Search
Search for projects by name or address
 Syndicate Chain
Syndicate Chain
Badges
About
Syndicate Chain is an Arbitrum Orbit rollup on Ethereum using SYND as its native gas token. It serves as the primary settlement layer for the Syndicate ecosystem.
Badges
About
Syndicate Chain is an Arbitrum Orbit rollup on Ethereum using SYND as its native gas token. It serves as the primary settlement layer for the Syndicate ecosystem.
Why is the project listed in others?
Consequence: projects without a sufficiently decentralized set of challengers rely on few entities to safely update the state. A small set of challengers can collude with the proposer to finalize an invalid state, which can cause loss of funds.
Learn more about the recategorisation here.
2025 Jul 29 — 2026 May 28
The section shows the operating costs that L2s pay to Ethereum.
2025 Jul 29 — 2026 May 28
This section shows how much data the project publishes to its data-availability (DA) layer over time. The project currently posts data to![]() Ethereum.
Ethereum.
2026 Feb 06 — May 28
This section shows how "live" the project's operators are by displaying how frequently they submit transactions of the selected type. It also highlights anomalies - significant deviations from their typical schedule.
Last 30 day anomalies
All liveness anomalies detected for this project in the last 30 days, helping you review recent downtime and availability issues.
No Tx data submissions were performed for 1h 5m (from 2026 Apr 30, 16:45 UTC until 2026 Apr 30, 17:50 UTC). These typically occur every 1h 58s on average.
No Tx data submissions were performed for 1h 3m 48s (from 2026 Apr 30, 14:43 UTC until 2026 Apr 30, 15:47 UTC). These typically occur every 1h 58s on average.
Funds can be stolen if
MEV can be extracted if
No actor outside of the single Proposer can submit fraud proofs. Interactive proofs (INT) require multiple transactions over time to resolve. The challenge protocol can be subject to delay attacks. There is a 7d challenge period.
All of the data needed for proof construction is published on Ethereum L1.
There is no window for users to exit in case of an unwanted upgrade since contracts are instantly upgradable.
Anyone can become a Proposer after 1mo 5d of inactivity from the currently whitelisted Proposers.
All data required for proofs is published on chain
All the data that is used to construct the system state is published on chain in the form of cheap blobs or calldata. This ensures that it will be available for enough time.
- Sequencing followed by deterministic execution - Arbitrum documentation
- SequencerInbox.sol - source code, addSequencerL2BatchFromOrigin function
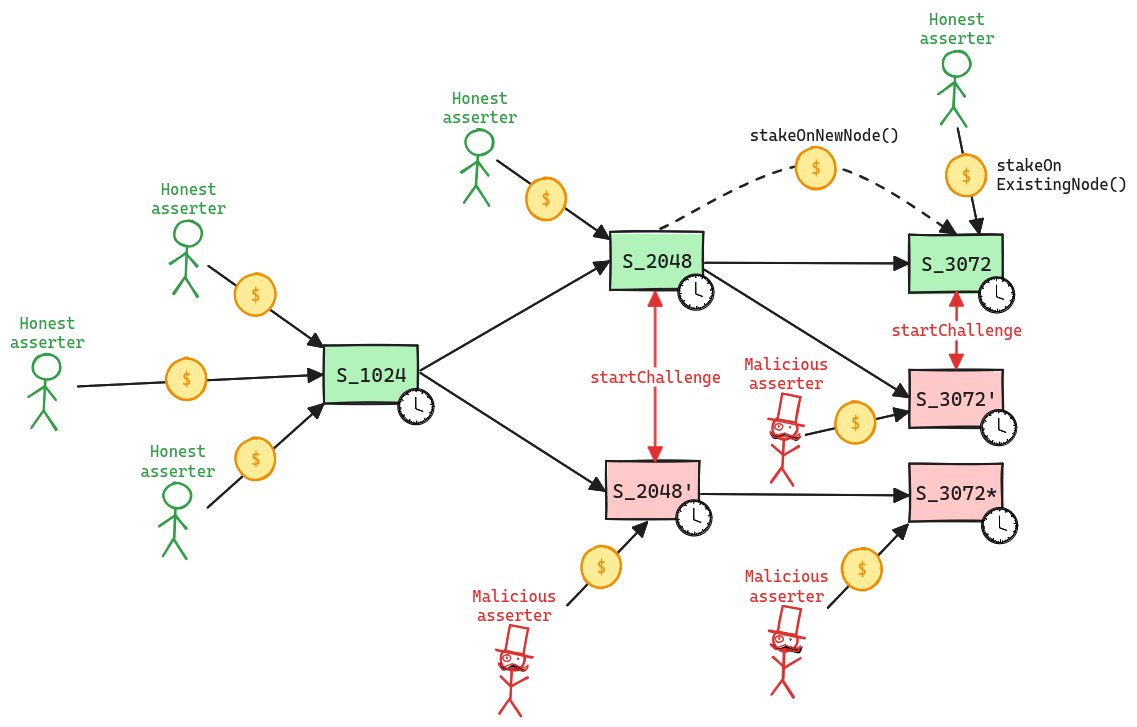
Updates to the system state can be proposed and challenged by a set of whitelisted validators. If a state root passes the challenge period, it is optimistically considered correct and made actionable for withdrawals.
