Search
Search for projects by name or address
 Immutable X
Immutable X
Badges
About
Immutable X is a NFT-focused Validium providing zero gas fees, instant trades and scalability for applications.
Badges
About
Immutable X is a NFT-focused Validium providing zero gas fees, instant trades and scalability for applications.
Why is the project listed in others?
Consequence: projects with a low DAC threshold rely on the honesty of few entities to safely attest data availability on Ethereum. These entities can collude with the proposer to finalize an unavailable state, which can cause loss of funds.
Learn more about the recategorisation here.
2021 Mar 26 — 2026 May 30
Immutable X migrated to Immutable zkEVM
2026 Mar 5th
Immutable X deployed contracts for migration to Immutable zkEVM. Operation of Immutable X halts.
IMX Token introduced
2022 Jun 29th
Immutable announce IMX, the native ERC-20 utility token of Immutable X.
Funds can be stolen if
Funds can be lost if
Users can be censored if
MEV can be extracted if
There is no mechanism to have transactions be included if the sequencer is down or censoring.
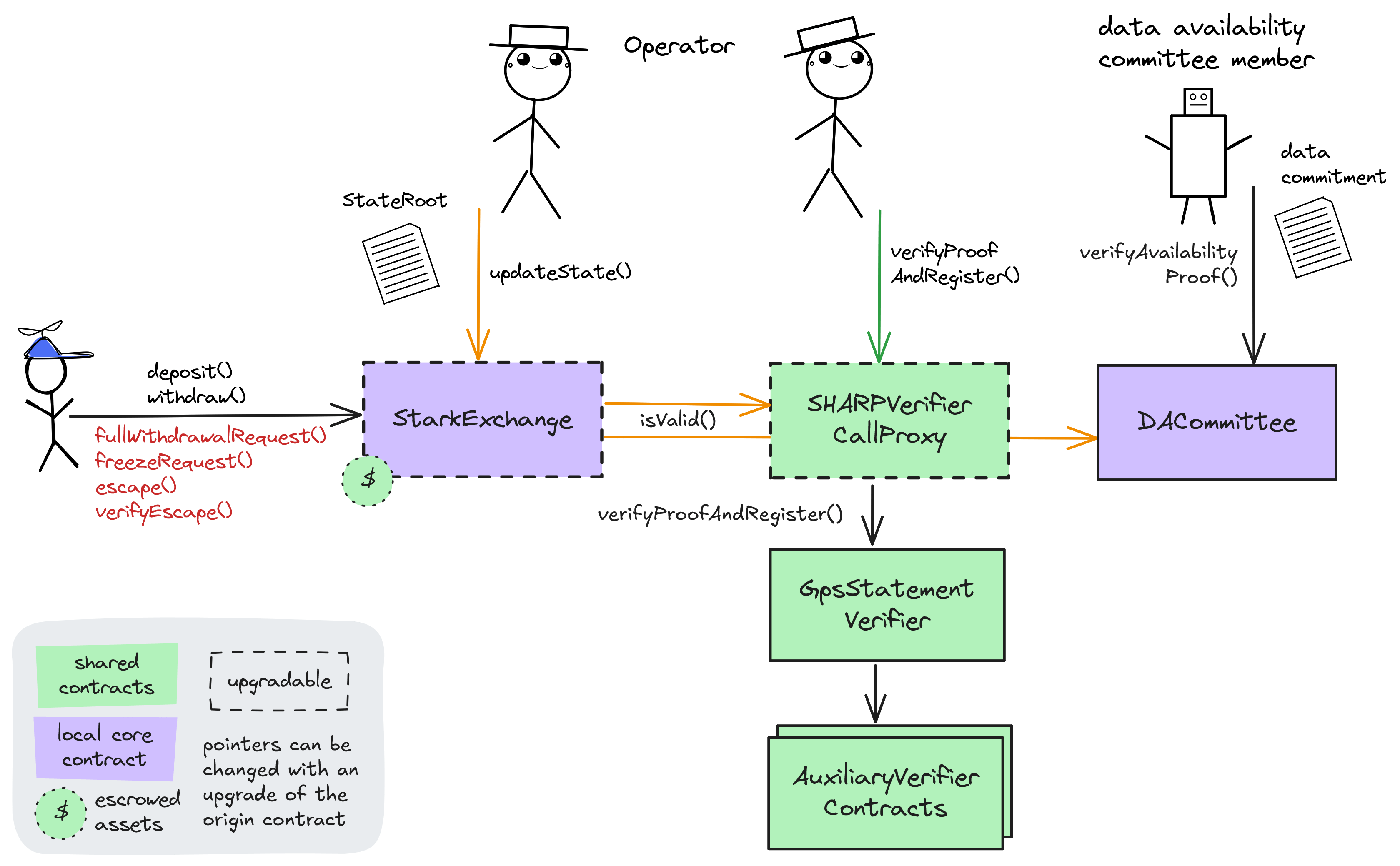
STARKs are zero knowledge proofs that ensure state correctness.
