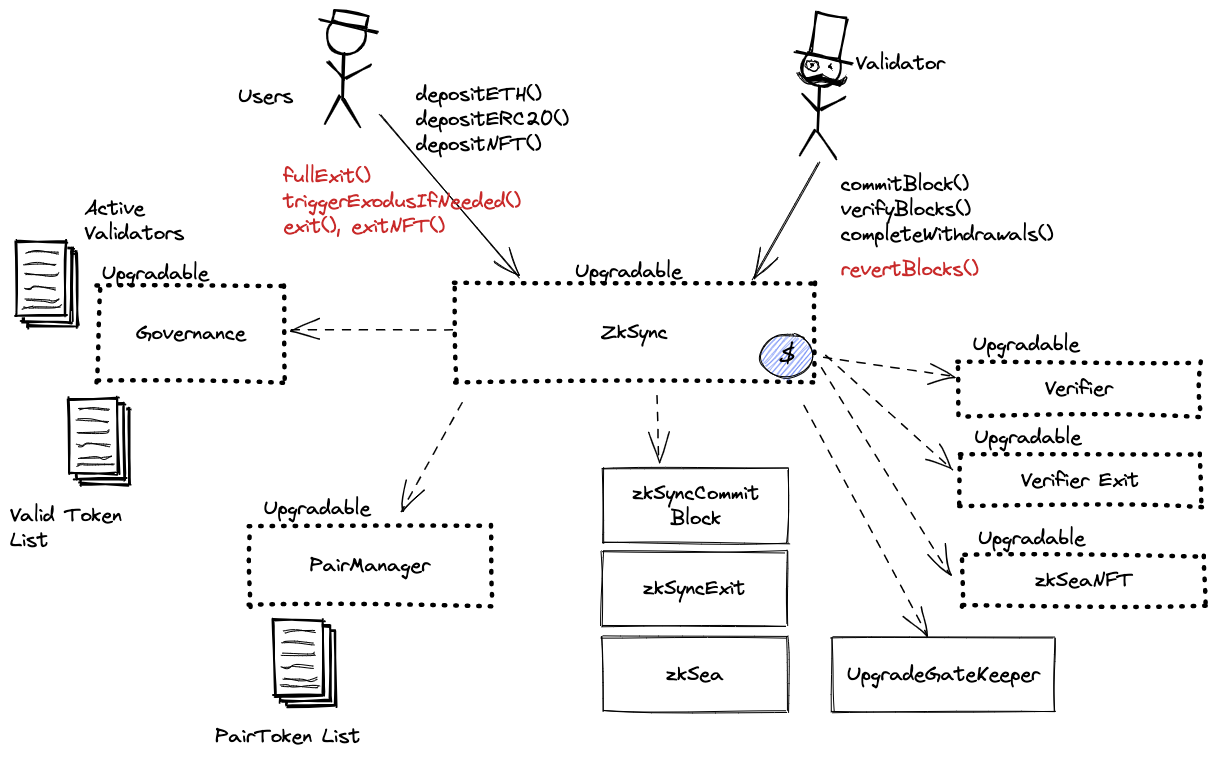
The system consists of the following smart contracts:
The main Rollup contract. Operator commits blocks, provides ZK proof which is validated by the Verifier contract and process withdrawals (executes blocks). Users deposit ETH and ERC20 tokens. This contract defines the upgrade delay in the UPGRADE_NOTICE_PERIOD constant that is currently set to 8 days. This contract can store any token.
Can be upgraded by: zkSpace Admin
Keeps a list of block producers and whitelisted tokens.
Can be upgraded by: zkSpace Admin
Manages trading pairs.
Can be upgraded by: zkSpace Admin
Contract managing deposits and withdrawals of NFTs to Layer2.
Can be upgraded by: zkSpace Admin
zkSNARK Plonk Verifier.
Can be upgraded by: zkSpace Admin
zkSNARK Verifier for the escape hatch.
Can be upgraded by: zkSpace Admin
This is the contract that implements the upgrade mechanism for Governance, Verifier and ZkSync. It relies on the ZkSync contract to enforce upgrade delays.
Value Locked is calculated based on these smart contracts and tokens:
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 8d delay on code upgrades.