Whitelisted validators propose state roots as children of a previous state root. A state root can have multiple conflicting children. This structure forms a graph, and therefore, in the contracts, state roots are referred to as nodes. Each proposal requires a stake, currently set to 0.1 ETH, that can be slashed if the proposal is proven incorrect via a fraud proof. Stakes can be moved from one node to one of its children, either by calling stakeOnExistingNode or stakeOnNewNode. New nodes cannot be created faster than the minimum assertion period by the same validator, currently set to 15m. The oldest unconfirmed node can be confirmed if the challenge period has passed and there are no siblings, and rejected if the parent is not a confirmed node or if the challenge period has passed and no one is staked on it.
Funds can be stolen if none of the whitelisted verifiers checks the published state. Fraud proofs assume at least one honest and able validator (CRITICAL).
A challenge can be started between two siblings, i.e. two different state roots that share the same parent, by calling the startChallenge function. Validators cannot be in more than one challenge at the same time, meaning that the protocol operates with partial concurrency. Since each challenge lasts 7d, this implies that the protocol can be subject to delay attacks, where a malicious actor can delay withdrawals as long as they are willing to pay the cost of losing their stakes. If the protocol is delayed attacked, the new stake requirement increases exponentially for each challenge period of delay. Challenges are played via a bisection game, where asserter and challenger play together to find the first instruction of disagreement. Such instruction is then executed onchain in the WASM OneStepProver contract to determine the winner, who then gets half of the stake of the loser. As said before, a state root is rejected only when no one left is staked on it. The protocol does not enforces valid bisections, meaning that actors can propose correct initial claim and then provide incorrect midpoints.
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2026 April 07, 22:00 UTC3changesEigenDAOperationsMultisig member removed (0x4985...), threshold unchanged at 3, now 3-of-4 (75%) instead of 3-of-5 (60%). Shared contract with eigenda/megaeth.
EigenDAOperationsMultisig member removed (0x4985…), threshold unchanged at 3, now 3-of-4 (75%) instead of 3-of-5 (60%). Shared contract with eigenda/megaeth.
| contract EigenDAOperationsMultisig (eth:0x002721B4790d97dC140a049936aA710152Ba92D5) { | |
| +++ description: None | |
| values.$members.1: | |
| - | "eth:0x4985238672d91Baed43dF1B2431F67bc332A1753" |
| values.multisigThreshold: | |
| - | "3 of 5 (60%)" |
| + | "3 of 4 (75%)" |
| } |
2026 March 13, 16:31 UTC43changesDiscovery rerun on the same block number with only config-related changes.
Discovery rerun on the same block number with only config-related changes.