Proof construction relies fully on data that is NOT published onchain. There exists a Data Availability Committee (DAC) with a threshold of 5/7 that is tasked with protecting and supplying the data.
Users have 14d to exit funds in case of an unwanted upgrade. There is a 14d delay before a upgrade is applied, and withdrawals can take up to 0s to be processed.
Users are able to trustlessly exit by submitting a Merkle proof of funds. NFTs will be minted on L1 to exit.
Data is not stored on chain
The balances of the users are not published onchain, but rather sent to external trusted parties, also known as committee members. A state update is valid and accepted onchain only if at least a quorum of the committee members sign a state update.
Funds can be lost if the external data becomes unavailable (CRITICAL).
Users can be censored if the committee restricts their access to the external data.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract. The system state is represented using Merkle roots.
Past upgrades
The metrics include upgrades on the currently used proxy contracts. Historical proxy contracts and changes of such are not included.
2026 May 21, 15:35 UTCHigh severity33changesUpgrade to ImmutableX contract: https://disco.l2beat.com/diff/eth:0x58b5484F489f7858DC83a5a677338074b57de806/eth:0x273b65a7231321D4ee47a4c47408Ef43517455Ec. It introduces 7 hardcoded L1 addresses that are granted VCO tokens from the ImmutableX bridge, each different amounts. They have already withdrawn these tokens. Amounts are small and token is worthless according to coingecko. Also, added registerSender and registerEthAddress functions from Users.sol in StarkEx repo to register an eth address for a given starknet address after checking a valid signature.
Upgrade to ImmutableX contract: https://disco.l2beat.com/diff/eth:0x58b5484F489f7858DC83a5a677338074b57de806/eth:0x273b65a7231321D4ee47a4c47408Ef43517455Ec.
It introduces 7 hardcoded L1 addresses that are granted VCO tokens from the ImmutableX bridge, each different amounts. They have already withdrawn these tokens. Amounts are small and token is worthless according to coingecko.
Also, added registerSender and registerEthAddress functions from Users.sol in StarkEx repo to register an eth address for a given starknet address after checking a valid signature.
| contract StarkExchange (eth:0x5FDCCA53617f4d2b9134B29090C87D01058e27e9) [N/A] { | |
| +++ description: None | |
| sourceHashes.1: | |
| - | "0xb71805b4d4f8f1e27f622cf275932a3b69fce577df37460525fce8b64adb1d00" |
| + | "0xc122235bc278c4eacd03c0bc862ed748a4d0c810460ff5348df2b85c2979c6a5" |
| values.$implementation: | |
| - | "eth:0x58b5484F489f7858DC83a5a677338074b57de806" |
| + | "eth:0x273b65a7231321D4ee47a4c47408Ef43517455Ec" |
| values.$pastUpgrades.9: | |
| + | ["2026-05-20T23:38:47.000Z","0x9af235b6b0759b9fa2b301c7bc7bf04e05e5bd15000abe74b405466e09fca332",["eth:0x273b65a7231321D4ee47a4c47408Ef43517455Ec"]] |
| values.$upgradeCount: | |
| - | 9 |
| + | 10 |
| values.implementation: | |
| - | "eth:0x58b5484F489f7858DC83a5a677338074b57de806" |
| + | "eth:0x273b65a7231321D4ee47a4c47408Ef43517455Ec" |
| values.HOLDER_1_AMOUNT: | |
| + | 4900000000000 |
| +++ description: HOLDER_i_ETH addresses are hardcoded into ImmutableX v2 rollup contract initializer, which assigns them custom amounts of VCO tokens (small amounts of worthless tokens). Tokens were already withdrawn. | |
| values.HOLDER_1_ETH: | |
| + | "eth:0x5eBb994EBC1c44815FbF2fA61a6E1f8368dcB0C7" |
| values.HOLDER_1_KEY: | |
| + | "3538623774493345151179551783812164840645197873942623890310120442690648622931" |
| values.HOLDER_2_AMOUNT: | |
| + | 125000000000 |
| values.HOLDER_2_ETH: | |
| + | "eth:0x216e8577B504aC3dB213eDd261e47fffBb354248" |
| values.HOLDER_2_KEY: | |
| + | "896591154720277861849412210959098837543990746331085354094151559066127293616" |
| values.HOLDER_3_AMOUNT: | |
| + | 7540000000 |
| values.HOLDER_3_ETH: | |
| + | "eth:0x10cbBBb225BBEA137aC01F0F6D91CDB126BccaA6" |
| values.HOLDER_3_KEY: | |
| + | "2337782983793367352107417745440247520204745783973227763313597957897585144884" |
| values.HOLDER_4_AMOUNT: | |
| + | 4900000000000 |
| values.HOLDER_4_ETH: | |
| + | "eth:0x409F85D2207796b543b8abdB6a0E2490BB1483D1" |
| values.HOLDER_4_KEY: | |
| + | "3515120365152864005724897321625748708134718892093672796597024618874380434380" |
| values.HOLDER_5_AMOUNT: | |
| + | 382500000000 |
| values.HOLDER_5_ETH: | |
| + | "eth:0xCE5A537D4dA620DE59efA6F74a0A065732600c71" |
| values.HOLDER_5_KEY: | |
| + | "320866735717256483006023350708017670742221720926224055507147702459465353560" |
| values.HOLDER_6_AMOUNT: | |
| + | "266488641810000000" |
| values.HOLDER_6_ETH: | |
| + | "eth:0x941f54cb53Dc1478Cb126a2Ba8a83b2130419dB5" |
| values.HOLDER_6_KEY: | |
| + | "1072283648975915474201171160655623968861623556483236771217709513165697501697" |
| values.HOLDER_7_AMOUNT: | |
| + | 235000000000 |
| values.HOLDER_7_ETH: | |
| + | "eth:0xBC6EeB5111fEa2B5e9B2Bc534bBcbCa9568999a4" |
| values.HOLDER_7_KEY: | |
| + | "750813242579361465277803604892953637745780756132536315292318654687088446962" |
| values.VCO_ASSET_TYPE: | |
| + | "1485183671027309009439509871835489442660821279230223034298428454062208985878" |
| implementationNames.eth:0x58b5484F489f7858DC83a5a677338074b57de806: | |
| - | "StarkExchangeMigration" |
| implementationNames.eth:0x273b65a7231321D4ee47a4c47408Ef43517455Ec: | |
| + | "StarkExchangeMigrationV2" |
| } |
2026 March 05, 09:30 UTCHigh severity163changesImmutable X migrates assets and the state root to immutable zkevm. Immutable X is deprecated now: https://x.com/Immutable/status/2016389261575258446?s=20. State root is injected into a specific contract ( zkEVMWithdrawalProcessor ) on immutable zkevm via Axelar message ( sendVaultRoot() funtion on VaultRootSenderAdapter ). Tokens are migrated manually by migration manager ( migrateHoldings() function on StarkExchangeMigration ), data for each token must be given as TokenMigrationDetails .
Immutable X migrates assets and the state root to immutable zkevm. Immutable X is deprecated now: https://x.com/Immutable/status/2016389261575258446?s=20.
State root is injected into a specific contract (zkEVMWithdrawalProcessor) on immutable zkevm via Axelar message (sendVaultRoot() funtion on VaultRootSenderAdapter). Tokens are migrated manually by migration manager (migrateHoldings() function on StarkExchangeMigration), data for each token must be given as TokenMigrationDetails.
| - | Status: DELETED |
| contract DACommittee (eth:0x16BA0f221664A5189cf2C1a7AF0d3AbFc70aA295) | |
| +++ description: Data Availability Committee (DAC) contract verifying and storing data availability claims from DAC Members (via a multisignature check). The threshold of valid signatures is 5. |
| - | Status: DELETED |
| reference SHARPVerifierCallProxy (eth:0x47312450B3Ac8b5b8e247a6bB6d523e7605bDb60) | |
| +++ description: None |
| - | Status: DELETED |
| contract OrderRegistry (eth:0x518c4A79a1102eEDc987005CA8cE6B87Ca14dDf8) | |
| +++ description: Helper contract for registering limit orders from L1. |