Initial discovery
| + | Status: CREATED |
| contract EigenDAOperationsMultisig (eth:0x002721B4790d97dC140a049936aA710152Ba92D5) | |
| +++ description: None |
| + | Status: CREATED |
| contract StakeRegistry (eth:0x006124Ae7976137266feeBFb3F4D2BE4C073139D) | |
| +++ description: Keeps track of the total stake of each operator. |
| + | Status: CREATED |
| contract BLSApkRegistry (eth:0x00A5Fd09F6CeE6AE9C8b0E5e33287F7c82880505) | |
| +++ description: Keeps track of the BLS public keys of each operator and the quorum aggregated keys. |
| + | Status: CREATED |
| contract RegistryCoordinator (eth:0x0BAAc79acD45A023E19345c352d8a7a83C4e5656) | |
| +++ description: Operators register here with an AVS: The coordinator has three registries: 1) a `StakeRegistry` that keeps track of operators' stakes, 2) a `BLSApkRegistry` that keeps track of operators' BLS public keys and aggregate BLS public keys for each quorum, 3) an `IndexRegistry` that keeps track of an ordered list of operators for each quorum. |
| + | Status: CREATED |
| contract PauserRegistry (eth:0x0c431C66F4dE941d089625E5B423D00707977060) | |
| +++ description: Defines and stores pauser and unpauser roles for EigenDA contracts. |
| + | Status: CREATED |
| contract SequencerInbox (eth:0x12ad349e5d72B582856290736e0f13FE5fA57Aa4) | |
| +++ description: None |
| + | Status: CREATED |
| contract EjectionManager (eth:0x130d8EA0052B45554e4C99079B84df292149Bd5E) | |
| +++ description: Contract used for ejection of operators from the RegistryCoordinator for violating the Service Legal Agreement (SLA). |
| + | Status: CREATED |
| reference AVSDirectory (eth:0x135DDa560e946695d6f155dACaFC6f1F25C1F5AF) | |
| +++ description: None |
| + | Status: CREATED |
| contract EigenLayerRewardsInitiatorMultisig (eth:0x178eeeA9E0928dA2153A1d7951FBe30CF8371b8A) | |
| +++ description: None |
| + | Status: CREATED |
| contract Syndicate Token (eth:0x1bAB804803159aD84b8854581AA53AC72455614E) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProver0 (eth:0x2420b6bF83B8fEEab576F2f3e5B5d130F2376b2F) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract OneStepProverMemory (eth:0x27CD0B994cc40a74962Db2fA6b973bf7d19f6Ec6) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract EigenDA Multisig (eth:0x338477FfaF63c04AC06048787f910671eC914B34) | |
| +++ description: None |
| + | Status: CREATED |
| reference EigenLayerOwningMultisig (eth:0x369e6F597e22EaB55fFb173C6d9cD234BD699111) | |
| +++ description: None |
| + | Status: CREATED |
| reference DelegationManager (eth:0x39053D51B77DC0d36036Fc1fCc8Cb819df8Ef37A) | |
| +++ description: None |
| + | Status: CREATED |
| contract Bridge (eth:0x3C8cF0ae6E89AC0796f29B3a58e7dEa1cD072277) | |
| +++ description: None |
| + | Status: CREATED |
| contract RollupProxy (eth:0x451bD7813909B899DA6EbEC55E8fF823c057e14A) | |
| +++ description: None |
| + | Status: CREATED |
| contract (eth:0x481D290473e4f6929AA45CFb7Ef7c7847aBeD007) | |
| +++ description: None |
| + | Status: CREATED |
| reference EigenLayerPauserMultisig (eth:0x5050389572f2d220ad927CcbeA0D406831012390) | |
| +++ description: None |
| + | Status: CREATED |
| contract GatewayRouter (eth:0x534Eb1F79C8df3aB1E507e408EeF4e99D53A1239) | |
| +++ description: This routing contract maps tokens to the correct escrow (gateway) to be then bridged with canonical messaging. |
| + | Status: CREATED |
| contract SocketRegistry (eth:0x5a3eD432f2De9645940333e4474bBAAB8cf64cf2) | |
| +++ description: None |
| + | Status: CREATED |
| contract Inbox (eth:0x5EA55Fd41D42Eb307D281bdE78E4e7572A35ea13) | |
| +++ description: Facilitates sending L1 to L2 messages like depositing ETH, but does not escrow funds. |
| + | Status: CREATED |
| contract ERC20Gateway (eth:0x6CA109706c6EBe5379c45f20B3311441D50cb711) | |
| +++ description: Escrows deposited ERC-20 assets for the canonical Bridge. Upon depositing, a generic token representation will be minted at the destination. Withdrawals are initiated by the Outbox contract. |
| + | Status: CREATED |