| contract StarkExchange (eth:0x5FDCCA53617f4d2b9134B29090C87D01058e27e9) { | |
| +++ description: None | |
| template: | |
| - | "starkex/StarkExchange" |
| sourceHashes.1: | |
| - | "0xfaa0bf87cf9230ba5a3f5530b447f76606e0cd9fb9d1acd2f3b87d30884e63d1" |
| + | "0x2e7cc0661a38ee126a3b09ecb461b7b1d7e0301c2f7b4245c5334553d16f9848" |
| proxyType: | |
| - | "StarkWare diamond" |
| + | "StarkWare proxy" |
| description: | |
| - | "Central Validium contract. Receives (verified) state roots from the Operator, allows users to consume L2 -> L1 messages and send L1 -> L2 messages. Critical configuration values for the L2's logic are defined here by various governance roles." |
| values.$implementation: | |
| - | ["eth:0x4EDD62189732e9fF476ABa880b48c29432A7AC9B","eth:0x62BCA4DB742A99c834e2c24b609656A70EA25379","eth:0x8536850750956c2FEebeCAB786d82271a5467687","eth:0x1c3A4EfF75a287Fe6249CAb49606FA25659929A2","eth:0x3799ad2a4Eb4E882219B02C036656d4ECbD437A1","eth:0x1688abB0B5c72F34B7f78e857Aa317deD5B5D339","eth:0xB3788a88F063B217227E27ae16Ba550db3132bE6"] |
| + | "eth:0x58b5484F489f7858DC83a5a677338074b57de806" |
| values.$pastUpgrades.0: | |
| + | ["2021-03-10T15:13:08.000Z","0x9b57c19aa91cc17c9487085b68532cd65d1e4c263b5928f14c03a9d36c9097df",["eth:0x49401Ddc4E0A858B5B4cf3D6De38393B7fAC7378"]] |
| values.$pastUpgrades.0.2.1: | |
| - | "eth:0x61d3389Aa2d001c860859cC021153e40D557BF4b" |
| values.$pastUpgrades.0.2.2: | |
| - | "eth:0xA4E9524EfbA0CB6BD7474a48C14582dEb300469E" |
| values.$pastUpgrades.0.2.3: | |
| - | "eth:0xedB67D40161D9fa660DCFFE60f859B7381E4793a" |
| values.$pastUpgrades.0.1: | |
| - | "0x9b57c19aa91cc17c9487085b68532cd65d1e4c263b5928f14c03a9d36c9097df" |
| + | "0xf42d8fc579401fc76769bf63ba72f7277aac976aeb2a4cd3eca899ca08de7c20" |
| values.$pastUpgrades.0.0: | |
| - | "2021-03-10T15:13:08.000Z" |
| + | "2021-03-16T18:04:39.000Z" |
| values.$pastUpgrades.1.2.1: | |
| - | "eth:0x61d3389Aa2d001c860859cC021153e40D557BF4b" |
| values.$pastUpgrades.1.2.2: | |
| - | "eth:0xA4E9524EfbA0CB6BD7474a48C14582dEb300469E" |
| values.$pastUpgrades.1.2.3: | |
| - | "eth:0xedB67D40161D9fa660DCFFE60f859B7381E4793a" |
| values.$pastUpgrades.1.1: | |
| - | "0xf42d8fc579401fc76769bf63ba72f7277aac976aeb2a4cd3eca899ca08de7c20" |
| + | "0x79f72bef0984e3ae76ab638c078f92f1a0d4ad2a289b8a91e072d81f77d505ce" |
| values.$pastUpgrades.1.0: | |
| - | "2021-03-16T18:04:39.000Z" |
| + | "2021-03-25T11:24:15.000Z" |
| values.$pastUpgrades.2.2.1: | |
| - | "eth:0x61d3389Aa2d001c860859cC021153e40D557BF4b" |
| values.$pastUpgrades.2.2.2: | |
| - | "eth:0xA4E9524EfbA0CB6BD7474a48C14582dEb300469E" |
| values.$pastUpgrades.2.2.3: | |
| - | "eth:0xedB67D40161D9fa660DCFFE60f859B7381E4793a" |
| values.$pastUpgrades.2.1: | |
| - | "0x79f72bef0984e3ae76ab638c078f92f1a0d4ad2a289b8a91e072d81f77d505ce" |
| + | "0x9e8cc538b40a70723a287ece3ecb4e6aafbbde0e04f621124df6e4c2d7995dc7" |
| values.$pastUpgrades.2.0: | |
| - | "2021-03-25T11:24:15.000Z" |
| + | "2021-03-26T08:01:31.000Z" |
| values.$pastUpgrades.3.2.0: | |
| - | "eth:0x49401Ddc4E0A858B5B4cf3D6De38393B7fAC7378" |
| values.$pastUpgrades.3.2.1: | |
| - | "eth:0x61d3389Aa2d001c860859cC021153e40D557BF4b" |
| values.$pastUpgrades.3.2.2: | |
| - | "eth:0xA4E9524EfbA0CB6BD7474a48C14582dEb300469E" |
| values.$pastUpgrades.3.2.3: | |
| - | "eth:0xedB67D40161D9fa660DCFFE60f859B7381E4793a" |
| + | "eth:0xB8563AD5aF1F79dd04937BE8B572318c8e6f43AC" |
| values.$pastUpgrades.3.1: | |
| - | "0x9e8cc538b40a70723a287ece3ecb4e6aafbbde0e04f621124df6e4c2d7995dc7" |
| + | "0x26fb60bb6b5ff3ef22cd959d007588f7410586499870411cfddc2759b97d44d6" |
| values.$pastUpgrades.3.0: | |
| - | "2021-03-26T08:01:31.000Z" |
| + | "2021-08-31T08:15:29.000Z" |
| values.$pastUpgrades.4.2.1: | |
| - | "eth:0xF65C115efd24102315Af53f84aD65aD240bc9D57" |
| values.$pastUpgrades.4.2.2: | |
| - | "eth:0x97AA9658cfE27D6382b71FF9E72d773615Bd529E" |
| values.$pastUpgrades.4.2.3: | |
| - | "eth:0x86d8f977C9cEC503ad4E6805802cEf62Cde13773" |
| values.$pastUpgrades.4.2.4: | |
| - | "eth:0x0D7c8d7A16c7832869d8FeEf02730238CdFe083A" |
| values.$pastUpgrades.4.2.5: | |
| - | "eth:0x2D542881E93491e765E5110c1e373FC2968E720A" |
| values.$pastUpgrades.4.2.6: | |
| - | "eth:0x970d1Fa79c64b256ef68bBFEab34137786811C7F" |
| values.$pastUpgrades.4.1: | |
| - | "0x26fb60bb6b5ff3ef22cd959d007588f7410586499870411cfddc2759b97d44d6" |
| + | "0xeaa0efb3937eee43c1083cc776d5033b131e6ef12ba0d0646db1b34e600847cd" |
| values.$pastUpgrades.4.0: | |
| - | "2021-08-31T08:15:29.000Z" |
| + | "2021-09-09T16:30:02.000Z" |
| values.$pastUpgrades.5.2.1: | |
| - | "eth:0xF65C115efd24102315Af53f84aD65aD240bc9D57" |
| values.$pastUpgrades.5.2.2: | |
| - | "eth:0x97AA9658cfE27D6382b71FF9E72d773615Bd529E" |
| values.$pastUpgrades.5.2.3: | |
| - | "eth:0x86d8f977C9cEC503ad4E6805802cEf62Cde13773" |
| values.$pastUpgrades.5.2.4: | |
| - | "eth:0x0D7c8d7A16c7832869d8FeEf02730238CdFe083A" |
| values.$pastUpgrades.5.2.5: | |
| - | "eth:0x2D542881E93491e765E5110c1e373FC2968E720A" |
| values.$pastUpgrades.5.2.6: | |
| - | "eth:0x970d1Fa79c64b256ef68bBFEab34137786811C7F" |
| values.$pastUpgrades.5.1: | |
| - | "0xeaa0efb3937eee43c1083cc776d5033b131e6ef12ba0d0646db1b34e600847cd" |
| + | "0x658a93571ca9733ba346bd746790a6d07821d86c89fd90809e85bf7f2f8d9797" |
| values.$pastUpgrades.5.0: | |
| - | "2021-09-09T16:30:02.000Z" |
| + | "2022-01-13T08:08:51.000Z" |
| values.$pastUpgrades.6.2.0: | |
| - | "eth:0xB8563AD5aF1F79dd04937BE8B572318c8e6f43AC" |
| values.$pastUpgrades.6.2.1: | |
| - | "eth:0xF65C115efd24102315Af53f84aD65aD240bc9D57" |
| values.$pastUpgrades.6.2.2: | |
| - | "eth:0x97AA9658cfE27D6382b71FF9E72d773615Bd529E" |
| values.$pastUpgrades.6.2.3: | |
| - | "eth:0x86d8f977C9cEC503ad4E6805802cEf62Cde13773" |
| values.$pastUpgrades.6.2.4: | |
| - | "eth:0x0D7c8d7A16c7832869d8FeEf02730238CdFe083A" |
| values.$pastUpgrades.6.2.5: | |
| - | "eth:0x2D542881E93491e765E5110c1e373FC2968E720A" |
| values.$pastUpgrades.6.2.6: | |
| - | "eth:0x970d1Fa79c64b256ef68bBFEab34137786811C7F" |
| + | "eth:0x4EDD62189732e9fF476ABa880b48c29432A7AC9B" |
| values.$pastUpgrades.6.1: | |
| - | "0x658a93571ca9733ba346bd746790a6d07821d86c89fd90809e85bf7f2f8d9797" |
| + | "0x3425fd24435e4aefdb08f3970e61e446eb5d21a1e0c916d1ba9331b060b72192" |
| values.$pastUpgrades.6.0: | |
| - | "2022-01-13T08:08:51.000Z" |
| + | "2024-05-20T06:39:35.000Z" |
| values.$pastUpgrades.7.2.0: | |
| - | "eth:0x4EDD62189732e9fF476ABa880b48c29432A7AC9B" |
| values.$pastUpgrades.7.2.1: | |
| - | "eth:0x62BCA4DB742A99c834e2c24b609656A70EA25379" |
| values.$pastUpgrades.7.2.2: | |
| - | "eth:0x8536850750956c2FEebeCAB786d82271a5467687" |
| values.$pastUpgrades.7.2.3: | |
| - | "eth:0x1c3A4EfF75a287Fe6249CAb49606FA25659929A2" |
| values.$pastUpgrades.7.2.4: | |
| - | "eth:0x3799ad2a4Eb4E882219B02C036656d4ECbD437A1" |
| values.$pastUpgrades.7.2.5: | |
| - | "eth:0x1688abB0B5c72F34B7f78e857Aa317deD5B5D339" |
| values.$pastUpgrades.7.2.6: | |
| - | "eth:0xB3788a88F063B217227E27ae16Ba550db3132bE6" |
| + | "eth:0x58b5484F489f7858DC83a5a677338074b57de806" |
| values.$pastUpgrades.7.1: | |