| contract OneStepProverHostIo (eth:0x6D25E739016f42B70885E63629C7356C2E29a2D7) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProverMath (eth:0x78471572Be99D99f9CE5867B208F15A75F074235) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract EigenDACertVerifier (eth:0x787c88E70900f6AE10E7B9D18024482895EBD1eb) | |
| +++ description: None |
| + | Status: CREATED |
| contract EigenDADisperserRegistry (eth:0x78cb05379a3b66E5227f2C1496432D7FFE794Fad) | |
| +++ description: Registry for EigenDA disperser info such as disperser key to address mapping. |
| + | Status: CREATED |
| contract ProxyAdmin (eth:0x817BE2d0f28b594D7023dAdf2b3Aa54327180c66) | |
| +++ description: None |
| + | Status: CREATED |
| contract ProxyAdmin (eth:0x8247EF5705d3345516286B72bFE6D690197C2E99) | |
| +++ description: None |
| + | Status: CREATED |
| contract RollupEventInbox (eth:0x82E761873714cDe47C594aA6F23E6b1844CD98dB) | |
| +++ description: Helper contract sending configuration data over the bridge during the systems initialization. |
| + | Status: CREATED |
| contract EigenDAServiceManager (eth:0x870679E138bCdf293b7Ff14dD44b70FC97e12fc0) | |
| +++ description: Bridge contract that accepts blob batches data availability attestations. Batches availability is attested by EigenDA operators signatures and relayed to the service manager contract by the EigenDA disperser. |
| + | Status: CREATED |
| contract Alchemy Multisig 1 (eth:0xA4fB12D15Eb85dc9284a7df0AdBC8B696EdbbF1d) | |
| +++ description: None |
| + | Status: CREATED |
| contract OneStepProofEntry (eth:0xa8aA9784FA7eC40Dc81d298130746c2FA4785EC8) | |
| +++ description: One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine. |
| + | Status: CREATED |
| contract ValidatorUtils (eth:0xAa1EaB2ea108FDbCABd760a37E0B06f6e1dA8cC0) | |
| +++ description: This contract implements view only utilities for validators. |
| + | Status: CREATED |
| contract EigenDAThresholdRegistry (eth:0xab26536B7CaA4928708152272967FF1B32Fbf96a) | |
| +++ description: Registry of EigenDA threshold (i.e, adversary and confirmation threshold percentage for a quorum) |
| + | Status: CREATED |
| contract ChallengeManager (eth:0xABf2988264170a7f94E6Fa76ECA5965B906E229d) | |
| +++ description: Contract that allows challenging state roots. Can be called through the RollupProxy by Validators or the UpgradeExecutor. |
| + | Status: CREATED |
| contract PaymentVault (eth:0xb2e7ef419a2A399472ae22ef5cFcCb8bE97A4B05) | |
| +++ description: Entrypoint for making reservations and on demand payments for EigenDA. |
| + | Status: CREATED |
| contract IndexRegistry (eth:0xBd35a7a1CDeF403a6a99e4E8BA0974D198455030) | |
| +++ description: A registry contract that keeps track of an ordered list of operators for each quorum. |
| + | Status: CREATED |
| reference EigenLayerOperationsMultisig (eth:0xBE1685C81aA44FF9FB319dD389addd9374383e90) | |
| +++ description: None |
| + | Status: CREATED |
| contract EigenDARelayRegistry (eth:0xD160e6C1543f562fc2B0A5bf090aED32640Ec55B) | |
| +++ description: Registry for EigenDA relay keys, maps key to address. |
| + | Status: CREATED |
| contract EigenDAThresholdRegistry (eth:0xdb4c89956eEa6F606135E7d366322F2bDE609F15) | |
| +++ description: Registry of EigenDA threshold (i.e, adversary and confirmation threshold percentage for a quorum) |
| + | Status: CREATED |
| contract Outbox (eth:0xf555Bc86D1C953414F676479Bf7C979b1A737E8C) | |
| +++ description: Facilitates L2 to L1 contract calls: Messages initiated from L2 (for example withdrawal messages) eventually resolve in execution on L1. |
| + | Status: CREATED |
| contract UpgradeExecutor (eth:0xFA4d1D308f4B4f6E6F836Db2B77Db549606A460c) | |
| +++ description: Central contract defining the access control permissions for upgrading the system contract implementations. |
The system has a centralized sequencer
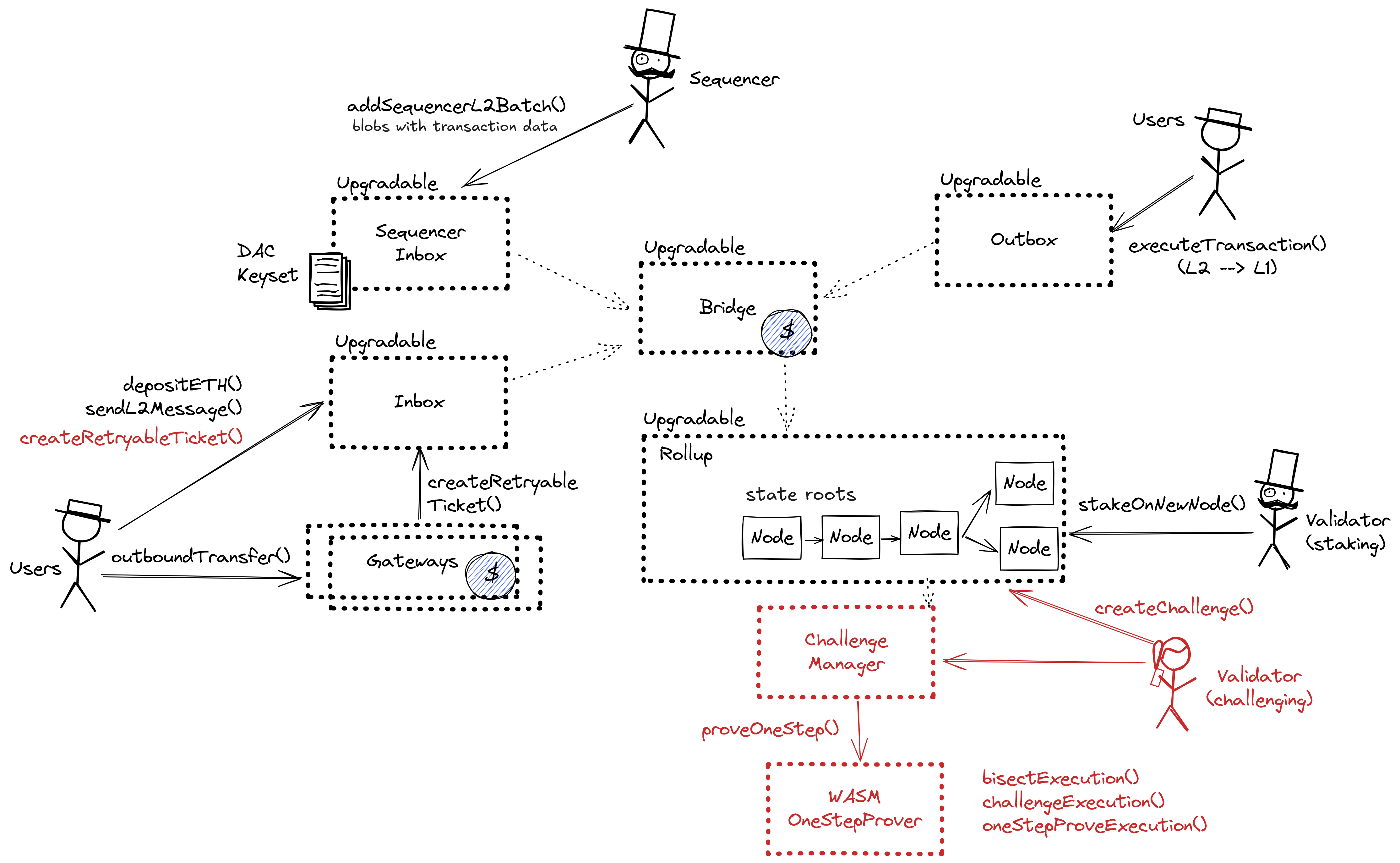