| - | "0x3425fd24435e4aefdb08f3970e61e446eb5d21a1e0c916d1ba9331b060b72192" |
| + | "0x07ac699d0dc30804af73843cc1cba5f50780135e25932cf78be69a3e6c11b194" |
| values.$pastUpgrades.7.0: | |
| - | "2024-05-20T06:39:35.000Z" |
| + | "2026-03-05T01:07:11.000Z" |
| values.$upgradeCount: | |
| - | 8 |
| + | 9 |
| values.defaultVaultWithdrawalLock: | |
| - | 0 |
| values.DEPOSIT_CANCEL_DELAY: | |
| - | 172800 |
| values.FREEZE_GRACE_PERIOD: | |
| - | 604800 |
| values.getLastBatchId: | |
| - | 37990 |
| values.getOrderRoot: | |
| - | "168353765887718686397671181439168594225139531838374564195072013673941816314" |
| values.getOrderTreeHeight: | |
| - | 63 |
| values.getRegisteredAvailabilityVerifiers: | |
| - | ["eth:0x16BA0f221664A5189cf2C1a7AF0d3AbFc70aA295"] |
| values.getRegisteredVerifiers: | |
| - | ["eth:0x6e3AbCE72A3CD5edc05E59283c733Fd4bF8B3baE"] |
| values.getSequenceNumber: | |
| - | 37802 |
| values.getVaultRoot: | |
| - | "543280986076401044787518957175086881219650536676907070252569311042264623146" |
| values.getVaultTreeHeight: | |
| - | 31 |
| values.implementation: | |
| - | "eth:0x4EDD62189732e9fF476ABa880b48c29432A7AC9B" |
| + | "eth:0x58b5484F489f7858DC83a5a677338074b57de806" |
| values.isStrictVaultBalancePolicy: | |
| - | false |
| values.MAIN_GOVERNANCE_INFO_TAG: | |
| - | "StarkEx.Main.2019.GovernorsInformation" |
| values.MAX_FORCED_ACTIONS_REQS_PER_BLOCK: | |
| - | 10 |
| values.MAX_VERIFIER_COUNT: | |
| - | 64 |
| values.operators: | |
| - | ["eth:0x9B7f7d0d23d4CAce5A3157752D0D4e4bf25E927e"] |
| values.orderRegistryAddress: | |
| - | "eth:0x518c4A79a1102eEDc987005CA8cE6B87Ca14dDf8" |
| values.STARKEX_MAX_DEFAULT_VAULT_LOCK: | |
| - | 604800 |
| values.StarkWareDiamond_upgradeDelay: | |
| - | 1209600 |
| values.tokenAdmins: | |
| - | ["eth:0xdc1bFbC2B8f01439eEea8e4659bbb452D0f9eE2A","eth:0xeDb0219557ba13816f1dEb7fA54688362B05A5aE"] |
| values.UNFREEZE_DELAY: | |
| - | 31536000 |
| values.VERIFIER_REMOVAL_DELAY: | |
| - | 2419200 |
| values.VERSION: | |
| - | "4.0.1" |
| + | "StarkEx-IMX-Migration-1.0.0" |
| values.getAssetInfo: | |
| + | [] |
| values.migrationManager: | |
| + | "eth:0xD2C37fC6fD89563187f3679304975655e448D192" |
| values.NATIVE_ETH: | |
| + | "eth:0x0000000000000000000000000000000000000Eee" |
| values.rootSenderAdapter: | |
| + | "eth:0x9Fabd9Cc71f15b9Cfd717E117FBb9cfD9fC7cd32" |
| values.StarkWareProxy_upgradeDelay: | |
| + | 1209600 |
| values.vaultRoot: | |
| + | "543280986076401044787518957175086881219650536676907070252569311042264623146" |
| values.zkEVMBridge: | |
| + | "eth:0xBa5E35E26Ae59c7aea6F029B68c6460De2d13eB6" |
| values.zkEVMWithdrawalProcessor: | |
| + | "eth:0xCeA34C706C4A18E103575832Dd21fD3656026D1E" |
| fieldMeta: | |
| - | {"$admin":{"severity":"HIGH","description":"Permissioned to upgrade the proxy implementations and access all `onlyGovernance` restricted functions in the various implementation contracts."},"isFinalized":{"severity":"HIGH","description":"Finalizes most of the configuration of the contract, which cannot be changed afterwards (only thorugh an upgrade)."},"DEPOSIT_CANCEL_DELAY":{"description":"The time delay required before canceled deposits to the L2 can be reclaimed."}} |
| implementationNames.eth:0x4EDD62189732e9fF476ABa880b48c29432A7AC9B: | |
| - | "StarkExchange" |
| implementationNames.eth:0x62BCA4DB742A99c834e2c24b609656A70EA25379: | |
| - | "AllVerifiers" |
| implementationNames.eth:0x8536850750956c2FEebeCAB786d82271a5467687: | |
| - | "TokensAndRamping" |
| implementationNames.eth:0x1c3A4EfF75a287Fe6249CAb49606FA25659929A2: | |
| - | "StarkExState" |
| implementationNames.eth:0x3799ad2a4Eb4E882219B02C036656d4ECbD437A1: | |
| - | "ForcedActions" |
| implementationNames.eth:0x1688abB0B5c72F34B7f78e857Aa317deD5B5D339: | |
| - | "OnchainVaults" |
| implementationNames.eth:0xB3788a88F063B217227E27ae16Ba550db3132bE6: | |
| - | "ProxyUtils" |
| implementationNames.eth:0x58b5484F489f7858DC83a5a677338074b57de806: | |
| + | "StarkExchangeMigration" |
| category: | |
| - | {"name":"Local Infrastructure","priority":5} |
| } |
| - | Status: DELETED |
| contract GpsFactRegistryAdapter (eth:0x6e3AbCE72A3CD5edc05E59283c733Fd4bF8B3baE) | |
| +++ description: Adapter between the core contract and the eth:0x47312450B3Ac8b5b8e247a6bB6d523e7605bDb60. Stores the Cairo programHash (`3485280386001712778192330279103973322645241679001461923469191557000342180556`). |
| contract IMXAdminMultisig (eth:0xD2C37fC6fD89563187f3679304975655e448D192) { | |
| +++ description: None | |
| receivedPermissions.0.via: | |
| + | [{"address":"eth:0xdE2BCd3F0297d29c25e83228E5A33C0b43b51Ec8"}] |
| receivedPermissions.0.role: | |
| - | ".$admin" |
| + | "admin" |
| receivedPermissions.0.from: | |
| - | "eth:0x5FDCCA53617f4d2b9134B29090C87D01058e27e9" |
| + | "eth:0x4f49B53928A71E553bB1B0F66a5BcB54Fd4E8932" |
| receivedPermissions.0.permission: | |
| - | "governStarknet" |
| + | "upgrade" |
| receivedPermissions.1.role: | |
| - | ".$admin" |
| + | "admin" |
| receivedPermissions.1.description: | |
| - | "manage the token admin role." |
| receivedPermissions.1.permission: | |
| - | "interact" |
| + | "upgrade" |
| receivedPermissions.2.via: | |
| + | [{"address":"eth:0xdE2BCd3F0297d29c25e83228E5A33C0b43b51Ec8"}] |
| receivedPermissions.2.role: | |
| - | ".$admin" |
| + | "admin" |
| receivedPermissions.2.delay: | |
| - | 1209600 |
| receivedPermissions.2.from: | |
| - | "eth:0x5FDCCA53617f4d2b9134B29090C87D01058e27e9" |
| + | "eth:0xBa5E35E26Ae59c7aea6F029B68c6460De2d13eB6" |
| directlyReceivedPermissions: | |
| + | [{"permission":"act","from":"eth:0xdE2BCd3F0297d29c25e83228E5A33C0b43b51Ec8","role":".owner"}] |
| } |
| + | Status: CREATED |
| contract AxelarGasService (eth:0x2d5d7d31F671F86C782533cc367F14109a082712) | |
| +++ description: None |
| + | Status: CREATED |
| contract AxelarGatewayProxyMultisig (eth:0x4F4495243837681061C4743b74B3eEdf548D56A5) | |
| +++ description: None |
| + | Status: CREATED |
| contract RootAxelarBridgeAdaptor (eth:0x4f49B53928A71E553bB1B0F66a5BcB54Fd4E8932) | |
| +++ description: None |
| + | Status: CREATED |
| contract StarkExchangeMigration (eth:0x58b5484F489f7858DC83a5a677338074b57de806) | |
| +++ description: None |
| + | Status: CREATED |
| contract Operators (eth:0x7DdB2d76b80B0AA19bDEa48EB1301182F4CeefbC) | |
| +++ description: None |
| + | Status: CREATED |
| contract ChildERC20 (eth:0x8804A8aA1F18f23aE8A456dD73806FdA3219FaD1) | |
| +++ description: None |
| + | Status: CREATED |
| contract VaultRootSenderAdapter (eth:0x9Fabd9Cc71f15b9Cfd717E117FBb9cfD9fC7cd32) | |
| +++ description: None |
| + | Status: CREATED |
| contract RootERC20BridgeFlowRate (eth:0xBa5E35E26Ae59c7aea6F029B68c6460De2d13eB6) | |
| +++ description: None |
| + | Status: CREATED |
| contract Wrapped Ether Token (eth:0xC02aaA39b223FE8D0A0e5C4F27eAD9083C756Cc2) | |
| +++ description: None |
| + | Status: CREATED |
| contract ProxyAdmin (eth:0xdE2BCd3F0297d29c25e83228E5A33C0b43b51Ec8) | |
| +++ description: None |
| + | Status: CREATED |
| contract Immutable X Token (eth:0xF57e7e7C23978C3cAEC3C3548E3D615c346e79fF) | |