While forcing transaction is open to anyone the system employs a privileged sequencer that has priority for submitting transaction batches and ordering transactions.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly. After a delay of 4d in which a Sequencer has failed to include a transaction that was directly posted to the smart contract, it can be forcefully included by anyone on the host chain, which finalizes its ordering.
Delayed forced transactions
To force transactions from the host chain, users must first enqueue “delayed” messages in the “delayed” inbox of the Bridge contract. Only authorized Inboxes are allowed to enqueue delayed messages, and the so-called Inbox contract is the one used as the entry point by calling the sendMessage or sendMessageFromOrigin functions. If the centralized sequencer doesn’t process the request within some time bound, users can call the forceInclusion function on the SequencerInbox contract to include the message in the canonical chain. The time bound is hardcoded to be 4d.
Autonomous exit
Users can (eventually) exit the system by pushing the transaction on L1 and providing the corresponding state root. The only way to prevent such withdrawal is via an upgrade.
EVM compatible smart contracts are supported
Arbitrum One uses Nitro technology that allows running fraud proofs by executing EVM code on top of WASM.

Ethereum
Roles:
Can submit transaction batches or commitments to the SequencerInbox contract on the host chain.
Can propose new state roots (called nodes) and challenge state roots on the host chain.
Actors:
A Multisig with 3/5 threshold.
- Can upgrade with 10d delay
- swETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- TaskMailbox TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- AVSDirectory TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ankrETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- rETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- PermissionController TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ProtocolRegistry TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- METH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- DelegationManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- BN254CertificateVerifier TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- cbETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- KeyRegistrar TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- OperatorTableUpdater TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- osETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- StrategyFactory TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EmissionsController TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- RewardsCoordinator TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- wBETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- StrategyManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- sfrxETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EigenPodManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- CrossChainRegistry TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- stETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- AllocationManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ETHx-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- OETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- bEIGEN-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- RiverV1-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ECDSACertificateVerifier TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EIGEN token TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ReleaseManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- Can upgrade with 24d delay
- bEIGEN token TimelockControllerBeigen with 24d delay → EigenLayerBeigenOwningMultisig → ProxyAdmin
- Can interact with UpgradeableBeacon
- change the beacon implementation with 10d delay TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig
- Can interact with TimelockControllerBeigen
- executes scheduled operations after the delay
- Can interact with TimelockControllerOwning
- executes scheduled operations after the delay
A Multisig with 3/6 threshold.