| +++ description: None |
2026 March 02, 11:28 UTC2changesRotated ms member.
Rotated ms member.
| contract IMXAdminMultisig (eth:0xD2C37fC6fD89563187f3679304975655e448D192) { | |
| +++ description: None | |
| values.$members.5: | |
| - | "eth:0xb3538EDB1cD74AE43e0aD25eac6F03553657E3fB" |
| + | "eth:0x94e97260182B9537822687Dd3c301225c6f87a5e" |
| } |
2025 March 07, 13:48 UTC2changesMS: single member change.
MS: single member change.
| contract IMXAdminMultisig (0xD2C37fC6fD89563187f3679304975655e448D192) { | |
| +++ description: None | |
| values.$members.5: | |
| - | "0xbD8Dc294478ec4dAd9f1b4596bf275f4d0309817" |
| + | "0xb3538EDB1cD74AE43e0aD25eac6F03553657E3fB" |
| } |
2024 December 12, 15:33 UTC6changesRemoved Multisig1 as admin of StarkExchange, now admin is only Multisig2.
Removed Multisig1 as admin of StarkExchange, now admin is only Multisig2.
| contract StarkExchange (0x5FDCCA53617f4d2b9134B29090C87D01058e27e9) { | |
| +++ description: None | |
| issuedPermissions.1: | |
| - | {"permission":"upgrade","target":"0xD2C37fC6fD89563187f3679304975655e448D192","via":[]} |
| issuedPermissions.0.target: | |
| - | "0x9C41deab42Bae7c0ec4DB3cECc0faD86F4D6EC91" |
| + | "0xD2C37fC6fD89563187f3679304975655e448D192" |
| values.$admin: | |
| - | ["0x9C41deab42Bae7c0ec4DB3cECc0faD86F4D6EC91","0xD2C37fC6fD89563187f3679304975655e448D192"] |
| + | "0xD2C37fC6fD89563187f3679304975655e448D192" |
| } |
| - | Status: DELETED |
| contract IMXProxyGovernanceMultisig1 (0x9C41deab42Bae7c0ec4DB3cECc0faD86F4D6EC91) | |
| +++ description: None |
The system has a centralized operator
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force exit the system
Force exit allows the users to escape censorship by withdrawing their funds. The system allows users to force the withdrawal of funds by submitting a request directly to the contract onchain. The request must be served within a defined time period. If this does not happen, the system will halt regular operation and permit trustless withdrawal of funds.
Users can be censored if the operator refuses to include their transactions. However, there exists a mechanism to independently exit the system.
Regular exit
The user initiates the withdrawal by submitting a regular transaction on this chain. When the block containing that transaction is settled the funds become available for withdrawal on L1. ZK proofs are required to settle blocks. Finally the user submits an L1 transaction to claim the funds. When withdrawing NFTs they are minted on L1.
Forced exit
If the user experiences censorship from the operator with regular exit they can submit their withdrawal requests directly on L1. The system is then obliged to service this request. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular exit.
Emergency exit
If the enough time deadline passes and the forced exit is still ignored the user can put the system into a frozen state, disallowing further state updates. In that case everybody can withdraw by submitting a merkle proof of their funds with their L1 transaction.

Ethereum
Actors:
A Multisig with 4/6 threshold.
- Can upgrade with no delay
- RootAxelarBridgeAdaptor ProxyAdmin
- StarkExchange
- RootERC20BridgeFlowRate ProxyAdmin
- Can upgrade with no delay
- AxelarGasService

Ethereum
- Roles:
- admin: EOA 1
- Roles:
- admin: ProxyAdmin; ultimately IMXAdminMultisig
- Roles:
- admin: IMXAdminMultisig

- Roles:
- admin: ProxyAdmin; ultimately IMXAdminMultisig
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 14d delay on code upgrades.