- Can upgrade with 10d delay
- swETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- TaskMailbox TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- AVSDirectory TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ankrETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- rETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- PermissionController TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ProtocolRegistry TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- METH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- DelegationManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- BN254CertificateVerifier TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- cbETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- KeyRegistrar TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- OperatorTableUpdater TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- osETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- StrategyFactory TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EmissionsController TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- RewardsCoordinator TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- wBETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- StrategyManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- sfrxETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EigenPodManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- CrossChainRegistry TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- stETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- AllocationManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ETHx-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- OETH-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- bEIGEN-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- RiverV1-Strategy TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ECDSACertificateVerifier TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EIGEN token TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ReleaseManager TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig → EigenLayerProxyAdmin
- Can upgrade with 24d delay
- bEIGEN token TimelockControllerBeigen with 24d delay → EigenLayerBeigenOwningMultisig → ProxyAdmin
- Can interact with UpgradeableBeacon
- change the beacon implementation with 10d delay TimelockControllerOwning with 10d delay → EigenLayerOwningMultisig
- Can interact with TimelockControllerBeigen
- can cancel scheduled operations
- Can interact with TimelockControllerOwning
- can cancel scheduled operations
A Multisig with 9/13 threshold. Member of EigenLayerOwningMultisig, EigenLayerBeigenOwningMultisig.
- Can upgrade with no delay
- swETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- TaskMailbox EigenLayerOwningMultisig → EigenLayerProxyAdmin
- AVSDirectory EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ankrETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- rETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- PermissionController EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ProtocolRegistry EigenLayerOwningMultisig → EigenLayerProxyAdmin
- METH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- DelegationManager EigenLayerOwningMultisig → EigenLayerProxyAdmin
- BN254CertificateVerifier EigenLayerOwningMultisig → EigenLayerProxyAdmin
- cbETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- KeyRegistrar EigenLayerOwningMultisig → EigenLayerProxyAdmin
- OperatorTableUpdater EigenLayerOwningMultisig → EigenLayerProxyAdmin
- osETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- StrategyFactory EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EmissionsController EigenLayerOwningMultisig → EigenLayerProxyAdmin
- RewardsCoordinator EigenLayerOwningMultisig → EigenLayerProxyAdmin
- wBETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- bEIGEN token EigenLayerBeigenOwningMultisig → ProxyAdmin
- StrategyManager EigenLayerOwningMultisig → EigenLayerProxyAdmin
- sfrxETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EigenPodManager EigenLayerOwningMultisig → EigenLayerProxyAdmin
- CrossChainRegistry EigenLayerOwningMultisig → EigenLayerProxyAdmin
- stETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- AllocationManager EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ETHx-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- OETH-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- bEIGEN-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- RiverV1-Strategy EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ECDSACertificateVerifier EigenLayerOwningMultisig → EigenLayerProxyAdmin
- EIGEN token EigenLayerOwningMultisig → EigenLayerProxyAdmin
- ReleaseManager EigenLayerOwningMultisig → EigenLayerProxyAdmin
- Can interact with UpgradeableBeacon
- change the beacon implementation EigenLayerOwningMultisig
Participants (13):
0x1791…41160x34C3…B2BC0x72Ff…4f54Safe0xED73…594b0x97b4…48150x65C4…842F0xe377…9D600x8ffC…Cd950xAF4D…F0610xe8F0…707e0x6A66…0b1f0x33E8…1626A Multisig with 3/4 threshold.
- Can upgrade with no delay
- StakeRegistry ProxyAdmin
- BLSApkRegistry ProxyAdmin
- RegistryCoordinator ProxyAdmin
- EjectionManager ProxyAdmin
- SocketRegistry ProxyAdmin
- EigenDADisperserRegistry ProxyAdmin
- EigenDAServiceManager ProxyAdmin
- PaymentVault ProxyAdmin
- IndexRegistry ProxyAdmin
- EigenDARelayRegistry ProxyAdmin
- EigenDAThresholdRegistry ProxyAdmin
- Can interact with RegistryCoordinator
- can add and remove strategies
- Can interact with EigenDAServiceManager
- can transfer ownership of the contract, update the metadata URI, set reward initiator and set batch confirmer
- Can upgrade with no delay
- SequencerInbox
- Bridge
- GatewayRouter
- Inbox
- ERC20Gateway
- RollupEventInbox
- ChallengeManager
- Outbox
- UpgradeExecutor
Defines and stores pauser and unpauser roles for EigenDA contracts.
- Can interact with EigenDAServiceManager
- can pause the DA bridge
A Multisig with 3/4 threshold.
- Can interact with EigenDAServiceManager
- can create rewards submissions
A Multisig with 3/8 threshold.
- Can interact with EjectionManager
- can eject DA operators from a quorum
Participants (8):
0x9308…a1250x5262…0aDA0x9951…683F0xA383…350A0x44aC…B9040x3C20…63e90xA4f7…dD310x542a…Bd7EA Multisig with 5/8 threshold.
- Can upgrade with no delay
- RollupProxy UpgradeExecutor
Participants (8):
0xa335…d1100xFB00…B1ca0x35A2…E1d70x0012…55120x04a2…F2Bd0xd144…16700xeD99…56540xB2aa…1a9dA Multisig with 1/1 threshold. Member of EigenLayerCommunityMultisig.
Participants (1):
0x5e6a…d3B5A Multisig with 1/1 threshold. Member of Safe.
Participants (1):
0x43cC…701CA Multisig with 2/8 threshold. Member of EigenLayerPauserMultisig.
Participants (8):
0xDe64…33700x55b0…44E80x4719…331A0xa9f9…3d280x5CCF…d0600xA756…84450xd757…B5530xe2eB…26D2- Can upgrade with no delay
- EigenDAThresholdRegistry ProxyAdmin
- Can interact with RegistryCoordinator
- can approve the replacement of churned operators from a quorum
- A Sequencer - acting directly
- Can upgrade with no delay
- RollupProxy UpgradeExecutor
- A Validator - acting directly

Ethereum
Contract that allows challenging state roots. Can be called through the RollupProxy by Validators or the UpgradeExecutor.
- Roles:
- admin: The source code of this contract is not verified on Etherscan.
Keeps track of the total stake of each operator.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
Keeps track of the BLS public keys of each operator and the quorum aggregated keys.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
Operators register here with an AVS The coordinator has three registries 1) a StakeRegistry that keeps track of operators’ stakes, 2) a BLSApkRegistry that keeps track of operators’ BLS public keys and aggregate BLS public keys for each quorum, 3) an IndexRegistry that keeps track of an ordered list of operators for each quorum.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
- churnApprover: EOA 7
- owner: EigenDAOperationsMultisig
Contract used for ejection of operators from the RegistryCoordinator for violating the Service Legal Agreement (SLA).
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
- ejectors: EOA 4, EOA 6, EigenDA Multisig
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
Registry for EigenDA disperser info such as disperser key to address mapping.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
- dispersers: EOA 9
Bridge contract that accepts blob batches data availability attestations. Batches availability is attested by EigenDA operators signatures and relayed to the service manager contract by the EigenDA disperser.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
- batchConfirmers: EOA 1, EOA 2, EOA 5
- owner: EigenDAOperationsMultisig
- pauserRegistry: PauserRegistry
- rewardsInitiator: EigenLayerRewardsInitiatorMultisig
Registry of EigenDA threshold (i.e, adversary and confirmation threshold percentage for a quorum)
- Roles:
- admin: ProxyAdmin; ultimately EOA 3
Entrypoint for making reservations and on demand payments for EigenDA.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
A registry contract that keeps track of an ordered list of operators for each quorum.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
Registry for EigenDA relay keys, maps key to address.
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
- relayers: EOA 8
Registry of EigenDA threshold (i.e, adversary and confirmation threshold percentage for a quorum)
- Roles:
- admin: ProxyAdmin; ultimately EigenDAOperationsMultisig
UpgradeableBeacon managing the single implementation for all strategies deployed via StrategyFactory.
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Task lifecycle manager where users create tasks with fee payments directed at specific executor operator sets, and executors submit results verified via BN254 or ECDSA certificate verification, with fee distribution on successful verification and refunds on task expiration.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Contract that enables AVSs and operators to delegate the ability to call certain core contract functions to other addresses.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Admin-controlled on-chain registry that tracks all EigenLayer protocol contract deployments (addresses, names, configs, and versioning) and provides a pauseAll function to pause every registered pausable contract in the protocol.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
The DelegationManager contract is responsible for registering EigenLayer operators and managing the EigenLayer strategies delegations. The EigenDA StakeRegistry contract reads from the DelegationManager to track the total stake of each EigenDA operator.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Verifies BLS (BN254 curve) certificates for EigenLayer operator sets by computing the aggregate public key of signers, performing pairing-based signature verification, and returning signed-stake weights for quorum threshold validation.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Manages the registration and deregistration of operator cryptographic keys (ECDSA or BN254/BLS) for specific operator sets, enforcing signature-based proof of key ownership and global uniqueness of keys across the protocol.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Central coordinator for EigenLayer’s operator table system: accepts BN254-certified global Merkle table roots from a designated generator operator set, then allows Merkle proof submissions to push per-operator-set tables into the certificate verifier contracts.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
UpgradeableBeacon managing the single implementation for all strategies deployed via StrategyFactory.
Factory contract for permissionless strategy creation via beacon proxies.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A timelock that allows scheduling calls and executing or cancelling them with a delay. Member of EigenLayerBeigenOwningMultisig.
- Roles:
- cancellers: EigenLayerOperationsMultisig
- executors: EigenLayerOperationsMultisig2
- proposers: EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
The token backing EIGEN and used for intersubjective staking.
- Roles:
- admin: ProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Allows AVSs to create generation reservations that configure and schedule the transport of operator tables (stake weight data) from L1 to whitelisted L2 chains, managing per-operator-set configs such as staleness periods and operator table calculators.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Contract used to create Operator Sets, and used by Operators to register to them. The Allocation Manager tracks allocation of stake to a Operator Set, and enables AVSs to slash that stake.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
A strategy implementation allowing to deposit a specific token as a restakable asset.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Defines and stores pauser and unpauser roles for EigenLayer contracts.
- Roles:
- pausers: EigenLayerOperationsMultisig, EigenLayerOwningMultisig, EigenLayerPauserMultisig, ProtocolRegistry
A timelock that allows scheduling calls and executing or cancelling them with a delay. Member of EigenLayerOwningMultisig.
- Roles:
- cancellers: EigenLayerOperationsMultisig
- executors: EigenLayerOperationsMultisig2
- proposers: EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Verifies ECDSA-based certificates for EigenLayer operator sets by recovering signer addresses from concatenated signatures, confirming each signer is a registered operator, and tallying their stake weights against quorum thresholds.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
The EIGEN token can be socially forked to slash operators for data withholding attacks (and other intersubjectively attributable faults). EIGEN is a wrapper over a second token, bEIGEN, which will be used solely for intersubjective staking. Forking EIGEN means changing the canonical implementation of the bEIGEN token in the EIGEN token contract.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Manages software release lifecycle for EigenLayer operator sets, allowing AVS owners to publish versioned releases (containing artifact digests, registry URLs, and upgrade-by deadlines) and metadata URIs that operators can query for required software versions.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Central contract defining the access control permissions for upgrading the system contract implementations.
- Roles:
- admin:
- executors: Alchemy Multisig 1, EOA 11 The source code of this contract is not verified on Etherscan.
Escrows deposited ERC-20 assets for the canonical Bridge. Upon depositing, a generic token representation will be minted at the destination. Withdrawals are initiated by the Outbox contract.
- Roles:
- admin:
All supported tokens in this escrow are included in the value secured calculation.
This routing contract maps tokens to the correct escrow (gateway) to be then bridged with canonical messaging.
- Roles:
- admin:
- Roles:
- admin:
- batchPosters: EOA 10 The source code of this contract is not verified on Etherscan.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
- Roles:
- admin: The source code of this contract is not verified on Etherscan.

- Roles:
- admin: UpgradeExecutor; ultimately Alchemy Multisig 1, EOA 11
- validators: EOA 12 The source code of this contract is not verified on Etherscan.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
- Roles:
- owner: EOA 3
Helper contract sending configuration data over the bridge during the systems initialization.
- Roles:
- admin: The source code of this contract is not verified on Etherscan.
One of the modular contracts used for the last step of a fraud proof, which is simulated inside a WASM virtual machine.
This contract implements view only utilities for validators.
A beacon with an upgradeable implementation currently set as DurationVaultStrategy. Beacon proxy contracts pointing to this beacon will all use its implementation.
- Roles:
- owner: EigenLayerOwningMultisig; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
Manages the distribution of rewards (arbitrary tokens, EIGEN) to restakers and commission to operators.
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
- Roles:
- admin: EigenLayerProxyAdmin; ultimately EigenLayerCommunityMultisig, EigenLayerOperationsMultisig, EigenLayerOperationsMultisig2
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).
Funds can be stolen if the source code of unverified contracts contains malicious code (CRITICAL).